
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
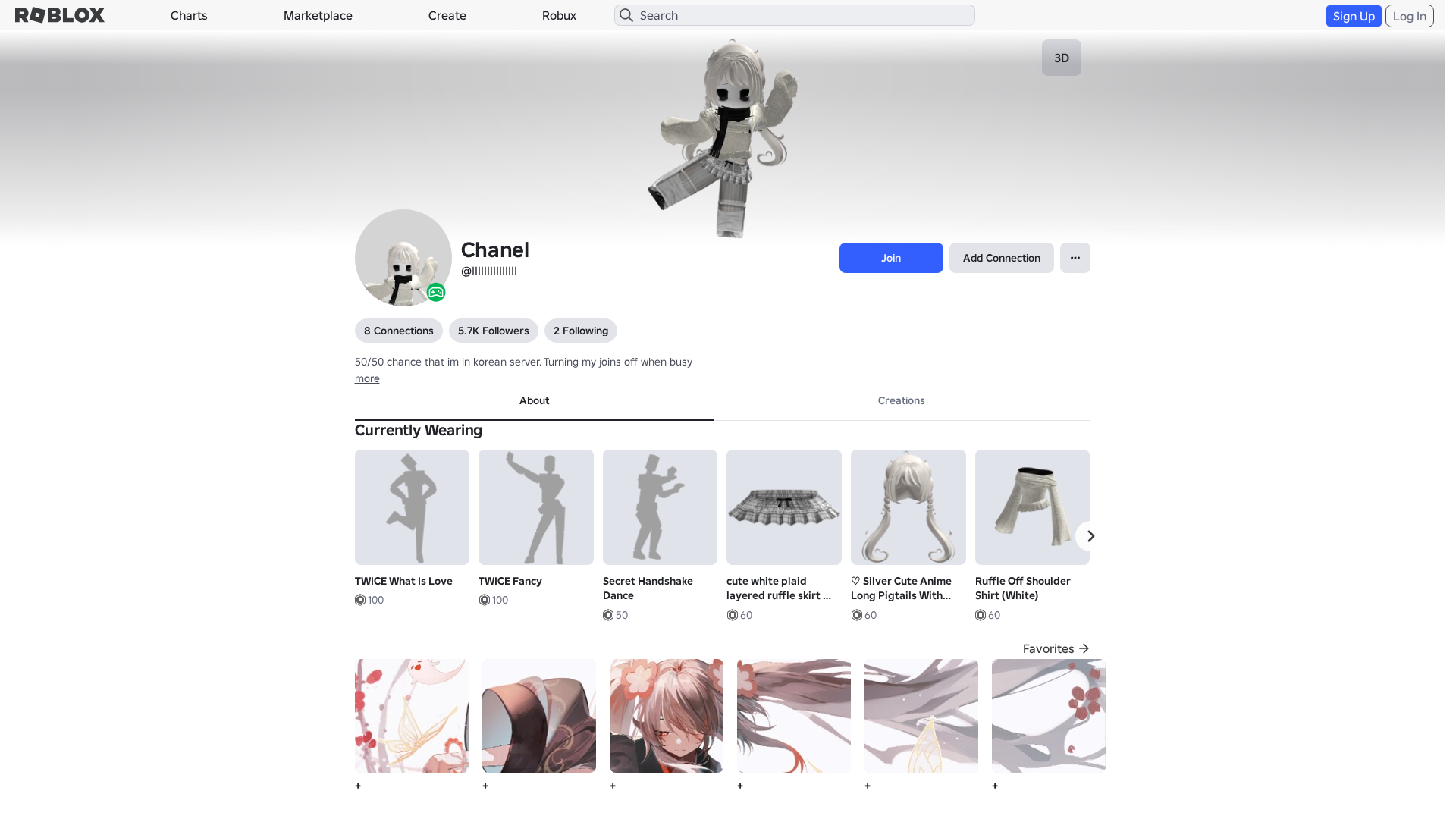
Detection Info
https://www.robiox.com.py/users/369657886823/profile
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
072522d2-5cc…
Analyzed
2026-04-08 10:10
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T13F73327292542837627B79D6F064672AD2D3D70FCA8346E1A2F8D39A0FD6CE1E85340D |
|
CONTENT
ssdeep
|
1536:F9VXWn4rFwtDjQsgJMgP6gbqgRvgTBgIrgyWge4gjIgxHdgjDg4XguDgSzg97gJ/:rVXW8wNUdnVuP9mF/s5n/yE7IIoVHZQ9 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b146734699ccdc65 |
|
VISUAL
aHash
|
0000d3ffc3f3c3c3 |
|
VISUAL
dHash
|
e8c836300e260f1a |
|
VISUAL
wHash
|
0000d7ffc3c3e3cb |
|
VISUAL
colorHash
|
074000400c0 |
|
VISUAL
cropResistant
|
e8c836300e260f1a |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/13344121112/TWICE-What-Is-Love
- https://api.injuries.lu/catalog/134373057501582/Secret-Handshake-Dance-2-Wicked-Official
- /login?returnUrl=
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F369657886823%2Fprofile
- https://api.injuries.lu/catalog/123826481391033/Ruffle-Off-Shoulder-Shirt-White
- https://api.injuries.lu/catalog/82771661276566/Silver-Cute-Anime-Long-Pigtails-With-Bows
- https://api.injuries.lu/catalog/18538158932/adidas-Sports-Swim
- https://api.injuries.lu/catalog/94596985409445/Kawaii-White-Sweater-w-Bows-Lace
- https://api.injuries.lu/catalog/3576686446/Hello
- https://api.injuries.lu/catalog/86499698/Woman-Right-Arm
- https://api.injuries.lu/catalog/136276875045281/Popular-Run
- https://api.injuries.lu/catalog/133304526526319/Popular-Walk
- https://api.injuries.lu/catalog/120642514156293/Secret-Handshake-Dance
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/18538150608/adidas-Sports-Idle
- https://api.injuries.lu/catalog/83937116921114/Popular-Fall
- https://api.injuries.lu/catalog/16371235025/Skadoosh-Emote-Kung-Fu-Panda-4
- https://api.injuries.lu/catalog/130373407996664/Popular-Jump
- https://api.injuries.lu/catalog/11309263077/Elton-John-Heart-Skip
- https://api.injuries.lu/catalog/86499666/Woman-Torso
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/134384128693598/emo-dark-plaid-winter-scarf-3-0
- https://api.injuries.lu/catalog/81633558240156/cute-white-plaid-layered-ruffle-skirt-w-bow-3-0
- https://api.injuries.lu/catalog/14618207727/Default-Mood
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/108067704306069/nervous-sleepy-eyebags-moe-face-Dynamic-Head
- https://api.injuries.lu/catalog/11893914579/black-mini-skirt-w-knit-tights-coquett-90s
- https://api.injuries.lu/catalog/86499716/Woman-Left-Arm
- https://api.injuries.lu/catalog/18538170170/adidas-Sports-Climb
- https://api.injuries.lu/catalog/13520623514/TWICE-Fancy
- https://api.injuries.lu/catalog/130046968468383/Fashion-Spin
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F369657886823%2Fprofile
📡 API Calls Detected
- https://ro.blox.com/Ebh5?
- GET
- https://apis.
- get
- POST
- https://help.roblox.com/hc/articles/30428367965460
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 212 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Roblox users
Attack Method
credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
HTTP POST to backend
Risk Assessment
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 212 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 212 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
www.robiox.com.py
Registered
Unknown
Registrar
None
Status
Age unknown
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for www.robiox.com.py
Found 10 other scans for this domain
-
https://www.robiox.com.py/users/262683709646/profi...
https://www.robiox.com.py/users/387072077925/profi...
https://www.robiox.com.py/users/217025834840/profi...
https://www.robiox.com.py/users/335157511751/profi...
https://www.robiox.com.py/users/239884675658/profi...
https://www.robiox.com.py/users/377777277866/profi...
https://www.robiox.com.py/users/255445160301/profi...
https://www.robiox.com.py/users/378472335145/profi...
https://www.robiox.com.py/users/411240076850/profi...
https://www.robiox.com.py/games/90118298734859/EMO...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.