
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1F0D16270D029CC3B418785D8B2B59B4F3691C255CB230B0467F8A3BE6FEACBAED55254 |
|
CONTENT
ssdeep
|
96:TggUUZUbEArkGAnvI5vPelvpAiv9301C5b2K8UnKAkRhfTKDI:3/2AykfvEvmlvtv9EwJ8UnKAYhbKE |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
ce4ea8b96466a6a3 |
|
VISUAL
aHash
|
f0f0f0f0f8ffffff |
|
VISUAL
dHash
|
2424242420000000 |
|
VISUAL
wHash
|
90900010b0ffffff |
|
VISUAL
colorHash
|
066000080c0 |
|
VISUAL
cropResistant
|
2424242420000000,fc987a32f4e47939,b2b210b0e4f0328c |
Code Analysis
🔬 Threat Analysis Report
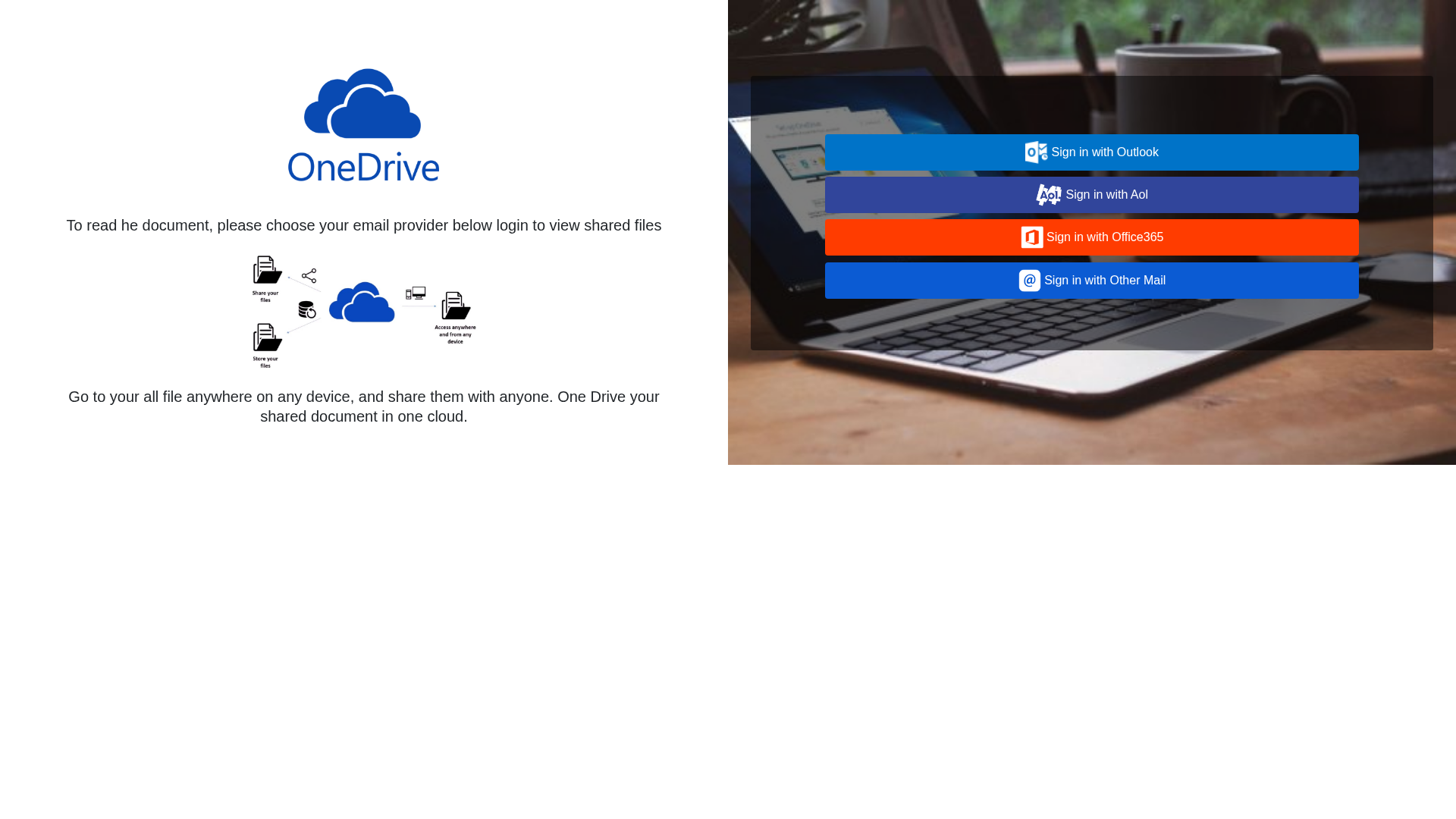
• Threat: Phishing
• Target: OneDrive users
• Method: Impersonation and credential harvesting
• Exfil: Likely steals credentials entered on other sites
• Indicators: Suspicious domain, branding attempt
• Risk: High
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Personal Info
- 11 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker is using a fake OneDrive login page to harvest user credentials by prompting them to sign in with their email provider.
Secondary Method: Social Engineering
The page tries to trick users into believing they need to log in to view a shared document, making them more likely to enter their credentials.
🌐 Infrastructure Indicators of Compromise
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for dvh.cil.temporary.site
Found 6 other scans for this domain
