Phishing Analysis
Detailed analysis of captured phishing page
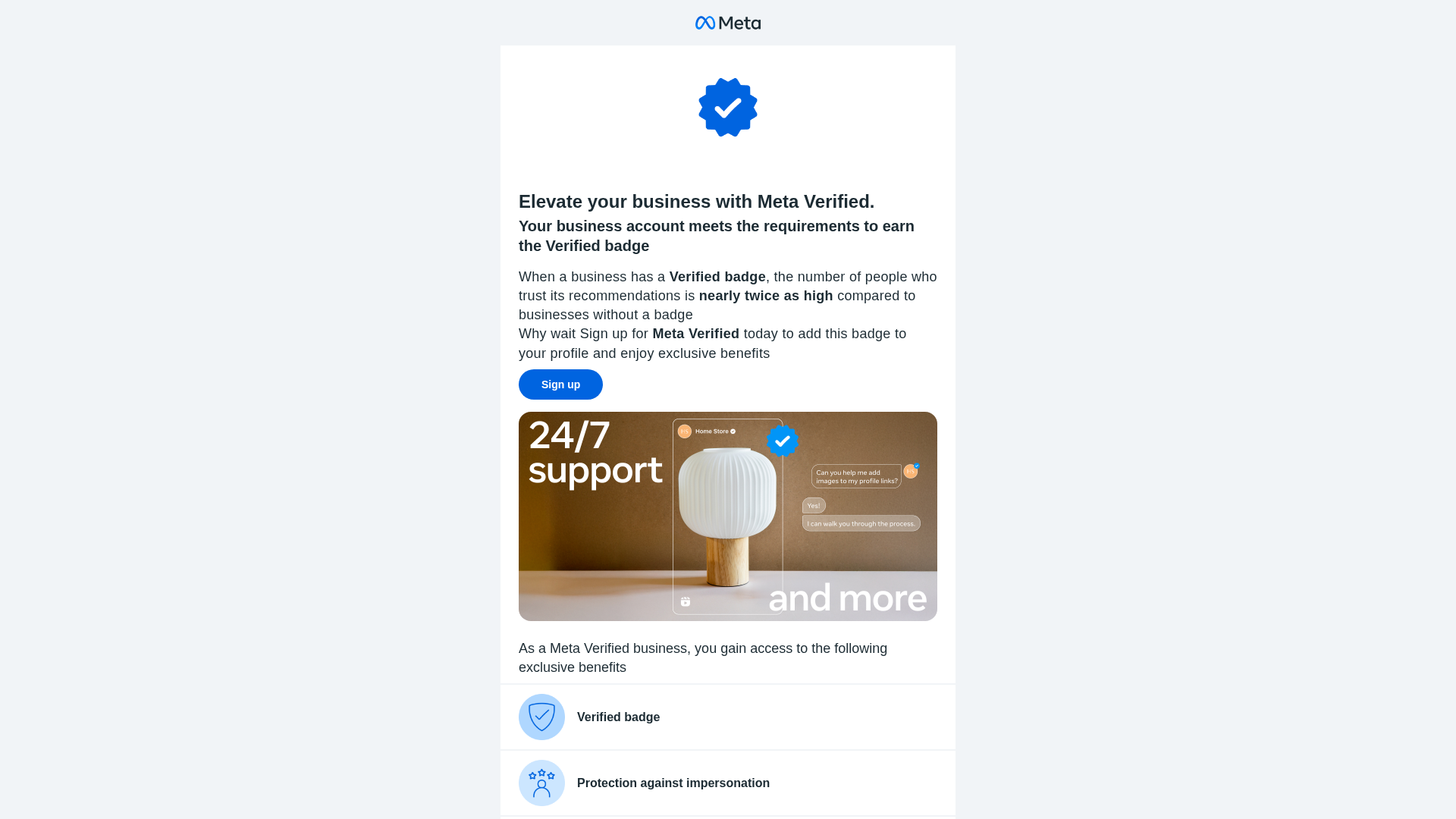
Visual Capture
Detection Info
https://rebrand.ly/pageticks
Detected Brand
Meta
Country
International
Confidence
95%
HTTP Status
200
Report ID
0210fc2f-a4d…
Analyzed
2025-12-27 10:31
Final URL (after redirects)
http://135.148.61.188/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T164F18621C6402B6D55688162F232BEC963A0461F876305F4FA629B3FB85D072BF577BC |
|
CONTENT
ssdeep
|
192:jUGjEFEw+0LrVSa3Yvm1l0Br7vrCkrqsICO1l+xrZO:AY6 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b3cecc3364cc3364 |
|
VISUAL
aHash
|
ffffefcfc3c3ffff |
|
VISUAL
dHash
|
28284c1c5d5c1818 |
|
VISUAL
wHash
|
3c24040cc3c3cfdf |
Code Analysis
⚠️ Phishing Confirmed
🔬 Threat Analysis Report
• Threat: Brand impersonation phishing
• Target: Businesses using Meta services
• Method: Redirecting users to a rebrand.ly link to impersonate Meta Verified feature
• Exfil: Unknown - likely aiming to harvest business information or login credentials on a subsequent page
• Indicators: Domain mismatch (rebrand.ly), Meta branding
• Risk: MEDIUM - Could lead to business data theft or account compromise if further action is taken
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for rebrand.ly
Found 10 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.