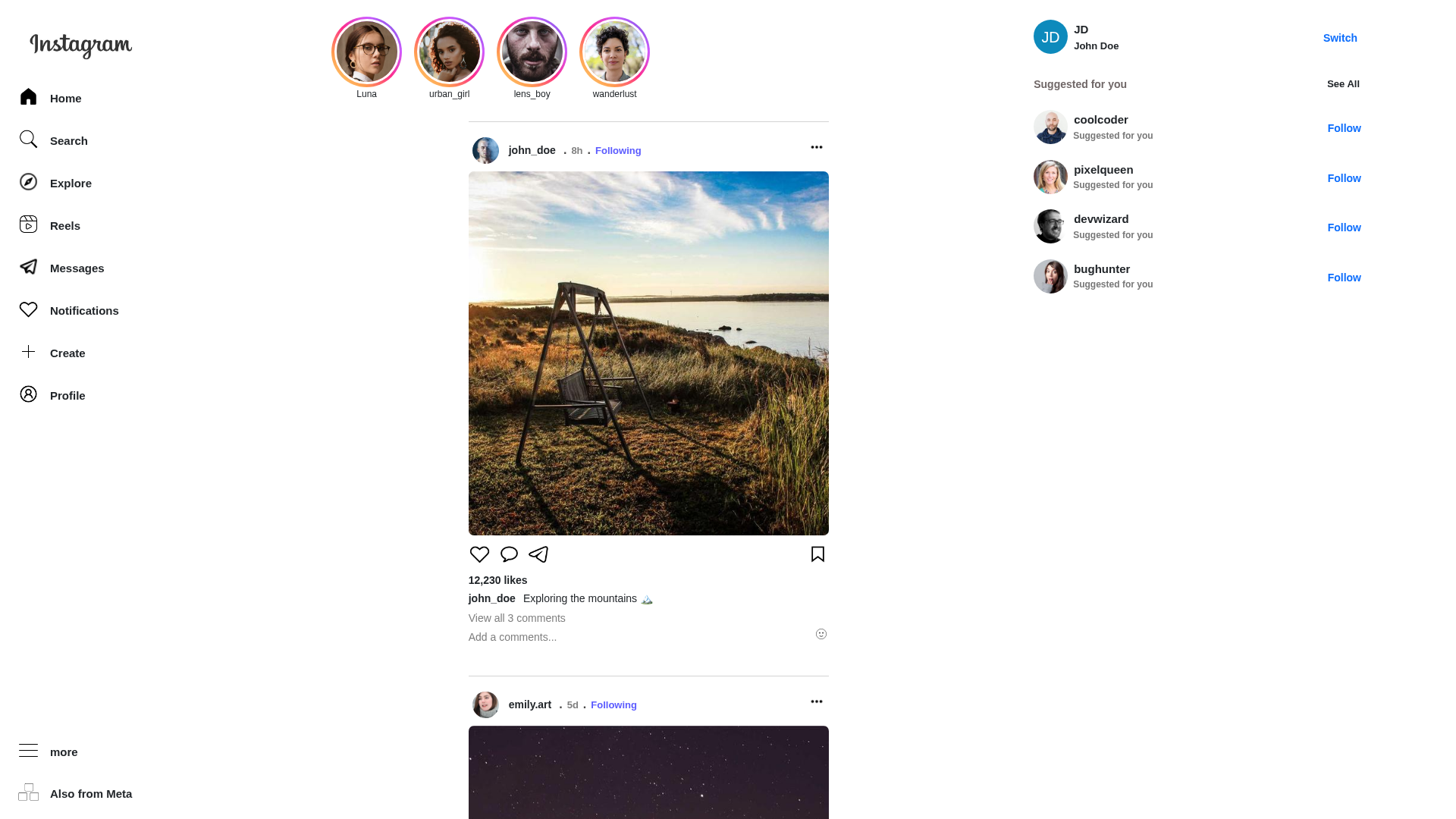
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T15B52F679C2E690371127C8C3A9352BBD70F293BDD8321816B2FC93990BD9D85BD42E59 |
|
CONTENT
ssdeep
|
384:xJWMAO0LdHg0LRVA0LHdI0LTCE0LRAo0L0xb0L/B10Lu/w0LHx10l3VA:xJ1AOMHg2VAKdI8CE8AotxboB11/wexX |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b3cccc8c33cc3966 |
|
VISUAL
aHash
|
cfffe7c7c7e7ffc7 |
|
VISUAL
dHash
|
b28b8b9d8d1d108d |
|
VISUAL
wHash
|
0b414147c7c7df47 |
|
VISUAL
colorHash
|
07c00208000 |
|
VISUAL
cropResistant
|
b28b8b9d8d1d108d,385f8923571a4763,a0a0a000501008c0 |
Code Analysis
🔒 Obfuscation Detected
- fromCharCode
🎯 Kit Endpoints
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAADIAAAAyCAYAAAAeP4ixAAAACXBIWXMAAAsTAAALEwEAmpwYAAAChUlEQVR4nO2Zu24TQRSGPxeElgYbEVKYPAIFEC6vgAQO8gUJER4AiYuIkBLogBdAooIUSBGiIDFKHQINl7wBDS2kCiIhsYPRkf6VpjCIxTNj77KfNNLK3v3/Pes9Z86MoaBgJDkEzAALwDqwAexqfAU+6rsrQIUR5CzQBjpA7y+HnbsMnGEEmARWnJvrAq+B68BxoAzs07DjE8ANYE3nJte9Ao4OK4gW8E038h24DxxMcb0F9gDYksYm0CAy887TXATGB9A6Ajx39OaIxD0Z/tRxyZPuNWAvVjAtGZlhLYD+tBNMnYCJneTE7VAmwKyTM9UQBitOToSk5ORMO8Q80VOFmSA846qEPeC0T+G2RK3ExsJKs3ku+Ww7OprA0swTg2LzTFftjR0PzFU9mVXi80bel32ILUjM2o7Y3JT3Ex9i6xKz3ik2U/J+70NsQ2Ix8yOhIu8vPsR2JDZGfPbL+0deAtnMy6v1yWey26IoNqfkbWU4F+X3sQ+xGYnZ8jQ2b+V93td7mrQoXlqFlC1KBzjgS3RZT8YauVg8lKe19N44KdHtIbTxx3yLt50n5Gud3g/TfiGvlyEMqpqYelqOhuKOPGxn8nAok4az+WAbBb656Gw+nCMwc04ws55es5J+iSSIPe3YECuYJGdsk+1fmXBywh1WeptEoO7kzJZKc5p5pqwSu+00ht0+wTSIQNWpZonxmlqLKU2mYxoVfXZLvZN704tK7OYwg0FbNksp/1aw5cGzPs3o74KpE5GyNgqeAh9UQnc0uX0G3gGPdFN/WhY0RiEYX1h57/QJ5hI5CqZFBpnOUzC1/yGYJhkNZrcIJiMFYJ6McsH5Ze6ScWox/84uKAB+ATiuEwljmLOIAAAAAElFTkSuQmCC
📡 API Calls Detected
- ./data/suggestionUsers.json
- ./data/posts.json
- ./data/profile.json
- /data/stories.json
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
- 2 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 2 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for www.instagram-clone-mu.vercel.app
Found 1 other scan for this domain