
Phishing Analysis
Detailed analysis of captured phishing page
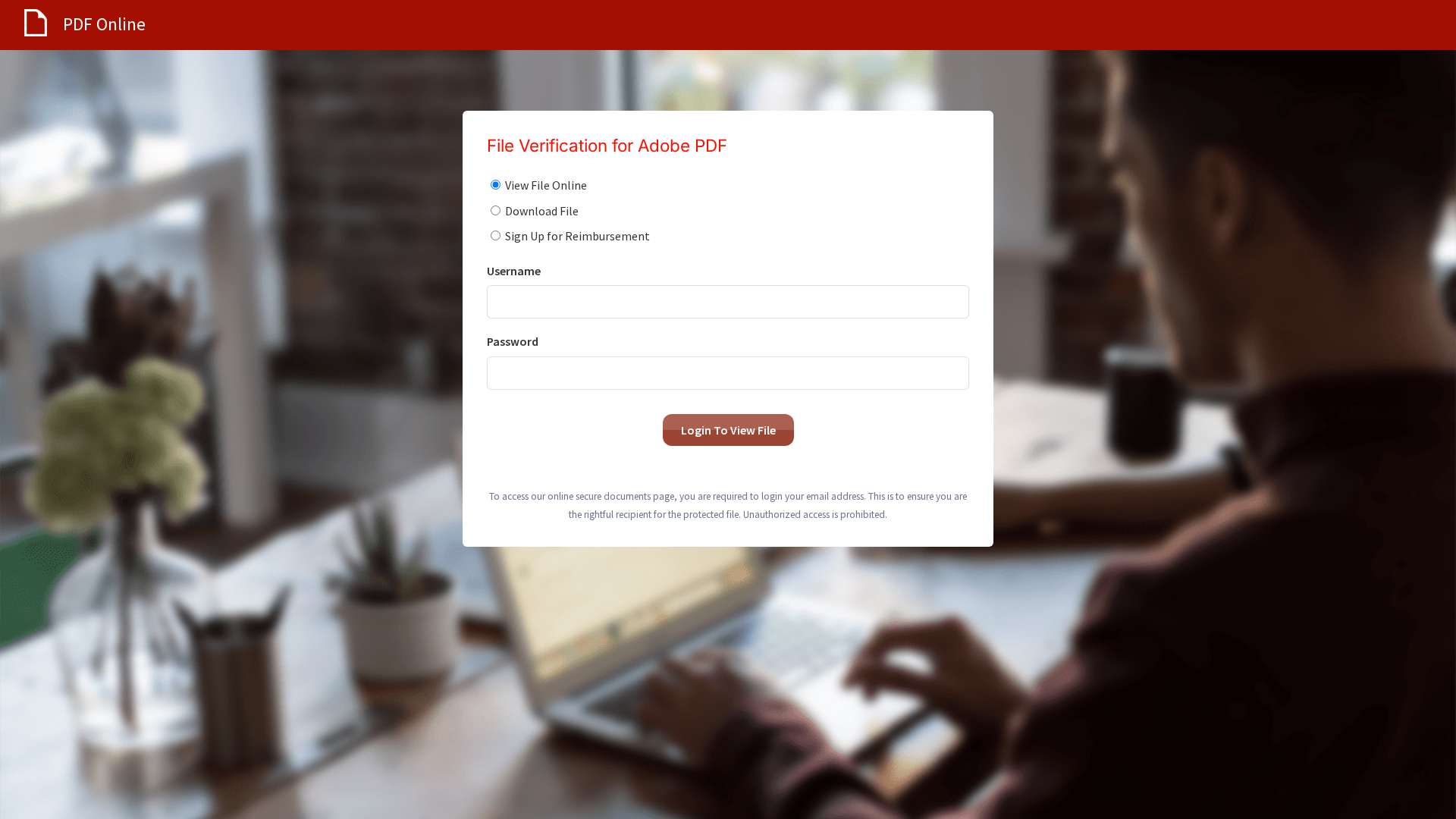
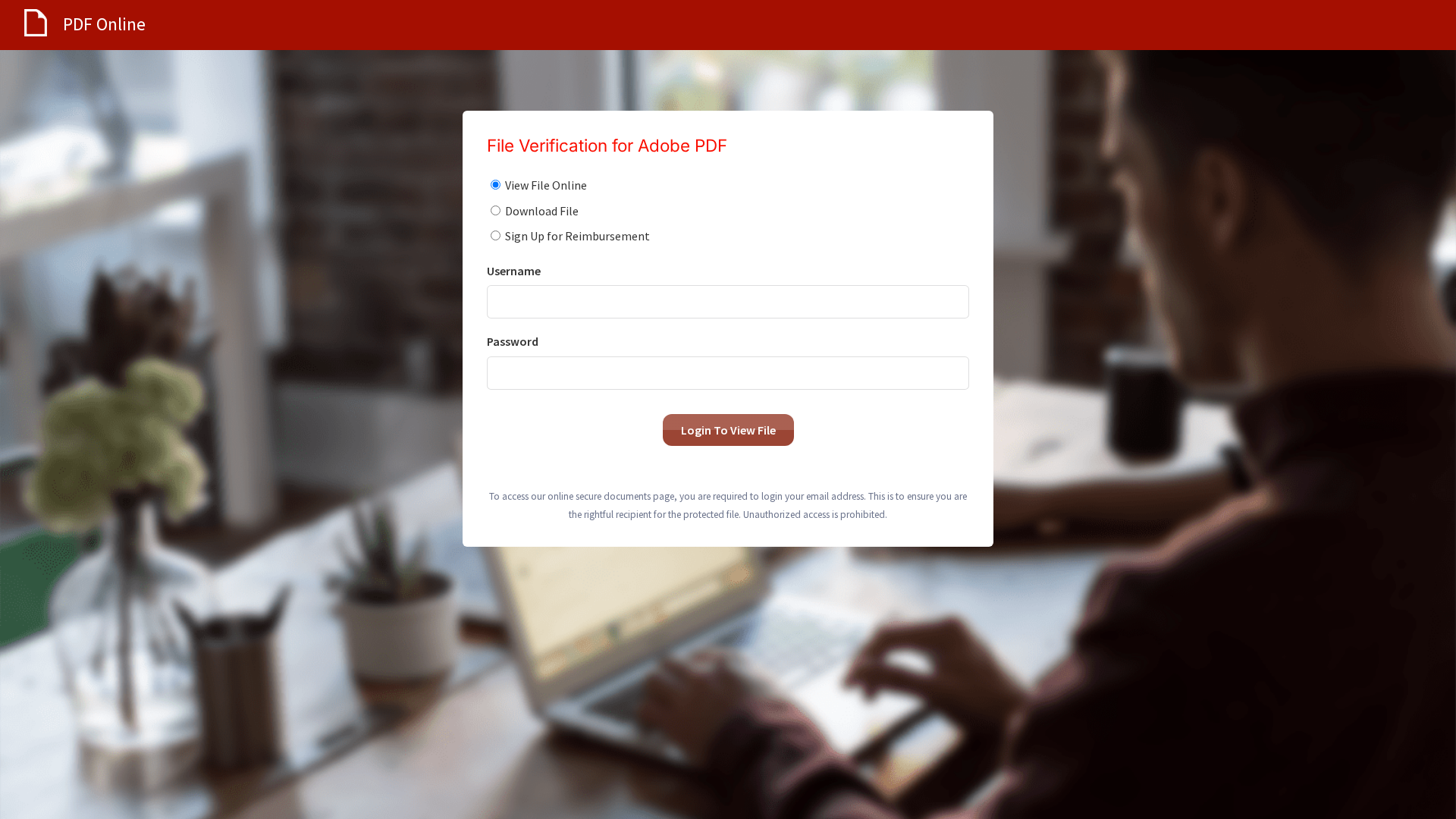
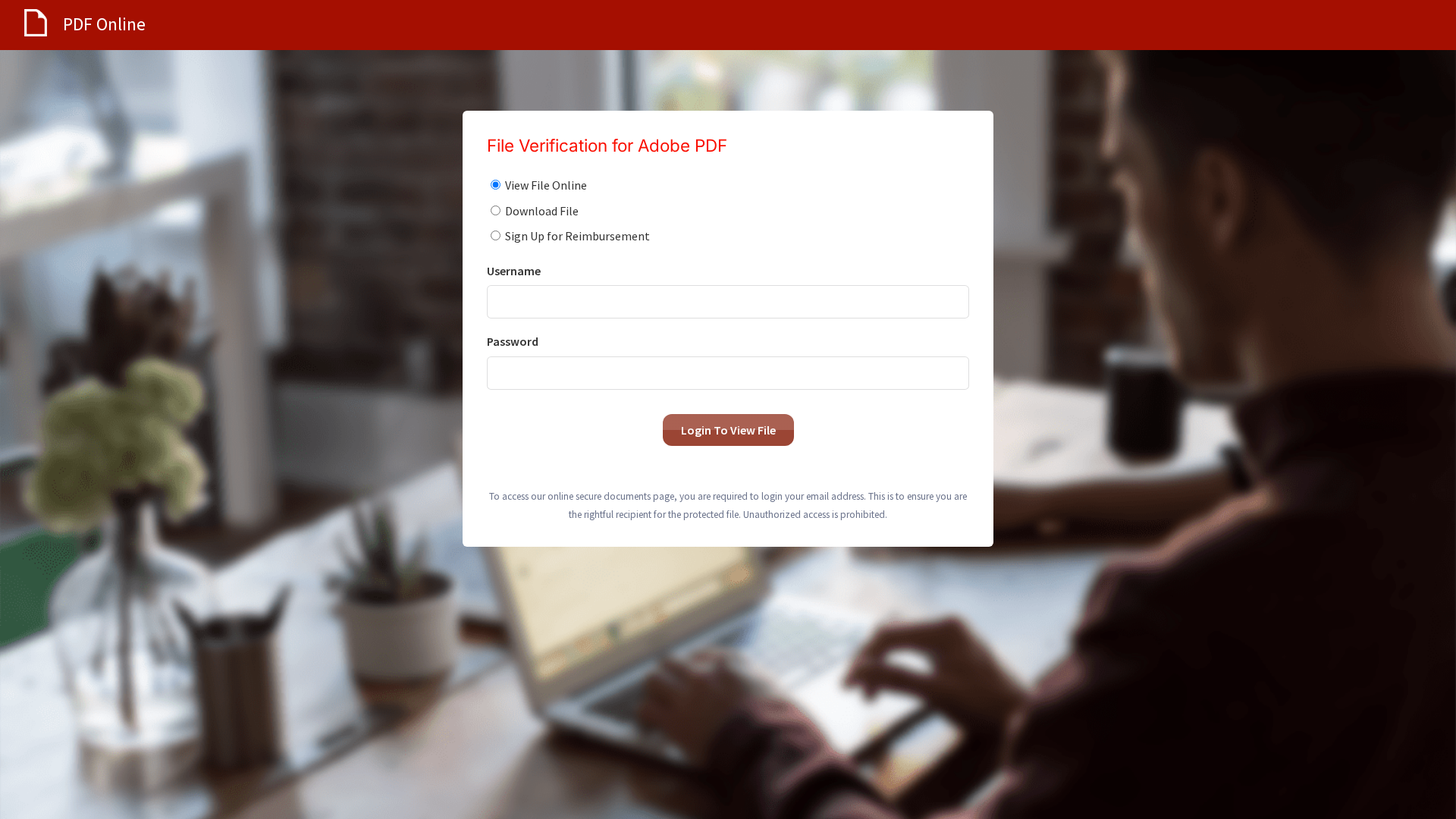
Visual Capture
Detection Info
http://mail.lucrativehiring.com/s/63BZGFSVBWSFCDX7Y9/584dd8/90eab167-7429-489f-99f6-ce86e8d0d81a
Detected Brand
Adobe PDF
Country
International
Confidence
100%
HTTP Status
200
Report ID
0dd971b5-e2f…
Analyzed
2026-03-17 01:22
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1A061543190459C7A6252D398B3D6FF0465CEC1A6C70A6800A3F4E3CDE7E7D10DEA6599 |
|
CONTENT
ssdeep
|
48:TICYWVBcWzcYRlUxv8Xhj1fvHgoaZ6pB+OTgl162phmzeVb8JoaTokg:T7JLREAhRfvHgoaZ6KOTg2ywSNqomokg |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
de9c73102738253f |
|
VISUAL
aHash
|
98bcbc3c3c7cf8a0 |
|
VISUAL
dHash
|
3038316868a02949 |
|
VISUAL
wHash
|
18bcbc3c3c7cf8a0 |
|
VISUAL
colorHash
|
0fc00018000 |
|
VISUAL
cropResistant
|
3cdcdc9909e9ddde,bc3438b6f4d43464,3038316868a02949,8b8b8383838387e7 |
Code Analysis
Risk Score
65/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Adobe PDF users
• Method: Credential harvesting
• Exfil: /site/submit
• Indicators: Domain mismatch, login form, impersonation
• Risk: HIGH
🔐 Credential Harvesting Forms
📤 Form Action Targets
- /site/submit
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Domain Mismatch
The domain doesn't match the brand.
Form with Credentials
The page has a login form requesting sensitive information (username and password).
Impersonation Attempt
The page tries to impersonate Adobe to steal login details.
🔬 Comprehensive Threat Analysis
Threat Type
Credential Harvesting Kit
Target
Adobe PDF users (International)
Attack Method
Brand impersonation + credential harvesting forms
Exfiltration Channel
HTTP POST to backend
Risk Assessment
HIGH - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Personal Info
🏢 Brand Impersonation Analysis
Impersonated Brand
Adobe PDF
Official Website
null
Fake Service
Document verification
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker sets up a fake login page to collect users' credentials. The victim enters their username and password, which the attacker then captures and can use to access the legitimate account.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
mail.lucrativehiring.com
Registered
2015-11-13 17:25:18+00:00
Registrar
None
Status
None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Adobe
http://webaccess-alert.net/s/63BZGFSVBWSFCDX7Y9/584dd8/90eab...
Apr 07, 2026
Adobe
http://pilot.webaccess-alert.com/s/63BZGFSVBWSFCDX7Y9/584dd8...
Apr 06, 2026
Adobe
http://negative-report.com/s/63BZGFSVBWSFCDX7Y9/584dd8/90eab...
Apr 06, 2026
Adobe
http://reply.mycircleonline.com/s/63BZGFSVBWSFCDX7Y9/584dd8/...
Apr 06, 2026
Adobe
http://federalnewsmagazine.com/s/63BZGFSVBWSFCDX7Y9/584dd8/9...
Apr 06, 2026
Scan History for mail.lucrativehiring.com
Found 5 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.