Phishing Analysis
Detailed analysis of captured phishing page
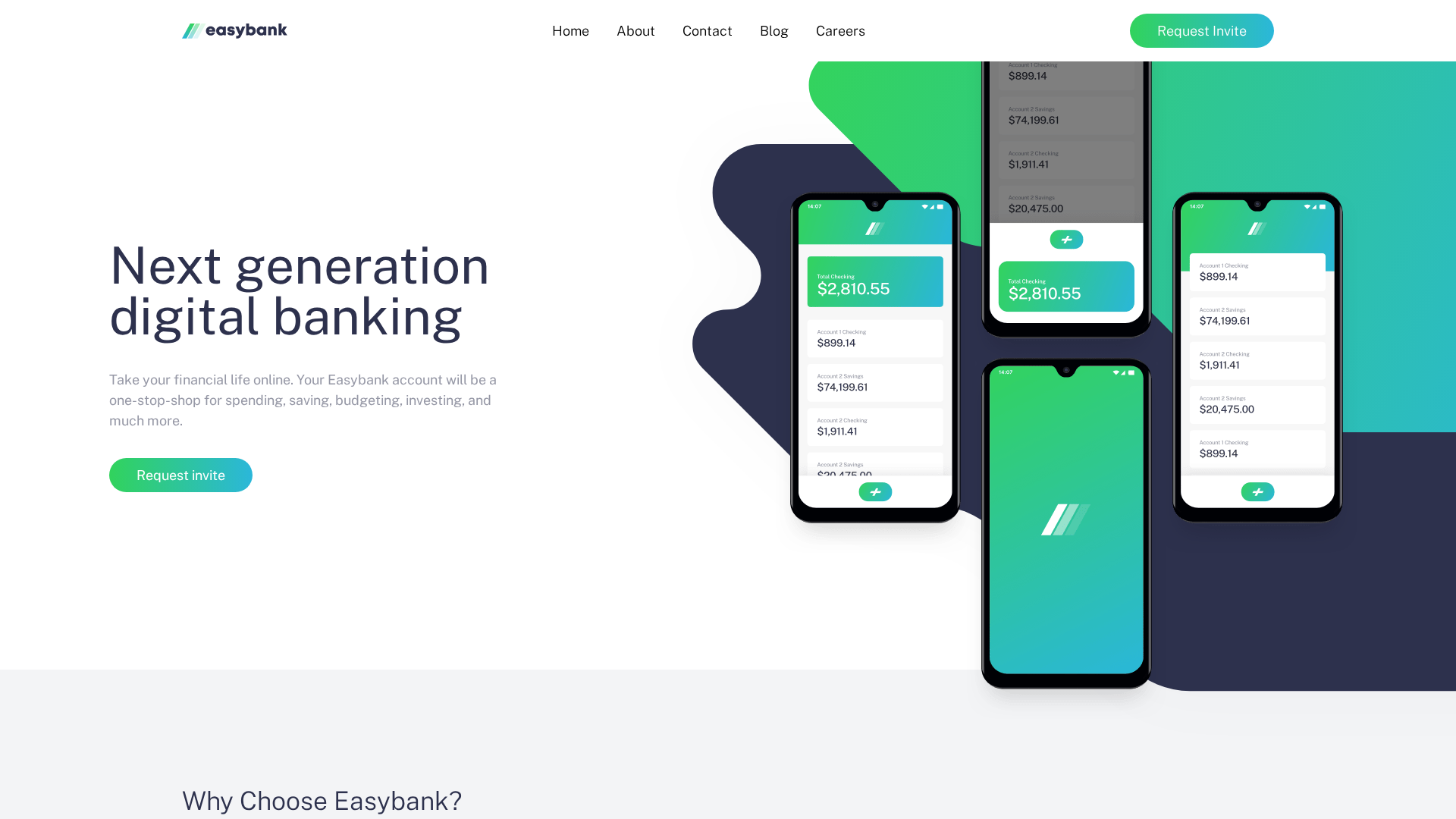
Visual Capture
Detection Info
https://easybank-landing-pi.vercel.app/
Detected Brand
Easybank
Country
International
Confidence
100%
HTTP Status
200
Report ID
00abab67-2d5…
Analyzed
2026-03-13 11:39
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T12462857463700E2705A306FEBAD2A632A691E34AD716C9C01BD65DF53BE1F57E83204B |
|
CONTENT
ssdeep
|
384:pLMJ4KQ9WEN+9nYo0jBBkotrOeU49/5syBbaps:t0o+1KrOeU4/tBmK |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cd64b259a99b96a4 |
|
VISUAL
aHash
|
f8f0f0f0f8f8f8ff |
|
VISUAL
dHash
|
5107666a42408827 |
|
VISUAL
wHash
|
f0f0b080f0f0f8bf |
|
VISUAL
colorHash
|
07003000c00 |
|
VISUAL
cropResistant
|
5107666a42408827,b28c8cb28b82b3aa,0c7354ccd41403c2 |
Code Analysis
Risk Score
68/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 Banking
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Easybank users
• Method: Impersonation
• Exfil: Unknown, likely harvesting credentials or personal information.
• Indicators: Free hosting, brand logo.
• Risk: High
🔒 Obfuscation Detected
- fromCharCode
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Free Hosting
The use of free hosting on vercel.app is a strong indicator of phishing.
Brand Impersonation
The site displays the Easybank logo, creating an attempt to impersonate a legitimate brand.
Obfuscation
Obfuscation, which can hide malicious code, was detected.
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Easybank users (International)
Attack Method
Brand impersonation + obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Banking
- 2 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Easybank
Fake Service
Digital Banking
⚔️ Attack Methodology
Primary Method: Brand Impersonation
The attackers are attempting to mimic the legitimate Easybank website to trick users into providing sensitive information.
Secondary Method: Credential Harvesting (Likely)
The site likely aims to collect user credentials or personal information to gain access to accounts.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
easybank-landing-pi.vercel.app
Registered
None
Registrar
None
Status
None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for easybank-landing-pi.vercel.app
Found 2 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.