
Phishing Analysis
Detailed analysis of captured phishing page
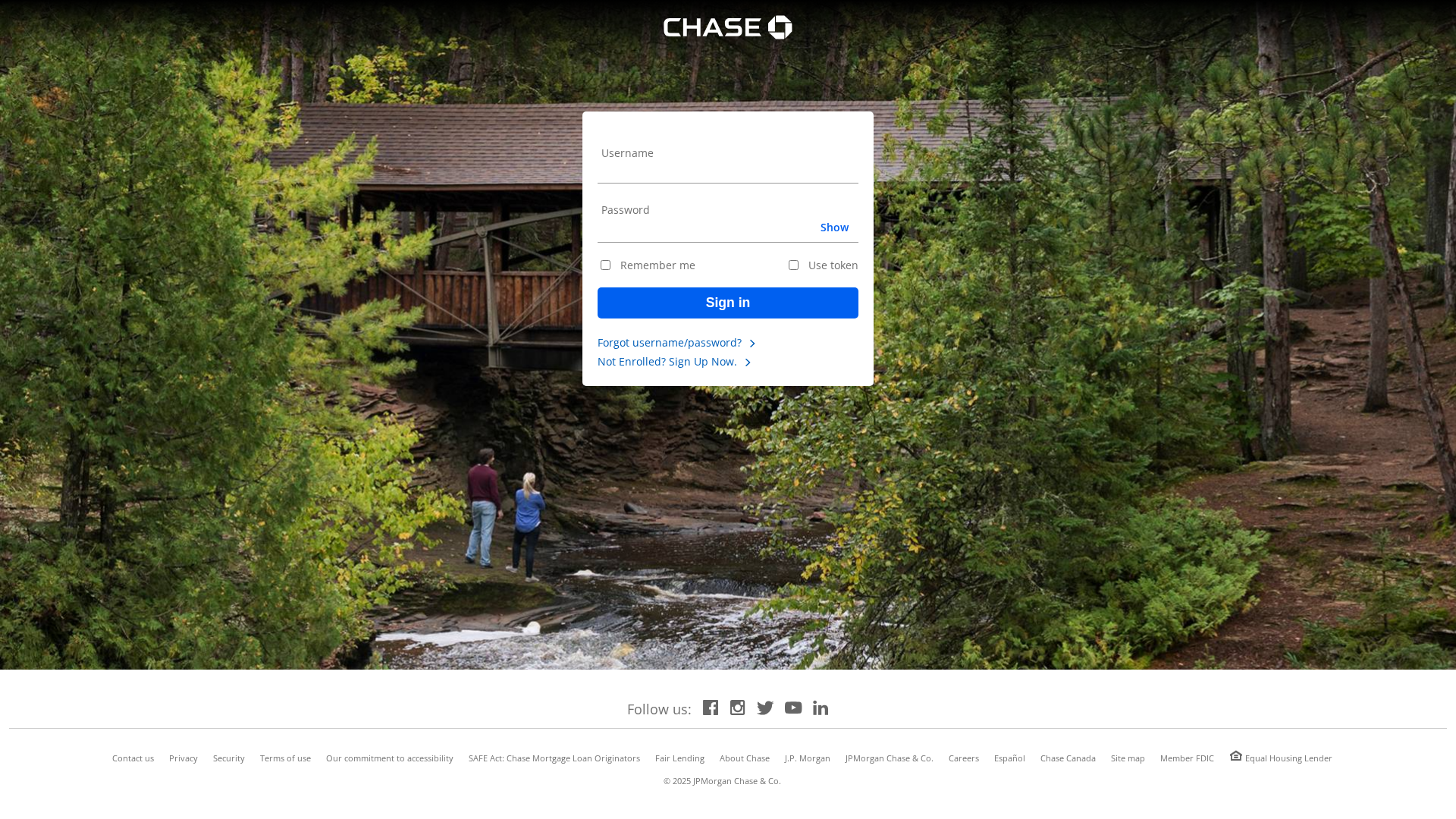
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1176110F14584A42902A282D18E32E369D382D474DF730B0B9AE5E75EBBDBFD8CC05079 |
|
CONTENT
ssdeep
|
48:nXjLFTNmTNMitOKsanfI6SfnCw02hse5SnCw02hsesdQ5YpP5hvopBliFOo6wXmb:nTLG4KVZS6l3ONl3/2Ex0ZN |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
c958e663b30e35e2 |
|
VISUAL
aHash
|
001818180000ffff |
|
VISUAL
dHash
|
91b2b0b0dbd2e200 |
|
VISUAL
wHash
|
007c5c584848ffff |
|
VISUAL
colorHash
|
0b580001000 |
|
VISUAL
cropResistant
|
d4e0d4d0d0d6dcdc,e0e1000c20150800,1db2b1b0b1dbd2f2 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Chase customers
• Method: Impersonation and credential harvesting
• Exfil: Data posted to post.php, potentially via Telegram bot
• Indicators: Domain mismatch, login form, visual imitation
• Risk: High
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- fromCharCode
- unicode_escape
🎯 Kit Endpoints
- https://api.telegram.org/bot7571937466:AAGs4WrakEQckPQy5-v_8kD26YOiIKFc7TU/sendMessage?chat_id=1418778003&text=New visit%0AIP:207.244.255.96
📤 Form Action Targets
- post.php
🔑 Telegram Bot Tokens (1)
- 7571937466:AAGs...iIKFc7TU
💬 Telegram Chat IDs (1)
- 1418778003
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- 1 Telegram bot token(s)
- Kit types: Credential Harvester
- 28 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker creates a fake login page that mimics the appearance of Chase's login. The user enters their credentials, which are then harvested and sent to the attacker.
Secondary Method: Data Exfiltration via POST
Data is submitted to a 'post.php' script, allowing the attacker to capture the victim's data.
📡 Telegram Command & Control Infrastructure
💬 Message Templates (3)
| ID | Portuguese | English | Trigger |
|---|---|---|---|
🌐 Infrastructure Indicators of Compromise
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for gillmedical.org
Found 2 other scans for this domain
