Phishing Analysis
Detailed analysis of captured phishing page
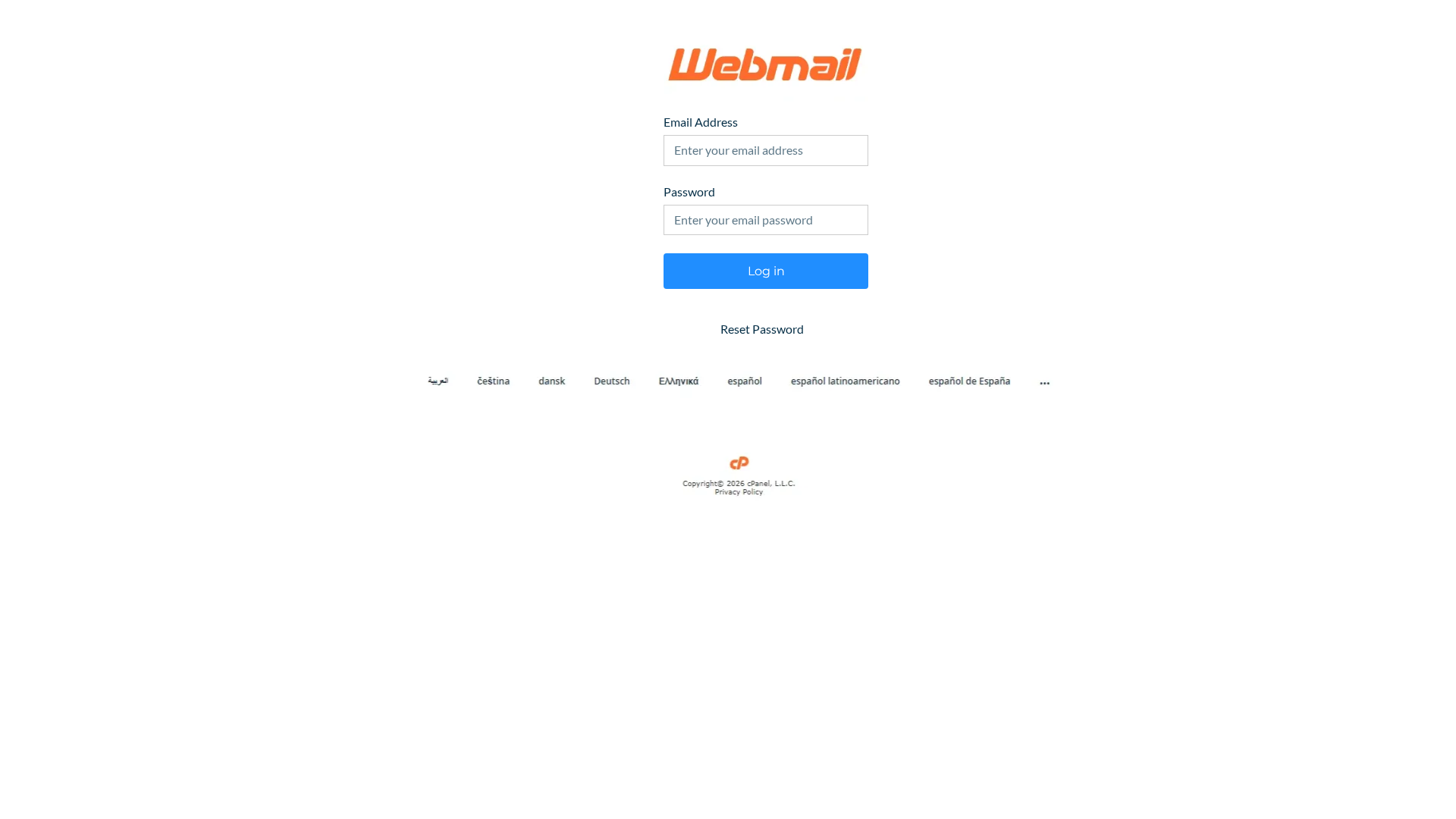
Visual Capture
No screenshot available
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T19D1146A151491FFEB187C164BAC1E39BE7C84940CB4707011FD4A3D559DDD9CC9786C8 |
|
CONTENT
ssdeep
|
12:nwMy7FUEDg8NOckr7dFgBZcRoWwXaPJE6HdEI9FuP05MP4HKkUt3YbFgLeK:n/CjDfQr7dcZgAXaPJECeIJvaSK |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e666999999666626 |
|
VISUAL
aHash
|
e7e7e7e7ffffffff |
|
VISUAL
dHash
|
0c0c0d0c00000000 |
|
VISUAL
wHash
|
e4e4e4e4f0f0f0f0 |
|
VISUAL
colorHash
|
07002c00000 |
|
VISUAL
cropResistant
|
0c0c0d0c00000000 |
Code Analysis
🔒 Obfuscation Detected
- base64_strings
🎯 Kit Endpoints
- +encodeURIComponent(src));event.stopPropagation();}}}catch(e){log(e);} if($(
- /v7/idp/sessions/login
📡 API Calls Detected
- POST
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- 1 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters credentials into 1 fake form. Form data is captured via JavaScript or backend submission and transmitted to attacker's server for account compromise.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 1 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Light
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)