Phishing Analysis
Detailed analysis of captured phishing page
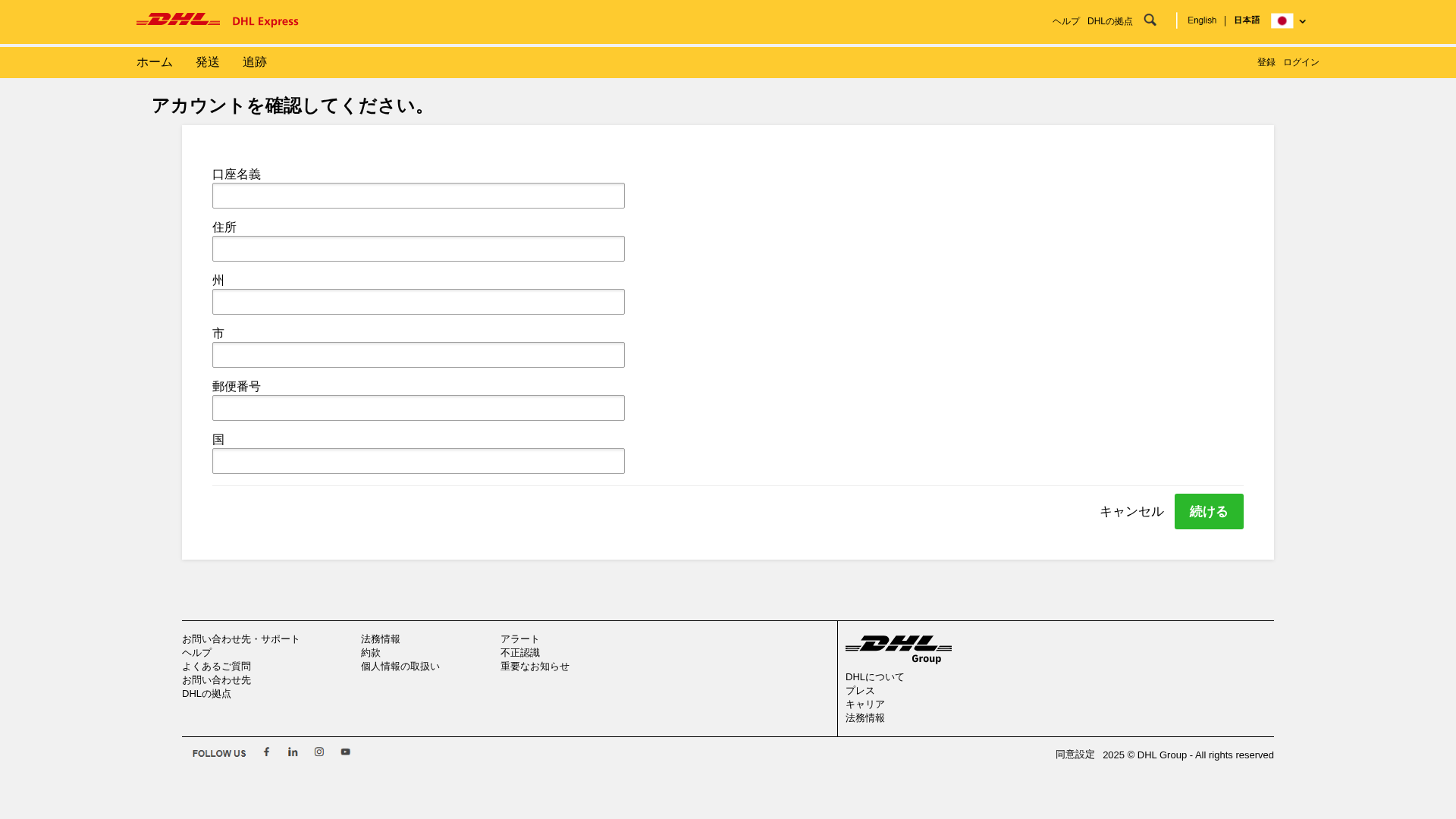
Visual Capture
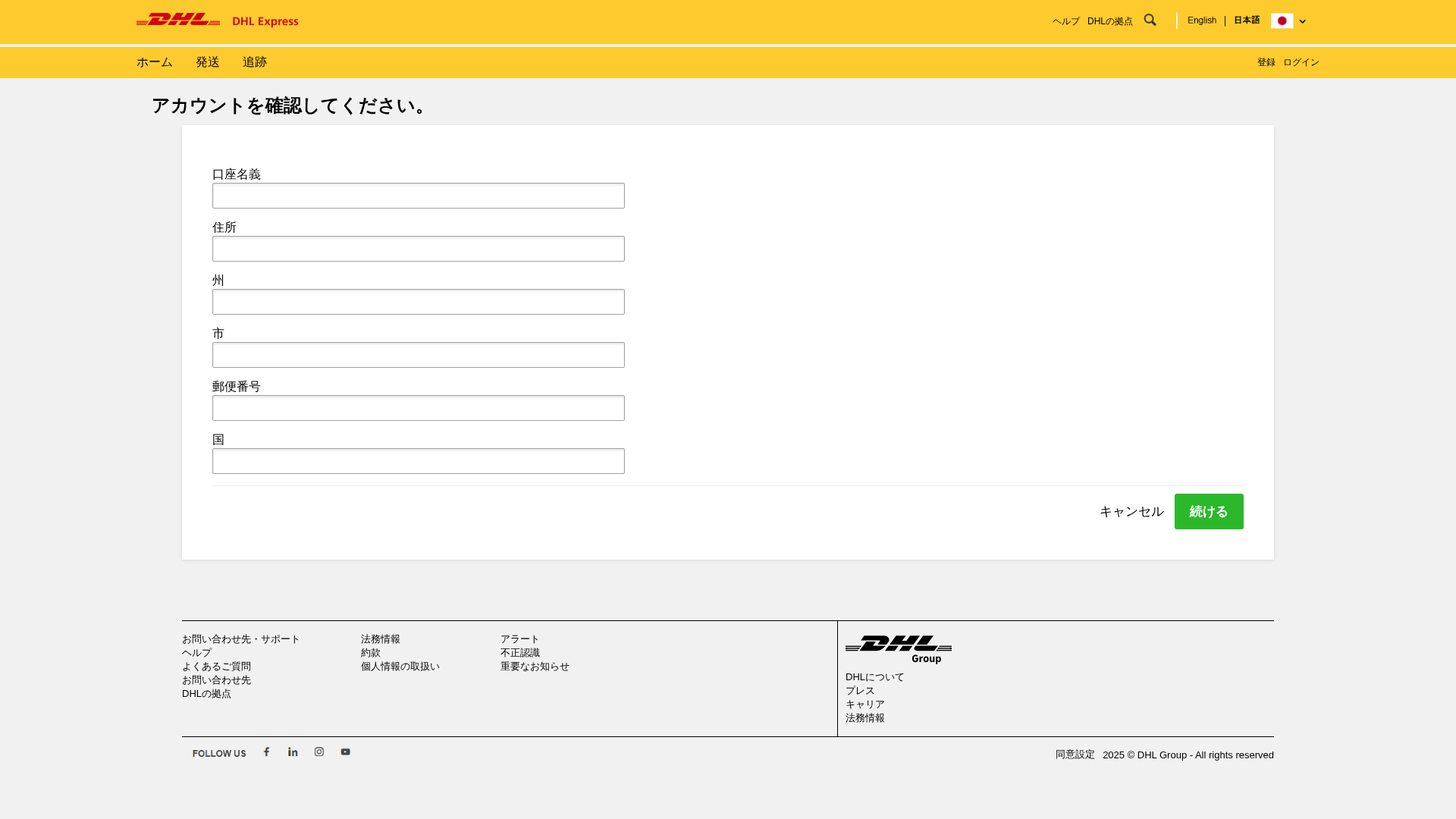
Detection Info
http://bsb.test.nidgecloud.com/sm2
Detected Brand
DHL
Country
International
Confidence
100%
HTTP Status
200
Report ID
02457fb2-077…
Analyzed
2026-02-27 11:11
Final URL (after redirects)
https://bsb.test.nidgecloud.com/sm2/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T10E818A3480499C778483D1E0DBB5260B7686CA62CC8B3B089BEDD798AFD2D5DCD56D60 |
|
CONTENT
ssdeep
|
48:nXsHfGGIcGklftSUGzvT+FGTGWGTWWiSi5igRgnvWuIsFtZ:nAGbkaU9GTBGTRivYVTX |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
97172f6a5b2d5242 |
|
VISUAL
aHash
|
00fffffffffc0301 |
|
VISUAL
dHash
|
6960d0d4d0957649 |
|
VISUAL
wHash
|
007e7e7e7e7c8081 |
|
VISUAL
colorHash
|
07000038000 |
|
VISUAL
cropResistant
|
6960d0d4d0957649 |
Code Analysis
Risk Score
95/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Phishing
• Target: DHL customers
• Method: Impersonation through a fake login form.
• Exfil: Unknown, but likely through JavaScript obfuscation.
• Indicators: Domain mismatch, form requests for personal information, JavaScript form submission, obfuscation detected.
• Risk: HIGH
🔒 Obfuscation Detected
- fromCharCode
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Domain Mismatch
The domain is completely unrelated to DHL.
Form for PII
The form requests a lot of personal information with no clear purpose.
JavaScript Obfuscation
The javascript code is obfuscated to hide its intent.
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
DHL users (International)
Attack Method
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Personal Info
- 6 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
DHL
Official Website
https://www.dhl.com
Fake Service
DHL Login / Account Verification
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attackers are using a phishing website that mimics a DHL login or verification page to collect user credentials.
Secondary Method: Social Engineering
The attackers likely used emails or other means to trick the victims into providing their personal information.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
bsb.test.nidgecloud.com
Registered
None
Registrar
None
Status
None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for bsb.test.nidgecloud.com
Found 2 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.