Phishing Analysis
Detailed analysis of captured phishing page
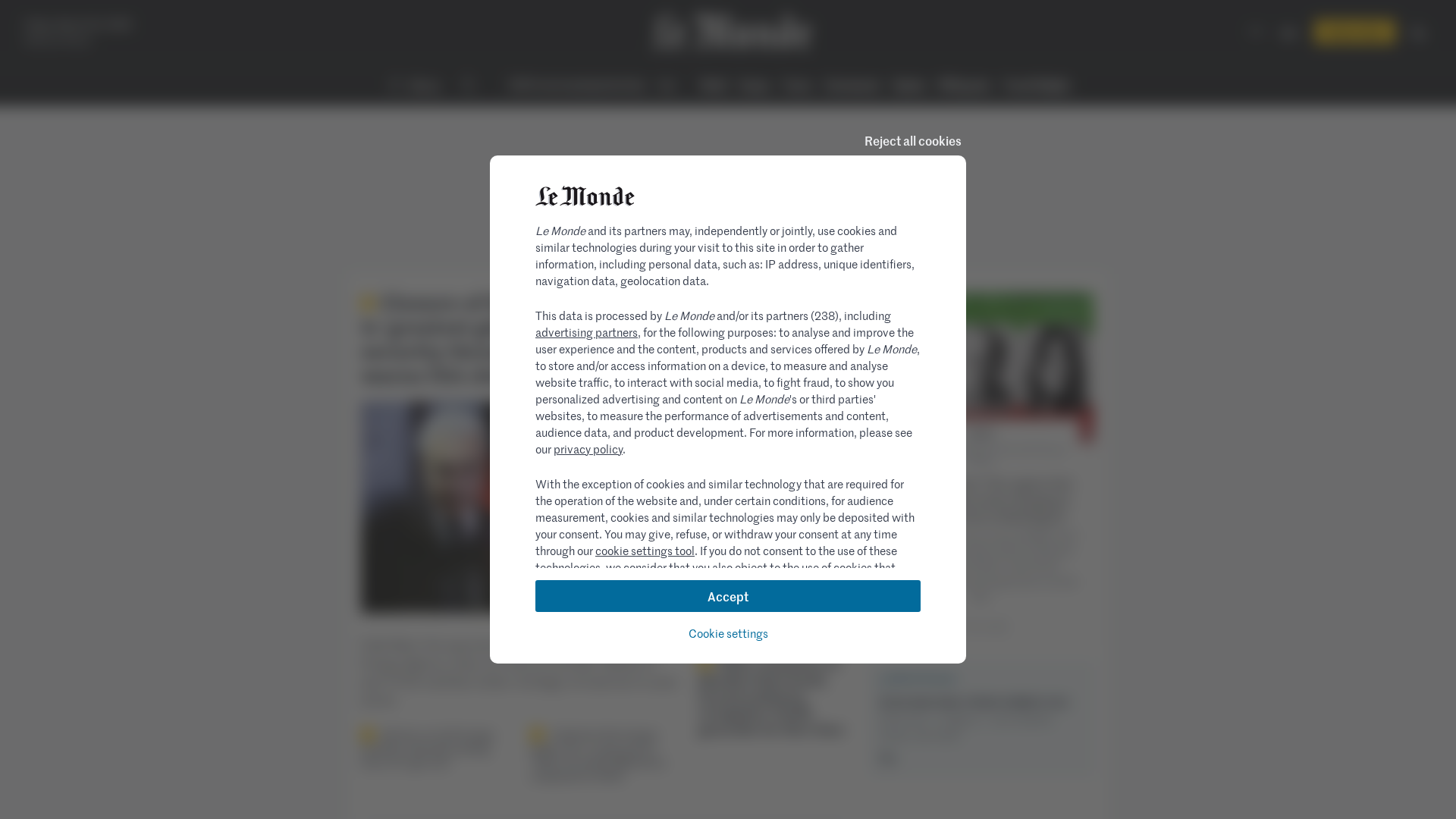
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T15A04B7E1A0806B7F425F83C59BB1FFDCB2EA105EEA950856C3E8839452D3CD4EEA7544 |
|
CONTENT
ssdeep
|
1536:CaohanNLqfej64BraX42u5Iaa4MtNJktpjHK2lK2qzvaa6Cv9VYDxMYdS1IB6ZBY:Caohans3NObHK2lK2qHeBUBUB7ByBS |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9849673465671cdd |
|
VISUAL
aHash
|
001c3c3c3c1c3c00 |
|
VISUAL
dHash
|
1771717331396914 |
|
VISUAL
wHash
|
003c7c3c3c1e7e4e |
|
VISUAL
colorHash
|
072000001c0 |
|
VISUAL
cropResistant
|
62329a22b2aa332b,1771717331396914 |
Code Analysis
🔒 Obfuscation Detected
- atob
- fromCharCode
- base64_strings
🎯 Kit Endpoints
- https://www.lemonde.fr/actualite-medias/article/2010/11/03/la-charte-d-ethique-et-de-deontologie-du-groupe-le-monde_1434737_3236.html
📡 API Calls Detected
- POST
- /ajax/fetchLives
- GET
- https://cdn.amplitude.com/libs/amplitude-4.2.1-min.gz.js
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Personal Info
- 55 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 55 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for zorro.form11420.pro
Found 3 other scans for this domain