Phishing Analysis
Detailed analysis of captured phishing page
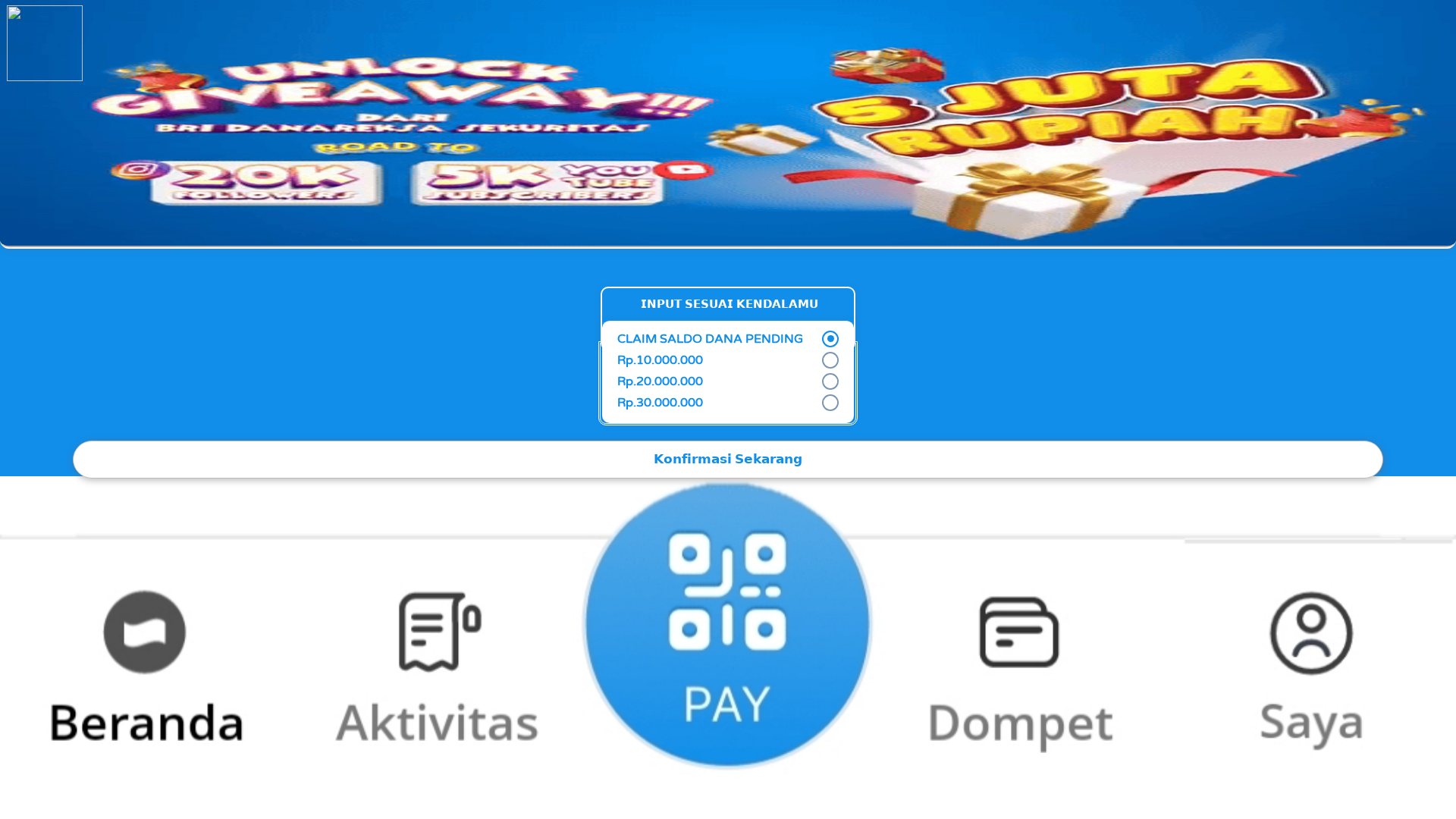
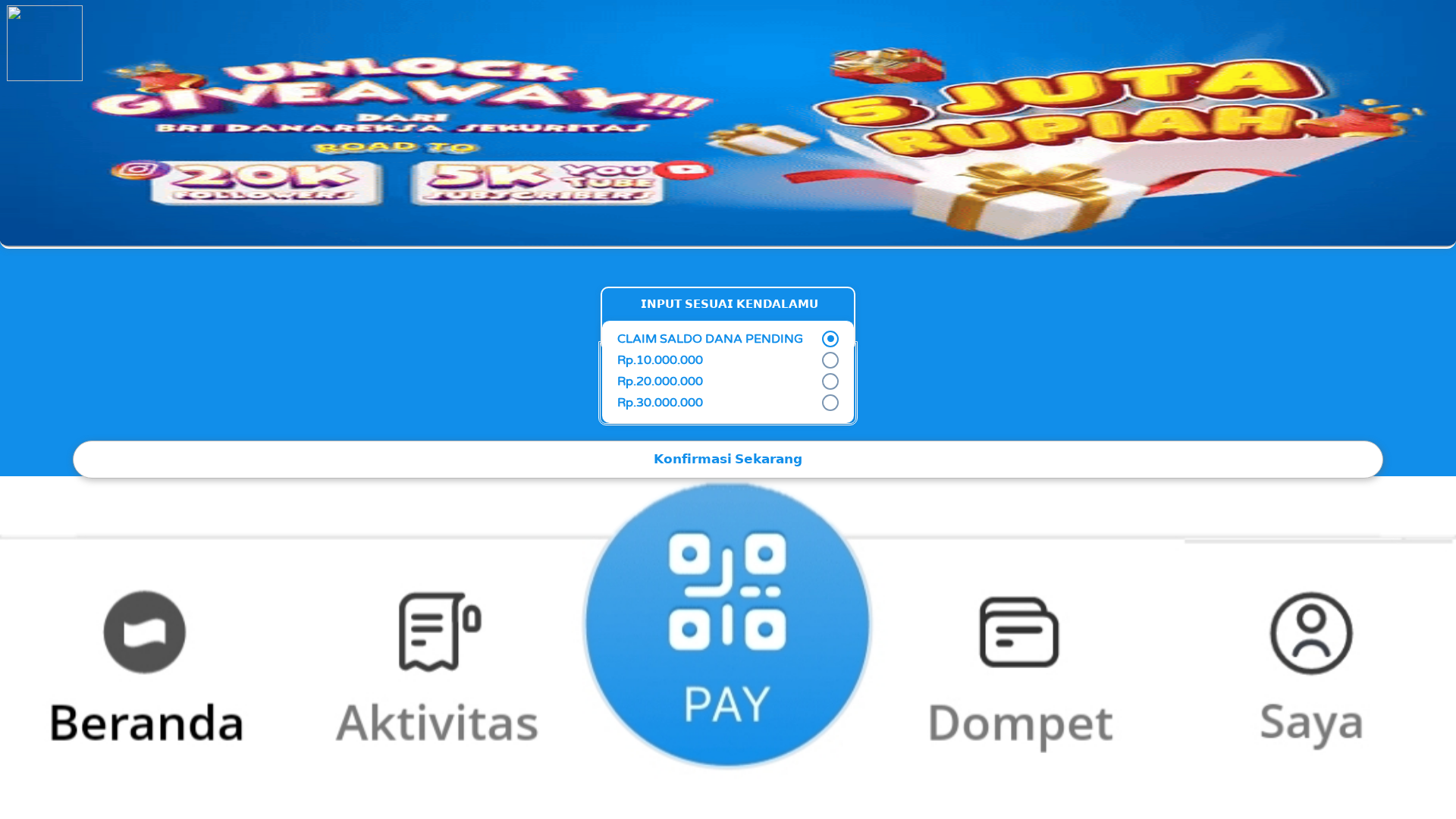
Visual Capture
Detection Info
https://qwip.qzz.io/dana/yrt54s/xxf/
Detected Brand
BRI Danareksa Sekuritas (likely)
Country
Indonesia
Confidence
100%
HTTP Status
200
Report ID
06c3031c-3a1…
Analyzed
2026-02-20 11:26
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T17962A7F19248041F3326D6C5DEA6AFCD6267C50BCB06455AFAB5205BB78EDF8C4B2350 |
|
CONTENT
ssdeep
|
384:fdDmYDmCSiSpWy58So179bC9zT0VB62T6z4Nk9Gs90s90s90zdte:fdDmYDmCjwWy58So179bC9zToB62TAtb |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
951ca7a74969ea62 |
|
VISUAL
aHash
|
00040018ffffe7ff |
|
VISUAL
dHash
|
caccac32a88ccece |
|
VISUAL
wHash
|
00000018ffffe7ff |
|
VISUAL
colorHash
|
03000000180 |
|
VISUAL
cropResistant
|
bc746bade4872738,261872643c94b8c9,ee3cc0ec96b692d6,b232b20ccececeea,d0ceccac5db233b2 |
Code Analysis
Risk Score
68/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 Banking
🔬 Threat Analysis Report
• Threat: Phishing
• Target: BRI Danareksa Sekuritas customers
• Method: Claiming giveaway
• Exfil: Unknown, likely to steal credentials
• Indicators: Mismatched domain, giveaway claim, forms
• Risk: HIGH
🔒 Obfuscation Detected
- fromCharCode
📡 API Calls Detected
- POST
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Domain Reputation
Unrelated domain and likely malicious.
Phishing Indicators
Giveaway, form, brand impersonation.
Content Analysis
Suspicious text and calls to action.
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
BRI Danareksa Sekuritas (likely) users (Indonesia)
Attack Method
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Banking
- 2 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
BRI Danareksa Sekuritas
Official Website
Unknown
Fake Service
Giveaway/Claims
Fraudulent Claims
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The site uses a form to collect user data, possibly including credentials, under the guise of a giveaway. This data is then likely sent to a malicious server.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
qwip.qzz.io
Registered
Unknown
Registrar
Unknown
Status
Inactive
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for qwip.qzz.io
Found 2 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.