
Phishing Analysis
Detailed analysis of captured phishing page
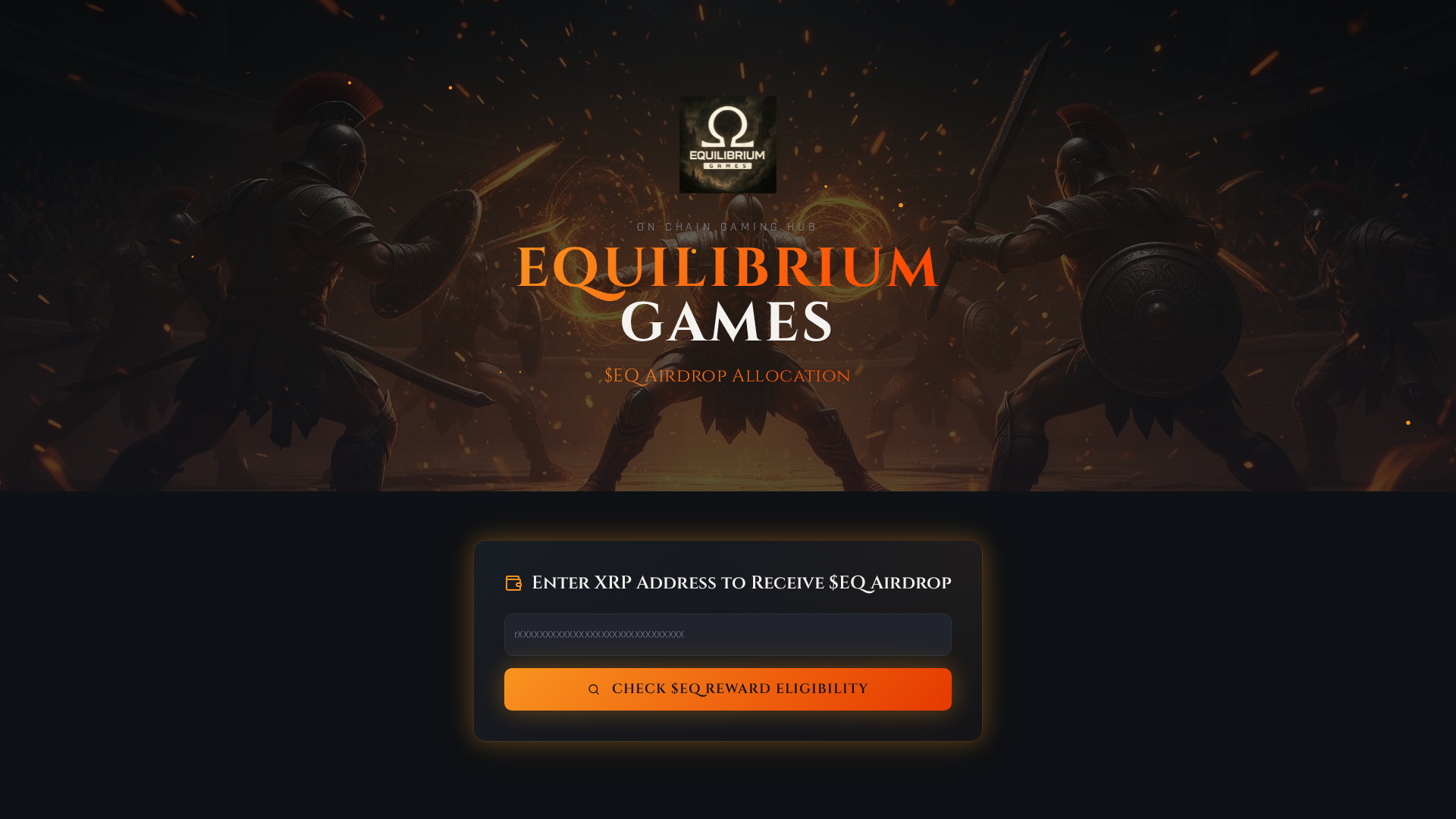
Visual Capture
Detection Info
https://equilibriumgames.info/
Detected Brand
Equilibrium Games
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
0f6f3883-7ca…
Analyzed
2026-04-08 08:37
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T19323A47512851F3ED013C6E4F6B1B7285379869DDBF74899EA5E03A3C78BD88D623280 |
|
CONTENT
ssdeep
|
768:fPnBI91byQxup5KwfPC8eNQNM26kaNcFD+6/XIid:BIlkgcx+6/Xd |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cc31643333ce33ce |
|
VISUAL
aHash
|
00183c3c3c183c18 |
|
VISUAL
dHash
|
f0f0f071f1716160 |
|
VISUAL
wHash
|
003c3ebdff3c3c10 |
|
VISUAL
colorHash
|
30c00008000 |
|
VISUAL
cropResistant
|
f0f0f071f1716160 |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔒 Obfuscation Detected
- atob
- unescape
- js_packer
🎯 Kit Endpoints
- data:image/jpeg;base64,/9j/4AAQSkZJRgABAQAAAQABAAD/2wBDAAgGBgcGBQgHBwcJCQgKDBQNDAsLDBkSEw8UHRofHh0aHBwgJC4nICIsIxwcKDcpLDAxNDQ0Hyc5PTgyPC4zNDL/2wBDAQkJCQwLDBgNDRgyIRwhMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjIyMjL/wAARCAQ4B4ADASIAAhEBAxEB/8QAHwAAAQUBAQEBAQEAAAAAAAAAAAECAwQFBgcICQoL/8QAtRAAAgEDAwIEAwUFBAQAAAF9AQIDAAQRBRIhMUEGE1FhByJxFDKBkaEII0KxwRVS0fAkM2JyggkKFhcYGRolJicoKSo0NTY3ODk6Q0RFRkdISUpTVFVWV1hZWmNkZWZnaGlqc3R1dnd4eXqDhIWGh4iJipKTlJWWl5iZmqKjpKWmp6ipqrKztLW2t7i5usLDxMXGx8jJytLT1NXW19jZ2uHi4+Tl5ufo6erx8vP09fb3+Pn6/8QAHwEAAwEBAQEBAQEBAQAAAAAAAAECAwQFBgcICQoL/8QAtREAAgECBAQDBAcFBAQAAQJ3AAECAxEEBSExBhJBUQdhcRMiMoEIFEKRobHBCSMzUvAVYnLRChYkNOEl8RcYGRomJygpKjU2Nzg5OkNERUZHSElKU1RVVldYWVpjZGVmZ2hpanN0dXZ3eHl6goOEhYaHiImKkpOUlZaXmJmaoqOkpaanqKmqsrO0tba3uLm6wsPExcbHyMnK0tPU1dbX2Nna4uPk5ebn6Onq8vP09fb3+Pn6/9oADAMBAAIRAxEAPwDwKiiimAUUUUAFLSUtABRRRQAUUUUAFFFFABS0lFAC0UUUCCiiigApaSloAKKKKAFzSgjFJRQA4UuM00N60vXpQAuMUgpeaXPqKAE96KUik60AIaU9KKD2oAKOD1pe+KBz1oATB7UoPrQAR0oyD1oAXg0bfSk2ntQCRQAdKKdw1BX8aAEooooEFFFFAwpaKKACiiloEFFFLQAUUUUALRRRQMWiiigApaSloAKKKWgQUUUUALRRRQAtFFFAwpaXcNmMc+tJQAZooooEFLSUtABRRRQAUtJRQAtFFFABS0lFAC0YopRQMMUU5VJOB1pWRlOGBBpXHyu1xlLRRTELSikpRQAopwpopRSAcKcKaKdQAtLSUtADhSim04UAOpRTRTqAHClFNpwoAcKcKaO1OHtSGOFOFNHP1pelADweacDTKcKAHg04UwU4UgHilpo64pw5oAdS00c0ZoAdRSUUALRRRQAUUlFAC8UUlFABSGikNAAetNNKaQ0ANNIaU0hpgJSGlpKAEpKWkoAQ000tIaBCGmmlNIaAGmmmnHrTTTAaaaacaSgBppppaQ0ANNNNONNNADTSGnGmmmIbSU6kNADaKWkoGJSUtFAhKSlooASiiigApKWkoAKKKKACiiigYUqqWIAGSegpK3fDNgt1fmeX/VQfMc9z2rKrNQi5M1o03Umoo1VjHh/w6zNxczDP4npXGsSxJPJPWtrxHqZvr4oh/dRcD3NYhrLDQajzS3Zvi6icuSOyG0UtJXUcQUlFFABSUtJQAUlLSUAFJS0UDEpMUtJQISilpKAEooooASkpaKBiUlLRQAlFLSUAJRS0UAJRRRQAUlLRQAlFFFACUUtGKAEoxTsUmfSgAxSZz0oAJpeBQAmKKOT7UnvQAtBpaO1IBtOxxmkpe1AxMYpKOppaAEFLRSGgQUUmaKYBRRRQAUUUUAFFHeigAooooASiiigAooooASiiigAooooGFFFFABRRRQAUUUUCCiiigYUUUUAFFFFIBKKKKYBRRRQAtFFFABRRRQAUUUUAFFFFABRRRQAtFJS0AFFFFAhaKKKACiiigBaKSjNAC0UUUAKD2NOz09KZS5oAePajr2pufSlBzQAuOaP4qKX3oASgdSKWkPr3oAXpQADmg0gNAC7SOlGQeDxRk9xSnBBoATb6UAkUL96n8HigBNwPWgr6UhX0pORQAuCO1FODjuKXaG6UAMopSpFJQIWiiigApaKKAClpKWgAoopaACiiloAKKKKACloooAKKKKAFooooAWiiigBaKSloAKKKKAClpKWgAooooAKWiigAooooAKKKWgApRSUopDLNk6x3cTuAVDDIPpW14ks44jDPEoCOMHHrXPqcVvX2owXegwxs+Z1wCPpXLVUlUjJHfQlF0ZQZgUlLSV1HAxaWkpaYCinU0U8UhoUCnYqzZ2M16+yFNxFFzZzWcpjmQq1Z+0jflvqa+xny89tCtS0YorQyYtOFNpc80CHCnCminUALThTRThQA6lFNFOpAOHFOzk5NNFOwR260DHCnUwU4UAPHWlFNpRSAePWnZxzTBS0APBxS02lzQAvWikzS5oAWikooAWikooAXrSUmaKAFpDRSUAFNNLmmmgBKSlpKYCGkPWlpKAEo5PSg0K200AN6UhpzEFsgU2gQ00hpxphoAQ9aYacaTGaAGmmmnGmmmA2kNLSGgBppDSmkNADTTTTqQ0xDaSlNJQAlJSmkoASiiigBKKKKAEopaSgApKWigBKKKKACiiigAq3bahPaQyRwvtEnWqlJUyipKzLjNxd4ik5OaaaWkqkS3cKSlpKBCUUtJQAUUUUAJQaXrSHrQAUlLSUAJSU6koASkpaSgApKWigBKSlooASkpaKAEopaSgYlFLSUAFFFFACUUUuCaAEowTTto70Fh2oATbjrSE+lHJowAeaAEwTRgClNGKAEyaTFL3oxlqAADvR2o+lH1pAA6UtIOtLQMaetKF4zQaKACko7UnWgAJpKMUtMQlLRSUDCiiigQUUUUAFJS0lABRRRQAUUUUAFFFFACUUUUAFFLSUAFFFFAwooooAKKKKACiiigAooooAKKKKAEooooAKKKKAFopKWgAooooAKKKKACiiigAooooAKKKWgApRSVNbsiTxtIu5AwLD1FJuyGld2IqK7jVPDlrqemrqOjBc7ctGvf/69cSylWKsCCOoNZUq0aq0Na1CVJ67DaKKK2MAoopaAEpc0UUAFLSUZoAWjNFFAC5p+ajpc4oAkoxxTQw704dKADB6UAdKWikAnAoPSlxx0pD0oAEHNOpF70tACHINGfWl7mkJ7UwDHpSYIp23ikz7UAKHI680uFbpxTetFAC7SKSnBiOtOyG9KAGUU8p6U3BHUUCCiiigApaSloAKWkpaACiiigBaKKKAClpKWgAooooAWiiigAooooAWiiigAooooAWijtRQAUUUUALRRRQAUtJRQAtLSUUDFp2abS0h3FopKKBC0tJS0wFFPWmCnipY0dd4LKG5uIyBuKgitDxZZB7JZ1XmM4JHoa5rw5d/ZNYgcnCsdjfQ16DqMAubGaI87kI/HtXi4luniVI+jwqVXCuB5WRzSVJKpVyp6g4qOvZi7o+fmrOwClFAxnmjvx0qjMcKWkHSlFADqWmjmnCgB1OFMFOBpAPXqKlYjbjNQinDtQMdSiminDrQA7oaWm0tADxS03NLmkA/OTS00GgHNADs0UmeaU9qAClzmm0UAOzR2ptFADqSkzRQAtJRmkzQAU00ppDQAGmnilNIetMBKQ0tJ2oEJRRSUAIaDRSUAIetNNOPWmmgBtOVwvWm5xTTTAWQgniozSmkNADaaacaQ0ANNIaWkNADaSlNIaYhppKcaaaAEpKWkoGOiUPKqsQoJ5J7UtwsazMIjlB0qOilbW476WCkpaSmSFFFFACUUUUAFJS0lABRS0hoAKSlpKACkpaSgApKWkoAKSlpKACiiigApKWkoAKSlpKACkpaSgBKKWkoASilpKAEopaKAEpKWigBKKKKAEopQpPSnbfU0DI6dtNLkDoKQkmgAwBSFvSgL60uAOtADcE0YA96dkHpSHmkAmfSj60oGaQ9aAEo9qX3pKAFPWk96XFGKAEFLiiigA70hpaaT7UDEozxSUUCCiiigBKKKKYBRRRQAUUUUAFFFFACUUUUAFFFFABRRRQAUUUUAJS0UUAFJS0UAJRRRQMKKKKACiiigAooooAKKKKACiiigBKKKKACilooAKKKKACiiigAooooAKKKKACiiigApaSloAKUUlFAG1oPiC40S53p88LH95EehHt70eJL6w1HUftVjGyB1y4YY+asaisfYx5+dbm3t5un7N7BRRRWxgFLSUtABRRRQAUUUUAFLRRQAUtJRQAtAOKKKAHBs9adTKKAJc+tHXrUe6ng5pAKBjpQKM+1KDigBAcGjvml60YpgIPmOe1OyOlNA/wD1UY55/KgAIwc0pHFHUYPagcrQAmPWjHPFOowAMmgBAxX/AOvTg4PWm7uc44o4PtQA/CmjYexpm00oYj3oAMEdqKcH9RTvlb0oAjpaeYx2P50hRh2oAbRRRQAtFFFAgpaSloGFFFFAhaKKKACiiigApaSigBaOpoooAKWkpaACiiigApaSigBaKKKAFooooAWiiigBaWkooGLS0lKKAFFOFNpRSAmRypBBwR0NdevikPp6oeJdu0n+tcYOtOBNc9XDxqW5uh10MXOimo9SeeTzJnb1OaipM0tbpWVjmlJyd2LS02nCmSLS0gpwoAWlpKWgB1KKbTs0AOFOFNFKKQDqcKaDSigY6lFIKWgBRTs00UdKAH+1L34ptFADs8Uuabml6UgFo70lFADqSrOnoj6hbpIMo0ihh7Zq/wCJdPTTtWaOMYjdQ6is3USmoGqpN03Mx6KKStDIWkNFJQAHpQaM0lMBKGOTRSfzoASkpWBU/MMUhoEBpKKSgANIe1KMd6QnmgBppppxpppgNNNpx6000AIaSlNNNACUhpaQ0ANPWkNLSUANpDTqaaAG0lONIaYhtJTqQ0DEpKWkoAKSl7UUAJRRRQIKSlpKACkpaKAEooooAKSlpKACkpaSgApKWtDR9Mk1XUI7ZMhTy7egqZSUVdlwg5yUUZxpK09cgtLbVJYLPPlx4UknOT3rNohLmipBUhyScRKKKKogKSlooASiikoAKKKKAEooooASilpKAEopaNpoAbRjNP2gdaCwFAxu096XCikyxo2+tAAW9KTBPWnYpCeeBSAMAUm70oxnrRjFACcmkxTsFcGgjvQAgHWilFLQAwcUcUoHJpcY6UANx+FGKdSUAJRiikJoAKQnH1pCc0UABOaTFLSUAGKKKSmAUUUUAFFFFACUUtJQAUUUUAFFBxng5pKACiiigAooooAKKKKACiiigAooooAKKKKACiiigApKWigYlFFFABRRRQAUUUUAFFFFACUtFFABRRRQAUUUUAFFFFABRRRQAUUUUAFFFLQAUUUUCCiiigApaKKACiiigApaSloAKKKKACloooAKKKKACiiloAKKKKAFooooAWiiigBQSKcH7UyloAkBHQ0vHrUVLmgCXHoQaTHbHSmjBp3P1pAGKQcNTqCAev50AJj5sfjQeTilwccc0g4NADgMcHpTSATxSjOSKAPXtQAL82QaBmlTrmk75NMA47jFG30pcn0pD1yOKQACwp4c4PtTM4PNPIHWgBd6nr+tG1T0pmB60YIoAdsPbmkwR2oDMKcJPamA00U/5SKDH6H86AGUU7YfSkoEFFFFABRRRQAUUUtABRRRQAUtJS0AFFFFABRS0UAFFFLQAUUUtABRRS0hhT1jZlJCkgdSO1Jir2lXCwXYSTHlSjY+amcmldGkIpysyjRVvULM2d20Y+4eVPqKqU4yUldEzi4tpi0tIKWqJHClpopwpALS0lLQAtLSUtADhS00U4UAKKcKbS0AOFKKSloAcKUU0dacKQDqcKYKWgCRTznFOdw7ZAA+lR0ZoAdTqZ3pc0DHA0uc0gBY4AJqQR/3jj2FADc04BmPAJp6hVHCj6mnFj03H8KQEexx/CcUnsakyVXHrTgQRhgMUAJCxjmjcdVYH9a6rxxHuawuMffjIz+tc9ZWTX15HbQY8yRtq5PFdn40sWj8O2jucvC6oSPpj+lefXmlXgejQg3QmefGig9aSvQR5zCikopgFJmjNJmgAoB2sD6UZxTetADnbexNMpTkHmk5oEBHGcj6UlFBGD1oASkNLTT1oAQmkNBpDTAQ000p60hoAQ000ppKAEpppaQ0AJSUtJQA+KFpn2r1pJ4Wgfa3WnQTmCTeKLmczvuPA9Kj3ubyNrQ5PMr0lKaQ1ZiJSUppKYCUUUUAJRRRQAlFFFAgpKWkoADRQaKAEo60tJQAUlLSUAFJS0lAwrq9IvLbRvDVxdpIhvZyURQeVrlKM1lVpe0VnsbUa3sm5JaisxZizHJJySabRRWiVjFu+olFLRTEJSUtFACUUU5VLsAKBjKKc2MkDpRtJ7UANpKk2Y60hIXpQA3aTS7R60m4npRtJ60AGQKQsT0pdoHWjIHQUAN2k9aXAFHJ9qTGB70AG70FAyTk0o6e9Gc9aQCnqKYw+annoKY/Y0AGMUnXJ7UvbpR2oAOtJ0OOtLjPWnYoGNA59qXFWbW1a6k2LTryzezYBsc1HOr8pp7KXLzdCnSUpPrTC1WZi9aQtSHJpMUCA80YopaAExSUtJTAKSlooASiiigBKKWkoAKKKKACkpaSgAooooAKKKKACkpaKAEopaSgAooooAKKKKACiiigAooooAKKKKACiiigApKWigBKKKKBhRRRQAUUUUAFFFFABRRRQIKKKKBhRRRQAUUUUAFFFFAC0UUUCCiiigApaSloAKKKKACiiloAKKKKAClpKWgAooooAKKKKAFooooAKWiigAooooAWiiigAoopaACiiigAzTgSKSigB4b8KdmoqKAJR7UvsRUYY5pwf1pAOIHanH7uKbuBpaABRhTmhPWlPTFGBj3oAN2Gx2PrSMMc0pXIx+tIDggNQA3jb71IelNIAI96caAGgDGeuaUqRyKXhuDxSfMvuKAEz6ijg+1L15x07Urcj0oATaaBuHenjnFNxkHmgADkdaXeCORQMHqRQUxyKAHYQ0hT0NMxS4YcjNMBdhpMYpQ7d6XzPUUAMpaflD2FLtU9DQIjop/l88Gk8tqAG0tLtYdQaSgApaSloAKKKKACloooAKWiigBatWFt9svYbcEL5jhcntVWnKxUggkEcgjtUSTa0NINKSbOs1zwnFpmntdRXDNsxlWFcpV+61rULy1FvcXLSRDsaz81jQhUjG1R3Z0YipTlK9NWLVxfS3VvFFIAfL6N3NVqSl71vGKirI5pScndhS0EYOKO9USLS0lLQAtLSUtIBRTqaKUUAOFOA4zQFx1pxbbQAuzjIpKUNuOc4NSHDYBHNAEYpacUIGQcim0AOpRTaUUAOpwpgpfekA8UA03NOUFmwO9AxwBJwOtS+Vt4Y/MR0FAAj6cn1oJPU9KQDgeg9BjijOPemFh2ppc5yBQBLknvgUd85NRg7jk8/WjOCCelAEgfPBOTQCQc0zIZuO1AIJ4IoAt2t5JaXMdxE22SNgymtrWPFN1rNqlvLHGkSncQn8R9a5zn2ozjnp9KylRhKSm1qjaNecYuKejJCit0ODUbKy8kcetL5gJ5H4irEbJsIOM9OetamJUzSVYkgU/dO09h2NV3VkbDDBpgGaSkzRQIKKSkoAU8mkoPWkoAKKDSUAFJRQQcZIOPWgBppppTTTTADTaU0hoASkNFJQAlIaWkNACUlFJQAlJSmkoGJRS0YoAbSU7FNNAC7P3ZfPfAFMpaShCYlFHaimAlFLSUAFJS0lAgooooADSUtJQAUUopD1oHYSkpaKBCUUUUAJRS0UAJRSgH0pdpoAbSU8KKXAFAyPBNTphIm/vtx9BUZcU0ufSk1cadh2AKaXpvJ6mlAH40xCctQF9aXkn0oAwwzzQAvTpTeScU+mHhqQCbe5NG3uKUjnH5mjGKYCdKQjnmlz69KMZPFIA44pCBnOaXGaXHegBP4RSMOKdinxRNNIsaDLE0m7ajSbdkQgcUuMVavoI7aQRI+5gPm9jVTdQndXKlHldmLmlHJx3pm6gMR0oEi7a3jWL7lAJ96hvL6W8k3ufwqseaKlU1fm6lurJx5eglGKKKszEopaSgQUUUUwEooooASilpKQBRRRQAlFFKFLdBQNIbRSkFTg0lMBKKWkoEFFLRQAlFFFABRRRQAUUUUAFJS0UAJRRRQAUUUUAFFFFABRRRQAUUUUAFFFFABSUtJQMKKKKACiiigAooooAKKKKACiiigAooooAKKKKACiiigBaKKKBBRRRQAtFJS0AFFFFAC0UlLQAUUUUAFLRRQAUUd6KAClpKWgQUUUUDFooooAKKKO1AhaKKKBhS0lKKACilpKAFopKXoaAClpKKAFooooAWlBI6GkooAeHPenBwf/r1HRSAmo68YqEHFODn60APwM0uD0pocdxTgR60AJhh2GRS8+vFLzRjPWgBCMcjr3oJBXNKBSbeRzQA7pSL6Up5GKQr0weaAArz7UgyBkU7rRnAwaAEOM+9KxxjA+ppMfPStgsBQAmM80mKcaQevvQAmPejBFKcg8UfhkUAKGYUvmHHSgKD26UbSelADhL6inb1PWotpJPtQVxQBJhT6UbBn2qLFKMjnNAD9noaTYw7Ub2pwk9qAG4PpRTxIvpTtyn0NMCKnEDGR2p+1SOn5UbVz/8AXpAR0U/y+OvNJsb0oASlowfQ0UAFFFLQAUtJS0wFpabS0ALS0DkinjA6DJ96QAqk+wqQDHA/Om5xyaQkmgBxOOlJSUtABT1kI68imhTjpRQBZViBxyKUqsnK8GqysVOc1Or56HBpANIIOCKKlDAjaw49aa0ZHK9PSgBo7UuaaKeFP8XFADkUs2B+NSAgcCkPyjaMDHX3pCcUDHM2OtNLZIpvU5JoZwp9D6CgB4POeSfegSKn3sH2FQlmY4HT2pdnHUZoESM7ZBTgHvSFX6lufrSxlcFG/I/0pHhZTlTuH8qAJouZCRimyxkjeuODyB2p0Rw7fSmqNg3SH8KBjNzrznNOEoPUYpscZZiei0+VVygXrjv6UCHghueDQv1A5qEoVOVbkUqzYPzj8aAJ95IAzz9al3hgFcArUAIODx9aUNgjNIY2SIqSU+ZPWoquK+SAenc96jngx8yHPfFO4FfNJRRQIKKTNFABmgAscCnKhbk8Cn8Kp6ACgYgUJywyf0FJvwcHkd/ao3kJyBwKYCR04NAh7pj5l5H8qiJqRZADzwfWhkDDK8H09aYEJpDSnIODTaACkopKACmmlzSUAJSUppKAEoopRSGhMVPbWc95L5dvG0j4zgCowM13/gXTNtvJeOvMh2r9BXNisR7GnzHZhMN7adnscDPbyW8hjlQo46g1Aa6XxjKkuuyhAMIApx61zZ61pQqOpBSfUzxFJU6jiugyilNJWxzCUlWbK0e9u47dDgseT6Co7iMQ3EkatuCMVz60uZX5SuR8vN0IqSlpKokSilooASilwfSjaaAEpKdtPrS7PegBopKftFBAB7UgGUY9qcSPaguM/wD1qYDdppdppN/1pN3tQA7aAOcUZA9Kbz6YpOe9ADi1Jv56UgWjGOtIAyTSYJ607r0pMYNMBNoFGARkU4j+dIB82O1IBB2oPtSgZBBpPrTAKOn4Uv3uaQikAp64prdRTu9NIzQAmcHPWjBJz0p2MUdKAE29KOlIWFNLGgB9IWAphJNJg0AO3elaMc8dhaZQhrmQdf7orMxRiplHmNIT5NVuKxLsSTknrTcUtFURuJRW7o2ixzwvqOosYdPh5J7yH0FZN7NFcXkssEIhiLfIi/wjtWcailJxXQ1lScIKUupXooorQxEopaSgAooooASiiimAUlFFABSUtJQAUUU5VLMBSY0rj4YTK4AGavPCtvDlqmto0t4fMfFZ13cmeT/ZHQVz3c5WWx28saULvdldzuYmm0tJXQjibuwooopiCiiigAopKWgApKWkoAKKWkoAKKKKACkpaKACkpaKACkpaKAEooooGFFFFACUtFFABRRRQAlFLRSASiiigBaSlopgJRRRQAUUUUAFFFFABRRS0AJS0UUCCiiigAooooAKWiigAooooAWnMjL1HWm1s6bFFqNu1s+BIo+U1E58iua0qfO+XqY1FT3NtJaztFIMMv61DVJpq6M5JxdmFFFFMQUUUtABRRRQIKKKKACloooAKKKKBi0UUUAFLSUUALk0UUUAFFFFAC0UUd6AFzRSUtAC0UlLmgBaKKWgBKXtRRQAUUUUgFGfWl3GkooAeH55FODA1FS0ATUuPaoR1rsdK8GSan4Vl1eG7UyoWxDjsvXJ9ayq1o0knI2pUZVW1E5QDFIelGctjHNGcHB4rRGTVhAMN7UrDLf1oyKXIpiG7Qe9KVz9KdgUmKAGg4PT60dxxxT9uRTcEMM9KAFzgYpcADnqaOjA9jSMG3ZxmgAYYwR1FLwwyOopBk7jj6UD5cHsaAFB4oIAGaMfNntS9X56CgAC46mlII5AyKb1Ofwp/QD60ANAVucUYTsaDwdw6elKqgvnt1oATZ6Glw/rSEDdx605uOh/CgBMt6Uoc+lADHBxSnPdaADzPalDim8HtTggZcjr6UALlfalwvtUYA9KUJkcUASbFPT+dJ5fvQYWAUkEA9CR1pNpHQ0XG1YXZ70m0jmlw/rSEmgQq/eFP6A0wDkYqTtQAgBPPWnbfU4oGM+h9qcCFOCBQABVPelC89aPlJwR+VL5QI4b8DQAoB9aaVy3NNZGTqKQAk+9ADyhGKNrDtSYb3oy/fNAEiv/AHqkVwOCM1X3HvSqxxSAsHHWl+6wJ69ajA3MeeB3p5IJBPpQMXd0oHvTO/tQxwoGeTQAM/ZfzpApNKowvOMGlBoAdwAPSlyFJB/lmmDk4p+Mntn1oAaV3DC885zUieYvUgj600yIvUn6CozPxgLx9aAJ1bcN3Qd6QEs+dv51GsvygEc0MxxuRhx1BoEStJJj5VApq4PLn5j60xZyOq/iKeGjfgnB9aAHcqcjBHvSuBJjt/Soyjr05HtSq+fTHpQA35om7H+RqVWEgyOPamEDGO1MwyMCPWgCycpt3YOR2NOLkY5z7VEjh16c0pwBz/OgY2QBjuAxUdS8c4qMgHvQITmnhcHJ5P6Ug44FIxJ4BA96Bjmk257moS2eppSreopNuetADetHGMmnED14puBnGaBCYyccUK5Xg8ijaf71IVPrQBL8sg6GojGexpBuUfKaCz+1MBnekp23LfNQVyetADKSn7fek2j1oAaoy1OOAelGQOKQsKQxrcmgClyM5pykZpNlRVyxaWz3NzHCgyzsFGK9gggh0jRecKkMePyHNcV4D0z7VqbXTrlIBwf9o10Hj3UBaaSlohw8xwfp3rwcbN1q8aKPoMJFUaLmzzO/na6u5Z26yMWqkRUzvk1EWNe5BcqSPCqy5pNjNppNppSTTTmtDIntriS0lMkTAMVK5x61CQCSS2Sec0nPpSc+lKyvcfM2rC/LRx6UmDRtPc0yRcj2pNw9aTaPWpre2a5uI4Ixl5GCik2krsaTbsiHeKNx9K1fEGn22lal9jt3ZzHGvmlufmPWsrJPoKUJKcVJFTg4ScWGW9KQ7vXFOxwPekaqIG4PdqNq+tOwMe/vSY3HPQUAJgDtR8vpT/lz04+tNfgigBCw7LQATyfwpeGPTignPAoAac5wBQw4BpcbaTqhoAU4603q3NKD8poHA6UAB57Unf6UvNGD3oATvSc7smnYA7UUANwc5oK96XIpu4UALilpm+k3E96AH5Appam0YpgBY0hOe9GKXFADaOlLRQAlFFFIApKWigArY0TSI7vfeXr+TYQ8yOf4v9kVjVZmvrie3jt3f9zH91BwPrWdRSkrR0NqUoRfNJXLuua22qSrDCvk2MPEMI6fU+9ZFLSVUIKCsialSVSXNISiiiqMwpKDSUALSUUUwCkpaSgAooooAKSlooAKmgIU5NQ0Z4qWrlxlyu5YublpcIOEHaq1FJRGKSsgnNyd2FJS0VRAlFFFABRRRQAUUUUAFFFFABRRRQAlFLSUAFFFFABRRRQAUUUUAFFFFACUUtJQMKKKKQBRRS0AJRS4p6wu3QUm0hqLexHRT2Qr1plNMGrbhRRRTEJRS0UAJRS0UAJRS0UAFFFFAgooooAKKKKAClpKWgAooooAKWkpaACp7W5e1uFljOCpqClpNJqzKjJxd0dZqUEOr6Ut5BjzUHzCuUIxxU1veT2wIikZVbqPWo5GDsWAxnrWNGDp+70N69SNW0lo+oyiiitzmFooooAKKKKBBRRRQMWiiigAoopaACiiigApaKKACiiigAooooELRRRQMWikpaAClpKWgAooooAXNLmkooAdRTaXNAC0UZpc0gCiil+tAADWpYa/qOm2NzZ2ly0cFyMSJjr9PSsuipnCM1aSuXCcoO8WL3zSEnPNLSVSJbCl3GkpaBChqdvFMooAlDClzniosZzRyDQBNmjqai3Gl3nGDQBJ/nmjAIxTA/tTt4NADgBijaccUgIxS0AIAQB60ozjBFGecZpc+1ACHHTFIvTrx3p2R6UEKRzmgBGGCMUp5x0pcetJtI9xQA5mIHH500c9Tz607+DFNBweRQAq9Dkd+Kch2uPfimhgKUd3NACgZY+maAcNSZGPQ0u4AcdaBnU2kC654SmtlA+2aefMj/2kPUVywQZ5JHpVzTtUudLuvPtWAYqVbPIIPrVWRizFj1JycVhThKEn2ZvVqRnGPcYVK4OeKVuMU4/6sfSmnnGa3OccOop56D60zril7igBc/zp2R+FJ1agEEcigB+ATjP0NKVKkGmlcLkc0qtxtYj8aAHrJ2/TtTSR5men0pGXYeuc0Zy+exoGSAg/X1FKJCDg/gai6NleKeGB4IApAOb5/wDGoh3p4JzjNNA+b8aAJRwPrSk8rSE89KQnLfhQAvQE0ijIyeSaRzyF/GnJ0OcYoAPT0oJwcCmswByKVeBk9aAH8KMmo2kLcdB6U1m3H2pKAFxSikozQIeqluAOetJmpYxsAJOC3SkkUffXoevtQA3jj0pCBzikzil70wFWRk75HpUhxJ86EZ7g1CenPWjBUgr1pAShucHinZ4OelMyJVyBhhQp3EZ4HvQAKfLcZ6dDUp5bBGBVd2yf0zUytlAfwNAx2QCO+fSkPWkBHA96QnrkUAMO4NkGjLkdaUnkUuMjOaBDMvSbm9qfTR940DGlmIp6ID97qTxTOpAqQfdLE47CgBCgDspHT0ppx2JoLF2PYHrQxG0CgQ0gjr+YppOTTs/KaZ2pgDdRTWBB5P60rHpTW60AHB9aMKPWkHbFKOSSaAD5ewzS89lpUALfjVqWKJI8q3zemahysaxg2rlMY9OakQDPFMIycipbYp9oi8z7m8bvpnmpm7K5VJJySPX/AAbpo0/QImYYkl/eN+PT9K8+8Y6n/aGuzbWzHF+7X8OtekapqkGn+G5biJ1IEWIyD1JHGK8Wlcu5YnJJyTXjZfTdSrKtI9nHVFTpqCIyajJ9qcSKYete6jwWJknsKTv2pT1xQ3HFMkQ59aTnpSgnPPSjvxQAmD680bT65pcDPWgkg8ZIoAZ3FdD4Wihjvp7+ZgEtIjIAe57VgHBBNKXYJgEgEcgHrWdWHPFxua0pqElJq5JcTvdXctxIcvIxYmoW7etLkkcCkwepq0rKyIk+Z3YqglenTmkYfKa0LZo4bCR2wZH4ArPPSlGV2ypQ5Un3EA3CkLY+XtS9gM0mAKozEYYApX6ClOOwpCc0AGcKABzSYPrzS8+tJ+VACjjvmkJ6470hNIW9qAHdqKZk0hz60wJCcd6aXFMooAUsfakJPrRjjNGKAEopcUUAJg0Y5paKQBikNLSUAJRRRTASiiigApKXNJmkAUUmaKACjNFJQMKSlpKYgpKKKACkpRSUAFFFFABRRRQAlFLSUAFFFFABSd6WkoAKSlpKACiiigBKKWkoAKKKKACiiigAooooAKKKKACiiigBKKWkoAKKKKBhRRRQAUUUUAFFFFABRRRSAKUDPFJVu2iBPNTJ2RcI8zsPtbMyEEirkwito+cfT1pHu47ZMKAW9Ky5p3mcsxzWCjKbu9jslKFKNluNlfexPao6KK6ErHC3d3CiiimIKKKKYBRRRQAUUUUCCiiigAooooAKWiigAooooAKKKWgBKWiigBVxnnpUjxFAGHKnoajqeCUIdrjKHrUu61RcbPRkFFWbi28v50O6M9x2qvQmmKUXF2YlLRRVEhRRRQAUUUUAFLSUtABRRS0AFFFLQAUUUUAFFFFABRR3ooAKWiigApaSloAKKKKACloooAKKKKAFooooAKKKWgAooooAKXNJ3ooAdmlptFIB1LTKXNADsUUmaXNABRRmlzQAlL1NFFABRRS0wEopaKQBS5I70lFADtzetKHNNooAdv8AanB6ZRigCTfSgioqKAJxxkDoRSZNRAkHNLk+tAEnJPantkY447VDuNPMpK470DQvfpS8dxTN9KHFAh2B2OKMZ6mkyvrS5HqKBiHPTNK3ajj1FGM96BDh1FOHUcUzoeacPzoAUcHP6mlIyaaBmlxzSGL8yHg8U4bX9j/Okxk9TRgDGD+YoAeEO0880gXPfFBA69z70DtQA7yz/eFIM9cUD9aPxoAXOBQvBGaaafn5jQA7vSDk/U0L1JoT7w+tADWOWYmlWQBcEDjvTD95gPWlVthzgE+9ACqMt9OaHOTtHQdaUcIW9aYFJGe1AC0Uqozk46j1pQnHzcH0oEOWIshbv2HrTUwWwTj60rSsQAOCO4obDrv6MOvvQMkG5wpzhl4/CnBgilThlxUaANh/bBxSMAqDnOTQA2pHieNVZhw36UijYnmEfN/DmnRSbyyOc55yaBEX1oqUQEnG4UjRbBklT+NAEYJQhh2p7kYyOhOaYcAinygfL06UDGVJGfvD8ajUZPt3pUP7ygC3IIxDCUOXIO6oT0NIDzQehpLQbdxCaCcAUrqUIBGO9NBwfWmJqwHIA9KByDQTkdaQHANACE80MeMUmelKBxk0AIPQfnRjBoLBf8KYST7UCFLACm8nPp3pcAY9aPemA054pG7ZpT6U09KADt0xS5yfakowaAHAge1KSemaYQc5zSdaVilIX8aAwpnvS8UrBcsNeTvAIXmcxr0QtwPwquxyevFJSZpKKWxUqkpbi0xu1KaQ88mrIFPPNJyaXpx/Ok79aBB1ODTaX8aCfegAxQR70lJn6UAKR70dsU3dSbqAH0maZuNGSe9ADyfekJFMzRQMduFBYU0CjFACl6TJoxSUCDmjFFFMBKKKKAEopaSgAooooAXPFNoooAKKKKACiikzQAGikJ4ozQAUUlJQAuaSiigAooooASlAzQK6nw1pEKxPq+o4W1h5UH+I1jVqqnG7N6FB1ZWRjXWkT2enx3VwRGZT8kZ+8R61m1p61qsur6g9w3CD5Y0/urWZTpc3Lee4q/Ip2hsJRRRWpiJRS0UAJRRRQAlFLRQAlFFFABSUtFACUUUUAFFFFACUUUUAJRS0lABRRRQAUlLRQAlFLRQAlFLSUAFFFFABRRRQAUUUUAFJS0UAFJRRQMKKKKQBRRRQAVcsNOmv5CEwsa8vI3RRRYWX2pyzuI4U5dz2FWb/AFNWhFnZKY7VevrIfU1nKTb5Ym0IRS5p7fmZ9wkcdw6RSeYinAbGM0glZRgGo6Ku3cz5tboUsScmm0UUybhRRRQAUUUtACUUtJQAUUUUwCiiigAoopaBCUUtFABRRRQAUUUtABRRRQAUUUtABRRSikMs21x5Z2uNyHqKdc2wUeZEd0Z/SoFQmp42eLjqp6is3o7o3jrG0irikqSQDcSvSmVomYNWYlFLRTEFFFFABRRRQAUtJS0AFLRRQAUUUUAFFFFABRRS0AFFFFABS0lLQAUoBPSkpyOUzjvQCEooPJzRQAUUUtABRTkwCdwzTaQWClpKWmAUUUUAFLRRQAUUUUAFFFFAC0UUUAFFFFAC0ZNBBB5FFIBc0uabRTAdmlptFADhRTaWkA7vTjg0ylzQMXFKBk0Y9KQUgsLikpelGcmmAUUdDS0CEpaKKAClxRiloATFLRjpRjAoAKXmigZoAXJ4pdxpKWgBQ7DpWvoWmLrFzLA0xR1jLIAPvGsit7whII/EUGWwGVl+vHSsMQ3Gm3Hc6MMoyqJS2MaRWileM8lWIP4Uzdir2rxCHV7uMdFlOKo4rSEuaKZnUjyzcRdxpQ5HakxRirIHeZ7UGQ8elNxRigB281Ln5qgqXJOKQEiDc+KBkP8AQ0znOe9OJ5HPvmgBo/1xHvSMNrEU7pMSe3NLIuQD3H8qACThQKI/ukZpJAWYDvSIcN7UAOjJ8wgnrSmV1flRkcU2QchhTuJRknDCgQeYuc7SD7UqyJngcn1pohJP3hQVRF5O5/QdBQMcPlOA3B9+lKArH5m4HFRgYwe5pSFU5PNAEhlBcggFaQSovA/QUjIjYMbgE9QaQQnPzMoHrQBYV8r8rZFVmbc/XgU5pFRdsZ+pNNAwuT3oAJBkg+tOl6L+dNfopznFOYEquKADGI801fvL9aXcdpBWmqcMPXNAEvelPSkzzS8kYpMpGrr8QjltHAADwL0rHzzzVq+v5LuOBXA/cpsGO9USzVnRTjBJmleUZTbiP9+1Npu40bj6CtTEcDRyehxTdxHpSbz7UAOxgnPUUlIXJbIApu4+gpiHHpR1pm40hY+1ADjzTTik3GkJoAngEe/96flxURIyccDtTCe1JStqO+lh24etJuGabSGmIfuGKTdTaSgBxekLU2igB272pNxpKSgBdxpMmikoAXJpPxoooASiiigApKWigBKKKKBhRRRQIcorQh0i4ns2uVHyLWeprpJtagi0BLWD/Wsu1vauetKasoHZhoU5JufQ5ojFIASQAMnoKUmnQzNBMkqY3IcjIyM1vrY5dLlrUNPGnxwLI+Z3Xc6joo7VRqS4uZbqdppnLSOeTUVKCaXvbjqOLl7uwUUUVZAYzQetJkijNABRSZpM0AOpCaSkoAXNJmiigQUUUUAJRRRQMKKKKAEooooAKKKKQF3TbMXVyBIdsS8sTV3Wtba+CWcHyWcPCKP4j6mqC37R2TW0aBd33mqnWPs+afNLpsdTrKFPkh13A0lLSVscoUlL2opgJRRRQAUlLRQAlFFFABSUtFACUUUUAFJS0UAJRS0lACUUtJQAUUUUAJRRRQAUUUUAFFFFABRRRQAlFLSUAFFFFABRRRQAUUUUDCkpaKQCUUtJQAUUUUAO8xtmzcdnXHam0UUBcKKKKAEopaSgAooooAKUUYooADSUtFACUtHelxQAlFBopiCiiigAooooAKKKWgAooooAKKKWgAoopQM0hhSjrThGT0owQfelcqzL9pEHxV82IZOlZVtMYnBrpLOaO4QcjNcVZyi7o9TDKE1ZnPXNo8RzjiqhWuzmsllTBA5rnr7Tnt2JAO2ro4hS0ZliMI4+8tjLxRT2WmkV1JnntWG0UtFMkSilopgFFFFACjpRSijFIAooopgJRRRQAUtJS0AFFFFAC0UUUAFLRRQAUUUtABRS4opDsJS0UUAFFFFMQUtFFIAooopgFFFLQAlLRRQAUUUUgClBwQaSigB7tuxxTaKKACiiimAtFJS0AFLSUtIBaWkpRQMcoq4umXbWv2lbdzCP4gKqJ1r1fwhLBqWhJCVUtEPLdf5VxYvESoxUkj0MFh4Vm1JnlJXBpuK6PxTobaPqjIqnyJPmjPt6VzzCt6VVVIqSOevRdKTixlFLikrY5xeaMmkpaBC5pc02nCgBeOtLTcYp8QUv8360DAGjmllAVuKZzQIf+NFMyaXJoAfU1vPJbTJNExSRDlWHaq4al3UmrqzKTad0TySPNK0kjFnY5YnuabimBuaXdmhK2gN31Y44PSjFN3UbqBDsUU3dS7qACpB90VFUiH5TQA6lzzSdaKAFfBbPQZp4CgfKTj1ph+ZMZ5pEdvu+lADzuA3dfwqPo2D3pS8gOMgUwlieTyKAJevBphypznmhW6ZNO6gg0APRwTg8GoiCr4bqKaev8qk3eYmD94dPegBST60hJOSe9NzwDR14oAci5JJOAO9LJJvHoOwprsMhV6CmqexoAco56UpPamfd4NJuoAfnccZ+tS88c4X3qDpz3qVuIh7mgB5bnqCB3qNTmTp3pB93NOT1oAf3q1ZwC4nWMnANVKeJCpDKSCOhFRJNrQ0pySd2WtTs1tXTaeCKziOalmleVgXZmPqTUJzRBNKzHWlGUrxWgYFGBRSVZkGBScUtJQAnFFGKSgApvFKRRTEJSUuKSgBKSnUhPNACGm06koASkp1NJFABSUZooAKSijNABQaM0E+9ACUUZpKACiikzQAtFJmigZv+FNKj1DU2nuhiys0M05PQgdB+NZF7cC7vp7gKEEkhYKowAM8Ct69vI9K8KwaVbMDPeYnunU/w/wAK1zNc9K8puo9tkdNa0IKmt92FGaSkroOUcDSk88HNMozRYdxSaTNJRQIM0ZoopgJRRRQAUlKaKBCUUUUDCkpaKBCUUUUAFFFJQAUUtJQAUUUUDEopaSgApQCTgUlGTg4pAKxHQU2lpKBhRRRTEJRS0lABSUtFACUUUUAJRS0lABRRRQAlFFFABRS0UAJRS0UgG0Up60lMBKKKKACkpaKAEopaSgAooooAKKKKACigUUAFJS0lAwoopaAEooopAFFLSUAFFLSUAJRRRQAUDrRR0oAXjk0lFFABQaKDQAlFLSUASAYxQVyM96XHAoz60AMoxmlPWlzgUAJ7UlFFACUUUUCFFJ3opaYxKWiigQUUUUDCilooEJS0UUAFPU4NMpaTGi/bhWx0qaW1VlyKzY5GQ5Bq8l2GXB61hOMk7o7Kc4SVmVWUxtg1YtrloXBBqKZw1RA1VuZamfNyS907TTr6O5QKx5q9NZpPGVYAgiuGtrl4XDKcV12laqlwoRyAa82vRlTfNE9nDYiNVcstzA1PSXtnLKuVrIZa9Mlt47mMhgCCK5HV9Fe1YyxjMftWuGxfN7stznxeCt78DniKSpWXFMIr0UzyHGw2ilopkiUtFFADh0paQCnYoAbQaX+dIRwaAG0UUUxBS0UUAFLSUtABRRS0AFFFFACinKOabTgcGkxokMZpBGT2qWJgeDitK2t1kIFYyqcu5106KnsZBjI7U3FdMdK3JkCsq8sGgJIBxUwxEZOxVXBzgrmbRTiuKSt7nG0JRS0lMQUUUooEFFFFABRRRQAUUUtABRRRQAUUUtACUUUtABRRRQAtFFFAC0tJS0DHCuo8HaudN1dA7Yhm+R/b0NcuKmifawrnr01Ug4s6sNVdOakj2nxPoi65ojeWoMyDfGff0rxmaJo3ZWBDA4IPavYPA+urqenC2mbM8Q2n3HY1y/j/AMPfYr3+0IE/czH5sdm/+vXkYGs6NR0Jnr4ykqsOeJwBFNqVxg1LYi3N2i3I/dN8pPp717jlZXPC5LysVKWrupadJp8+0/NE3KOOjCojbBrMXERLBfllH90+v0oU00mglSlFtPoV6tWMcUt7DHMcRs4DH2qtTkO1gfSnJXTsKm0pJs3/ABJpFtppiktjhX4Kk55rn63/ABCySwWU0bZRo8YzWBWOGbdNXZvi1FVXyqwUUUV0HILRR9KUdaBhRVy+sfsQh/eq/mJu+U9Kp0oyUldDlFxdmLSikpRTELRSUtABS0lLQACnIcN9aaKWgCYHmjFHBAINApAA/WkPyuG7GlNB5UigAk6q3bvSMMjPelU7lwabyp2mgBBycU4nsKTgH60HIPNACdKToRTs5pvWgB+cinRoZJAoOCe9Rg9qcsjI2QeaAHTRGKVkPOKYFz1pSSzFm5J5ooAMbhg9e1JghsHrTsYOTSH5jmgAbgVI4yqgVFz071K2dox3oAY3JAHSpBwKYBTqAF6UhNIx496Q8CkMaW9KM8U2imAuTRuNJRQAbjSbjRSUCF3Gk3GkpKYC7jSbjSUUAGTSZNBpKBC5NJk0UlAATSGiigBKKKSgAooo4weee1ACUUUUAJRRRQAUlLRQAlFFFABRRRQNCkknk5NNp1IaQ2JSUtJTJCkoopgFFFFABRRRQAlFOPAx3ptABRRRQAlFLSUAFFFFAgpKXGelJQAUUUUAJRS0lAwooooAKKKKAEooooAKKKKACkpaSgAooooASiiigApKWkoAKKKKAEooooAKSlooAKKB1p2OKQDaDTqKBjD1pKcetJQAlJS0UxCUUtJQAUUUUAFFFFACUUtFAxKKKXtSAQ0UUUAFFFFACUUppKAF7UlFKBk0AHakp7DBpp60ANoopcUAIBmlPWgcUds0AFJS0lABRS0g4NAARRS560lAEp+6tNpKKAButFFFACjg4pCMHIpc0daAG0p6UUvWgBtGMUUuKAEpcUu3JxR7UAJRR0NKBk0AJRWvBoz3MO+GQNgVVudOubUZlhYL/eHIrNVYN2ubOhUSvbQpUU7FJWhiJS0UUwClzSUUgHZpRTaWgBwOKswXDxOGUkGquaUGplFM0hNxd0drpGsrIBHIea32jjuosEAgivMYpmjYFTgiup0jW+kchrycThXH3oHu4TGqa5ZlPWtDa1dpYlzH3HpXPsuK9Q3RXcODg5FcfrejG2dpYVyncDtWuFxV/cnuY43Br44HOEUlPYYNNr00eK1YSiiloEOUcUtA6ClpAJwKQ9DTsZprdDTAZRRS0xBRRRQAUtFFABS0UUAFFFLQAUtJS0hj1JBrQsrvy3GazRTgcVnOCkrG1Kq4O6O9064inQA4zU13pyTocAVxllfvbuOeK7DTdTS4QAnmvJr0Z0pc0T38NiIVo8rOV1HTHt3JC8VlFcGvSLq1juYjwCK4zVNOa1lJA+WurDYnn917nDjcHye9HYyKKcRzSV3nktChcim4xxTgxFITnmjUHawlFFFMkKKWigBKWiigAooooAWiiigAooooAKKKWgAp8aNI4RRlmOAKZT43MciupwynIpO9tCo2vqPngkt5PLlUq3vUdX9T1BdQMT+XtdVwx9TVCpg24+9uXUUVK0XoKKcpplKKpohOxtaJq82k6hHdQscqfmH94elewTTWfifw0+0hkkTj/ZavCVatCy1q+0+KSO3uGRJBhlB4Nebi8F7VqcNGj1cLjFBcs9ivdxmG4kjPVWIqrT5JC7Fick9SajNehBNKzPOqSTk2jUttTRrF7K9UvDgmNh1Q9vwqnaXJtZ9+NyN8rof4hVeikqcVfzB1pO1+hYvIooZ/3Em+JhuQ9wPQ1BSUoq0rKxm3d3Q8uxUKWJA6D0ppoFFFrA3fcKKKKZIUtJRQMcST3opKKAFpaSloAWtK2tYrrR7l0GLq2YSHn70Z4P5H+dZtWtOvPsN4spXehBSRP7ykYIrOom1puaU2lL3titRQcbjjpniirM2LRSU9EaRtqKWb0AoBK+wqttPXg9akPHPrUPtT0fbweRQA/rQffpQeOeoNKCMAUAMIxginHDj0NFN6HigBvfB60uTTuGGOhphBB9aAFyKOKSloGhcZpduBmnIuavNpl0til60LC3diiyY4JHas5VFF6m0KMpK6Rnj3oPtT2XFMNWmZyjYPc0AknA596ACT1ozj5QKZAcAYHJp6ggc/gKRVxyetO780AAFL0oPFNJ4oATvmmsecUucc0zrQAUo60mOM0ZpFI6WLR7WTwi99z9oBJzn0PSucwM+lXk1e4j0qTT1x5LtuJ71nk1jRjOLlzPqdOInTko8q2WorqFPDZHrTDSmm1ujlYUlLSUxCUUUhoAKSlpKACkpaSgQUmKWpS6eQE2/Nnk0mykkyA0lOpKZI2ilpKACnIhkdUUZZjgCm1JBM9vOkyY3IcjIpO9tCo2vqWdSsRYSxxb9zlAzexqjU1zcSXU7TStl2OSahpQTUVzblVHFybjsFKQPLznnPSkpKogKKXtSUAApwFNp69aTHFFyCyaVc+tQ3VuYGwa1rWeJYRkjIFZuoXIuJsjoK5oSm526HfVp040r9SjSUppK6jz2JRRRTEFFFFABRRRQAlLiingcZpXsNK5GaKU9aSgTCikopgFFFFAgBwciiiigYlFLSUAFJS0UAJRS0lABRRRQAUlLSUAFFFFABSUUUAFFFFABSUtJQAUUUUAJRRRQAUlLRQAlFLSUAA6040g607GaQwxRS4IIFGOaQDGptPcc0ymAlFLSUxBRRRQAlLRRSAKSlooGJRRRQAUH0oooASiiigAooooAO1JS9qSgAp0f3qbSrxQA5zls0ylNFAAOtJTl60h70AJR2o6mlPAoAbRRRQAGiigigAoNFLQA4Ak8UnenkHHAqPp1oAKWkpaACiiigApe9IetKaADHIxS4ptKKAHgDGM803uc04HBFD9AaQDPeigAmlApgWbW8ntX3RSFSK6C18VfuxFewK6kY3KP6Vy+OKQk55rGpQhPdHRTxNSnszp7q20fUEMlrMsMmM4PGT9K5uWPypGQkEg9RTCaTvTp03DS90KtWVTXlswooorY5woopaBhRRRSAWlpKKAHZqSOQoQQcEVFS5pNXKjJp6HTaTrRQhJGronmiu4ecHivOVYg5BxWna6tJCmxicdq8+thLvmierh8fpyzF1ayWCYtH909qzZIXjALKQD0NW7y+NxT7W+Ro/IulDIejeldMOeMVc5Kqpzm7Oxm0CrF1CkMn7twyHkGq9bp3VzklHldmPHpS0nalFAgxTW6U/HNNbpQAyiiiqEFFFLQAUUUUALRRRSAKWiigApaSloGLSikooAcDirdrdvA4KsRVOlzUSipKzNIVHB3R22m6ws6BXb5qj1R45YGziuSimeJsqSKtSai8se09a4XhOWfNE9SOPUqfLPcSDTbi8Dm3TeV6qOtU3Ro2KOpVh1BHSrFrez2VwJoHKuP1ro0uNM8RQhLrbbXwHDDgNXRKpOm7tXRxxp06qtF2l+ZyNFT3VubW5khLBipxlehqCuhO6ujkkmnZhS0UUxBRWhpGnjUr5bfdtyM5pdX0uTSrswuQwIyrDuKz9rHn5Opr7GfJ7ToZ1KKSitDIWikpaACiiigA7ZooooAWiiigApaKKACloopAFFFFAC0uabS0DuLmigdRT3XjIoC11cZRRRTEFLSUuKAClpKXJoAKKKKACiiigApaKKAFFONNHWnd6QCd6WgjBooAKWkopgLVvTr59PvEuEUNt4KnoQaqUVMkmrMqMnF3RLPL5s8kgULubdtHamZpKKaVlYTd3dkkbc7T0NOPy/SoalWTHDcigQv0o68UYweOhpDgH1oAMc8UAmloxQAYU9qVFBbBpACDx1pyEE+hzSZS3JYlw+PevTIYEu/hG4Cgtbzsx49/8DXmkZPmZNem+BbiK68L63pkjDJQuq/UY/mK8rMLqKkujPVwlrHmkqYJ571AVAPrVuY7WOetVjnGe1ejTehxV0lJj47fzYZn3Y8tQcevOKiwBwBmrNvKscdwhOBJHtHuc1XGAaqLd2YySsrBzS/zpM0mT1NUZi89SeBTTycUEn6CmM3YUDBjk4puaKKYhR0pKKKBiZooooAKSiigQUhpaQ0AIaSlNFACUhpaKYCUUUUAJSUtJQAu0lSwHA602nmQ+XsB+XuKZSQOwlJS0lMQUUUUDCkNLSUAFJS0lAgooooAKXNNooGP3nGMnFNJpKKVhuTEoopKZIUUUUwCiiigAooooAKXccYpKKQ0wNJRSUxBR0oooAKKKKACiiigAoooNIBKKKKYBRRRQAUlLSUAFFFFACUUtFACUlLRQAlFLRSASrNpYy3jFY14HJJ6Co4YxJKFZgo7mtG71COG3FpZ8L/G/rWc5O9om9KEbc09jKkTY7JkHBxkU2lpK0Ri9wpKWkpiCiiigAoxRRSAF+8KlA/Oo1+8KlNJjG4yaMc+9KAR9aU4yaBkTjFNp79aZTEJSU6kPWgBKKWigQlFFFABRQKDQMMcZpKcvXFIRg0AJRRSigBKSlooASilpQpNAWEAzwKVkIGakjXknFDgYpXHYgpRRS0xBSUUUAHQ0d6XjFJQAe9DHJ4pKKAEpaKMEmgAoxmnbPU07AHSgBoT1NLxgjpS4zQSB1pAAZT3wadjI5Apm0Gk+ZeRTAcYx2ODTSpHanCQHgj8qePm6NQBCKU9akI9RTSnoaAGUtBUjtRQAlLRRQAtL2+tJ3o74oABS96SloAXOKCMikzTgaAI6Peg9aKAFpKWigAo70UUAFFFFAC0UlLQAUtJS0AFLmkooAWiiigBaKKKAH9hRR6UtIA701+lOPamt0/GgBlFFLVCCiiikAtFFFABS0UUAFFFFAC0UUUDFoopaACiiigBaKKKQwozRRQAH60UUUCCiiigCe0u5bK4WeFtrr0qXUNRn1K4M05y2McVUoqeSPNzW1NPaS5eS+glFLRVmYUUUUAFFPSN5M7FLYGTim0rjs9xKWkpaYgpaSloAUU5ELMFA5JwKaKljyrAg8ipk9C4K71Nc+F9QFr5+xemdueaxGUqxB612cXiyIafsliYzhccdDXHytvkZsdTmubDzqyb9ojsxdOhFJ02R0UUV1HAFLQKXGKLjsJUoOVIqKlBoauNOwoGTihlKnBoU/NmnyEEjFLqFlYZRRRTJCiiimAUtFAoAKeiNI6ooyzHAHvSAZNbV5oNzpukadrG9ZILrJUr/AwP3T78VnOoo6PdmtOk569EZE8EltO8Mq7ZEOGHpUdbPiNAb6O6XlbmJZMj1xzWNRTnzxTFVhyTcQp1NpwxWhmLmikpaQBS0gGadtNFx2G0tFFAgpaSl70AFLSUtADlcg+op+VJHXFRUoOKAJDweuaVVLNtXrTQc8d6UMVOR1pDXmKwKHkfWlDAnPekZy7Fj1NN5HIpDdr6EytWro3iG90OeWa0KbpIzGwcZGKxgec96M9KidKM1aS0NYVpQ1RNJIZJCznknJNMc5PWm9TzRVqKWhEpuTuxc0daToOtNLntTIH9O9WLWFLhZo+fNCbo/cjqPyqoW9T+FEUzRTJIvBU5FKSbWhUGk9Rpam1LO0bTu0QIQnIB7VFTWxLVmFFLSUxC0lKDikoGFJRRQIKKKUDmkNBSVKkZY4AoeNkOCMEetLmV7F+zdrkJpKcaaaohiUlLRTEJRgnoM0Uquy5wetIBtJSmkpgJRRRQAlFLSUAJRS0CgBMUhp9NPWkgaEpKWkpiCkpaSgANFFFAwpKKKBBSUtFACUUUUAFFFFABRRRQAUUUlABSUtFMBKKXvRQAlLRRQAUlLS4pDsNopaSgApKWkoEFFFLQAlFFFACUUtFACUUtJQAUUUUDEopaMUAJRRRQAhooNFACUUUUCEopaKAEopaKBir94VIOmTUa/eqWkwCkI5pwpDQMjftUdSN2pnemhCGkNOppoAMUlOzSd6AEooooAKKXHGf0pKAFXrQwpKOTQAlBFOxzSsPegBlPKgNgCmVIg5GaTGiSOAucAVZFptHIq1YouRmtC5RBF24Fck6zUrHo0sPFxuYTJtz2qvJwatTuAfpVN2ya3hqclWydkRnrSUpoPAxWpgJ3o7UUUAFJRTgnrxQA2nBCfYU4YHTrS4JoAbgD3NL6UuAOppDIB0FIBcetIWVenJqMsWoCk0wFLk0mCacBjtRQA6jpRR1oAQgE+9NIwafSdaAASMMZ5+tO3KT/AHTTCKTkUATds9fekIB+tRhiDwcU8OG+tIA2elJjB6U/sfalyDxQBFR3qQqMcU3YVNMBKKKKACgUlOHSgBpHNPVQaaRg0vQUAN6HFKKSloASlIwKVetB60AJR2oooAKKKXrQAgFLS4xSUAFApaBQAUUUUALiigUvegB+MUtGKBSGHemv0/GnY5pr9qBEdLRRTEFFFLQAUUCloAKKKKBhRRS0CCiiloGFFFFAC0UUtABRRRSAKKKKACiiloASilooAKKKKACiiigAooooA0NOvY7SKfI/eMMLxVBjlifWkpalRSbfcuVRyio9hKWiirIClpKWkA4Dmuk0Dwrc65bSzQyogTgBu5rmwa2tH8S3+iJIlqy7ZOocZAPrXPiFUcP3e514aVNS/ebGfe20lndSW8oxJG21hVU1Nc3El1cSTysWkdizE9zUNawTSXNuY1ZJyfLsJS0lLVmRNbCM3EfnHEe4bj7Vv+ILrTpLGGG1CGRT1QdBXNUtZSpc01K+x0Qr8kHBLcKKmgtJ7rf5MZfYMtjsKhrRNbGLi0rhS0lamgW2n3esQW+qTPDayEqZE/hJ6E+2aU5KMXJjhHmlyozKK2vEfhy78O6gbef54m5hmH3ZF9frWNRCcZx5o7BOEoO0hKWiiqICiiloAUV2vh3ULfUPC2p+H76VE2obi1dzjDjqBXE1K8ZSONtyneCcA5I5xzWNamqisdFGq6buT3N69xZ29u6/6jIVs9j2qGGEzb8MAFGeaYwG0EHJPUelNq4xsrIiU+aV5CUtFHWrMhaWkpaBkkOzzU8z7m4bvpXTeJF0RbG3/s4xmbjOw9vf3rlqM1jOlzTUr7G9OtyQcbbgetFFFbGAUtJS0CLmnWn2qc5wI4wWcnpiq0hDSMwAAJ4AqzFd+TYyQp9+U/M3t6VUrON+Ztm0+VQSW4UUUVoYi0oPam9aWgY7PalB4pgPrThxSAu2kCTWt4xH7yNAy/nzVTPNPineHeEON6lW9xTKlJ3ZcmnFWFpDxSZ9KTiqIAmkJozmkpgFFFFAB7UUUUAFFFOxhc0gEbGeKbS0cbfemAlFFFABT160ynLSY47nXeBbWO58UWiyKGUEsQfYVH43s47bxJdrEoVS2cD6UeCbxLTxFBM5wqq2T+FR+LtRTUNYnmQ5DNkfSvK9/wCt+Vj2vd+rHMOOaZT3PNMr1UeNLcSiiimQJSUtFACUlLSUwCkpe9FACUlLRQAlHSg0GgAzSUUlABSUtJQAUlLSUAFFFFACUUUUCCiiigBKKKKACiiigAHSiilVdzAdMnFFxpCheM001NKhiYxnGR1xUJ60k7lSVtBKKWimQJRRRQAUU5EaRwiAkntQwAYgHOO470DLel2D6jfR28fVjyfQVs+IbTS9Kt0s7f8Ae3fWSTPQfSuehnlt33wyNG443KcGlQS3MwUbnkc/UmuecJOak3ojqp1YxpuCj7z6kJoq9f2S2QRGfMxGWUdqo1tGSkro55wcHZiUUUVRIUUUUAFJS0lABRRRQAUUUUAFGKUClApDSG4oxUoQ0hUilcrkZFUkUEkxIjUttGT7CmkU5ZpEjaNWIVuoHeh36CVr6kRFJSmiqJEooHWg9aAEopaKAEopaKAFX7wqT0qNfvCpKTADQfUUdv1prDdigYj9aYetOI+bHamnrQISkNO+tIaYDaKUUHmgBOtAGSBRQOtADmPpTMU7FDelADKcDSUYzQAp6jmlNNooAP50obBopKALkFyY8c1NNfs67QeKzskUZ461m6cW7m6rzSsOdyx560yjNJVpWMW7h3oNB4NOVM/SmIZgnoKcE9ak4XpSH1pXATGOgpQpP0oLAdB+dMLE9TQMflV9zTGc/Sm5J6UBaBCZJNKF9acAM0YoAMAUnWlAyaM8mgYYopaSgBaKUg0n4UCA9KSlpKYB6UvBPNJS0gEwKQinUUwGhiOKkDqevFNxmkK0ASY4yKfnmq/IPpThIR2zSAlIDdaYU5wOaUSA+1OHXIoAjIIPSk9jU+496QhW6gUXAhpTUhjHYmmFGHagA25FNxzinj2oJ5zTAaBzQ1IeTRjNABSj1pOhpaADFKvWkFKKAFbrxSClJzigCgA45oBxSdzSgZNACd6KCMGloAKUdaKB96gCTPPSjPPSgZpcZyKQwxxUb9RUgzmo5PvUANooxS45piEpaSloEFLQKKBhRRRQAUooo6UALRRRQAUtJS0AHeloFFIApaSloAKKMUUAFFFLQAlFLRQAlFLSUAFFFFABRRS0AJS0UUAFFFFABS0UUALRRRQAUUUUAFLRRQAUUUtAyxaX09kXMLAbxg5Gar9TmjFGKSSTuNybVmFOFJRTEjtdI8SWWoaDLoXiFiYkQtaXWMtEwHCmuMNOUIUYsxDD7oA60ysadJQbceptUqucUn0CloorYxCilooASilxRigBKKWpv9G+xf8ALT7Vv/4Dt/xpXsNK5DSikqSJQ7qpIAJAye1DdhJXdhMcUmKv6jYSadePbyENjBVh0YHoapGpjJSV0XODg7MbS0lLVkBSqu7PIGOeaSikAtFFFMApe9JRQAtFFFACjrQetA60ppD6CUA0UUCHZ4oJxTaXNAATmkpaSmAUUUUAFFFFIAoopRQAlBOaXjFJQMKSlooEJRUxjQW+7d83pUNCdxuNgpaSigRKkrxtuRsGkeRnJZjk1HSVPKr3NPaO1gNJS0lUZiUUtJTASilpKBCUUtJQAlFLRQMkih8wE7gMGmSx+W5XOcUqSNGcrTXYuxY9TU63KfLy+YyilpKogSilpKAEopaSmAlJS0UAJRS0mOKAEpQMnFFFACUUUqruNACUlOIwcUlACuoVsA5ptLRQDEooooAM5ooooAKKKKAClRGkcKoyTQFLMABkngCtW0tvLBGMvxk/0pN2GlcglUWNk2P9bJ8ob+eKz+lT6lN5t55YOVj+X8e9QUkNi1p2l5Bp9uzKu+6bo3Zay6KUoKSsyoVHB3W4+SRpXLuxLNySaZRRVJWIbu7sKKKKYgpKWkoAntLOe9m8qBCzAZPYAepNRSJ5cjJuVsHGV6Grb6gVtPslsvlRHlyPvSH3Pp7VSqI8zd2XJRSstwpKWirIEoopaAAVIg5qMVIpwahmkNztPCfgqfxCjTs4htlO0vjJJ9BWX4s0KPQNYkso5TIqqGDHg8itXwx48n8PafJaC2SZGbcmWxtNc1q+qz6vqE15ctullbJ9vYV51JYh4huXwnqVZUfZWW5mHrTTTiaaa9JHksQ0lOam0yQFJSmimAlFFGO9AAetFFLQAL94U80wcEU/qeaQwoopCcmgBMEmkIPXFOHfFOJB9aQ7EQFBFSBD6Ve0/SbjUZQsSHb3Y9BUyqRirs1p0ZTdoozMUhGDXUap4ZXT7A3HnEsvUHvXMsKmlWjVV4jr4eVF2kMo6UoGTiggDpWpzgTQ2KD14pppgFA6UYozxjNACU5gAcCm0vegBDSjpQaSgANJTgpPalEf/wBegBoGelOCetP4Haj5mPoKQxNq5zR7AYoJVe+aYXJ6cUAP+7yTUZakwTS7RQITk0Y4p1GKAGiloHSloGGOc0UUUAHakHrS89qMUAJRS4pOcdKAJM0YU0lHtQINp7EGmkY607NO3CgZEelLT9qmmlCOnNAhKKOR1oFAC0UUUDDFGM0uKMUAN20nIp+KKBDRIwp4kHcU3HFIVoAmDj1/OnD2NVuRShjRYCcqD1xTTHnofzpokPrn604PntQMjKEdRQCRUwYE0FQx7UXEQdTmjkVIYiOn601lZe1MBBzRmgUUALSnoKSikAU4AflTc0tACkd80lFFMBaUfepAKVetIBwpc+tIKM80DFPH0pjDLU7dSdWzQA3oaVqVsYH1pAMmgQAUpXvQeDig0AJQetGeKcRgA+tACGkpaTvTAWijvR2oAWikpaQBS0lLQAoooo60ALSrjIz0oHSkpDJZECgFelR0pYkAdqShFSab0ClClgcdqSlBweKCUJRS9TRTAQ0UUUAFFFFABitWzs9Ov4Fi+1G0vRx+/wD9VJ+P8J+vFZijNPZMDNRLXZmkNNWri3VrLZXL286hZEOCAQR+dQ0tJVLbUh2voFFFLTELtOM9qSlycY7UUAwooycY7UtACUtFFABRRRQAtSwqrSAN0qKlBxSeo4uzuWbiJVA28Uy1MK3MRuUZ4Aw3qpwSO+DUZdm6kmkqUnazLclzcyRs6zosdlHHe2MwuNOmPyPn5lP91vesal3Nt27jtznGeM0lEFJKzdwqSjJ3irBSjrRRVGYd6dtpB1pyn1oY0hpGDzTgM0pOeKBSuO2p0E/haQeFbfXrWcXELErcIBzC2e/tXPEYNdb4K8RR6VeyWN/h9LvR5c6NyFJ4DVmeKNGGha7PZLIJIhh4nBzlDyK5aVSaqOnP1R1VacZU1OHzMOiloxXWcYU4VcsNRazDRvDFcW7/AH4ZRwfcHqD7iork2zXDNaJJHCeQkjAlfbI61N3ezRpyq10ye7vnvLe2WUAtCpTf3Yds1SNL3p5IERXaMk53d6UUoqyHKTm7sioopRVmQlLWnFbaXLZM32yWK5C52SR/Kx9ARWbUxkmXKDiJRRS4IGccetURYSiiloAdsIXdTaXccY7UE5oQ3boJS0UUCCiiigAooooAUDOaSlooASiilxQAUoFAFSxpuIFS3YuEOZ2IsGkrr/Fvhm30O002W3Z3FxFuct/e68fnXIkVnRrRqx5omtai6TsxKSloxxWxgJRS4ooAbRS0lABRRRQIKSlooGJRilqVAzDYBnJ9OaTdilG5ARRUrxMrFWBBHY8VGaE7ilFrcbRS0lMkSilooAQDikIqRVzV25ltRpsNvCgM2d0shHP0qXKzsaRhdNtmbRSnr1pKszEopaKAG0UtJQISkpaKAEpKWigBKKKKAEooqSKNXV2Zwu0ZA9TQ3YaVyOnBgq8daaaKAvYO9JS0lMQU/wAs7NxojTe2O3enzOD8o6Cpb1si0la7IaKKKogKMUUopAJRinBasWlq13dRwqPvHn6UnJLUpRb0Ro6XpoMAu5nVFZtoyefwHvTZbwR27zgBUXiNPVjxz6+tXtQnNtOljGsQBjaKRQDkg9d2eMggYxXO6lNmRYF+7EMHHdqiN3qzSVo6IppkyZPXqalqOMdT+FS1oZMTvRRRTEFFFFIAoo7UUwEoo7UUgDvR3pe9JQAUUUUAJS0UUAFKKQUo6UikP3U0mko7e1Kw3JidqTvS96TvVEg3Wm96WjtQAlOK46UnSlJzjmgBB1oI70o+9QxoAZT1TcM02noeAAaAGnjilAJpHPzGn9eP5UAMORQKUjmgCkAo5p6rmhEJOMV2fhrwk94y3F2hWLqFP8Vc9fEQox5pHbhsNKtKyM3QvDVxqjh3BSDPU9/pXdPFp/h/TwW2oAOndjU+parY+H7MKNvmY+WMV5prGsT6lcNJM/0UdBXkxVXGSu9IntSdLBwstx2ua3JqkpH3YgflX/GufbrUjMSc1H1+te1SpqnHlieBiKzqy5mA45pCc0UmOa1OcSkqQ8e1MoEJTyq7Mj86QKT2pwQDuaBojxzShD9KlA9BSHA6mi4DNgzyc04ADoKQuOw5pNzGgBxPFNBwfbvSYz1owMUAO8wD7o/OmFmbqaUjGMd6XAFADAtOAGadSUAFJS+1FACd+aSlo2k9AaAEHSloHIxRigBKXknpTsAHk0hJPAoAQrjGTRSkcUhYCgBG4GKXsKTqQaQuKAE3nuKcHU+1RUUxE/40tQA04ORSAlx6UZI70wOD7Gn5yODQMdkHgik2KehxSfSl/nQA0oRzj8qSpATnFKcHjHNAEf0pwzShcEEHNbNjBbToAdpPp3rOc+VXNaVL2jsmYuKQiujm0SFwTGxQ+lYt1bNbSbGOfephWjPRF1cNOmrsq0tBorY5w7UhANL70d6AGbfSjBHSpWTHOeKbQFhoc9xmnBwe+KMA0mwUCJAxxwaXrUW0g8GlDMOozQMkO09RTfLGeDSCQe4p4IJoAb5belNxipe/B/OnA54NAFfvRU5RD25pph/un86LiI80oGTSmNh1FOQZ4oGkNwRS4qwIflz1qBhtOO1JO5Ti0JSnpShGKF8fKDgn0NJTJDHANBHFHSjk8UAN780DrSkYoA4oAlit57liIYXkI67Fzikkglgk8uaN42/usMGiKWSI5jkdCeu1iM0SO8jb5HZ29WOTU63K923mMYDNKRR796UtwD3qiRnfFOK4FIeadnigBlLj5c0d6VetADe9LSkc0oUn6UXCwgpcVOsAGSx49qlRY1GR95f/AB6oc0bRoSZWWNj2pxhcHBXHOKsiVFkK4BU8j/CpDcKwIbk/dz6jtUOozZYaPcpmCRQCV/z0pvltxweavpOA6k8gHvU6yIWYEZBJxS9q10K+qRezMjBFJWzEkbOw2jaWxj8ag+wpKzbW298gfWmqq6kywckrrUzcc0VM9vImSVOB3qGtU0zllFxdmgoopaCQooPWigAxRRS0AKpxT2fIxUdFKxSk0hO9FLSUyQoopaACiiloAKKXFLtIoHYbS0UtArCUUtFACUtFWLG0+23aW4mjiZ+FaQ4XPYE+9JtJXY4xbdkQCirN7p91ptwYLuFon7Z6H3B71WoTTV0OUXF2YVNbRxSXMaTymGJmAaQLu2j1xUVKKGC0Zo6rot1pLoZSktvLzDcRHKSD2Pr7VnkkqAeg6U8zSGHyfMbygdwTPyg+uKZSjdL3hycb+6A64pcUlOzTJEpetJTqBoQGlZ2fBZiTjHJzSHrSUWW47vYKKKWmSKuNw3dM84pz7DIfLBCdgetMIIODS0h30F70MaKCKAEo70UUxDgavXVgLe0jmMgLOAdtUKcXZgAWJA6ZPSoabaszSMopNNDacXJQL6U2irM7iUUtFABS9hSUooAKKKKBBRRS0AFHeiigAooooAKWiigYoqeLrUAqVGwaznqjei7SPTfGSC7+H+jXg5KhAfxXH9K8ubrXpE+oW1z8I4ojMvnQyhNhb5s7s9Poa84bqa4cvTjGUX0bOvHWdmR0uKWnAdK9E86w2mmr8Fl50TSM4VRwKpMMGkpJuyKlBxSb6jKKWkpkElvbTXU6wwRl5G6KKZJG0UjI4wynBB7GrFjfT6fdC4t2AkAI5GetQuzSyPIxyzHcxqby5vI0tHl03GlCuM8Z5ptPLFupzim1RGnQB1rovDtjO0v9oC0ea2t2zIwHArnhwa3dN8U3ul6Nc6bAsflz5O8j5lyMHFc+IjOULQOrCyhCd5kfia8tr3VnmtVAjwBkDGTWIaczZpprWlDkiomVap7SbkIaSnq5UHAHIxzTK0MRKUCijpQCOt0jwzBd6X9pmlYOwLDHRR71y06hJnUHIUkZ9auRaxeRWZto5mWM9qz2OTXNShUUm5vQ7K9Sk4RUEWJ74zWFvaCCBFhJO9F+dyf7xqpS0ldCSWxySk5bhSUtFMkSkNLSUwEpKWigQ2ilpKACkpaSgApMUtKBQMSkpxpKAEopwGeKGUrwQQfQ0XCz3AMQuBxmm0GigLhRRRQIKUUlKKBo0NLsG1LUIbRDhpWxn0rs/wDhHP8AhGo5btpUnkb5bcY5Z8cD6d/wrmPC7SxazHcRReY8QLKh7t0ArQ1vU59Tv0Ek3mRCJjkfKpJPOB6cdPSuGaqTq2T909KnKnCjzNe8zNkuDFbXErS+Z8wZ/cjO0A+mSfyrmzk5Zjlj+ZJrU1eVQ0dnD3Idx744H6n86zsAMFGCe/tXZFHnyeo9RtUClo70dDVECAc0UCl60AFBBHUVZt0iQM8p6dFqKaQyybscdhSvd2LcbK7IqO1FFMgO1FA+lFAB3o74o70HrQAlApe1AoGGKSlpO9ABUtusLXEazuY4SwDuoyQPXFRUUmroadnc0dWi0yGdF0u5lnjx8zSLt5qiMbD60ynKwAwehqYxsrXuVKSk72sMoopxGFqyBlL/ACoooAUjHSm9KdSAZOKAE60D0pzDBxQUIUN2NILCKMtTyMHikUYXPHNKScUANZRuzR06UHrSseeKBjTzTkFIRSqcUmVHfU9B8I+FEdEvr0A55SM/zrc1/wAS2ujQGC2KtPjGB/DXFL4zvY9MS0jCoVXbvHU1z1xcyTuXkYkk5JPevH+pVK1Xnrbdj3XjaVGly0tya+1Ce9uDNM5Z2PeqTsSeaMnoKTYx/wDr160IKKsjxqlWU3dsYTQvWnFMfWjYe5qzEa3Bpu0mpcAUhcD/AOtTENCeppwUDoKaZM9BTfmbvQA8kDqaaZPQUmz1pcCgBuWagL6mn0lADcUtLSUAJS0UUAFLSd6WgAxSUUYJ7UgEop231P4UYA6c0wG4NaFjqf2CJxHAjSv1d+ePSqJJpOlTKKkrMqM3F3Q52Mjs/GWOcCm8YxRj3xSFlGfX2pibvqHalPqeKjMh7cUwnJpiJGcdsmmE4JxSUUCDNJRRTAKKKKACiiigBaM4pKKAJBIR708Op68VDRSAsZ445pe1VwcU4Oe/NAywCQAQeKcXwQwOD6ioRIOhyKeGBHWk0NOxei1C6RcLKSPQ1XuJJJ23MQagVtpIPSng+lSoRTukW6s5KzZGQR1BptT7jikIU9RVGZBmnnAANOManoaTyj2OaYCbiRg0UBTkilII7UAGKKKUUAJRS44oIpAJgHtSFB606imA3DDoaXLU6g5xQA3e2KcJPUflQPSjANIB6up6N+dO4PPWotgpNpHQ0AWQ3GM/nUbqzHOKjDSL3z9acJiOqilaxTk3oxpBHUUlSiVTwQaP3b9wKZJH6Ud6k8r0bNMZGXkjigBM0qngikII7UCmApo4xRjikFIBwNGM4pO1FADe9LTm5xTaYAOtL2pKkRB1PApN2KjFydkKkZbk9Km81YwF4Pbp1FRPLt4/Q1XZ9xOT+FZ6s6UlDYsNNuXbk4HT2FRGQg57jg1EWIPv/OgnjI6U7D5iVpMfzFCyHJHtUIbgj8qTdgiiwuctCQ7h6ZzUscx3jnv0qmrZwKcrYcemalxNFM0YZ8OAe5zVqGX5XBPUYNZKPhhU6y4Tr71nKJvCoaXmb06AjqB7npUM2np5AkRvmwfl9feo4nIwOp6n6npV1pQu1AcnoSfX1/Cou4vQ0cI1F7xjFSpwRTa2pLVJ4ixOAOnHSsqa3kgcLIuCRkV0QqKR51bDyp69CKgUUVoc4ClpKWgAooooAO9FFLQAlL26mkx2pTQAlKKKUUAOQc1cNjOLcTmJvK/v44qotdf4a1eFo/7NvtpjfhGbp9DXNiJyhHmirnbhacKj5ZOxyTJim7eM+ldPr/h19OczwgtaseD/AHfrXNMuDVUq0akbxIr4eVKVmR0Yp2KStjlsJRS4opgb+neIUa3FhrMJvLHop/5aRe6n+lYkwjE7iEsYtx2FuCR2zUdLWcaai7o0lUlJJS6BSiilqzMKBRTtpABxwe9AxKWjFFABS0lLQAhopaKAEoxS05XKqygDDcHNAJDKUUU4CgAopcUmKAEoopaAEp2RtxjnPWk7UpOce1ACUVI0eEVt2c9R6UzFF7g00CNscGhl2OR+X0oxQSSAD2GBQHQbS0UYpiCilxQP0pAJS0HGeOlFABRRS0AHHaiiigAoopcUAApwOKbS0ik7D95xjNMJoopJWKcmwArYuNEmt9IivycpJ29BWSOtehZS58AgcZWL8iDXLiasqbjbqzswlGNVSv2PPySBjnFRtUjdaY1dSOOXYjopaKogSjtRS0AJS0oGasrYXDWrXKwuYFOC4HAqXJLcuMJS2RUxRTivNIRTFYbSUppKZIlHbrS0UANop204pdq7M55z0ouOxHQaWkoEJR2paSmIULlS3YU2looBjaSnUlAhDSUtFMBtFLSUAIaKWkoASloq5Jps8WnJeSYVHOEB6sPWpcktyoxctinQKKKZJ1nhSLSbWCfVdTkRjCcRwk8sfpXP6penUNSnuyoTzWyFHQDsKqZpDWMKNpubd2zonX5qappWSEpKWitznCkpaKACiirNhbfartI/4fvMfYVMnZXZUYuTsjo9FH9k6eL4SpHc7lkQHqcnAx+prMEsMMjzOwMapnaOSTnofTNa2uEQRLYO0Be3+djGcneVGEP0Hb1NczqsnlRrbLjJ+ZsVjSV9X1Oiu7PlXQoS3DzTySv99zyaSMd/wqP0xmpwMKBW5yiig8mjtSimAnajpQetKRxmgBOTyaUdaXsKbjHNACHrS0uMmkIwcUAHbpSDrTwBxTT1zQAh7UppQM0ntQAnWilIAHFJjmgABwaD1pSoAyaQDmgAFJ3pRSYpAOUcH0ptLzjFGDnFACUEk80UdqYBj9aKKWkAUDgg0UY6UDDqQTwKV33Y9qQ9h2oPUUDEwMY70oAHJpDS8kcCgQdqTqKUKR1pSozz1oAbntQAfSn/AEH5UE+ppDAIT/FS4Ue5phf0H500uT0oHclLAe1MLj60zBPU0oWmK4hYk9hSEsTj+VOAHpRjmgQzaaXZxTqKAEwKXH5UopyqScDrSbGlcZijFdFp3hS9vVEjYijPOW6mtWTwhaW0JaWdyQM56CuWWMpRdrnbDAVZK9rHD4pKuXcUcVwyRHKg1VYCumMrq5yThyuzGUUUoUk4qiBKO9O280ZAPagQ3ByOKD6ClJGTjk0dDmgBeAaTOKCOaaWA/i/KgBeaOnamGQ9qYWJ7mmBIzD1ppk9KZSUAKWJ6k0lFFABRRRTAKSiigQUUUUAFFFFABRRRQAUtJRQAtFJS0AFFFFAC0ZoooAXcfWpFlxwR+IqKikMsiRT3/OncGqtAJB4NFguWsDtzjrS/yquJWA9akEw7gikA4n5xnHPrTs+/51E7hsYNPVgRjPNADsA9RRsGetGKKAE2H1oKN6Zp2cDvS5NAyM+9FS7s9f1pNqn2oAjpaf5ZHQg00qw7UAN96XHFFL2oEFFGKKBhRxS0daAE2ik8v0NOpTxzQAzaR0z+FAkccE5HvTx0zQcGgBVcEnrSlVPbFR7PQ0DevfigBShGccimdOKk8zkbgaXejHn9RQBH6UtSeWjdD+RpPLIHBBoAjNAFOKkDkUgoAFHNDyAcdPrStjbjt9KhPXrUPU3iuVCFjz3FNyDSYI6U3v70xNjs9mpM44PNJnjmkz2NMVx2cHFL0NMJzg/hViGyubkAxwsVPRmIUfmaLBzEanDilB+b8atx6WSQJb6xhI/56Tf4A099LjVsLq2nOTz8sjf4UWDnKgb5voKlQ5YDsBmpk0meUgW01vcZGf3coB/I1WkV4JWilRo5AcFHGCPwqWjWM0Wkkxgk9f8AOaswNltzHGen0rOQ7m5PAq6r4xn16f0rGSOqlK5rRSFmXHf7qnoB6mlurWOSEo5xKedzdfqfT6UkLLChLfM/XA9alEa5824JaV/uxrXNdp3O5xUo2ZzroUYq3UUzpW3fWLS27XOFQjnHc/41jEY4rupzU1c8SvRdKVhKd2FJjgUd6swAnJo70pxSUDFHXpTnKnBXr3FNo7UB5CgfKDTT1pwpDQAe9AoxRjFAhw61KjYqIU4cGk1c0hKzO78NeIopo/7O1Qgow2o79D7GsHxJp1vp+qPFbSK8TDcADnb7VjxtzUzljycnPc1xxoKnV54vR9D0JYj2tLlkte5PpWiXutzzQ2EQlliiMpTOCVHXHrWc6FGKsCCDgg9qv6Zqdzo+pQ31o+yeFtynsR3B9jXXeKtOs/EGjDxZpCBOQL+3H/LJ/wC9VyrShUSl8L/Mw9jGcLx3RwGKSnEUldRxtCd6cKSlA7mgApaKWgAq/pltbXk5t7m5+zlh+7cj5d3v6VRFOqJJtWRpBpO7Vy/qej3mkzbLmIhT92ReVYeoNZ9aY1y8OkSabIwlgYgrv5MePQ1m1NNztaZVVQveAlGKWgdea0MrCUUvfjpRTAKKezAkYULim0gaEpw6UlOA4oAKCKfjIGKbigdiey0+e/MwgCkxIZGBOOBU+i6U2s6lHZJPFAzg7Wk6E+n1NUVYqTtYjPHBxmnI7IwZSVYHIIPINRJSadmaRcFa69Sxqel3WkX0lpeR7JU/Ij1FVMVpaprd7rEdst66yNbqVWTHzMPc96zu1FNy5Vz7iqKPN7mxpNqEMmgLYPBmaOXdHKP7p6g1mmlGMUoxkZ6U4xUb2CcnO1xmKMVZuIolRXjYc9qr4pp3IlGzsNxTuWGe4HNSiDfDvQ5YH5l7iouVb3FO9ws1uJ1opzAEbl6dx6U2mS0JS0tAGTQA6OJ5ZFSNSzk8AdTTWUqxDAgg4INWrW6exnEsYG4Ajmq7sXcsepOTUpu/kW0lHzGUUoGfpU1zHFFNthl8xMA5x3p31sTy6XIRUsixBUMbliR84I6Gk25j3AjjgikxSKtYbRS4opkiUpOTmigUAAq/HqV1HZNaLIRC3JWqNOBqZRUtzSE5R2YrA1GakLEioyKaJkNIwcGkp5Ur1BGRnmm4pk2Eoqxb23nxzv5qJ5Kb8MeW5xge9Q4ouNxa1FXrXoEHkRfD6QcZaMk/UmuA2kKG7HpU/wBtuPs32bzW8nOdmeK5sRRdW1nszswtdUb3W6K7U04x704mmmuhHK2NpKdQScY7A5pkDaWiigEeg2ui+H18ENdz+UZ2h3mUv8wfsAK89NPySMZOPTPFMP1rCjSdNtuV7nTXqqolZWsNpMUtKx3HOMcV0HNYbSe1LSlSDyCOKBDaQ0ooxQISkpccZ7UlMBKSnUhoAbRS0lAhKKWkxQAVI9xNJEkbysyJ91SeBTAM0hGKLJlJtISil70lAgooooEJ3oNFFABRR2pccUAJXT+HrYwW73Zby5DzG+3JHpgdznn8K5+0t2urqOFertj8K6fU2SzjNoMfaAgVWjb/AFadwx/vH07VjVd2oI6aC5U5soZQahc3CgeVDuVSx3Fv7zE9yec/Wubldrq4eVsgE5PsO1a+py/ZrCK3TrNGpP06k1jSEAbEPyjqR/Ef8K0irGU3diIMuPapaRF2r7mnAcZqjMCOBSCpFAB9aRvvEUANGBzRS9RRjigBOtBGDilxSgEnpnNA7CDg8ijuadgnHB/KmnPegLBSd6XtSY4oEFJT0Qv060jIUODRcdnuIRxn17U0inE80cE80AGc4oIBoPsaBxQIbSgcUAZo70AA60H1oHDUUAIB3peopKUZ7UDExSgcUoVqUJ6mgBoGau2OnXGpXK29pEZJG7DsPU1XUAHOM/WtTTtcudKtZ4rQIkk3DS4+YD0FZ1HPl9zc2oqHN7+xn3tjNY3cltNt8yM4O05FV9g7n8qmdy7F2JZickk9ajJA71Ub21Ina75dhNuO350fjSF/QZ+tNwzd6ZI4kDqabv8AQUuwCrP2C7EPm/ZZxGRkN5Zxj60NpbjUW9ioSx9aNtOA5NGKBDdopcUtFACYoIxTs4FIaAG0dzRR3piCjmjafSnbfU0AN6VPbzeROkm0NtOcGosAD396GYDpUtXVi4ycXdHUP4zvTFshiii46jmsa71O9vWJnuJHHpniqRfA4pCT61jDD04axR0TxdSas2DD1NNwMc5NL0NIRk5JrdHM3cMgcZApuecjrSF1DD0prSjPApkjuTyeaQkKMZqMux702gQ7fSFyabSUwFJPrSUUUAFFFFABRRSUAFFFFABSUtJTEFFFFABRRRQAUUUUAFFFFABRRRQAUUUtABRRRQAUUUUgFopKKYC0UUUALRSUtIBaKSigY8Oy9DTxMQeRUVFAFhZFJOTipV2lh0PvVOlBxSsNMvGP5cjtUZ47VEszr/F+dOWYfxD8RSSY210H5wetKGIpAyN0Ipdo9TQIXIPBFGxD3IpMe9GBnHOKADy+OGH40hRh2p/WjOOlAEfTrR2qXPrSYU84/KgBgop2wHocUFCFz1+lADcUppAD+FFAC0c0UUAFJgHtS0tADNgNKAyng07vRQAglI6r+VDyLt4x+NLVeQ5Y4zQXFajWIPOf1ph69aCPU/hRhff8qRbEyfXPtSlsjBpOPWmmmIDx0p8cRkyzMEQdWNJGgOWb7q9R6+1K7lyM8KOAOwpkNkglji4hQZxy7jJ/AdqjeR5fvuz/AFPH5UgFO2457djTIGAcZGBRknqadjNGKAG8Vt2viCUxG21KP7ZbMvlljjzkX/Zb6gdayohEyOJA+4DKlMcn3qPqeBxQNM17rTfs8f2y0mF3YE4WZVwUP92Rf4T+h7Uy3IQeYe3T3NVtP1GfTbkyQFSHXZJG4ykq91YdxWxJa289v/aGnZ+y5Cywsctasex9VPZvwNY1I6HXh6mtmJA2073wST90/wAz/hWlDhNpb755x3b6/wCFZ9tE0zqUGMdCegHrWhJcW+nL1LzHnJ6k+3p9a4p6uy3PYg1CPNLY0UhiWNpbjrg/ebH/AOquPuyj3UhTBXPGOhqW6vprtjvOE7IOn/16q10UKThq2eZjMTGr7sVoIOlJinUCuk4AOMUmKUUpHIoGIRVmynW0u45nhSZVPKP0YVXP3vpRSaurMcXZ3Rvz6PbanA15orElRmW0Y/OnuvqKwWQq2CCGHBB7VLb3E1nOk9vI0cinIZTU+pai2qXQuZYY45NoDmMY3n1PvWUFOLtujao4TjdaMpD3pSMUGlYd81qYB2pythWG0HcMZPb6UygdaBpjwcVJvBpmOfam1NrlqTQ5jk1LFd3EMMsMU8iRTDEiK2A4HqO9Q4oIweDn3ocU9GHM73QDGeamu7UWzRgSxyb0D/Ic7c9j71CKTGDinrcV1Zqw3vSjrS0Y5FUQKKO3BpSMcUoFIAHSnZOMdqQClpFCUUtJimIKX60UY4oAKUYzzQTk0d6AEpcUGloCwqxswJCkgdSBSgYFdb4KubZjPp88aky/MuR19RWV4i07+ztVljVdsbfMn0rmjiL1XTaOuWGtRVWLuY4op2Kb+NdByjanit2ljd1IwvXJqLvS5IyATg9aTv0HG19RKKWjBFMQY6UdqOp5p1AxuKVdoYFlyueR0zWlodtZXur29tfytFBKdhkX+Fj90n2ziodT0+bStSuLGcfvYXKn396jnXNydS/Zvl5innD5TK88c9KCd3Xr60Yo71ZBc0u1hurvypiRlTtx61UkTy5XT+6SKfBNJbTLLE2116Gmu5kkZ3OWY5JqUnzX6FtxcErajXTY2MgnGeKEYBgTzigCjFUZ9boTqc0qqCcFse9JRQIcyKvRwTTe9LSUDHpnG3t1rrl8Aai+lrdo8bOU3+T3x9fWuRU4NdRH471ePTxaK0XC7BJt+YCuXEKtp7I68M6Nn7U5iRNjlSOQcUzFPdy7lj1JzTK6o3tqcs7X0DHFFGeKKZIU6m1YhgedtqDJqW0tyoxcnZENNxVue1e3I3j8u1VyM0Jp6ocouLsxhyeTk/Wkz6U4ikxTIG4op2DSUwCjvRQaQxDSGnUlADaKdSEUxE1p9mErfag5j2HGzruxxUOKMUoFT5lX0saGiW1ldavbxajcC3sy2ZZD6DnH49Kv+MNU0zUtRiTSLRILO2j8pGVcGT3NYQUtwKHjdCNykEjIyMZrJwTqKbexspP2bikQkUlPIptbnO0NpTk8kk0uKTFACDpTTTyMU3FAhMUlOIGPekpiEakpe9JQAmOaCKXvQenvQIbjgGkp4zimigBOhoPJoopgJRSjpRjjNADR1pT14oNAoASjGKXGKD1oASiinpG0siogyzEAD3pNjSvodD4WswZTdSv5UZYRCUjKoTxk/jgVXdTPqE0ceCZAOWGAD3Na13K2k6fHYxRxvvQNubnGM9B65+b8BWDezm1tnZeGlyiDuMjk/gKwp+83LudNW0UodjN1K6W4vmdRuVQET02jvVNFLuM/Wm8elTxLtXcerV0HLuSKhY8A4HWnMei9q1QsdnpmcgySiskjJqIy5rmtSnyJdwxjGO1IcmnA4GKTGasyFjieQ4VScdcdqtR2B4Mr7QRkAVtWcdsbH9x90jBJ6hvQ1lTlo3aN+oOK5vbOTaR6awcYRUpa3BYYImA27s5wT60vnoshCoBwe3SqUkh25J5BqIyHeadm9xOUY7I0PtI3kgY54/z+NR+eh42g5JrP8w4680nmEDINUokOpcvNFFIw2naT+VQOhXPceo6VEJCBnPJ4qRJskbs7fSqTaMZRjLYRXKdKV3MjAmpHVXBePAHdf8Kgq1Z6mEk46MKAM0Uo9BTJEI54o7U7Yx7H8aUR88kUAMHSjmpNi49aXAzwKVwItpPQU4R+pqQbdwBYDnr6Vt6l4dFhpS6hHqFtcxHAxG3OT6d6iVSMWk+ppClKSbXQwdoHalOelNLn+ECkIdupNWQSHaOpFNLqOnNNKYHNKFA5oAQyHsBSbnNO9qWgCPaT1NKEp3YA0uM0ANxgcUYpSOKKAEqyuo3qRGJbucR4xs3nGPTFVu1FJpPcak47MQdTmjFABJp208dqYhvekzzTtoHrRwDwKAG4NLtz3pcnpnij8aAEwMUdBiijrQAZpPxoP5CkZ1HQ8+1AheKawORgc0hmA6Coy7E5zimBPnB6gfWmmRR3zUBJPfNJRYLkpmP8IAqMuWPJNNopiuFFJRQAUUUlABRRRQAUUUUAFFFFMAoopKQgooopgFJS0UAJRRRQAUUUUAFFKOtJQAUUUtACUUpooASloooAKKKKACiiigAooooAWiiigApaSikAtFFFAwpaSigBaWkooAWlptLQAtKGI6Eim0tAEgkYd6cJj3ANRUUhk4lHcGniRDxmq1LRYC0CD05o6VWB9KcJGHekBY7dKXPHeoBMw6gGniYehoGOJ2nI6HqKcNp6ioy6sMZpUbJwTx2oAdtQ9KDH6GnY6YoweuKAsN2N7GkxjrT+aO3egLDB1o9qeFHrRs96BjOgqrI3PJq4yHac/pVBh83+eaRcRuaOO5o96MUxiZHvSAFmCjvUot3cbjx6Zp627Rgt1PQBaCWRNyQgPyr096TOKkEUnQKasR26ry3LfoKdzO1ymSw4Ax9RToQXZkJ+bHFWrlQ4HIGD8zHt7VCrojDy1G7+83WmncGrCKryYKqzY4OBmpBZ3B4EEh+gq1bWdxeDcXYJ35xiup0bwLNqcwjSV1PHzswAGeh9aGwscdaxFvtch4EcJzn1PApsNvDLEzyXSRFc/KVJJ+lepXnwe1mBJSsUkwZRu2uDx1BrgdY8Lalo7MZYXKLycrhlHqR6e4qdyvkYmBxxWv4da9j1QSWkIlQKVuI3OI3iP3lc9AD/APqqnZWTX87AMI4kG+WVuRGvr7+w7mtKW9UQC0tUaKzU525+aQ/3nPc/oO1TOXRF04r4pbGjqV9b2lzcW+lyebbh/kmYYOOwx7dM1iMWZizEknkk04Op6g1u3tlpL6QtzbXAWYAZTPU/SsPdpNK251tzrptvY52ipDGc8GkMbe3510XOOwwggjII+tBrWudVN5o8NlcWiNNbkCG5Xhgn90+tZRFTFt7oc4pPR3ExzS4HrV2z09L2NljmVbkH5Y34DD2PrVWWKSCVopUZXU4IPahSTdgcGlzPYj70o4oPWiqIDoaVuOlKQAoPem0DDqakXBFR04HBzQA0DBp3GaOKX3oAU598CkFSBmKlc8HkimkYOKRVhB0xSYpcZNKATQIb6UuO9LjqKUDP1oAawwAaAMc08jIpOcUXCwh5OaKcVZQCRgMMijAxjvQFgHSlxilUZ6dqklhkhk8uVCrjBKn3pXK5dLkXep5rcRorBgc1C33qBnik7lRtZpo17TR0vtEluLdibqBsvH/eX1FZGK0dI1OTSr5bhPmXo6f3l7iq17JHPeSyxR+WjsSE9Kzg5qbT2NaihKClHcrgCgjBp4RiN204HfFIRn8K1uc9gQgHkZGKSj60vagZPaXMlldRXER+dGyPetnxBrVvq0VuY1YSJndkfpWCBxRWUqUZTU3ujaNacYOC2YGkpcUlamAg60tFFMCW28j7Qn2jd5Wfm29QKkurZ7OcxPzxuVh0YHoRVepHmkkijjZsrHnb7A9qizvctNctmMxRTgM0CqJsIpwc0+SSSaRpJXZ3Y5ZmOSabjJ96P50vMfSw3FSrBI0bSKjMq/eYDgUzjjjmtjTNZWwsLq1aHzBMODnocd6mcpJXirl0oRlK03YxjSYp5HFJ7VZm0AIAbgEnofSm4pcVq6Nf2lmZ4ry382GdNpZQCye4qZycVdK5UIqTs3YycUU+QKHbYSVz8pPpTcVVyGrMbS/SjFOIx3zx2pisNopcUYoASg0vpRQAmKSnYoxQAlX9Pu1tZCWXKtVGndqmUVJWZdObhLmRo6hfJdBVQYA6k1nZyaKSlCKirIqpUdSV2DDB60lL1oA96ozN/VdGsLLw/Y3sF35lxMBvjyP5Vz2OacFLEKMkk4Aqe5sLm0AM8TJnpnvWdNcitJ3ZrU9/3oxsirjmg0veitTESkxTsU4jblTwaB2I8UYp3TI9aTFACDgg4HrzSn5mJwBk5wOlJ7UopDR1Hgvw9/bmrDzQBaW48ydj0x6fj/Km+N9Xi1nWmlt1RbaFRBDtGMgd/wDCm2viCbTfDE2lW5iBvT5kksbEuF6bD6Hj8jXOucsea4oU5TrOpLpsds5xjSUF1IjScZp3ekIrtOFgxB7YpuOM08r2FL5bFN2DtzjNFx2bIsZPtQVwKccik7YzTJsRn2o+lKwpKZIlJ3FOFIaYhMUdhSkUAZIFA7CYpMVfsNOn1K9htLdC8sjYUD+dXPEGipompNYrdLcMijeyjADelZOtFT5OpsqEnHn6GJtO3d2zTCKmOcbe1MI7VomYtDMUueBSntTaYgAz1oxhqAcGl96AEPNaOjaU2qXojJKwqN0jj+EVVto4pHYSsV4+XHc1ch1WWz06axgVU81vnlB5I9KyqOTXLDc3pRinzT2INTS0S/lWy3G3U4Ut1NX/AA3ZPPdyXIRWS3XJ3HA+ufYVinJrp2B0vQorYFw9wC0qjow9/WpndRUO5VOzm6ltEVLuZru9eYsxBOFLdSP6Vz+oT+dc7UYmKMFVz+p/Otae5ENpJIuSQNqn/aNYax/uy7HAB5z1PsK2irIxnK7uMRdzBatAZqOFSctjBY8VYbCjaPxNO5KQwsxxlicdM0qjnJ7UmKM4+lAgfG7g/WgUDHelANAFiyvHs5xIo3KeGQ9GFampQJcWi3ducoBwe+PQ+4PFYgQ1paTM0dx9nYbopztK5xhjwDXPVh9tbo7sLXsvZT2f4GSzZU59ahZ8YHfFbOo2dlo9zLb3fmXF4jYMUbBY0+rfxfhx71RbVplGLWGC0XbtIiTJI9ycmtYq6uY1J2dii24KMqQD0yKQsOBmpGuLh8FpnOOBk9KjMrnq276jNXYy5xN3PtTt2B9abuU9Ux7rSMuBlTlfWiwKRNHKUYFTg1ZG2X5vu+tUQ2OlSJIVIOSKRe6sy2FQds0ucdBimAl13KT70m2mZNWHb/ekL56DNAUUuB6UCG5Y9KTBPUmpKQ5xQFhm3FOwAOlKelHekMRelLSL1IpaAEbpRj1oPSimAUUGjBpAJ2FFLtNBUDk80wGnkUuM9+KXFAFACbVB5JNHHGBS4ox70gEJPSkx707AFNLADrzQAEUYphk7U0yHscUxEh4ppdcdaiLEnk0maAJPNx0GfrTTIx74plJTEKTmkopKACkopDQIWkoopgFJRRQAUUUUAFJRRQAUUUUAFFFFAhKKWkpgFKBk0lKDg5pDHH6U09aXNIeaAEooooEJRS0UwEooooAWlIJ57UlKMigBKKD60UABopQCTQQQaAEpe1JSjrQAlFKetJQAUUtFACUtFFABRRRQAUUUUAFLSUtABRRRSGLRRRQIKWkpaBhS0lLQAdqWkpaAFopKWkMWlpKWgApaSloAKWkoFAxwYjoTUqSM3G7ntnvUNFIaZP5hHBGDR5o96arhhtk6dm9KR42jPPQ9COhpDt1RIHU9TzS8GoKXNMRNz61TkHJwuAP1qcMexpHG5cD8aRUSvHGztwM1ajgRDk8n3ojKouAKfvWgGx9HFNDA96d170CFzUFxMIlwp+c/pUjMEXLdBzWY7mSQsepppCbsOyz4zyBwKswBRyQCf5VXTA5qQP71RDZswXZIxkqp/u9q6vQ9ebTXWSBwW7kjII9CPeuAjl+bIJFWY7pkYFGKkUNAmfSWhfEG0vLaOK6BW5XCkKw59TjtirPiyPT9QtHk3xvJH8wIPzAEZGfUV8722rS27iQO6yA5+U4/Wt2PxVcTR/vZwX2kM5HzHPqe/HFQ4lpl3WPCC3Vhc3OiqEniJmubFP8Alooz+8QeoHVfckVwmAa7a28RNDqENxbuySowJI4rO8U2kEzR61ZIscN0f38SjAil74HZW6j3zU7MtO6Oa20m0inUUwEAbPXHPrVi9tZ9Pu5LWYoZExkowYHIzwR9ahpc560tbj0sMEh7gU4SjutKBnNGAaAsKJEznkGpJ7lrrZ50hcqMAnrj61esNBuNTsbi5tmjJg5aMn5iOuayivNSpRk9N0XKM4x12Y7y1PehoxxzTNp7UvzDuasyF8s+oppQ07e+ecGjzT/doAbsYdRRtOM08Sg9jS+Yp9aAGbTjNAHNTKy84PWgoD1ouFiMcdKcCu1tykkjg56U4oTgAjgU3y2/CkMbSjrijY3cUYNMAH3uTS0pqa32iVWcfLSbsrlRjd2IR6UY554FWbzyvN/dj646VX64qU7q45x5XYQ+lL8pUYzuzz6UEYNHeqFYVeuKnnuGuEiVlXdGuzcOrDtn6VAOtP21LKV0rDWHSkqaR3lwXOSFCj6CmEUJg0NApxPFOPQCm4NFwsTC7lWIxgjYRjGKgxVyy0+S/leKJ4ldI2k/eOFBA5IBPeqnakmr2Q5KTSbExSgc0AcUtUSbEOiPNpb3iuAF5x6isllxU0d7cR27QLKwibqueKjI4B9aygppvmZvVdOSXIrEeM8UEYxzTgdrAkZx2oY7mzjH0rUwtoMxSkUUuMnFMmwg60tFKPpmkM0dKNm04ju1+RuN3p70up6VJYXEgGGjHKsO4Pes4Vak1C6mto7eSUtHGCEB7A9qxcZKfNF6HSqkHT5ZLXoVaVfeijGK2OcVgufl4pKntbWS8uEgjxvbOMnrgZphiYJv2naDgn3qeZXsVyO1yMZxSYwaf2oxnn0p3JsMPWirFrZT3shjt42kcKXIX0AyTUGP0p3Wwcr3G0e4pxHTFJimTYSl7Yxz60pyevbikxQAlFLilxQAh/KkpcUDigBVxn5hxSNjecdKDSUB5BSgnGO1HpRQAoGaU5UbSPekoJJOTyaAEqRI1ZwGfap6mmYpccUmNCH5Sdp6dDUktzPMqiWV3A6BjnFM6LjvTaLId3shMcZoXg9OKP5U4Dii4kiZrdVg35O7r7VXx61Zt7aS5ZlXbhRuO5sCoGGDj04qU+hclpexHS+1LRjmrMxuOaUDP0oxzQOKQ0IVw1IRg0/GetNPJoAbinBcdO9W7Wy+0RO+/G3iognOMZxxU86vY19k7JvqRqmSMVspot2dO84f6s/w1P4f0Y394Cw/dIck11GuzR6dpjBcB2G1B6CuCvimpqENz0cNhVyOczzdosuQeMdaikQKcCp2Y7iR1quSd3NehG55dS3Qa23Ax171H0xUhHNPnt5bdgsqFCyhhnuD0NWn0M2m9SAjHQ0ooNX9H0m41nUorK3HzPyzHoq9yaUpKKuwjFylZBp+j3epx3EsCDyrdC8rscBR/jVAdRXYeJdUtdOsB4c0dv3Cf8fMy9ZW9K4/vWNGcppyei6G1aEINRW/U6/wnq1poNpd3TIX1CYeXbHsvqTW7q3ha3XSZJJG33hHmvMT1Y8n8K82DEd61m8R6lJpxspLgvERj5uuPTNclfC1HUU6b9TuoYqmock0ZMi8moSOcVMXONuTjOcVEeT1r0Y3PMna+gjKQ+1hgimsOfalPJ5oI71RmxtFOQlWDAZINDZdi2OvNMLaAGwDxyeKb2pdh9KXYaQGjoVib3U41IyiEE+57Cr2sXUc18qAux5h3nlU2uQduO3Srmkr/ZGiy37K2/YXGB0Y8ID+efwNYrhYIWba21FyzHuQxyB9TisY+9NyOma5IKPzM/VpmeZYfmJQlmLdSc4z+lUpX8xxjoAABTnYyytNKeGyevLGnW67n3seF/nW5zbssxbI0YYy2MKfSmbaflaNwHcCkA3bxS7BnpQXHrRv9jQAoGO1LTNx9KCWNAD8/hRn1NMwT3owaBk16BcWEUvWSImJz7dV/qKy+ufSuh0qwu9SFxZWlrLcTSqu1I03cg9/TjNbA+FHir7M1w1nFGo5CNKNxz6AVMNLoup71mcQUBgLd1YZHsf8/rUeM8AZ9hWzqWh6lpEjwXdvIhI2twCP0rKDSQ8A8HnBFaGREfT9KASpyPxFStIsiEEYccg0zqM4JoEMIwdw6Ht6U4H1NJjsTwetIOOtJlxZNHJsYHn3q3VDNWoG3Jt7ikUyXFFKATS7D60EjOaKeEHrS7VFAWI+4ozzUny/3aM+1ADADjoaXaTx0p+49hSc460BYTZ6mk2qKXbmjgdTQAmR2FHJpN6D1NNMvoKAH4yaQjpUZkb1/KkGWPWgFqSkgdwKYZF9c1oa1oV3oc0UdyFYSxiSOSM5VgeeDWUamElNXjsVODg7SQ/zcDgU0yMabRVkCjLHqaspZOwyRimWrKJQW6Voz3kaR4Q81jOck7JHVRpQceaTMmVNhxUVSSvvYmojWqvbU5p2voFJRRVEiUUUlAgoopKACkpaSmIKSlooASiiigAooooAKSlpKACiiigAoopVGWoASilPWkoAKSlxRQADrRRRQAqLuYChgQxB61LCuQx/WmS4zwaOo7aEdFFLimSJSU7tSUAL2opwUkU2kAuOcCkIxSg8044IoGCDmkfJNGSOhoHU0ANopSMGjpQIG5NJjjNLTj0oGMoopaYhKKWikAlFLR3oAKKKKACiiigYUUUtABSjrSUCgApaD1ooAKWkpe1ABS0lLSAdGwVwSMj0pO59KQUooH5C0tIKWgApaKKBhS0lLSAexQou3IbvTaSlBwaB3uKAMEk804O3llP4TzSYyNwpMkHikGwUUUUxBS0neloAKWkooGLS02g8CgCO5ciPbnrVQVYuF3EYYE9xUO0gcjH1polig880/OaipQSBTESK3PWnhjjioc4qW3VXcljwo3Y9fagdjU0zR7/VD/o6RKuDiS4mWFD7BnIB/Cq0vnWtw8M6MksbYZT2NQyFiQZX3fw9/l+lNkLcxucmMfKfb0pAXFujnrn0ro9DuBffaNNlb93dJtXJ6MOh/A1xqNWzochTUoGzjJOD71FTY0pr3iNo3R2RlIZSQR6Gm1ra/EYNcugAMMRIP+BKD/WszI6kVMXdXLlGzsMFSLHmMv6UYU+1L/DgHj0FDBeZHinumwId2dy5+lIVpNppgSQ3E1uxMMrxlgVJU4yD2qKlxRSsgbewnetfT7TTJdI1Ce7ujHdRBfs8Y/jJrJwaKU4uSsnYqElF3auIeaQil4oqjMbtFG2ndaKYCbKX5h3NPBG05602kFgDv9acJD6UlL+NAx6zAEHGD1pdyE9aZgUbRSGSbVbpinbcqBUWzPSlAYdCaBi7GPpR5belKHYHkZpwk9QaVx2I9p70uDUwZSa6XUbfTrvwfp99ZxLFdWkn2a7UdX3ZZXPr0IrKdXlaTW5rGlzJnKjrTscCptq4q1aaZc3pxBExH97HFOU0ldhGm3oimAVBA/iGOlOjtpJjhELe/pXY2HhPPEu6V0GSqr09j6V2+i+CQXWSYskWciIoAx/wFcNXHwjpE6/qySvUdjzHTvCt5fkLGRvxkr02j1JPAqxe+Fp48JHDsMZ2tLk+WffdXreo6hpPh6IW8UKPP0CK3APq5/p1rzXxN4onunYNKxlxgKPuqPYdvr1+lYU8TWqz901VOmo3asjmbmK0sUaJMXE/3TIwwq/7o7/U1mHk1JIxdyzEkk9zUfevVhFpann1JJvTYRSQQevtQfeirMskDWsSJEVlX7zZ61bZCV09SsBzU7KMcHOBUNSZOMZoYkMNGOBR3opiE6UopcUuBgY60xWG4/KlJycmnBQeuaAOaVx2DFOUDv8AlVg2y/Zkk35dj93HaoCMHHpUqSZbg47iMBu+XpRjigDnFB60ySazuGtbyG4XrG4arheC4uL9IiFikBkjDccg5H9azsZpKhwTdzSNRxVhO9LRS4qzMVHeNt0bMjcjKnBxTCKkbn600KT0FAWJLY263CNcxySQj7yxttY8dj9ahI546U8grlSCCDyDTaBPsIqgsATgZ60pXk45Ud8Uu04zRkhSuTg9RTCwoceQyeWpO4Hf3Ht9KZjmlxzig0AxMUmKcOlGOKLisEiqr4Vtw9cYplamm6R/aCTSNe2lrHEOWnk2k+wHU1nbctjP40ozTduxUoNK43HAqZFg+zuWLedn5QOmKiANSRRGRiBjgZ5NDCK12GmJwm/adhOM0zFaNxdRNZJAiHcBgk9BVDHNEZNrUdSCi7JiHJwTR7U49qCBjNMiwzHNTW7RxzBpF3Lg8UkSeZIq+pArsfG2hWWkWmmPawiNnUrJj+IgDn61hUrRjNU31OinRbi5rocXLteVmRdqk8CpIJfKfOxXH91hx0qPGDT1CkH1Favaxmr3uOSKSZiURnI54GaidSGO4HPvXpngm2t/7FEoVDK7necZP0rnfHEdnFqyrbKquUzIF6A1xU8ZzVnSsdtTCWpc9zk2x2pgHNPPpSAetd9zz2tRCOaTFWba2NzMIw6JwSWY4AxURUK2OuKXMth8jtcj7UoUlulLilU7SD6UXBLXUnFvPHkYYbuoFPt4WkdUUZYnA4qT7c/2cqpwTwfWtvwlbJc6gZpedgyPrXLVqOEHJnfSpxnNRTOv0bT49O01Q2AcZY1w/ibUjfX7qnMa8Cuw8TamLDTzEh+dhivNDM6yrKrEOrbgfQ9a4cDSc5OrI7MZVUIqmis/B78dc1G3PNbusXNlq1quoKFg1HcFuYQMLL/00X09xWHg9K9enLmWqseJUjZjcEqWx060ssjy4LuWIAAyc8UYNJt9a0M/IiqaC5ntizW8zxllKkocZHpTMAd6CQOhoaTVmJNp3Q3BPrRtJ7Uu/wBB+dG4n2pgLsOaTb7ipYLae5fZFG8jYyFRSTio2jKnBzmpur2K5Xa43aOpNJhR3o2ikwKohhlBjpSFlwB/SlwKTA9KYg3jPHSjf7UYGKQdaADcfSrWm2pvb+KEj5Scv/ujrVbFdHotu1vplxfYxJINkZx+A/X+VZ1ZcsdDWjDmlrsifXrxxGmk+W0SHE7FxjfgEJj25rl9RmLrHGmV8w72U8YwMc/jk1q6nJ5+oOcfMIlWU7slSgw2c9+M1zdxM1zcPKSfnPGfSqpxUVYmrPmbZGQNxAbd2BHeriR7UA/OobePL7j0FWqtszSGbeM0oUUpGBigdKQBgDFLigc0uKB2E4opaKQwxXQ+F/DD67ceZPIYLFGw8g+857qme/qeg/SszStObU9Qjtg2xDlpZP7iDlj+X64rqn15YdlrZq0UEY8tIh/Cg/qepPrUt9EUlpc9R0a70XQrJLXTrQLEBk+WRuJ7liep46movE3jy1tWNtYybpgONmCOnUn+leQ3viGY3LvuAC8om3v71jSalIy7E4Q8sT1P41SiQ2butaq11MXlyW6sjHAAPtXH3ao8h2DH06VK0mSdzEgcVXkdTworRIhsqMCDTo2XOHGVPcdRQ5yaj70ASuhRtrcnqCO9MI+bn61at2Ei+Wwzt5GR2qb7PGSMrx6DipbLiigPap7Z9swB6NxTZofLbI5XtTUB3DHXNSaHTaXoVxq1pezWzoZLRA5h/icd8VlYwa0ND1640HURd26q52lWjf7rA+tZ9xcGa4kl2qpdi2FHAyayjz87vt0Lnycia3E75oxUZdvWmlj61qYktBKj+IVDSUAS+Yo9TTTIewplFMQpdj3ptFGKAEopcUuxiCQCQOpA6UXCzGUoPNBpKA2N+/8AEQ1HwvZ6XcQFri0k/dT5/wCWf901z5ooqIU4wVol1Kjm7yEpKWkrQzDNBbNFIaAuJSUtJQISkNLRTASkpaSgQUlLRQAlJS0UxCUUUUAJRS0UAJRRRQAUAZNFOx8pNADe9FFKBmgBtPj+9+FJt96VeN30oAaetGKKKACkpaKAEpQMmkqSNctk9BQApJRdo+pprkMRj0ocYP1ptAMQ9acDSZzSUABowcZ7Uo65IoZsmgA3EdKQUUvSgQuQOBS9RQignk8UrDY3HSgY3GOtL1xSnBGaE+9QA/arJ059ahFT4wCM1D3oQ2FGOKXFFAhtFKoyeamMaMh2HkdqAsRKuTSEY4pQcUlACUUtORdzY6UANoqSSPYwx0NR0AAGaKkjXLU1hhyPegBtFLRg4zigAooooAcRlQfSm09TtpXXgMOlIBlFLRQAlLRilxQMKWkpaAClopQKACilxS45pDEooxRQAUtFFACqxU5o60UUAJTj97ikpT1oAPaiiigAoprOkeCx/D1qM3ce7hGAoAmpsjhF55PYUwXCPwHCk+oqRLXcNxJK/wB4c07Bcq4LHPWnrkDGT9O1X1055FDRESZ7DrUT2MiLkhlHuKZJV2qeSv5cU3ah7sPwzVjyTGQWOM1CRk8ZzQMbsXH+sH4g06Jlif72QRgkDpTD1pp6UgRaKjILSow7BT1qMyB7nceBnFGPKiAH325NMxgjNIoVM10PhsRTapaxyuqDeFBY4AOeOffpXPpyxAGTnArSshYJciK6mlD7gC0YUqPUc/zrOqrxsa0ZcsrnSeNY/s3ieWE9Y4YlYjuQoFc/uU960/ECN51rMWdkeEIjPjJCcDp1Pr71jVFFe4jSt8bJsjtQcHGB9ahzQCfWtLGNybJ9ae23C7WJ45z2NV9x9asWd5JZXKzoqPjqki5Vh3BFJ3toVFq+omaMn0rR1GOwmthf6e4iUsFltHb5o29V/vL/ACrL8w0oy5lcqceV2H5B7UuR6GmCQehFOyBjtn1pkDkQSOFHU0PFscqeopARnOeaDzznJ96Nbj0sJsB70bPQ04qVAJ4yMigKcE9h1ouFhu0+1JtPpTqUH15oCw3B70tOzS4BxxRcLDacuNw9KXappQo7GkUhzdqQDpShT604KelSaWuCgE44HNKyjIx+NAHPNSIjM2FUsfSpbLSvoRbc1dsbKa6cICyxseuDzj271o2mhSMuZ+G27lUcjHqTXV2ViZ44Y7eFNwwNoUgye/riuOvioxWh2UsK95GPa6PbWsccksO5gcZf5sn6dOK6rSNEurxjHbxFEI+Z24wPTp+ldBpXg9nmE+oEEBRthTgLW1qeq6d4dtFeVkjjX5QPf09Sa8mpiJVHZGzrRh7lJXZVtdHsNBtvtN5MHZFz5j9B9BXNa941eZXt7FzBEw5Zfvkd8n+EY9Oa5DXvGE+q6hLKGbyckIiEglemCT0rk55ZJjl/m9BngV0UMHKWsyG1H3p6s2NQ1tGTy7YESZy05PJ/3R2+p5+lYbYYc85681GQc0wrzXq06UYKyOWrVlN3ZJsB6DpTfLX3pmCKTnPU1sjnY7yx60eX6EU6GKaaVYo1Z5GOFUDkmr++HTXKoI7m6H8Z+aOM+394+/T60nK2iGoX1ZTazlSNZJEKI33S3G76UzYQe9PknmnlaWVmeRurMck0sSyTSKi7cnpk4FNN9QaXQi2HPSl2H0pdzUodqdybG7rOhWOn6VZXdrfrcPOBuUEZB78elYO2po3Bb5gAPXFTl4WmEZJEIJw2Ofrisoc0VZu5tJRm7rQ2D4QuH8Jxa9azrOhyZoVXmMA4/HHeucxjg102jeJ73RbC6srZ43guUIKTD7hIwSPwrIW2zEx2N/st296zpTqJyVTboXOmmlylSKTy3U4DLuBKno3sa6dtCtvEFu99o6rbBFVGtnbJaTGWI9B6VzTxYYg8H3rR0HWJtCv/ADkyYnG2RB3HqPenVUmuam9RUnFPlnsZDIVYqwIIOCD2NIRzVu9dLq+nnQFVkcuAe2TVcp71vF3SuYSjZuwykqTyznrRsJHUUybDMU4c98UoQ+tAQ0AC1q2CwiwuWbHmjlfUYrL2mtXRLNb67a3d9gZc5rKs7RudGH1nYypSzSszHLE5JqPFaGp2ElhePDJ1HIPqKpbTitISUkmjGpBxk0xqnbSvtJ+Xj1o2GjYaokbijGadtNLsIxRcVhlLUixlu+MUm2lcfKxmBQKsR2s8pAjhkYscLhTyaSS3ljYrJGyMpwQykYNHMh8j7ELJjBHQ05XIXaOnWnbGxik8s496A2ehNa26zltzYwKrzRiOVkByBT1DryCR9KQxknk80ldO5UmnG1tSLGaXAqUJj3pY4PMcKCc1TZCiRxttYMOoORXSeJ/Ea+IYrGOOJkMCHdu7sfT8q5woAxAORTl+Q5DY+lYzpRlJTe6NoVHFOPRkbxsj4YEH3pv8qmdg7ZZsn1Jp8htPs0Sor+cCd7HpjsBWlyLK+g621C6st32a4ki3dQpxmq8sryuXkcszHJJOSaQFB0FOd42OVjCj0qVFJ3sU5ycbXIeOueac5jKrtznvmnbl/u0m5f7tWZjM4qWKNJFkLSBSq5AP8R9KbuHTb+lG70FJjQ3bzRt9KkGfauh0Tw6NY0rULiOYi5tgCkQH3u/NRUqxpq8jSFJydkcztI7Vp6Pqb6bKzdmqg5IJGOfeo9xpyipxswhN05XRpapqU2oy75Gz7elZu33pWxt++SfQUzAPrRCCirIVSo5yvIlihaaZYoo3kkc4VVGSahk+RyuORxXRWlxFoWifaIyjalfIQjA5MEXQn2Y/yrnpG3NnHNEJuUn2CpBRiu5ASfWr1zbwwabAQQ00vzHnoKp005rRq7RjGSSem4zbzSbafg9aTFWZWG45pcUUooGja8Ma4NA1qG+aHzUUFXQHBII5xVLWL2K/1S5uoYRDHLIXWP8Aug1VYDC4OeM0zGQTnpWSpx5+fqbSqS5eQYetJTjSH2rYwE+tPlaMkCNSoA6k8mmYowaADFN707BpQpoEPt4GuJ0hQfM5wK6S/mFvELRQfIWAFVUcllYHPtjFZ+jqLWKbUXXJjUiMerVRku5Li8aaQliQVwDwF54z+dZfFPyRv8FPzZUvG8m0A3KzTMSrchtnPJ+prOxwMdT0qW5l8+YkHEa/Ki5ztUdBTrWPfJvI+Va32OfdkyJsQL+dOqUIAaMKD0FTcdiLrSgH0qTgUoPOe9Fx2GBD6U9YXbsTSjnvWx4eubS21Ldej9w8bITjOM1nUm4xbSNaVNSkk3YxSmO9AQVZuxGLqUQnMW47D7VDx3PNNSurilCzsdHpdubPwpe34X57qXyEP+wg3N+pX8q5u4umEjMGIY9TXbTqqeBdFi5/eLPLx6mQjn8hXns7YORknvmsKFTmlL1OivT5acRjzEnOTmozKWwc8+1TwNFAgnlQSPu+SNvun1Le3t3p1whvpXuC1lbyO2fKT92o+g6D8TXamee0VTIeM9aZuJGM9aa6vFI0bqVdTgg00seopiHhdx25xTXXY2M03NIST15pD0sTQttcN71eI56ms5OmPWr4OUU+1SyogQDweajWIK2RyKkopFXCnvIXSNTj5BgYGO/f1plFAXEopcUu00BYQj5Qcjnt6U3FSBCaQrilcfKMxSU7FJTFYSrVvJF9mlhaLdK7DYw7VWozg8HkUmrocXyu51cPhqw0pFuPEd6ISRlbKA7pW+uPu1DqviqOWwfTdJ06GxsXGG4DSP8AU1zTSM7FnJZj1JOSaZWKoXfNUd/yN5Yiy5aat+YGkpaSug5RKKKCKYhKKUDmlxkUANxSYxT8c0mKAGGmmpGGKZQIbRS0lMAq5dWBgtYbhW3RyD8jVOntNI0QiLsUByFzwKlp3Vi4uNmmiOkpaSqMwpKWigBKSlopiEopaB1oGJRWzrmnx2qWk8K4jmjHT1rHqITU1dF1abpy5WJT/wDlmDTKljHytVEIipR0pSMGkpiDBzUm35SPahAApY9e1IXJHHXvSGR96SnEGlVdxxuA+tMQyg0pGDiigAALEAdTU5wihRTEGELd6QsTzSGtBrnLU5VG3JqOpP4PWmCGMBninKBjPemmndEAoEMNJTsHGabQA7Hy5oAzxQOuO1BGDigBwGw/MKWRgzDHQUgbs3K/ypCMHg596Qw/hpVDDBFSpCGHJ5pi5VipouFhC+Rx1NMp7rhjTQMnimIXtSGlA5weKeygLnvQAxetWGICMagUbj708KxwGPHYUmNEXpTtoIoII4pQrYyKAGhGY4AqVQsR65ak8wKuB1p2Mgc5JPNA0MlYu3SmYqWUEEH8KjAZjxQhMUEJzTOppzIy/eBFNpiFHWnZG2kAzTgARSGhlLQRg4opgFSxH+E8g0wDmpSQoFJjQkgUKB0IqLipnO9N2OR1qKhAxOlLTgvyE+9JQITFLRSigAxTgOfekp6n5SMDnvSGGKAM1LHDJKrmNGYINzY7CmFe9K47PcYw4FJT3FMpiCloooAKKKWgApSKSnYzQMebeXyfN2/J61Hip3nleMRM3yr2qGpV+pUuX7JUu+q/Sq1XbhC+AMk9qiSEjkjmrTIsQiNjT4nlgcPE7Iw7qam2MegJppjf+61Fw5Ta0nxBaQzoNWsDPGD/AK23fy5B/wCyt9Dj610mpTaPqUSto0xlTZ+9VhtkJ9Sh6Y9sj3rz0j1FICyMGUkMOQQcEUCNKdHRyjqR+HWqsnAGRircGrJMoi1JGkXtOn31+o6N/OprmyXyVljmWeE/clToPZh1U0wMk9PxpYV8ycA9ByfoKRwVODT7UkeaR12f1pAhHbfIze9J1NIvSpFGOaRS1JLSLfcKMj76jP1qBIj9qETgg79pGOeuKu20DtvwOTGXX6rz/LNbMVoP+Eij1Rk32oh+3v6ZHG0/WTA/Gs3Us2bKk2kR6oWSeK1kAV7WJYX2n+MZLfjzg/SqkkJRQwOVPemSSPNI8sjFpHYszHuTyTTSTjGePrSimkhykm2JRRRVmQUUUUALS0lFAyQJ+63574xTcZpV3MpA5A5oVyh470itBKXNITk5ooJHbm9aUOwGM0yloGSbz3HFKJPUVHk4A7CikMlDj3p4ZT3qvmpUERicsXEnG0AcH1zSY0SjHrTgPSq4pwpFosKCc1Y3x+TtC/N6nt9KbZ2U90RgbIupduldFp2mW8TZRQ7JjdJL/wCyr/jXNVqxidlGlJmZaaNc3KecymOEDduYckewrorLSFtdq/dZ+AnVnzUvmTTSi2tzIwBONi53n39a6/QPB0jkXWrMwY4Pk55/E/4V5uIxTtqztjCFJXZk6PolzqEjLHGFgXKmRs7Qc/qa9C0rR7PSYsqu6Rhy7/eP0pbm7sdH05pnaOC3hGMj+QHc15lr/jm71FnW2kNpZEFcA/vJP8K4IqpXemxlKU62i0R2XiTx5ZaarwWr+fdDgRp0z/tN2+leP6tqV7qd2097MzuTwCeF9gO1QG4QSFpEZh12Buv1NVpbhpW3N+AAwBXrYfCqnr1IbhBWiMeQ4wowKj8wjryKeWGOeDTcrXckYSkMLA00HmpAoYgDrmppLRogNwIyP8indLQjlb1G3HkEJ5Od2PmyaZb20lzJ5cS5OMkk4CgdST2AqSC1kuJ0hhUtI5wB/X2FXbiKOO3+z2sq+Tn95ITgzMPQddo7D8fTEuVtEWoczuyK4mtraNrewZ2BGJbgjDS+oUdk/U9/SqibNwypYZ5AOOKFQ9uPetazsbG5026lN15V1CVKRuMrKO4H+1+lS5KCKjFyZnssElwdgeOM9AeSDjgfSnmxIYrvRl/vKcipt6QqAseJRnO4AjHr9ajLu7Z3NnGMCjmfQpxj1HpYqy4MigjnlgOKd/ZMrQiVAzD/AGRuGfwofTbqOOORoGCSruQ46j1pFhntj5u4wsp7HDCp5n0ZXIusSG4sniAdEYxEZU47e/pVbb612mj+KlXdDq9qLqB12s6DD7fQ9iOPrWZe+HXIku9ND3NlywaNDlPZvTFTCu0+WorCnQT1gYGDkEnjOM1pTNbwJF9lkYSg5LBuD+HrVcafclJJFgfbEMucdKrhCzADkk4xWrtLqZq8OhqtdR30MMUxRJY+AwAC49D71Wlso3LfZ/OdVTcSV6AdT9KpuzBsHqvBq3BOCArfJgYBXuff2NLlcfhHzKekik8W09c+470zbz1NaMVo1xepCWjiMrhd7nCLk9SfSq9zB9nuJod6yeU5QuhyrYOMg+laRmnoZSp21K2DjrS7T6mnAU6NmjbcuM4xVXM7EWD60YPrT8UY96dxWGjd61LDNLbyrLGxWRTkEUzFKqliAAST6UnZrUcbp3RNe31xfzebcNufGOmKrcnmr9jaQ3M5jnuo7YYyGcEgn0qtPGIZnjDq4RiAy9G9xUxcV7qLnGT95kYjkKFtp2A8nHApuD61KGfaUDEKTyueDR5Z37Ryc1dyLEeDjrSjJ6mlpyrk0rgkTWdpPeTrDboXc9h2HrXe6Z4asdPkjFyglnK5O8ZCnGRj+VSeGNLj0zSxcvGpupl3q5/h/wBmq19fNJGZIzztBGeowa8yvXcnyx2PYwuFSV5GpLfW9ulvEiKI0Mh246Y6VCt9DdyTCaKN8Rlm3KDuY9/yrm57vfdrzlWUmorO5ZlmwclowM+9ZJStc7XThsGpaNbNbCe0fypMDMZPBOe3v04rm3DqxVsgg4I9K0ptQL6hHAGJiRgoGepB5P51b1uzTyUvYuA5+f03H0rto1JRajPqeZicPFpzp9Dn+SeppMH1NS44zTotgcGRSV9K67nncpAVJPenxK+7KEgjuKew3EkDA9qs/YbmKEz7GCY5NKU0tyo023dFAqQcZpzkyyFjjcewGBTtuWxSyBFkIjJKg8GncmxEU55zSbBT+pqWGLfIq+pxQ3ZDUbvQg2DFKBjGApxkcitu/wBH+y2qzL+NZGD0xWcKqmro0qUZU3ZkOzBo2GpQuOopdhdver5jNRIo1YMCo+YHI4qa5me7vJJ5du+RsttUKM+wHSrh0u7isYtQKFYZHKRtnBJA5xVUwkEse1Rzpu6NfZySHqqYwafa6ld6XcNJZTtEzKUbHcGqzMQeDURyeTS5E9HsN1LbDHO4knvTKeRQgAdSwyueR61stDnerI8Udqe4BZtowM8U3FMVhvAPPSkfbuO0kr2Jpdua0JNCvodMXUJohHbvyhdgC/uBSclHdgoylsjLpMU8/WhULsFB5JwMnirM7EYB7Z57UFSjlXBBHUGpHXY5XPKnHBp007zKokIYp0Pc/U0XCy6kGBQFzjml61LLbyQFfMGCwyOaG+gKPUvadod5qUcj20e9YxlueaozwiF2RgQynBB7VYs9TvdPD/ZbmSHeMNsOM1UklMjl3clickk9TWUVPmd9jacqfIklqRke1A4INLle5qWRIlgDB/n9PWtm7GCjfUikcu2SB9Kb1NN3j0qSFkMyB+ELDcR6d6HohJXZof2HqP8AY/8AaptXFkG2+aeBms4IzOEXlmOAPevQPHXiaxn0y00TSmVrWJVaRk6cDhR/WuR0aNPOlvZf9VbLu57t2FctCtOVNzmrdjpqUoqajETV5BapBYREgQrmT3Y/5/WsKaQpkAcsu3NWZ5mmlklkPzMxZs1nTOXkJIx7e1dVOPLGxzVZ80rkecnjv0rSiVY41XIz3+tU7dMsXPQdKsVbM0Tbk9aPMX3qGilYq5L5oxwKPNPYAVFS0gH+Y3rRvb1NNpRQUhck9805AWYBQWJPAAyTTRVmwuTZ39vdDrDKsn5HNTLYuKuzotdnntvDem6bJHJHLawkSAjGGZi2PyIripcn6mvR/F1lHNdSXD3aQ2luQjyEk8HlQo/iOO1cNewwtGLm1kaSFnK7nTa24eo7Vy4aacb9zsxMHtfYzJCDMB0VcLSt95t33s8Uxxyc9c04yv5WVwGH3jjnHrXcjzHuMmDPIBglgoFIbeXqU2j/AGjimg85JOfXNSIF3AkZqiRBASB86fhzTTGAe5/StixskuZlR2wpPAJx+dbt54RaG384Kq4wPLBy31x70rhY4rkdBirVuwKbe4PSp5LMLkbWBHYiofszody54oY1oS8Y96TFOBjK/M4RvQ09IGkwIish9EbJ/Ko2NNyLBzgc+lGK1dM1E6R57pao16y7IpZOfI9SF/vehPSqMb7JRIyJJg5Kv0P1qVJ3ehfIrLUhAqRFBGMc560gAzyanjIMgYcc0pPQqEbs6/wd4ftrmK+1XUIw9lZRE7W6O+OB+FcfdAeaxUAAnIHpXdan4i0+28FWuh6axaV/nu2Axz1I9+a4SVssa4sM5ynKcvkd2IUIwUEViKQin4BNPCAHnnNd9zzuW5GkZY/TmjySBl2VRnuealaRo12rwe5H8qrsSTnvQrsGkhzpGqja5Jx/dwKipSSaSqRDEpKWimSJRRS9qAEHWnHpz3oA5FKRnFAAR6U2pFRnfCKWPoBmr8ejXDJvlZYlAzlqTkluUoN7GS4ppreWKygQFfnOOW7H8TVCae1DEJAr+9JTvsOVO27M80lTNKGPyxIv0FRknpVmVhhopTzSUwEop6plc5700jmgQ2ilxRQBatLQTK0khKxr39aquFDnZnbnjNW5rnzIUijTYigZGepqqetTG+7LnypJIbinIoZwCSBSU5PvVRCJJ7iaSNIXlZo0+4pPSq9Pb7x4ptJJJaDlJt3YlTREbWzn8KiFSbHVcjuOabBDTwcGkVdzACg9alUbEJPU0AMkI4A6VGKUnJooEw60lKKSmIApNGMHFPH3RTDzSAchAPPTNErBm46Ug60EY4zQO+g00ZOMUUY55FMQlSKMpUdSJ92kNDe1NNONNpiFo+tKo554pX+9QA2lAyaMHGe1KnWgCwuGG7AqAnMpPvRnBO0nFN70rDbHucgA0RDLZoVS3JyRTmxH908HvQHmNfJbPbtQ5LAGjjb70KRgg/hQAgBJ4BqZCWG1uvY0kRxzg5zTnwz5HYUXHYY+cg0m7PFSHawP94VFnOBQIaBzUxdTjB703Z8u7P4UEBhkUD2JW6ZqFSckijedu39aSgB8r7kAI5zUVSYyOaaRg4oExc0qkDgnFNwaeIwUz3oAa3LZFJQKXHpQA8bQM9TTc5zmnAcHmkxikMVOvXg01lKnFKOO1P2lzkCgLXExiE1HVjymI5Ix3pDbnPDLSuiuSXYhpal+zyAkbcn2qPaRwRj607iaa3HCPjNIvXmnZO3rTff3oAuWF41lc+Zt3qQQyZxkVC5Du7BdoJJC+lN285pWz+FTyq9yuZtWEYErUdSgnHNRsNrGqJYgp2MkADk8ADvUyWpypmcRKeQDyxH0qddQFgA1ivkyg4MrDdI307L/ADoFccdGu4YllvPLso2GV+0ttZh7L1NTad4fudYuBFpjeco+/LIvlRr9S1UWI3NdahI8kjc7XYkn/ePX8Kbc+ILyaH7NA5hh6FU4J/Lp+FFgudU/hnw3paka34vgE6/ettOgM7A+mTgVQ2eDp5BHbX+ug+r2kb5/ANXPWltEjBrgbj/DEO596tS3boWhgZI0wNzRrgj/AGaLDLktnpkU0qHVHkVT+7MUGSw91P3TWdIEV2Ebl0B4crtz+FRFhGuScA+vf/Go9zyn5RgeppWHce7qvVuaNsjJuwEXsW6n6CkXy4sNkFzyc8mntOWAcHZt9+aAHFEiQGaRgT0HegS2oACxTH1O7FQfast9wO3TPrVmDTL+9XKxhEHduB+dHqNPsJ51o5G/zkHqADUkdpZXA4vY0fsrLjNa1j4KnuYjLLcrFCoy8zELGv8AwI/0qynh3w2Mp/aN9eyg4xZQ7lP/AAJsClddCrPqc7caHcIN0RSYdyh5H4VSgnubCZjGWRiNrKRww9CO9dqvhnTxj7NaasGx/FKi/wAqJvDUUiCOSx1PpwwkRyPzppvqS4p7HGyGO4QNENrgcof6Uyz5eRTxla1tR8NXNo2+286VQM4eExt+HY/hWNG5S5DsMEHDDpVbkWsOXoB6VNGm4fjzSSoVnb3NWIUDgjt2A71EnZGlON2XbJ9l1bOq5IlAIx1U8EflmtG5vHg8L2engKBcSPMW/iMattQH23Bjj2FRQ2rOYLZWCSTEjd/zzTne5/DP5Gq2pXaXl68kSlYFAjhQ/wAMajCj8ufqTXOlzSR2TfJFopmkpxpDW5yMTvR3opSCDgjB96YhKUdetJS0CDBFFHaloGFFFLQAlLR2opAFFFLQMKmjtpJI96jIBqEVNBcPCTtPHcVMr20Lha/vEeMHFSwyJGXLwrJlSBuJG0+tNOZGJH1NTWtq91LsQcDqx7Um1bUqMXfQbDDJO4SNSzGug03Q186JZCsssh2qB0B/rUKpHEgitwWwPncdz7VpWFvNPci3s43klf8AgTlh9T2rir1nbTQ9ChQindmlfWEOkFUMpeQDlsZz/s1PpmkXeuMC8DwRIQXYggsD354rS0rw0vmb9QLXbIcLDE2QCecs3tXSXGo2ul24a7uIokj4CE4AH06sa8ipiH8MdWdzVi1pml2GiwpyDMRhNxyenrVDW/iBp+kxuiOLq86LDF91f95v6V57r/jaa9aWGwDRREkecx+dh7egNcrnA8yUnnovdv8A61a0cvlN89b7jkqTjfuzf1fxNqGtusl5IoiQnaijCrk9vU1hSXJLtszg9z1NV5JWkOW7dAO1IOh5r1qdGMFZI55VnLREvnMOwo88+gqHNArblMnJk3nDuv60eapPQ1FngCjjPFFhXL0YVVSTzFBJ4HerE9z5qBAQe5zWfHKUV8BfmXBJHT6e9XLEpFFNNIgYgAR+79R+A6n8KykurN4S0si3Iw060NshK3k6/vj0MaHkR/U9T+A9apxpwZWzsB5b+gqtI7SSF2YszHcxPUmr8W4oLiUIZNu2GPbgAAY3ken8zUtcqGtWSSRlH3XCfvHG4Q42hR2Le3tU0JAjZBCokkBXe7bQuT/CPp/Oqsc7SAxBn25LEtjPTk5+lS3F/cT2sVs7r9mgLGPABJJPPPU1DTehqmlqIYEVuZ4s56K2akVgp3RTxRnbj5Scn/8AXVF3APAK442k80skoChI3crgMSePm78VfI2RzpF5Zm2OHk3KPmUCShp0eOMxmc3HzeaxYFSO2KoQxyzOBGryMAWwBngDJP4dabvAPrR7NB7Vm1ZNYiYC85jkXBaLJaP1IHc/41aTVruG5ZrO6lEZ45XqBwNyjjpXOidmbOeeldj4K1bSrB7z+0HjikZR5byLkY5yK568OWLla5tTqKWhi3sryQhoGMaEBZEVyQ3uPQe1ZQUZO7OMduua3tU1G1udWnmso0SFiPk24VsdTimWulwT3sRLN9mkcg5IDA+lVTqckLyVhVKfPLQwAvPNSRDJIJGACeta2v6fbabqJgt5CybQeeSp9KzHl3+X8qLsUKNoxnHc+preM1OKaOaVPklZlhCjxhSAD/C56gY6YpslvH9mWSOXdJzviIwVHY+9XrHR7u/s7u9gUGO1AaU5wRn0FMiCSZi2APj8WHfnt61nzpPTobcl1qZO32puCD3rSu7J7Sdo5CMjoy8hh2I9qqHAGMAn1raM01dHNKm0QYpMe1SkA9BihU3OFHU8VdyOUixT43ZG3KcH1FSSRGJ9rdRTQKV7odmmPxEY35YyZG3HTHfNQkVKFppGDzSRTRHRjFO4oyMAY6VRAlbXhzThfakjzEpbQ/PI+MgY5ArHGM12vh1EtNCldy6TSSbgSvAx0z7VhiJ8sDpwtPnmaWqal5cikJlAOxzvX29K5bVLopKSJB84JJ7cj+Rpl5ebA+4lX7gHhuTyPQ1Shmw6MIxNcHmGNxlY16l2H8hXJRo31PVrVo04k6QX8kKXMdncvFGuWdYiRg0iSrbaZJcZzxhfr/8ArNWLTVZrW8DPqlxFdLuKFZDnP8O4HjHtV3xgulT6Za3kWo29rd3B33On7TiN8HdjHGCRwPeuh0uhxRxb1ucZaswnDAEsOn41s3F7JNClvuJXqw9T2/KqUVl9miS5E8NxFLu2SQtxuBwQQeQR/UUE8+9a8icr9jGVZqPKuokiMjFWBHsajqcnecsefeoiOcVojma7CLkHNdBea3DLpIgRSZnGHyOF+lYHTij0qJ04zab6F06soJpdQK5PBpNlOz6U9F3ZIzwMmruQlcjCCpY0KMGweOakjIBGRx+tXUlUWzRtArFiCsh6ge1ZznbQ3p009bm7dyxz6MRkZKZrkCOa0POOwpvYD8warvbso3dV7MOlYUY+zujoxEvaWaRX2+tSxopHGc1ZWxnKsVjLKpOSPpk1YbTHUnyctH8v7yQbOv1q5VY7XMo0pb2LVzqBvIIRINsMKBI0B4UD09z1p0em2V3p8lx9o8tlHfpn0qilvGIX8y7iQ4yqLliSO3HSpbXTkuFYNOwbjaoThvXJ7VztKK0djqTvo0YxRQecgeoFRMtbNxYx7iqNOVRcksgGX9B7VnPb4UsGGM8AnmuqFRM5KlJopkVLbywwibzbdZi8ZRCzEeWx/i9//r1cea1/shbdYD9r80sZjj7mPuj8aqJAZQzE4Crkcdfar5rrUy9nZ6FUikK8CrzaZctafa0ilMGcb9vAqgwI4zVxmpbGUqbjuhDgUrzM4Ad2YKMDJJxTduFzTMZq9CNUIWFJuFBBFNIzVIzaFaTIA2gAUwv7UoQn8OtLLBJDs8xSA67l9xT0E09xm80PI743MTjgZNIaQ0ybsSkpetGMnA60wEoySME1I6eVujdMSA+vT2qKgWwUUlLQIXdWwbi3/saG3HnRo2TgAESSepPoOOKxTV+ZvK0yziIyxLzfTPA/lWdRXsb0pWuZU0hCj5jhskj+lV3GXAUk5A/OnSuGk4HC8AVNFCFwzDLnn6Vtsc27HKuxQo7UtLiikMSiiigBaKKcBk0ikIKUVZmtTHDHMXUhx0HUVXxUqSexbi4uzFFOAzwaQVIopNlRWp1PikSal4Q0y9RmMcMSM6jp5mTGxPv8q/nXOrb+V4XgJHz3Ny7qP9hFAz+ZP5V1vh8JqnhXUtHbl1DOg9mAx+Tqv51k6hADqi2cQBg0u3S3JHQtjLH8WLGuGnU5U6b6P8D0HT52p91Y4xxhyPeljUFwOzAg1YuoispBB9KhgH75B33AV6MXdXPLnG0rFUDDY7g1PGBkU2VR9rlHYMamiCA+ZIxSHPJ7ke3vVmVjpPD9qszI5JUI4OzOC/v9BXVal4s0HSNPW0LC+uEBHkWrYAz2klI7egzXmU+oySRfZ4AYbfP3Qfmb/ePf6VXSIkdKTXcpeRevdbu71zsVYI88Inb8TWc3mOcu5P1NTCI0/wAgjtRcOUqbdvalBx0qwY+xqNYmZ9qgk0XHYvwymWEFiSy8Ek5z6VZt3hhdjNEJgVIA3YAJ6H8KhhtmVNsatI3VtilsflSlSDyrA+m01lubXaE71at0jMTszIGzgbicjvkfliqyqXOEVmPooJpSGjba6sjHswINEldBGVncUvmmHmg0+MKp3Pn2wKNh3cmMI2/738qaSMnn6U6TG7jv+lR4qkQ2AGcnsKZipQBjk49aYwwTjpTRLQkkbRuUcYYdRTKdSGmSxtFLiimIbS44pcV0OnaGu2F7iMyXEwzDb9N2emfX1qJ1FBXZdOlKo7IxbayuLo/uYiwH8XQfnW9YeF2nMbyyFgeqKOc+g/xrrv7IsNGsEu9XuxtAx5a8KD/dQdzXIav4nlu1Nrp0ZtLTPY/vJP8AePb6CuRV51nant3Ox0KdFXqO77GhdvpujR+VvRZh/wAsoxuYfXHA/GubutUluHJwAO247iP6VSx39etJjkV0QoqOrd2c9Su5aRVkNmkeQ5dix96iNSOORUZ61sjnY2jGTgUtSiIADP3v0FMVrkbR4xj681HU7MC/HPbmo2XAz2oQNCxHgio2GTxUqx7Vy3U05VCjJ6n9KAsQqRgikxVlLYs27OFp7LEoyoyw65qXJFxpSauQCN26KaBbuTzgVK83XHTNNEuG68Zo5mX7OPUgaJwcY5puCDVoSbQfU8Uu5CSSBRzCdJdGViox1pmKs+WjeoHWozFgE5OPaqTM3BoZGm457CnhiRnHApx+SLA69ai5A4J560E7CdW/GnuSeKYD8uMfjUqAHB6kUwGrHgZPUiou9Tbznpio2GGoENoFLUkCxtMglYrGWG5gMkDvQ3YaV3YjxSV12vS+E49NS00WCaW5BBa6k4z68Vy6qm75hWdOpzq9mvU0q0uR2vcb5WPvHA9qcEUcgZoHynjnmkdjuxjFWZgP9Ye2BTJB83JpTnIJGKQnnIFMGR09eM03HNOXk0CQ09aSnHrTaYEqRO43bgPrTGBD4bqKniIwPf8ASmzqdwP4fWlcbWgxCBkEZzTSpz0NOC08NjAHWgRFtPoaMc4qxGu45bp0qKRNkhWi42rEsRwMVERuJIPPpSqzKCBSYGaQwQDOCOaQ/eNO3j0zTc+tMRJG4Xgmkd9zccCkAy3NIRhvpQHQl8v5dynkdahBGelP8z5MUgXnmkDH5+TFMU/L9KU5xzTTxxQDFAy1K6qMYpFODmnOwYjHamA0HH1pyqXbJ5pg61KGC9BSBCMoVhxRnAx1pGz1ppyTQMVRlhUjgADGOtR9MHvTzuIBI4oAUc4o29+1C9P60xnzwOncUikrknyKfXvQZyD24/lVctzmkJyKLFp22J/NJyM980qynHXvVfd0PelB5/WlYFMuLLwWPXtUiyA8MAyjjmqSt0GelTJ8xxzgfrUtGilcn8hZOU4Hoar45xVh5AE2jjj8hUKgE+2aqNzOoo30FIKkE8j1pGOcAVLIf3eMGocDtTM2OA9OpqWNXbe0EZleNd7uBkIvrVV2PReeeaUSquSSfLH3hnG/2p2FcZLKx+ZicnnJ6mlVxAvnS/NIeVB7e/1qMMHZpZPug8LVaWRpXLGqJCWZ5XLOSas28YjAkcZJ6D0qvEgY5PQVYD4Yk/Qe1DBFq3dWllkJXeMBVPYev8qr/MAQwwSckmo22hs84PNIW3HOeKQx5ILlmJx2NN8wr9z5SO4pjMKjJLf4UAPMgxheT6mpIoJbqTA59z0FJFFnk9K0Ld/L5AxxxQwWrLtrZ21qgON0p4ya05NVSykWOOJJ7kDiEn93F/v+p9qwpLp4cbD+/YfKf7g9frTICsa46gnLZ/i+tJRvuU520Ruec97LHLqEzXcq/dV+IofQKg4q3DdPtAfOTwoDfdrnftLjJQHA5LVZt/MebfhliTuv3m/OqI3OwtpIiY4pgkqDooOCvuTXRaeqSQxTwxK7LgmNx8irnOc9T0NeeW0wX/SXXcsJHBH3s1u6bqdpAVMUM3zsv7ySU4GOWGB26c1LRSZ6VYxy6lGyW8SGIfMuT8siDg9ec/Wl1b4baN4jjWK404Wk4UMl1FhGx9Rw1cnf/EnRreFLKG3mu3T5T9mlZTKeRhm67T6VpaX4t8a6qscWi+HdK06FYgI2uWLkJ9CTUpDucP4k+FetaIks1p/xMrKI/ejXbMg/2k7/AFFcpp6JuAdgpT5mJ9O/5V7wg+JlwzpLeadA0fVvsXygezZ5rgPEnhvVJ3kutT06IydJLmwQIx7ndH0I9+tTNXVjWlLldzlZpvLsGnPyz33yoP7kCn/2Yj8lPrWWas3crT3Luy7Bwqp02KBhR+WKrUoRsiqknJiUlLRjg+1UZiUrsztuYksepNJTtvAoENpTTihAzSYpgNpaKUDNAB7UYpcUUhiUUtBIQZdto7DuaACpFgON0jJEvrIcfp1NVjct/wAsQE/2j1/+tUJmUMWZmd/bn9adhXNETWULcpLckHudin+tampavpF9Ok0WlPbokaxx2sT7VXHUs3UknNcsZ3PQBRU4xhd5cHAzg9KTiNSsai6jag4/sy3Axjl3J/Ouk0XUvDl5OLPUNMFjFIAiXEMxYRtnq2ecH17Vw+8RjO4uo6hv6VONrEMuduMjPpUTppo0hVkmema14Un0qVXtIy1jI21S0oJjbHKse/sR1rqdO8P/AGaMRvP9ltkRZJVGFY8c727D29Kd4E1RNb8IJbXJ/wBNsmEL7xnAHMbt+HH4V5trviDU9avGhmlCQo5UQqSEBzgk+v1NePWoVKkuW+h6tOv7vmdP4g8dQ287WWgRoVQbBcnp6fKO/wBTXB31/PcOxmleWRjl3kOSW9j6UxJltJfMVS0oGF3rwp9cVTJJOT1rroYWFP4UYVazta5Y3wJArKXeck5BGFX/ABqAsWYljkmm0tdSjY5nJsKnkuN9vDEI0Ty88qOXJPU/yqClptAmFSQuscyO6B1VgSh6MPSo8U4CgSHzyCa4klCLGHYkIvRfYUzFKBTx9zb6nNLYrccseVQghi38I7HPFXJ8IVhRsCLjI/ib+I/0+gFJYRlTJcHpCu4cdWPC/rz+FKkHnXgijDNvYKvqSeKxlLX0OiMdAtITLE0ky5t4DufaACxPRc++PwGadJLcXcoD/NIxAAUAD0C/QVduoUtgkOS8EW47kIxK/Qt9O30HvUlpExvvMmxC0hwQVxkEcgDsSOlZOa3NlTexlyReUzJIMbDtfac5NRltzkgBQegHQVe1J4/tTJC2+FMrGSm0kZzzVVXOApUMR90+laxd1cynG0rEWCTljyTzmn7FRA2dxJ7dqkJMMhaMDBHykjPBpo2EgnkgYxjincnlI1kkU5VmHb5Tg0hBBOQQfStPTJoba/Vp48xuNoY9U/2hV3X7QFUu0A67XwOvoazdW01Frc0VG9NzT2OdBK9Oo5qaLfK6pGrM7HAVeSTSBt0YjKpjdndjn6Z9KdBNJaXUU8Em2WJg6OvYjkVs9jBaMkljmtZmjuIXSQdUcbSKvaVfxwyNFdKHglG1yRynowPqKr6tql1rN+97eSK88mN5C46cCmR2MzRb+AcBgp6lT/F9KyavD3zaLal7pJf20lvcsrNvB+ZZAch1PQ1T71txlbnSmSTl7PLKehZGPP5Njj3NYrDDnvRTlfR9BVY2d+51XhDXI9O1kLcL/odwvkyp14PANV9ZsRpHiK4tGwVikyMHqvUfoaxI2Vyu0BSBjA7n1pzys7ks7OSerHJNZOjabkupqp6Hop0BtY0SK/gmjaSNDCI5Y+AgyR/wKuAvbGez8pplCidPMTBGduSOfTpXc+C9UvP7PuLWNI9pwu45Lh2yEOPTjFchPp8xunhkTZIshVtxxgjkg1zYeUoTlGT0Rc4uaMfkGjOMMGGfbtV28ght22iXzHwCcDAFbWo3Gm6n4KtJo0hg1KwlEEiKAplRuje/Tmu51dtNGcvs7XuczJIztksW9zT7WRY7iN5FDIrAsp7jPNRbuvAFdX4Ds9Hv9TurfVzGFeArD5hwN2eoPrTqyUINsUdZXNHxRZ6elnZ6paxosZIUquMMCMj8RXJ6jdwTsphiCkdTijV4XstQnsPtImjt5CqFWyp+lZ5rLD0rRTbua1q17xSDeaN5ptFdRyk8AMtxGm0sSwGB1NdTqlw9pFHGA0IZMkA/ePqfWsTQ7dZrxnf7sak5zjntVbVb1prlmQFIxwCTnPvXJVXPNLselhf3dNzfUjurpZmAl2pk5coMZH0qqt1IszbHZZCC8hA6Dsn5UljZXWsX62NjE81xMNqKOMHuT6KBnmvcPBPw60bSbdbjUY49Qu2wS7jKA/7I9O2TXTThZWOLE1ryuzxuC3jcRrBK+NytIiYACd/fjpms/VInfVYbXBRljWPaRjb1J/nX0N438HaXc6PLe6faQ22oW674nhUKGP8AdI6HPT8a8LntEvjqupxI6yW8UZZZW5V2baxHqBjv603FxkZwqRnErovlbo1GFVuPXp3oY816D4g+Hw/s4aroMzXKiISz2p5deOWQ9x14rz8AHnNEdhtqWwzk0cmrunXcVldiaWASgA4B7H1qq53uzEYyScChN3tYHFWvcaR6ZoAp2M4p6qADnPTjHrRcFERFDHnPAzS9+OKUKQfl61N5OEViwO4HAHb61LZpGJNpwtFuRJeB3iTkRqPvn0J7CtDV9WGpXMJit1hghXEcYGfrmqEBjVyTCrgjAVjwD61rWFlH8slx8oGGWPbkuOp49OOtctRxUuZnVTTasivBam5DSTDEYywK/KCT2H+e1blho0OXaOKSWExqUZ22+Y3oB7c1Xs7STUZ8bXMZyFJGdp9AB14ru7DTrlNPS3jjl8k/fVsFmBH97+EV5+IxDSsmb+7BXZzV3YtYiHyUDttAgRxuJBzuJPfHp3rAv4JWZ4nm8542JVcckd8DpgV6A/hnULpfKeFfIjXECl87M/z4quPA8sYKqclR8u5goPHtzWVPEKOrB1qbVnJHmEglZvmLZwABjH0pYIJZZQkaM0meh4r0x/BiSsXkwkgUbSJsgEfUdKI/B0doy3BikklDeYHEgOT2GP610fXoWM707/Eedy2EsitNbbiE/wBbGD/qvf8A3feqMksihk3h4zxkrXod1os0TCURkXOGf+5uB/hI6MB3rN/sJJxJNZQxiVMtIrHIUYwcA9R6VdPFxe5bpp6pnEvBGy7vmTvnqD9KRFMLDYRwQQOoz61pXdnLAZFEZxnG9hzx29qd9stE8OfYo4mN7JceZJJjhUA4ANdaqXWmpi4WZPP4tu38MLpDW0QZTtjuwMOIx/D7+ma5aX95JkKF9hWg8JeJpScBMAj65rpde0Lw9Y+EbO6s7oS6jIVztkzuyMtle2KIzhSaSW7MpwbRwjLg49KWFzDMkqgbkYMNwyMj1FSMuCajIxXZujltZmz4nvdI1OS3v9Pga2uZlJu7cL+7R/VD6H07Vz2MGpTUZFOnHlVkTUd3cHkZlAwBgY4GM/WoySQATkDpT8cZpmK0Rk7sRVBYZ6d6awG446Zq5eaddWCQNcxGMTxiSPJ+8p71TxQmnqhSi1oxtHPalNT2U8VrewzzW63EcbbjExwHx2Ptmm3oSlqVjSYqa4lNxPJKyopkYttQYUZPQD0qGmhNCUUoUnJAqa3gEznfIscaDc7nnA9h3NDdgSbdkFtAsheWbIt4hmRh+ij3NR3dy8ivMygM5AUdgOwFWL+YS7LWGNo7WIFgvdv9pj3NZl1Ju2LjjOf6ClFXd2VN8q5UQKBvA9+avYqiTj61fHIB9eatmUQGOT3prdaXFJSKuJRiloFAAKcKQV0ml6Tb6zoTpFti1C2lPz9pFYZAf8QwB7VLdikrmCZXaIRZ+QHIHvTMc1Yu7K4sLlra7haKZeqt3HqD0I9xUQFGxWr3BRUyLmmKKnjFRJm0EaugXY07V7ad2Ii3bJcf3G4P+P4VuPZfYdX8R6XKcyFluomA5dOd2D/utn8K5iNc4XGSe1dfPu1K10HUoJIxqdpm2uopW2F4hwGJPbacVwVYOUtOv/Do74TUUrnn+rWr294Qx4J7c1Bp9q0l6G6JEpldj6Dp+ZwPxr0m68GpqEvmtMzQYJCR4B46fMfyqtJYxaPHNHHpduoZVLmaQyEAHjkcDmu6k5ciTPPr8jm3Fnlkrr9plYYI3HHNOiguL6XbGjOfboB/SvQ5zYFszaTZysvIcR5BHr2aq7xaZPD5dncy6bLu+RG/eRjjvxkfjW3Mc3Km9zlYNBuyoZzHCp/iY9KnfRljby5L1VcDO442474PeptT0q5gnD6hcExsMpNG25JP93HSqYi0xI8M7SPjkEE4/GldsqyQNpzK2IbpJTt3cfdP0NNw8afvwVPOMDIP41Ulj2P+4lJQcjJ+7U1vdQRozXETTTtwhZvkAPXj1p2J5hkhGN1EM3kyB1CsR2YZBqS5a3nuyqsY4wuI846f7RHeq8tu8XPb3p2BtmnFq9+sZ+zalPbSA/cjAUEeowKk/wCEm12ywslyXQ87njDBh9aw1cq4bOMHj2rQtpDJmGUqyk4XdztbqB9DTsTdnUaf4x0y+bbqunfZ7goVF5puI5B9V6MP1qW6eezijntrqDV9KPA8yPcByRtcHlGP1rhbm3EbBosjPJXutTafrFxYuwR8xyDbJG33JB6MKTj2Gpdzorm3069jkudPBtXjyZrR23eX7qepH8qzLhGQLx8uOGqGeSNwlza7lCgZBOWQ+/tS/b2kyW2qMANHj7309v5VPKVz9Bm0kjHWnBN0m0nvzS7wF3xH5T1U9VPpSREM4yaHcaaYOmD3K+tMYDtVl16DGAOtECqIpTt3EDrjOKnm0L5LuxSwc0hHNSgcUwgjnFWZ2GYoxTqAOaZNi7pfkvOYpkBVhuHqcDOK6C28RWuj751jF5qEnBLH5Il7KD/PFcmC0bEqSDjANMxWM6Km/e2N4V5U1Zbl/UdSu9Vujc3czSyHpnoo9AOwqo3A+hpqNxjPShiACByTWkYqKsjKUnJ3Y1m5PPy56USKAoODz3ppGDT25AHOaogYSSgPcUzBJwBThkEjFKmEfLZ+gpiFwIc8A5701hkDGctSzEFhihGMbhiKB+RGy7T3zUioMjJyaY7bmLetKX9Bg+tMQ98g84OeRUkcXPmPnHUCoEJyD1btVuO7RhiVMf7S1Er20NaSg37zI5JTkEciqzvnkfjVq4iwNyMGU9D61U2ZGSQq9MmlGzNKjaGFulJu4FOJQDCp/wACY80059OPpWljn5hd3+NKH/WmGjpRYFMkL8YFOEmPrUOcUo55NKxakSMS/SkbGAMdKTf6DigndzQiJIbipUJxx34qKlBx061RA5xikOCv0p/Drz1qIigBKkRe5/CkRN2Segp7cAUmwSEZj2/CpLeyubvd5EMkpXkhFzio1Xc+ewrtLPxfYaP4cS00+2YXpXEjkcbj1PvWNac4Jckbs6KFOE2/aSsjjQhK9cY60xCA/B45od2lck9WOTSY2Oe49a2Rg7X0HsVyD/k1GckegpwGT05pGIAxQIQhQvTFNXrQWzSDg0xA3WgDJ+lK3XilOAtACq2Pp3qQuGkB6qKj6jpSx9cetIZN5QIJTOahxzUybgTjOBTniLDcoyR1pFWEjPZRwKgc7pSfel+YfdOKEXeowDu5poG7l+2ijaPkA5qncIElZR0FKkskQ2gkfhUTMWYknJ71EYtO5rOcXBJLURU3d8UFCOpA9KVDgkilzk5NWYWHIAp65NJzvPy0qHcQCvy560FyrbTxjvQMVV4wRjmlIwwPalDAgGkY/KMetABgck9BTf8AWtjoKa7ZOB0FORtvOetADWUoxBpMd6dIdz5zQVwgP9aBDSKUE4welJR1pgPP3RQFzSooYYGc0o447g0hjWGOafn5MfpSN0pvIFA0IzY4596iJpTz/jTD65pFATTgAMbvyFIOPrSgdDVENjgSDgAA/SniWQfxGmBSeakCZPB596BEqyCUgPGHPQFeGqeaKKCQJHKJAFGTjGD3Hv8AWktozCsszqVdABGCOrHv+AyfyphHAxWb1ZrF2QwnJ5o75xThjaQRk9jSYz0qiRWYFOvNVzJkkA9eD70SMd5Ve3BpsgT5dhI+UZLHqe+PamhMI2VT82fQAVGR5sm1eFHc0gaJDnczN69KR5wV2ouB3Oc0yRs0gJ2L91elRquT7CipMARkd6ZI4EKBmjdxyDTR6k4oJ5wKRQ/dnrTGbHuaaTtJpKBB1NSxJzmmIMtU4GAMdaaE2PBAY+lPVgF3seFHT1NQ5Ofalf7yxjtyfrQCFDEuWbJY8kipA3IXkEnv71ESQoGeTz9KvpafatOklhOZrY/vIu5iP8Y9cHg/UUAQqcOVJxj9TQskgf5iQAeDnoKiIyu7uOtJu+QljhR196ANI3wEAVR5cYHzEsTuPr/9aqrXEt3iJC0cGfXlvqap7jKwLcIOi1YDjaQelAXNfTZba2ZQsQLA5JB5/Ou40nxYbeZFaBXfePLEb+XlsYXcR3+vFeaLLuIOAvHAHGKuwXJ8sIsSkZyQ3IY0mrjTsfQQ1iTU7by3ntdPuLbyzL5pcJFg84cHD5A/Cruo2cU0Ml99nkVSvmKqDMik+g/iBOCCa8V0rW53t47C4uisbS7iwGD0xgtznPTpXqmiX73VlbRvbwIBC0EMjZDITwdwLcr0GepNZNWNIu5yPibwjDdgvGnkXrp5iMzABj12/lnjqCK8wuIJbaZopkaOReqnrXrut+HtV07T0S7h326sT50WcLnOA3f0rltQ09dYtZIp1ddRtk/cz44mUZOxsfxdefakmabnDUo9KUqVcqwIYHBB7GgDBqiRBT88U0DmnDG3mgELkEUzFbOnCx1C3XT7hY7a4z+4uBwGJ/hf/Gsu4ge2uJIZRtkjYqw96iM7trqaTp2SktiLFL06UoGaMYqzMSlIpwxg54A9aqyzF/lXIX+dLcb0Qsk23hOW9ewqs8oU8ks5pjyc7U69z6UgXb9atIzbA7n5Y4HoKuWdpFOG3PtI6VUpys2eDg+1Ek2tBwaTu0SmNY5WD4IQ8470j5X97vG4nPFIcY55A5PPWojmV+OgFAN66CZMjc/pVyyfZKEz1OVPo3aq6jHAqSMhZFYjODmh7BHRnuvgpLePxBfuvnRW9/GgWOcgOzAfMcfXNc78S9OjtvFX2m0RBFdruOwYG9Ttb+Qqt8OS1z4lje4kZ3MRAZ2P3iwxWr8TZhLrlqqpsdY3kkDHG3c3H8q86XuzselT1dzz+/fzWjkMgeQrtf1yPWqdad5fQkFLdBlhhm28D6VmYya3p35dTOtbm0YlLSgCjFaGQqozHCqWPoBmgKeR6cn2pwLIQykqfUHFb2lXMmoW13Z3LCTESmNmA3IdwHXrjms5zcVc1pwU3Yp6Vo9zq10tvapubqzHoo9TUOoWL6dfTWkjqzwsVZkOQa0LPW7/AERLi3sZFj8w4dinzqRxjNZbs0jl3JZmOSSeSayi5ubb2Npxgo2W5GqEkAZyTwKmNuVbDEcru4Ofw+tEMbSSoqDLFgAPU9qv21mq3ZW4STykk2SY4IP/AOuqnOwqdPmNCys2WO2tX8yB7sElwM7lbhBjt3596ILNtNku57jckts/kRY5+c5+bjsBk/XFak8Zg8QxrFBIjwyMfId8jaowBx046Vn6q6wj7GYtrRJ5bMHzucnJJ9eOK4YzcnbudzgoozAVleIPloIyAdvB255/HmrszptuZFk2IjDaGfMjZPGD7DrVO0QF23uyRY/eMO49PrkCq8v+t4GFxxzW/Km7GXNyq4xmLEnJ5602n7DgHseKesX7vdz154/KtrpHPZtgimWMp/EuSvuO4/rUn2Rks0uhLDhpCgjD/OCBnJXsPerFv5QTytihywZZD1B/u/So3gx5jSYjdRgDH3iDgio5tbGnJoVCXdiTudjyT1P1rQXWZPsqwvEkhAwS5yCPQj/PSoQ6N5hlLKwjwnlgDLdBn29ahQxpIGkTeoPKZxTcVLdCjKUPhZAzZcthRk5xjikEZKlh0FXbLTbjVtRW0sIS8shOxM9B7mq89vLa3EtvKCskbFXX0Iq1JbGLT3YyEhJUZkEiqQSp6N7Vfjv3W8e5ZR8+d0YOBg9h6Y7fSqCr17VKSpXgYbOSc8YokkyoScdi7Dc4u1kOP3hIZRwBu4/rVO4jZJXVzllO01IIGClSreZww+hFTXUDeZuCY3qHHHqM5+nWs1aLNGnKJRQYP86sRO9tcRzJjdGwddwyDg8cd61tOt9LbVo1Yy+RsHyzLyz46YHbNafiDVtHew+xWtuJJVwFlVdoj559zWU6zc1BRvcuNJKPM2T+ErxrvXri6lWLe8bzNCG2K5HIAHTA5NR+Ko0W/nZJAwuUSdVX5sZHOTXP6ZqsunzZVEkjPDI46juM+lamozSzaZZX2CUAe2JK46cgY78GsJUnGtzdDWMk4mDf3U19cNPO26RlAyBjgAAfyqmasSBsDOeM9abNA8D7XGDgEe4IyK742Sscc7t3IaWjFLirMxKKcAMinyRhGxuDeuKLhYixRinhCx4pMdqLhYuWUqRQTAqdzD72eFGKyp2aZjxgf54q8HxA0eOWI59qn0ix+26vbwhMqWLuB/dUFj+grKyTcmdDqe4oI6Hw75Hh2ydCAb65UF27qDyEz29T/wDWrr7fxa1varbQZjbGBIxyVHrj14ryiXUHe+lcyYJk3E1K2qkjGAIxnae5+vt7VtFXOOe56nqvjGWe2khZ90RYHPTp0H9fwryy4vvJutTjAUi8gcN2wQdw/lVBtSkkZxvYkjqW64qiZWeRXZgScgj8DWiiZ37HoHhrxtc2Ulu28hIlCADuOtN8Z2Vm9ymtaYgW0vD+9jXpFN1OPQMOR+NecQzmPBycGur0HUjeWV1pk75SWIlCezp8y/1H41nUjy+8jWlJSdigBz0qaK3lnLeVEzY67RnFDAcYGBWtoWrLpcr+YhZHHOOorKpOSjeKuzohCLlaTMqBFWdRKSqg88Zx+FWWhRj5ij5CxAz0p9/cRXuoPOkflox6CrbWoijjmGDE+cLnkVnKezZtCC1SKMiwiKPaCJATvz0PpVu60i7srW2uZFDQ3KbkZDkfQ+hqvHB5syx7sFjgE9z2roLZLu3t104DzFdt20PuUnOMfhWVWq4WsXCnzMyLe38plcKryAjCOOM9gfWuz0fw7qt4zyTnaJGV/NK/O30HZTWz4f8ADMVtIbi9CzSqd6M3IjHr/vfoKzfEniqWSOfS9GZ1VMma5jPLqPvYPYe9edOvKtLlh95XPZ8tM3XPhzQcreXEAmJLeWp3MD1wAOlWrfxFot1EPs12kZcECMAq5x7dq8ltreSa5VIo3llONxXkn3JPA+prcS1h0yOR57ea7nCEFLbOxSf779/wrOeFj1eonQ5tZNs7y0ubC4DGOW4lKjDFpwcZz78fWs59ahs3kjihvJmTOWDcAeuf4gPWvN5ruUu2f3KZx5SKVUdsGn22o3Wno32a6mRXHK5+U9sEGmsD5lqnFNnexeO4uBNYtIv3Tlhk/Styz8SaTcnyhI9qR8uH4U+wNeW2+q24haFw8CyDDsiBlI9dp6fhVl0uLOBiswaKXaUaL5o29Mn+E0p4SK8hPD05baHrKLhCwkWSMZ2vvDD8qbNp9pdRtG8ceGAz5Rwa860MyW8odzPEqAlo8Fo2UjjPtkjJrXj1HUYx5kQV1KErIg3xEdz6qB7VyyouLsmQ8NJP3ZFzW/CjSKssSmVwcPIR82B0JHciuB1XSJIojcJDsyTuQDqM/eHt7dq7iLxfPGUhKRySHI80EhTx2FObUNP1pVN6BbNgjzdwPUe3Q8VvSq1KT12NYqolaor+aPKirKjRO2M4PJ4WqMgCtlevOeOtelax4ZBhVgQNgKRvAmd4J6sOwGa4HUbU2r+WwyVJUvj72DXq4fERqbEVIe7dbGapA3ZRG3DGWGce496idcHgg/SpiFGSQT7CtLWdMtNNSyWC8FzcSwCWdUwViJ6KCOp9a7edJpdzjcbowyKfdNBJcM1tE0UXG1GbcRxzzQRSLtBO9S2QQOcYPrWnmZNdCvtOaQjFTgAMCQCAeQe9Mk+ZyQoXPYdBVpmbRE7O+N7s20YGTnA9BTMVJikI5pohomstPnv5GSBQSoy2Tjiq8kflSMjdVJBxTgzIflYr9DTWO45P5UK9/Ib5eXzGvtz8gOPeo6kOOOaaapGbEyQCAasaft+1fvBmPYwf6YNV8VZiCxQNM4JA5/z+NKW1i6e9yrcysspVhnCBFOeg6gVnO29yT3/SppZmKupxlzuY0ttFn5yOnStFojGT5mLDb4w0nJ7D0qyeDQKceRSbGkMxTW606grxmgBlLS4pQKAAV1ngCeOPX5LaUjy7q2ki2njcwG5QPfjiuUxU9tNLa3Ec8LlJYmDow7EHINZVY80WkbUnyyTOnv73Tp/9GAa5g5LRP+7MRHGY26jgfQmsS400KpmspxcwdxjbJH7Mv9RwatatAupJPq9pbt5W3zLhEP8AqX/iH0JPH19q5o3c6yZSRkI6bTyPxpUnzR1KrJQd0bNjp93fzpBaWs00rnCqiE/r0Fd3pXw/ihkX+2Lx5Jiu77Fp6GR+uPmboOeuK4Ox8d+KNMCpaa1dIijAQkEfkRXT2Hxh1Dylttc0ux1GDPLhfKk+u5eM1ryGPtX0PQl8KaLbRyJDNZrt+cxxPuZQPXuTkfSsfUdA01LbJhvopDuAkPA4GTkHt2469qs2vjvRtTtVXSMRsy7XtpVWOYfSTo4/I1x+pazfwxgpK7KuQ6z/AOtTPXK9D1pKIc7e5TvYbvTHl+yXzSxgD5Jhxg/7PaqCarA+1GiMVwO27CsB0AI6iq0t9uVTHK7qVPysOP8A9dZkzCRfnzyePVfcVaRDZrE28/zmSV5CSNhbG30571QllIfY7lsdM9QfrWYbh0cE8sO/r/8AXpDJkB+TVWJuaUWqypEyOQ0Z+9GRkN9R6+9Z10vk/vYcPCx6Hqh9KYH3EMTginiTbubaDG3DJ2osFysLvsV49DyKQyJ2GSRzTZoRHJhTlTypqJSEJyM0WFcttbRi3UrKxnOSY9vCj3NMjmZf3b569D/Kod7LnaxwetN3Z4P50WC5aZA/MWPcZp8jbCuwEtgD06VUBIOR1FSByBn8xQBeUtP8gYDneCwxhqz5Y8sxAAbqVHapVZWjOThs560zcNwbuOtADILh4XyOexB7j0qZypAdPu/+g+1VXGG9qdHIVbnp6UwLkU2BIh43rtA9D1BpyyEjBHzj07//AF6qkcBlzjr9KkLFsSDr39jSAvK7NECDlT39D6VYjuSls8KqPnPLVmQzbGKknY3BFW064J49h2rOUUbQmxTUkyZhSQfRgO1CxhuScLnFPVT5bxgbgT19DUtlpFPFAHNKQQcd6TFWZiqw8wMQCM9DSyAHJHanQhMkvjj1pkm3d8nSl1H0Ix97rStxxQB8w+tOf73SqIIu9SoQEJPc1FSjp14oEgXkkmkbqKTofapIbeW6k8uFCzYzgelF7asaTeiIiOaACxAp0kbwuUkUhh1BqSJC6gAgc55ovpcVtbEDoUbBoYfdAp7xOWII5pW2xcDlvWncLCMNgAJ5/lUffNLnnJ5oIx06UCHxSlTggMh6qe9TX1uqqlxC26GT7vrGR1Q+/wDOqoFT27MRJFgmNx8wHY9j9aTVndFqV1ZlXj6GlJURjLndnG3Hb1rptI8JX2qziBE/ek5ZB1A9Se3UVLrXhj+xmeOTaJUOGTPzD60+ZEWZyOeetB7VZmRfTmqpG3p+VUSBGOtJkmnDnkflTSO1A0wpQabSikUTIARk80jff44FNVip4PWlPWgTHA8nFI1AoY9qCRcYT73HpSKcnBptOwFGe9AACQcDoetIxxxilGBzSN1yKBjPfvT85XHWkCtjOOKTPNMQA4OaMbiAO9JThwc+lADmRFHOc1F3xTiSeT1ptAMdgg56005NOVS3SpNmFPegBg4OKU8MDSdxTmHANIZOrblXjkcVKrbJASTg/wA6qxAsCP19KsLGo5Y5NSykhrxbpDt6ZpP9QMDBOec0+SQKvHH0qKPEpbJ5PT0oHZXJvtKN8skfFVJUCylV6dqsNLkZOFKnGB6VEylsPjgcU0KWozGBx0oAyBTipYcHp2oxwKZI8DavK9O9Qud3zd6kL/LgDn1qKhDbJR/qxTCxAx+NCk5FEgw2elBI0DJpx9AKBwtSQ8OMYzQNIixUsJBOxuQen1p9yVOMKQw61CgJYBetG6HazB0Mb7ab0q3Ku6Pn7wGarqMsOKSYNWYK7JyOM0ZPWpZNo2kA8djQrIeHHFAW6EZ6VE3XrxVmSLau5TkVXZckY5oGiM/jQBubHJqwsA25PJoC4YcYx0oBkBUqcMCD6GnIucUOxeQkmlGQcfpVEGhawoXGeOep7V2cXhzSLvRhcR3S/aVba8TY6eoxXDpJt4YYIq9bXxgYOD042nkUmNG9p81jpdw9nqNuLzSLniVDxJAe0iHsRn8RWZr2hSaPdhEfz7aQ/uZR3HofQ4wfcEGoLq7Fwu8H52Hzc9TWrp+pLeaSlldkNEQYWY9UI5R8+3T6VLXUtM5lo2jb51IPuKb0Oc4961LsW8ZaBrgXCjBWSPp+tYV1OMmOP7o6n1oV2DstiOR1Qkjkk557VXJZzT0QufapDGAMCr2ItcgC+tBFPxTcZoE0Cjv+VOPTFFIelMkC2CMUhPA4oIpKChOtOA4pPSnDrQIevan5GKjFOBpkj065PQc0wtzk9TzSq6qCD1PepAkL/wB4e6nP6UikR78sDx9KsWl/NYahDeQhDJE24K4yreqsO4I4IqP7OM/LKv0b5TQYJEBLoceo5FAGjfXWlX9xNc20DaaXIItVzJGD32tnIHsc1lt87cfcXp70nl9D6+lOXGAOaAHYIXJ4HapNgjBWRWMjAbAD0+tQkktlvmx60Kzb8nk0CJ2RkZlwTt7jn8akR8gAk/hUCM+8sh2cY4PUU8OkAy7c+g6mgLGpaLgBstuzkbTyK7DQ/EOnaTE326SFeGASdmkJyB82xe+R6jFebyX8rArGfLT/AGep+pquCfxpNXKWh7ofjDoEWmpaNa6jdsoOXwiL7AA54HvzWDJ488KXwc3OjXkE0nLyRyhgzf3iBivLY4nkICKST0966HTvBGtapb+fbQxFQSCGkAYfUdvxrNwRqp+R0Wq6ZpWvRtf+HLyKa5A3TWRJWVuOWVT1PsCa5DHPTketbEfgPxHGFnS0ZgOQyMQykc8ZA6VnXQm+1SGdXWXOXDjDZ96laMt2auQADNO298cUAEjpTnfcRwOKZKWgylwTyTnNLjvSjpigYwcHFHck8DrS471WllD/ACAkAfrQLYJJgxx/AKqzztM/HAxg4prvvO1egpdoA4q0rENt6DQABgUtJS0yQqRcpn5cseBntTB1zTtxT5s/Mc8H0oAbI3J5z6n1NIoweaaOTmnjoKAHjrU0Kb5VX1YCoRW7o1lBfXiW6RTmdgdmxxgsAT/SonKyuaQjzOx2ngDYmsGZQxjWRBwmeFDOf1C1U+I90t34yuNvSOKOMjOcEDJH61t+DoEt7aFnBibb5+QwGd7BAD6/KrHFcTqt9He6teXWzd51wzhsnIXPGPwxXCnzVW+x38vLDUzaT0qxctA1wxtlZYf4Q3WoCK6U7owas7BilxSqrEEgEgdSKUCgLCAY61c02UW96juSI2yj/Q8VWA6VIVAwBmolqrM0g2ndFy/eN7kshDErhsdM9M1BDA88ojRWckE4UZOAMn9KjAqe3WQzKsJIkbgYOOvHWoS5Y2NW+eVya1dIYpf3AeYlWjlyQY8HPA9+K2Jp7fUdQEqpN5kzB5VOPmYn5selZq28kbmLIOTtO1sqfx71u6To9xcyFEtXkYE5cAqF7Dn9a5K04r3jsoxexraRHbHVFm2Tnyl8xiT/AKtBlsZ/i7frWLqNsvkIWDNO8hfIOV2HP65rt7Dw/PDBem4uhHJcKwPlrnavXqaimW2tIrdNPsDJdN8iOw3MAep/2TmvNjXSnodDcZaHE3WmJZW5nuybdG/1NtnMsh9T2Ue5/KsoWU7wPciJhAhwZDwufTPc+1emyWNt4dt1ufEeoBpXG6OxjUNI/wBSeg964rWL9tU1BpJCiWyDFvBGCEjXHAHv6n1ruo1pSOaXLL4THto41nRp0MkQYF0VtpYegParEdnLJKNkeRnA7gfj+la1vcztpIgSNHg+4/7oZBJzwepPHX0qW3uJLeweL7Nvgc7+Rghh059B1NVKtLoXGkupl6ho91pckK3kYR5F3hQ2SBnGD700QyXuEHMyLwCcbl69/Srs5m1GdZ7gyybOJJCcKOeADUVzIklwwiDbWPZup6Dk9qcZtpX3E4JGfcrGAiRMJEQZJ2YJJ6/UelJdw24t7d4Z97lcSIVwVbr+I56/Wp/Ja4m2W8LyShSzZ56ckge1VHx02AHvW0WYzQ21me1dpomlSZVzG8bY2n1NQOzSSM8jFmY5JJySalZAFXDAk9R6UBF2/OCOOAB1+taK25k03oRuQwByxc/eJqeSxmt4opZ0ZEkGVOOtQ4wMgEH1qzYpBc3kUV7dtbwZ+aUqX2j6UN21EkupHBM8JDISGB4YdR2q99ontRDcJKN+Hh2HkgDjB9sGqt2bdbqVLNpGtt2EMn3mHYmpIoXvpmAaNDhny7bV4GTj3qJJPVmkZNaIrLM8U4lV2EinIcHkH1pozJJ3LMfzJq3f2sNvJEIbhJkeNXOzJ2sRypz3qovy9KtNNXRDunZj/L2ybWyCDhge1dRLM134UiTyQfJuyA4OTgr0x2wBWHbm0W1uBPG7XDBfJZX+Veedw78VsWa7tBuyvmbVnjJA4AyD/hXNWd7PszopIwLiMoVyckg/gM1XcliCSScY5NX7sxyyGRerHOMcD2qbSoraRr03Nu0qC0kZdv8AA3G1vzrZTtG7MZxvKyMfbV22t7Sa1mMk7RXCAsuRlXGPu/XNQFeeBSrleR+taPVaGaVnqRhV2nruyMY6UYFPI7Uqxls47DNO4rEeCB7UmKfijb3oCxHiuh8JAx3t9dY4hs5FGR/E+FA/nWDjNbFs8lho888aq6yweYV75VyvX2/rWGIu4NLqaUknLXY5qK5ey1QyBUaSCbISRNytg9CPSmX8XmM97bqDasSzKi/8e5z9w+3oehHvVYzNJqHnMFZpC28Hpzmp7eeS3KvA5WQKN5Tk4IzhlPUV0xbic8kpXKqeWSuScdyTSQoWlCjrzjPTpU0yW1w4eMC3YjLhAWT6gdV+nIpqlSz7GLbVOTjAUYOBz3rbmVjDkdygpwOR7dK0NCkYarbgN/EeMZ7HtVQwlxuVvkIzknofQ1aswtvMmzJlZgMngnPYeg9e5pTa5R04tSRuw444zxUnktI52KSQM4UZpu3DHB6E1veGdYh0q8czoCkoA3YztI/pXHUk4q6Vz0IJN2ZhQgbwG6HrWlYafdajK0dqgO1S2GbHA61X1N4JdTuZLYbYXkLIMYwDVvShcEuICyuw2bhx8p68/hWdST5OZGlOPvcpetNKdQVkQLcZBw+cBSOOn8WfWussrJPtFvFFu88bEk8rgLjqAe2Op71HaWw021+zlw1+6FmdyCsJIHyknvxmug8M6csMS3j8zzLgEk4x1Jwe9ePXrORvOapwbRT8Syi2sY9Hs5DC7x7pDHySOQFHfLGuRfTLXTisd9I3muARZxN8xz/ff+gro9ZvUhnuRbqftkz/ADXDHhQPc9FA/WuXiKoJLyZysoBMMi5JLE/ex2Hp706F+XTYKUbR1HXWqz204hs4msrUklEVdhbsST1Peqd7bXltcyR+dMYedreZtDD86lf92yrOr25ZOSQZJm77sdv0+lUjLZxOGlgnmQ8/vJdpb8hxXXBdi2WzBNua4GqWwlKlgkkufvA7vmxjPt15qgNNlCE5V+Bjyplb8xnNWVisrhlCW2oKmM5U7wCfbHIqSDQY7hwLa6hJB5W4UxEe5J4qubl3FYz54Y41SNoZYZlyHaQ5V+eMDtU9pdSW8hdXDK/DwuPlcD1HTFaUGh6pbyljH5i8hCjrKhPuD1FXbOxtV33l7bCKQNsjwjGItj7zIeQB7cVM60bdwSsWJbZINOE9tugjwJLiK4feVDA4CgdsE/pmm6drtnZSpbxRTlC2fOkkHBPbHQKe9UpFvLLV/NnZTKylldCCLhe4/pj2qK90+OeMXumRssJbZJAPm8pz0A7lT2NcyjF6SLtdWZ0mpWtqkvy2eI3QyQz25A2YB3ZHfGOtYMmnvLb7rC5RwDwpwspB5JI9B61t6Na3ElpLbPIVgiUFrhjjyf7y89qx9TMNjqE8toqqJVLwTM3GO4UDoewqKb15UEXry3Lmma3Hpj2r30zmaYFXmDFkA6AMv976Uni7QrYxjVrSFZYJIw7xhu/94GshLiLWi0E8MKXZj2Rt0VsDP4N6HvWh4f1IWbjSLxUEEikgE7sOeq8+tW4uD5479UTKOvMjzuaPY5XHfFRgBRjHIP4V0fifTW07UpYdpWMv5kf+6a5/aQwI4PWvZpVFOCkjiqR5ZGnJpsOkXdo2rISlxbmbyV+8mc7d386x52jed2jjCRlsqmeg9KsXt7c6hdvdXczSzv8AeZv89Kq45q4Ra1k9TKbT0RGw56UrfOiKEUY7gct9aUjmtXQ7VLm+BcblTkiqnNQjzMVOm5y5UZs2nTwQRzOo2yDIA5I+o7UunaVPqd15ERVAql5JZDhIlHVmNdJq908LrAjlRg79vXB6CudImKtHGzfPwwDcMO2ainVlON9jSrh4wlZFGeOOOeRIpPNjViFkAxuHrioSKu3kEcE7RxSCRQByDnJxz+tbFnpOgyQRvPq7eYygmPbt2nuCcVt7RRimzl9k5SaRzBFJiu8/sXwwYMJL5j/3luear3GkaPBavcQxh5kH7tGm3bn7ZHTGetQsVBuyTKeEmle6OUWHyrczNHDIxICpI3TvnH0FV7y6S4AWONIUHPlKxb8ie1RXmZbmSSWbz2DYLnoT3x7ZqhKu1jwOvWumMb6s5ZytohQrSy4AOScH2rQVAuFXoOKraXE13fLH50UZ2kgyvtB9s1tnSL5W4tnkUfxQ4kH/AI7VSZMFcziOaKe64cjuDTMUhtCbS3QUu045p65xSE88UXCxFjmlApxAzmnKlFwSGinjA5JwPekA9KmhuDZuJ1DGVf8AVbRzv7VLLR03hfwp4h1Wfdaaa5s5V2TPc5iiZD7nk+ox3roT8ILCxhlbUdYvBKc+UIbM7cdsscj+VecXZ8RyF5ruK/OG+ZpQ+AfQ56U+z8V+INFnUwX13A68bfMYcfQnFOMbaomc29DqtR8G+HLLTQ8epz3NwehXGCf9kD+prirvRLq3G428qp2JXiulsPGtnf3SjXrbaDwbm1AjkH4AYb3zVrV3kkVrm2mi1G1IysqDaY+3zp/DgfhVK6IdmeelZIHyuVIOcitePWJb5FjuGBnB4mP3seh9RUN3GrDKrye+eD9Ky5EaN8jIINWRsaEzsJSVU7u65+8PUVGXHleYkhJ74HT61H5pljDg4ccHHY0xML+93rjkFSec/SgBX56nn1FRhioOencUCTEQUqOD1pm75gT0piJM5+lPBDYUDB6Ak1H5LN9wEg+gzTjGE/1kir7Zyf0oARs7Wjb7ynK1DtDgU/cC4K5wO5700YUkMcCgRGQUPtRjPQZp7He47AUhTHT8qAGBiO9OB446U0j25pOR0PNAEmSR7etITge9NDjHNGcngHNADiOMHOe9MIxxTs5PelZQVyKAESRk6GnLK27I4HpUXQ1KAO1A0SBlbqNp/Srdu4+VHcKB/Fg1S205CyHg1L1LWjN6DyCNq3MRf13Yz7c1Zkt1SAsf9ax+UDpj61zzNvbIABPbtUkV3LAcIxx3U8g/hWDpvudUaqtaxadOS1JFby3EmyKNpHPOEGTTxexXTBZB5TdAeo/H2q/Yale6I0y2+wNOm0uVydv+yf605OSWm5MYxctdimtkwGZAV+oqtMojfapyMda1QLq+Q+XC7YOWI5zWXLuEpypXHGD2ohK71CpBRV0iMfeB7ZpHOauoqNCqHhupzVaeMRybR2q09bGTi0rkFIVwM1JsJGcUfeGO571VyLEXWrFletYz+asaSZUqVfoQaYEGwnt61Goyw+tJpSVmNNxd0SXNw1zOZGULnsOgqDcR3NSyZPUj8qippJKyJk23dgGKnOc/Wg+tJS9qoQ9UBUk0zpxShsDGKQ0gEq/BiEIvf7zfXt+VUsHAqxJkSuO4agaR2XhbxbF4euJpZoHneUcuG5/Xj3rH8R+ILjXdVlvZlWMsAAidAB/M+prEEhxjPSt3U9ETTPDVleXBYXt4xdEzwkQHUj1PFZynGDV92aRhKaduhz9yksMpjmUo2AdpI78jpVVqsFIRCS8zebnhAuePc1WPBxmtUYMFOGBqT2xUe3jOaepyPegY9IFkyNxVuoqJ42Q4PIqQMUII61ISWyQOvagdyqKd2zUnkMXCopJJwFHXNbKWEWm2b3E5VpRwfQH0HqaVwtcyFtZWUHYQPU0jQhfvSpV5knugXkLRpxiNRyR6mmtYgITtCsOme5ouFih8uciQUvDDAI/OrLW5xgqPXharvGqnBIBHY0xD3KiIKBUBpduPun8jSA5PIzQgbJei/QVCevvS544/WkoBi7eeaTbnpzTgeRmgfepiGnr70KpZsClbGeKfD94/SgA4QY6U2R8njpQ+CePWmGkA4dakUBuCe9JLE8LbXUg4poOKNx7PUs7gowBxSbj17elQqxLDJpZGOABU2KuNdzvJ607huV49RSRKrP8ANnHtSyRiNgVPB/SqJDZzlqsQgNGyHvUAOR71JCwVsUmNEIyp9CKlUjd05zUlzH0kA69agHBB70bhaw8xbhxw1QEc471ZDAP16/pTJk+bcO/ahAyNVyc0r/MwHpRn5QKTvTEOK5XA6+lCnawP50AU7rQMSZw7cdKfCMAtTfLzjsaN+AVA56Uhp63B33EmmLw1SRAZyadKo4YdaBDGIOMUsaFjnsKETcRmpvlUAClcaV9RuNnHY0zhVwKVzk/SmGgGOQkHOOKa5wCx60/jaM8e9RMC33unamJkI6VJhMEknd2xTduKTGKYiRW+Xnk+tOUng81GKcTtGccCgCVGG4BztXucU+Kdk3Kv3Cc+9QJMPXb7HkGntgkMAFJ/u9KTGiSSQlVPqSeuaozKXuW9zmrBz/dB9xQyfKZDjOQMd6L2Ha5GAFXA6U09aUnmmmgYxhTO5p7dKZVIiQUdKBS+9Mkafemn0p5GaaetIYuMr9KQU4YBx2PFJ0OO9MTFpaSigQHmmnr6U7tSdvxoGgE8inhiR781NHeMhyBtPqpxVYjBpQKQ0aC3EEv+sjBP95flb/A0htw3MThx6dG/L/CqWKersmO/1oHZMmC9yOB1pANzDGce9PEySY3tg+pqCSXdwvC/qaLi5RzzBOE5PrUPLHJyT605VDcDrQq+vagACknAFWY4AMF+AT1oiXccRjJ6knoPrVgX0Vng26iScf8ALV+Qv+6KAOn0bS0ihae7e1sYuCtzeuVP/AEX5ia2h428PaApj01tT1WQHd5szi3Qn3x8xAPTJrzGa4muHLyyM7HuxzTooGmYAY5OMk4AqWr7lp2O/uvi9rk88jxW9jAZBtYiIuWHuWJrJvvEMuuxMb6wgFwgAS5iXYwx/CR0I/lWdZeHJ7p3UhgVGeBx+ddFrnhKbSbdp7fzpbaIhJt6YaM4Hze6nPX86zaV9DSMnY5on04FIO1OIqVVUpjHSm3YErhEVAZWGVbv3FKUQN8mX/DFMCn14qtdS7B5Sn5j94+3pStqO9lqNuJxISke1UHU561QlkLYXvjBp0j7R7molGOT1rRKxi3cUDApwbAPfNNopiuFKBk1P9iuxD532abysZ37DjH1qHoODgnvQFhQVA9/5CmM29uOlOZgqBQFLeuKaBimAo6U4CmipsoI8AZY4JY8Y9qTBAoyP5Vs6HHN9oj8hikjyBUYHHPTr+dZUUTynbGpZvQda6LTYvs0KsZBG+BHETniR+M/8BXJrKo1Y3pRfMmd2dQhh8N6hqFtHFAVjMUe1snnMSAD0xubPvXnH8q6vxPPax6Zp9paRohMe+QrnLKvypn34Y1yuOPeuPDrRy7nZXetuwlLjigClwa6TAlEgNvtA2kfeIP3hUYGTinJweg5PU1oWuj31zh44GRM8PJ8o/XrUNqO5ok5FJE3Ac459OKtQwLNiJAWlJzweMfjWwmlWcFsyTv5krEHerbQo7jnr/8AWq7pht7S4MduqmSRSmMdvXJ56CuedbRtHVCjrqYsei3LztEsbtt6kDAz9T71t2WhQxQYuLhInJyWjBdmX09BViyh1HU7gPaWUs4Y4yF4HPrXTL4LnRXu9Yv7axiUbvlI6fjxXFVxL2bOhRp09WZlvFo+nmN4bNN6jAlkO9j746Cuhhmu9Qjje1gkk3qd2BgKelZ48R+C9AjH2VJdSuB/EFzz/vNx+VUbn4nandK6adaW1kApK8b2/wAB+VccqVWrrb7xut0hH7zubbQZ3jZrqVYAy84YkjIwevtWRrGsw6JarHoMaSXMhK+c+G24yCcHvx+lYela/c3d/BPqN9Mw+VfmGUOQd2e2c4rS8QWKz2o2IAkMrYCDJb1x9DWChyTSkCpycv3jvfp0/wCCeeztJc3TTXcskssmd0hO4sfx7dqdDbG6hUxKRtO12znqeM/yq+1tHJcyRSmRvLjYqUxy2egAzwT2rd8OaNHHI9/OJYYrbLgd3B4AB6HjIP1r0J11GJo4W1ZFptq9vo7xmY26SSearSjAiXoGIPUt0qHWGtbdIpYrR3ULyrfLEpx0wO561NrN0927SyRkWsXyR25O0gY4P09TXN+cCwEobywc7VPB45rOnFzfOyn7qEvNSnu87nVQQFMca7U46cCtLTxpcmmSG7ZVnBwoZuQPYVguF3kqCFzwCc4po79Dkd+1djppxstDFVLO4spIbepO0cbhxn/Ip8dq12zrAm7y1Mh3EAkDr161FuKhlwOT1I6U+eWF0iEMJjZUAky2Qzeo9OMcVtZ9DJtCR/ZoDILiNpXBGwI+F685PX8qZfXbXk/mMiIoG1I41wqKOgFPghWaRA7ABnC4B5x60upqq3fyIirgAbFwDjjOPWmmubzJkny3KsRAdS6b0VgSvqKbLteRnVBGGJIQHge1OLEoEzwDTQMds5rRGTGooyN2cZ5xVu5e2a7c2sckdsWyscjbmA9zUW1cLgnPfI/lSbeaT1GhNuW9BSlCDjFT26I7hZXKJycgZ57UpVSi4B3Dr6Ypc2pXLpclt5I0EQlgSRFJLDOC2fU+1aVok5t5EiZfvcqD6AnJ9sZrHUYPPSt3TPKCtK8J8oAJId2eoPb34rnqqyub0mYUgJc5OabhgOCQG447ir3lWzWcskksguQ6+XGF+Vl5ySexFa2geH4Nb81TdSxvDHG/lhRltzbTgn047d62i76GE7LVnNeWTikKgdSB9a9l0/4Y6aIg8yOxY5AmJJA9MDAroYPCGl2kqGHT7cKTggQpx65zW6pyOSWIgjwSyt4XExlAP7tgnzYAbsTWtovhie/kSa6VorY8hT8ryD2z0X1P5V7JqvhWzawk+xQxx3SAPAwjUYdeR26HofrXOB4fPM9vEWR7YXMSY4IYfMh6Z6MOSOnGTSdNxeoLEKS91HCeNdDisLmLULWJYbedjHLEvCwzKOQPRWGGH41y8cTSuqRqzuxwqqMkn0AFe0X72drqCJPEs9mzwyFJIwyBQducHoQJByfQ1X8RaTp2jeI9M1CxiS1c70UwoFHmLhwcd8ruH41XLpcSq20PHQpLbQOScVoaqlza+Evsc2F/0veFI+ZR5YbB9juBx61u30ttbfGLbNGnkPfxkrt+X51GOP8AeNZnjiUvNOcFVkEM6qTkjMexh/30mKnl1L5zhEPleXMwzGCQfUjGD/OmalbSLJ9rg+6qru29QAMBh/snH4d6b1KgH8Kt2twYQqSBvJHKsv3oieuPUe1aXcdSbKSsZ0d+HBE6bnxw6nac+9XTvEzRu2UQLtI6YNJqGlAfvoAo3KWBT7knrj+6fY/hT3X/AEfzyMB0QD8Ac/yocotXQRjJO0isZUjjRnzu24QL1P1PYVe0xEk1O0kKFoo/3si8jIGWxn3xiqiWcl3PFCoLEKAEB69yc9gO5robd4YVeGAhoo7WeaSZRgSPsZBj/ZGcD8TSk+iHGL1bOhufDzXVjb6vofmXmm3RwiqMywP3jceo9e45qi2kalbybZ9OvIz7wN/QVT8DeKW8N6qY7hnbS7vCXcQ7DtIP9pev0zXtdrBHdmMs43s5TzlkO1HGOgz0YEMAPWplDsKNZrc8nstEutSaZLYxm7jwfsrnZJIO5XPB+mc1t6Yj6QdjoVvU+fynTB3dFHrgdfwr0ybS4PmjubbzPKj3q7Hdhh1UN159KmbTrG6tEBWO6jVA0Qm+Y7SOMP15rCrh3ONrmtPFqLu0edEST6iNPifcgba7E581/wCI/wA8V295dmw0mKSBAZRGSq8de5+n0qgvh2C01Fbix82Mq214ZiGKbudynvnnFZuvXpuFIjhuGwjQp8hAB5yfx/rXjV8POM0mtDs9pCu1bY5tEa9EhYGcyjcQZCAp3E/j/ICmG6MMiGz2tckcuo3CM9MLnv33e/FS3Nq9rGliIilzcICzgdFPRQPXjk1TWW3sVC4Es207ufkU9s+uPTpW8V2OltEs9lFsF5LMVxg438Anr83Vvw/OqtzqNuFjS1iiwAN2IgBn1ycse3OaqNcSyTM0mJGf5TuA4+npTDFvlWMKyZK53DkE+g6kVtGnb4iHLsP/ALQk2ljLOZuit5hAX3qBpXZMk7ieRuJOPepI4wXZEjLSg7sk4KgZyMdD/wDWp0tp1aNhIcBmWMErGCM/p3rX3UTqTwagLeF4xHnIBV2J3K/8RXHr0yavWmtX3nRymVnWPhYmc4x16dwPesmWGCKaaMTeaq8RMg4c+/p3pIZPLclgcY6dNw/wrKVOLV7FqWup2ulyQ6is0csDOBl9ittwf7yeh/2a17HQriyvJZyyfZtgy54WVe429jXLaRfxWN0bkJ5jIMYJ4J7V1FnrrSqIL0RmKUMOByhPQ15laMot22HVVT7Gw3XLuKTRZbXTx5aKAGjX72cdT7Vxsc8UqSWjI6JIu9Nw3ESAHp6KefpXQajbG1ufLZwFK7kbd8jr1xn3rmpIxHKLmLzPlYFi3Zs8Af41rh0rWLhFRj7pSjDWVyuyNjKo37lIwQOhBrS1GT7TJDIfLhlRASxIGcnhhj8DVWQLJL5yLseSQ7EBwF74Hsc1VY+Wx2xKJS5BUnOABz/Wuu3M79QvY6HXlOraHBfrhmB2y4UkqyjBH49a4OeIo5Haupsrstp97CXYt8s0ar03A/MfyrFuoNmHKZ8z51JPGM/41rhr07xZhWgmjIIwelMxirDxHJz1oMAESyPJGgdsKGbkj1x6V3po4HFkDJldyq2B1PpWx4cuI4Ll/MbG4ce5rJlR0wpA29AVOQaiDEHKkg+tKcPaQcSqc/ZzUjd1Ha11KxcAPk7s9KyTcLFbSJHtyeCSOT9KrszP1OTUZohS5VZjq1+Z3SGUg4pxpK3OQ0NN0a81YkwIghQgPNIwVE+p/oK7DSbfwVDatp93GL26fKyXLlk5/wBjH3azbO1trfQI0e823e/z2hGMAEcZ9SBz+NZd/eRPdb0jZGwAxzksfU1gpOTOhxUYq+4zxF4PNmWm0ic3Nr94RPxIg/k1cSxJJUg5zj8a7ZNUZVCZY+ntWbfQQXdx54TZNnk44P1rphNrRnLUpp6xMC1WSC6jkMZYK/K47d67GH7LIwNndKrD7oD7Grn2QoxRgQw6ikxROPNrcmnJQ0sdDcwzTNi4iWY+rrhv++hzWbLpwGWRmj/2ZB/7MKbY3V+JVhs2llY9IlUyZ/4DzW5Z/wBoXU32aTRLl5T2hjO4fVTWf7yPmbfupeRzkkEkKgspCno3UH8ahxXcnwjqu9P9Gay844AuiEVvbHOaSb4d3cbs015aW8SDdLKNxiRc9dxwPwrSMr7mU4pPRnFbeKneRXhQBQGXuO9WL6/8P2EjQWcV1qjoSDcPL5MTe6qo3Y9yabptvPrrSLp+lz5jGWKvuQexLdD+NNrqxRktkVoonmlWONGd2IVVUZJJ7AV3NlY2/g+1S9vWtV1Nl3RtckFIfTaOrH1I4zxmsRdH1rRyXja0t5pVKCQsHkTPXb2U+/WsybTC0265eS6uG43zMSfwqboqz6Gpqvi+x1G9aa5ubu5+bICDaufXGeTms2TV9Hul8trBUUDCkqMk+5HNKtikRG8DPQgAAVl30ESuGVQM+lUmmS4tIgvbSANm3yF9zkH6VBZ6heaVcB4JXQjjg1NbyQwyMbiMyJjgA4warTFGY7QQvbPWtEzKS6ou3M4vYvNhwjEfMqjAP0HY1mHnj+tIjmF8joeoqVkaWUCMFmfsKohkMb7H56Hg0rL83I5NLNGkWF3Bn746D296BckKBt5/KgLDhbyHGV2/7xAp5g2gAyxgH0yf6VXaeQ9CB9BURLN1JNAWRYdY04ExI7gDFR74R03GoCMUAcZpk3JzKMfKuPqabuy2emajxT1AzQBLgDpRSA8UZpiFOKYVBp2aSgCJlwcU5MkHHXvSuOM+lN5HzCkMBknJ9aeRx70g5FOPSgQxgMZp0ZyMGkxxQnDihlLclxS4pcUVBoIPStCz1a4s12Da6f3XUHH41QAoxSaTGm1sa8urJcLteKHBHUxAEfiKS3vo0cW8oAtnI68+WfUe3qKyaazUuRFe0Z2mm6wNOuJIGGbc9uu0+oPpUWvXFndtmBczAjLrwCP61incbW0l6l4yCc91OP8ACkdySAR0rnVCKnzrc63iZez5HsNzhtrZHvTWPQtg4p5wP4cjOKRlZueuB1Fbo5GREliMfhTSMEA08HaaY1UQwIYgDnFNHDc1N8oC5Pap7qzEcSyxsXUjnjpS5knZlKDauuhRY57U0gDGPxpxpCKszY3qaOlSCIshfIGO3rTMUCsJT1jJYDpmlQIpyx57VKWC/N17ClcaRHL1IwOKuTRf6exfIQgOcehANVEUyMAe561q6gXtXmWSErNGFQpIeQQP8mok7NI2hG6bYun21ve67aQT7YEnlGRuCgL+PSr/AI61ddQ15xbOGtIVFvGB0wvXH41zNvDJcztIxO1fmd26Ci4kEsgC/cUYX/Gs/ZJ1FNvZF+1tTcUtyEnJPX8T1qInJyamxyDTGGHIPY10o5WhgBPTNPQEVbTybeASypuZvux56+59qqvLJKc8KOwUYFArFi1tGupSNwRFG6SRuiD1qykYlBEAMUAGDI33n/w+lJIDDBHZqTuchpT6nsPwrSjW3VkMhCxJGSwJ6Y/qf61LZSRd0fSY4Ue78s+ZkRQZ5JcjJP4DH51m6xMLrVBBErbLVQuzHVz1P+fSty2utttBvwpMb3DDPG5sn9BgfhXP6ZDLPFJekFt0pY89/wDOaS7lPsMld1Ys6/OF2nYeKmjyLdC22NUyS5OcH/61EhAuAUHJGce5qK83N5NimAJXyzE9geT7DOfypiK22bUJGkAMVsOM+tLNpvkgHysqwyG610kEEQVEDBLeJflGeo/vGsi81ZSxttNjMjZ5mYd/9kdvqaLhZdTGa3IPCke4qJlI6g/XFaEul35QSzuRu9TmqT280R+8fx6U00S4tDBg8Hr/ADpMcE+nWgAnggg/zp6NyMn5uxpiGAbulAHzYNSOuOV4B6juKjJoAlwABx+FM5XOO/FNDdqd/DQA0+1BXA5pw4XPemsSaBFu5ufPgjQr8ynk4qpVvAPP6+lQSqAwI6GpjZaIuV3qxgODSHk5oxRiqJHodrjIqWfAVR71X5FOyTyTmkO+g7Penj1wcHvUajJwOtWUJaMjbwB1obGkPSQNEUb0xmquMfWgMQcCnjrnH40tgeonPH1pXY5Bx+NRsxY5xirLANAfbn8abBK5BKMPnseRTVHIp33gB+VICQc0CJCo2k9xSDFBckYxihSKAY6oW5Yn3qTvUbHLE0AODAAU4szDpgUxV55q3BDvOAufrQBEiMeNpI9uKlEJGMggnpmr4sysRyQFA3ZPB/A4qK4ESXAVcsoGd5bOT3xjtmlcdiu1nJJH50Clhnay9waq8D73BHHNatvMFuHXJCk454+h/wA+tJqFotxF54XbKOGweT+FFx2urowzMwckcj0NTJLHLwTtY+vT86jeAIRg7lI60nliqJsSSKVIUjnrTVClxuyBnnHpTQxBCsTgcD2pcEf096AOmsdB03VWZbS+Mb/wiTqao6t4dvdJBMy7oDwJU6Vko7R4ZWIbsQauPq+oSWrW0l3K8L9UY5Fc3JVjK6ldeZ1upQnCzjZ+RnmNgcbaljG3gHJ7mmbmHHGD7VIDtUk10M5UgJ2njio2bNHWk70igpD6UtNPSgBjUw05qQ9apGchMfrS9qO/6UtMQ08UgHNK3SgDgGgBSMj3pDzg+tOXnBpMdV/KmIbSmkHNLQIKMc/WloI9O1IpDHXvQvWpPvD+dRkbTQOxItKQKVcOvuKDkdaku2gzFLtozg08UAkRkY5FTDbMoOQrD7x9abimEEZwcA0JiaHyTEDZHwvf3qJVJNLtwamQcgdB6+lUQCKqjJGa1LWKRhxAZExx5hCJis/zI4eEXc/948/p0oaeeUg7tpHQ5yaTGkd/o0zXCorR2CPFHsMs8mAgPHAzg8d66CLxRoem2MCX2sW8ssQ2mK0RpGYHPDM2cjpkfSvHzCznLMWJ7nmtPTtFa7bLnYgP51m7GsU3ojU1mbQrjUGfRZpEic8QzJtwe+05PHsapSW88CK0kMiI3RipAP0PSu80vRvDFxo/2W6sYUcjiTOH/wB4NXPanpeoeDXa50y6+3aPLgSxSrlCPR16fRhz9KmMk9C5QlFXMCUmGHzWU7exxwT9ayHlBJYsCxPTNekW2i6D4ht4b3SfOtw/+ttzcf6iQc4wRyD2NS3mj7FD2jrP5ZG6zu8TKWwflJIznA7Va0M3qeVklmyaWvR49J0TU7aS8tLG3gkgJW6spgT5R6ZBByVz9cVWm8L6VPcG3+yXNjdYJjHm7orgDqYyR1x/CTVcxHKcGiNI4VASx4ArbsbS0hRhKBJPj7xI2p9B3Nbh0ODTW8+DTjcwPEHaOVstt55Rwev4dqsreQTrutEsYrbBwfs43EAchie//wBak3cuKS3Mm4vo2g8hstxtG1jnH4VlPYAqNkrhf4Q69K3tSSE2S6pp6qnzbZoUGQvuP6iuekk8wbw2GPYHNJFNplSa1khYmUdehHSq4q1KWwAc/X1qt3q0ZNCinCmipEUuwUH8+1AkbPh63d9QR13DbliV7KOv+FdTpfkza08QdY4YUO91h3ne/BA9DjjNcvaXD2MLTwnaXGxdwzkVuojWVkkskgywIzGRvMpGWz3wAcZrhr3v6np4e3LbsVtXulvdSnliBEAOyIE5wg4H+P41QC8cVYZo1HEOR2y1Xm+wf2fFPBGVuSxEiMdwA7EU4+6kiZLmbZQtbK4vH228LPjqew+pNaa6NaWwzf34DYyI4F3H6ZP+FQPqFzOvlrIQv91eAKFg2DdNJtHX0/U0pSZcYIvxXtlZn/QbGNWA/wBbcfO31HpSfar/AFBsq00n+4MD86qfaLaIh0jEnuef5/4U2TWruTKIwiU9Ag6fSsmpPZG14x3ZuW/h4GITahf29rF1OX3NVyLWfCeijFtYTanP/wA9JW2qD7VxMjO7b5GZmPdjk0nTFQ8M5fHL7tBOure6jsLz4j61LD5Gni302H+7boC3/fRrnbu8ubybzLq5lnkPO+VyxzVaAMD5owBGQct0J7D3qdtjxvMz/vWfIUDjHOT7duKqNGnD4UJSb1I92RmprdysgbGcdRnHFQgU9O4wOvWra0HF6nRLeSKIl84kAgDPK7QOOPxrr9L1Um0EM0XmKxZjGMAbWHPPfufWuC05nnK2qoXkJ+TH6iuv0e8tFdI7gSkjaoC8hVYkFc9T9a8rFQSWx6MGpR1JrrTJLcoixu0iyKyupI+U9DgdT29RWvcR/adPbS7YBfs0YklOc7mPVfWtSF1U26CNkxuyWfIXglhn+IcAZ96zVhxJPNbKYpJQ3nsPvRqRwRnk564rzvaN79COfm36HJzRpMZUugkaoG8p2G1m55z6+30rCuUUzlIsuN2FP94duK3L61V5DJGTIqABUkO1n65IA7ZzWXLYTxRLMUAQ4+bcDkn0/KvUoyS6l1Fcz2R1J3KRg4PsaezyTIiMxYRLtQY6DOcVcs7P7QXZpY0CLv8A3n8Z7KPUn0q2bSIXQfMIdpFby0B2LnOVPoR6V0OqloYqm2Yk67ZnXPOetFzJDLPvggECbQNgbdyByc+9SXkapdOqKVUHAGevv+NQ7ea1i7pMxkrOwghkYFlRiFG4kDoPWoZC7nLMW+tdPpGv29jcjzLNRHJH5U4XncPYdqwLqFoZ2Vo2jychW6gHpShNuVmrCnFJaMuWMOj3GmSx3M7216uXSRuVfjhcVlgZ60uKeFGAc856VolZt3Ieo9CCVDINowCBxml+5NuQ/dbKn+VOQxjAJcLj5sYPP+FPMe1d24HnFTcu2gm0ly/GQcmnKm+lbDsGAxkDP1p6rxUtlJDIlXzlLozruGVVtpI9AcHH1rt/Dei6N4ggll0XVZ454eZbW5iVpIz0zxgMM9x+lcgsZUhu/UVB9uufDviVdTsNyTAiaIAcMpHzKfY8inFxbtImpCaV4uzPRY/AOmI0bT6hdN5zMqKsaqC4/hzz/wDWquukxeD/ABPp7CeX7FqSPZzFm/1Tn7vzgDPOD+dbUuvaXILS+toY5Y76MSfMhO0nkc9yCrKcd8ZrG8f+IrfU9DuNPggaMptlSTcAVZeeB2GK6lGK2POc5y3Ot/4TBPsxtzn7UiYdnYAbhwQMdeasaf4rtmWOK4BkuQv3kGd/0HavE38QSSXX2uQ7xcBZGUtwSww305BNQ/2yyHzYbgrycAsSuKu7I9nE9pv/ABbAkYWCVfMJP7t5MbRnqT/QetcJp+s2+oWEtq7JG0M8ixMScDfl15znqWArhpdXferMeS27KjBb6DtVbSNTe2ubgpjeNrjPQkE9fzod2hxST0O51bVrfFskUjFXtpYUiZSoiwmBjk5yQD2GaztV8VyahYWAaQFo5o5hgklQcq24nvz06Vy15qbT/Zd5+YStJu7nPB5rIN5MLR4gR5asufb5uKSjcttI1/E+oG+1Zr6PKO0MeDnkFflz+lN1PVP7UWO7DfPKjCcd8kgn8m5+lZV7ITsYdwyn881nxztA5bGQ3Ue/rTSBvoPAw4Xj8KugEQYA6Hk/0qFY1mjMseCy8lR/d9R9PSrKsPs4UEc8mpqGlFbk+hTqk0sUgDQS71aNuR904Psc4qtdELpFopHLJ/Sk0vpI+7G1Xb9DT9ROINPi7hB/IVm1+8NU/wB2MupzbxvAhwGQCRh1bj7ufT271rW0tss0qXRZIGsAjCLAI+XdgZ4zxWBdZluXA6u2BWzpVzGutXcjqrwrbyoQehBXYP51ajsZSluM1extbR4prGbzrWRVZHJ5OeuR2+ldp4D8YNaWdzazuXMUG+IFurR9O/8AcOP+ACvPNLja9U2Jl2MFfb8pOSuSBx69M9BUen3TW+oxOGOGypwfUEf1rXl0sYXR7HZeK7mO1dLeUmGLLPc3fHnEkkfL13+mOBit/S/EdrbRNHdXIKJPItqykkiPr17kentXh8F629GBUblAJxzx6H9KvrqpVIk3ZCOcbuR8w5qHErRntl74it55beaAhMsYMjPAPKnt0cD8Ca6Sx1K21azjlULmWPcUJHynof1zXzz/AG5OLdkMrbSQQCfTmt/RPE4UyQPICVlZlLc5zyP1JpaoXInseieLUhn8Nzyoqpe24zuXkhA21gD6c15VdtFsjWIkHB3gjo2f14xXRW2uJqV09oZlUXKTRFn6DIUD9aw9X0u80m6EF5EY2ZQykHIb6H26VyVI+9c78PLlhysoo0e8BiVy2GIGcD2FPmlRpJW8ySUg4R2GMqPUdu1QqnPUKO5Y4AqO4uLOH7l2koUcsowPwzgn8qi2pvdonkYoixuoBXDADHOeck1Ob2b5kjYw/KVIjGF2nqPXmqNvcWl04SK5tiTkBXk2E/ngfrV+XT7yzkV7i0b5vnG7BRx7HPI+lDj3QKXmQFiZMyZZ+Adwzn0qxujkEapsQAYZ8EdT1I56e1LIkxjjRraSEclQFJDH8eRxUSMjbAqcgYPPJ5rNmiNAAw74Y8SoHx56ZAf0rUik8uYrFKrDkZA+9ntjtWQJljUpMBGob5izEEnBA4+laGnywQk3LhXg2Nk8n2BzjAI61zVItnRGSsdIjR3mmxWcp3Nysb7uYz2B+tYl5DiZYsiEz/LIjn7jD+I/lTrDWbKSZYPme327SwXGwk8MMdSKsaqqCOO4ZcyFX8xs8ZAwpHPfj61yqMoSswVk7Ix7S2W+mtNPabfvLKkgbPlseg56DIH51S1BE81gEkDhmSUEcBhxhfbipTbSuy3cC+QEG9pHcIoYHqCas+Ib3Tpit5DMsk1xiSRQCAjgYY9OQe2K7Ip8yM5SV7FCMrBDEwQq8iN+8JyGU/LjHt61nPE5fb1KDoD0xSNf7+FQuSOmNqDnPQdvxFU7u8Ll2ma3RnbcQigbcdgBXVCDuYTmrBLJFEVkJEzkE7F6A+5/wqnc3G1/NnKvI2AiL2HoPT+lRSXEfz+UjMx6bvlUfh1NMhtJbiRmOTtHzyY4Qeg/wrqSS3OSV3sSW54eVyN5+VQO3rj6f1pyRqclmwAPTqewqxFHAEcOzIVT92AM5OehPbvULgBjjoKaZLjZEOSpyCQfamY6n8qlKgNzTWA6VpcyaIgBu56U5I2llWONSzM21VHUmhgB0q7o13Hp+preSruECO6r/tbTiiTai2gjG8kmJrMD6PrL27uHlQDzdp43EZwKqR3cUj7WXIPCLnv7mqU121xJJNMxaV23Fieuao3MobCr34qqcdEmTWnq2jqYLuybC2tnGzEEB7hgd2By55+UegHWtHTbfQL6C3hubmWa7lYqQpEEUR5OSe/Tqa4VLl4w/Pyvx+A6DPpT2vC6sAgUN2U8Z+lbcqOZzZ6ELfwm0sMJYyGISCQvI21VHI+YYznsP8asW1hopWKQWVvDPMT5VvKDlcH+MkccD6D1yK83S7wvXDnkEj06VL/aDvHjfIZZfkZicnb7fWjlFznqdre/21bzw2Ajg0iAFZDaqIZLvAOeRyE9F6nBJNa2l6tpqIIYkFrZn5RHCyxnaBks5znGO3f1NeKJfyou1DxyCc9v6VI92xtgxkw8pzsC/rmjlJ5j1688Xy6hdyWXh+JIImlCfbGG87ugWNTxn3PFcD478US6jdf2Ja3Bks7ZsTSg83Mo4LE9wOg7VRtdbksNMllQhZY0MMGB0LD52z3OOPxrnbZcsCeT3otYpam94e0CK/mD3RbyFPIU8sfTNek281tZ2QtbcLFCi/KkeAB/9f3rze21PyIljBbAHQGnPq8rEckDtk5rCalJnVBxijqry6jMYMswJBPQVkS3Cb3kRck/dPoKylunuW2dffPai5ucIsYGMDnHekostyXQkuLnCk559ayJpt/ekllLfe4A7VWL9z1rWKMZSCQgimSDZtGRyM8c0hPem1ZkMIBpwmkSIxq2FPXHf8aQ0badxWI8UmKe2AQKUFMdeaLisRY9aDxTyV7VCxzTRL0ENLjgChRnmndPx4FUTYOwo/lSgcdKMUCAHilpMYrR0zQ9T1nzDYWckyR8yS/djj/3nOFH4mmIoUV2dt4P0Wyi87X/ABCikAH7PYoGJz/00bC/kGqU6v4N0s40/wAPpdOOkl67Tk/h8qj8jU3HynDr8xCjk+g5NWodF1ScfudMvZQehS3c5/IV2R+J2qW8UsWmWdnZI/C+TCqFPpsC/rWXcePPFN4pWXUZnXqAQTj6Zzii7CyMo+GdejjDPomoqvq1q4H6iq76TqSff067X6wN/hWkdb8Ryq3+kTlcHOVGAP6VB/besgEGdjnr8vX8qLsdkZbxSx/6yKRP95CKjQZkAHrWyviLUkGGAI6cEj+tMbWll/19orHrnaCf5Zo1BWKW0+lGw1cFzYTdjGfy/wAaeIoThg+UPfrUO6NlyvqU1iZsBQST2HenvbPHkSAIR1DHBH4VdimW3niljjUiNgSG53fWtfWb1EaNpIIL60mTzIi5zIgPYsOcg9jWMqklJKx0QpwcW7nJuyrwDk+1RqC5qxObdpC0UZReyk5/Wo8+gFbp6HNJakyTuiRoAvyng45NXYY5Jm+YAMBnArORPnDZya3EtrqzYNNBLErDqy4rObSNacW99ikRgAHjvUzRSW9osiyECYYZR6UtwFO1gCB0qJ5XMSxsflByB6UtXYNI3IGFPt4DcTrGDjPelRA74JxilK+S2QTns3Sqb6IhR6vYddxeQfLOMin2U4A8mTlG9arPIzEljlj3pq5zkcYpON42ZSnyzuh1zB5MpGcr2NQhdzAdBVmeczKm4AEccVCpwwOMjPT1qk3bUmajzabGo+iagNL/ALQMBFqOhJwSPXHpWYq7nz6frXVax4u+36SljbW3kIVCyEnPTsK5YHHIrGhKrJN1FY1xEaUWlTdwc564GO3rUQIwR+VOkIY8DFMxyK6EczJ0Hp3rrr+z/wCEh0ePUbcqJ0QQXKlsneBw30OP1rkIUaVwqjJNbem6i2gahHKD5kTDZPEejoeorlrxbs4bo7cO0k1L4WUruF001BEirDG+2Xac5fHU1knj6112rW8VjqDRxsG0+/QbXHYHlT+H+NcrLGY5GQ/wnGauhPmRGJp8rI+pFInlGTdMzBc5wo5NOcBYuPvt+gqMR5Ga6LnLYSVzNKWxgdAPQVPbqDIgPTcP51Eq9vWpk4xjrnilcEi1K+LrzwoJ3Egden/6qdcXS3ckcWzbEPnkGckn61XlmCSMvUE7uOqnvVfzPKVtgOSOpoEb09ziO5wMfuNqj04xWfb3Pk2aIrMdw5CtikaQMZMn7yf0qlCxKKPQ0JDbL3nMknLfvN2SRyM01LiM6hum8wgRhU8sgYNVWck78gGo2kKNu7lcU7CuX73UZJIRZxMRGBhzn73t9KfbSJbBfJPOOXx1rLQ4FWDPH5EQRWEq53kngjtik0VF9TZj1SQMQyqV9MVFO9vIA8Y2k9R2rJEpz1pTKQOtTylcxYNukjYUhWHIOeKhmEWQjr5bjqRyG96a0vlpk/eamwzRs5+0qXB75wRVakXQ/EccOXYsf4Sh6H3qGRomQFFYN9RinPFCSfLfj37VG1uyruBzTQmM607kcGmoxRsmpS6uQMYpsSSsI4w3FManHrTTzQJk5fAHpUTNuIozSUh3CjHenrGWGenpTSMMQaYWEpaTvS0CFHFTZ2w57npTYo95yelJIedo6A8UitkJ05/WgEjjPFJk0UCDaQM4qaKQBcGmq1LgHBoY1oM7nHAzxSgdyadsycDrTO9AhQBRRx6UM4Y4AwTQA1jgYHWkUZPHWgjHSjHGV60APU9DV+0nbeqqyqcHk8Z46ZrNLbjkcHuKAxHQUAac95IgMazu6EcZOPwI+tVWkJctwAOmKr55yeaXdn+tAyfzD5hJxznp2q+bgsgkwpOOR3JrMVRGkgZSXJG1geB68flSh5UkYRtxmk0NOwXP32x3+bHoahFTyQyBS7Z3dTUH3SPSmIQimBtvB5WpG5phFANDwMgYOR2pDx0z+NMXcp4/KplKvweD/L/GgLDMc0Oc8dhUjIIlyx+c9B7etQGkNKwp6UUCigqwU00tGKAGEZpCORVqK3LEZB/Cm3cRikxxyvbtQpK9glTajcrrSGnDrikaqMiNvSnnAAph5andfxpiFHBNBpOw/Kl4NMXUa3XPY0Uo54Pf+dJj8xSAUVInp61HinqpPSkyluDKY2yOlLtVx1/Gn8kYPNREFW46Ui3oMwyHNSLMDwwo3Bh0phTjijfcSuthzAdqRWwcHpTCrD1pOfenYVyyBQRUcZboRxU2Kl6Gi1Q1V3HbjntQeOF/On45BppHNFw5BqgD61IvBplKDQItwbWODXQafOsa7CCM8Ka5dWwQQeRWlZXmx13HofWokrmsHZnQwaksZaKQ5QnK8dK10163MYtmCOpXaUPTHpXL3lv56efbdDyQPWstpZVbDZyPWpUUy3No0dPvRoniOWK2bFrcHaPb+7+RrpU8RbdVjaWYRRlSVkBwBgcqRz3HB6/nXnVxKWcP3BzV5pWmaRSf9YNwye9a2OZ76G9q+rqmp2+sWmd7JtuF3f6wdCD9RT7nWY5rP7Msh+Vh5Ug6xkcqQex/+vXJs+T5YOQuRu7U6JlKAP0AIz7jpVWJudEfEE1zEku4LIGO5c4AJ649ATz7Vkm8EV08gTMTNh0Jxn/9XNZ+8jcAeSRzSEkoAAeASaVhmja3xWd0JIikB49PpWezGOUhTxk0xXJZT7HNNfls+9FgvoSeZhg3oelMdt8jNxz6UhPtSDpTQN9BRVmCMuyxjq/U+gqBQM89B1q9CCiZAzLIcBfr0FKTHFXZp6bGZrvztuYbb7o7Fu35da1PspupstIQp4QYy3/66gd4rGwitUxvHJOOfc/if5U2O8bcGz84P3q4k3N8x6LShHk+86CDwfNcw+chdYhwXxuxVO90M6bYhrjDEyHbLGcqR6fWui8G+JJNF1mKO+wbK5GyQnoM9Ca0fGk9vaX8kD7TaXXLIowMHoR7jt9cVDbYl7r1R5qJmQYTC++OaiYsxyxLH1JqSePyZ3j3btrYB9RTK1SRDbegsZADA9O31pOhz3pSOAc8mlxwPWmBf0rT11O+S2eYRNIDtJGfm7Cqs8D288kMgwyMVNT6XZXd/qMVvYKWuWOUAOORz1psiyTXDeYSZcncSep71ldqe+htZOO2pXGcY7elWEQeVu3Dduxsxzj1qMAAitGWOL+zrWWHIclklzj7wOQR7YIolKw4RuUMEHng1OgiMDbt/nbhtxjbjvnvnpTGXJJzmn7AcbCTxzkYwaTZSWpJExDDDbe+a6rSbnz5raSISebG372Nesi93/LGR+PeuatIVNwgmVjHnLYODt74rX0yZItYSeHciI4Mal+2e5+lcmISkjro3R6Hoc6/Z7qF3Lwqj/PnIUHsM1BHFJa3UMgkU5X5pMkBl6bAT15xVK0vZp7PUnt90byr5yICMY3c4qfSphdQyNKxCRjB2g5X0YZ9DwK8SUWrs15bOUjLKA3v+j2YaRWaOWEkNle+M89jVAqPtUIkG21JYxiJBvAzxx79K7G5tEDzXMcYSOReZEbGCQRnj3x+tchfnyVhaVU85kKDymxsA4+YfrXRRnzOxakpIpXLwx3D3EKgox8xFdvujOMYHeooLhradpIzIqNnaGYHAOQfrwcVPeQl4orlUASUHIRdoGDyuPXvVZxbqqIAHf7zOrHBB/hwR1FdsbNEsrahcSXl0JXCKwVU+QYGAMD+VVlQnmrMwAbaMeuQc0wYUHINdMXZaHO1qVGyrA9CDSzzS3MplmYs57051yRmmFcH1960VtzJ3GBcnnoKX6dM04LzUm7OcALkAEDvincVh0MAlYrv+YplAozub0qVy0yLtiwsS4JA569SahUlenGacu4cBiNw5561DLViUw7EQhgS2eB2pUHFS27p9nkjkRi2QY2B6Hvn8KcZxaulwFjYxsGCyLlHI6KR6GovrYuySubGh+H7nWJYznyoGJHmkZzgZIUd65T4gWsVj4hMFnK7QLCiqWfJyM5z6ZNel6tqEtrvvraIRw/ZwqxhsCJypLdDxhl215j4wuhcagrqh8x4h5hOOTxhh7dK3pRSZyVJykrvYg0vW7n/AIR6bTHnby7di8YJPyq/XH0cKfxNQma+utOkvIYpTaQbY5pAeAzcc9+axrSRlusdBIDGfx6frionmeKUjcwTO7APeupLU5ZbFk3J+yopOdhKc/n/AI02O8McZTaST0yeKppLgFWz8xBHsamWVVAEkaMvIBKnP5iqIvfUk895MJzuAwKbDLsE+eu3HPbmonmXZiOIKHGOpyfajcSkgAOdufrzTEWW8xkFxhQgIAXPSqrMfLl54Lf1pwk80xDcxKjG08gD1qPcDE/XmTjH1poGXlXzokUtgFm/PFUJoijlGGDmtJAkVnM3zedFPlRjjbjmobqRLgAqm04zWd7M0STRRhmktJQyk8HPv+Fao8u5TzrXhs/PGOhPt6H2/KstlDDB6io45JLeXfG21uh7g+xHem1zAnymha5EMikHhG/CrGqnbqcMY/gUfz/+tVZb+3uXX7QjQMcK0kRypHuDzUl/NBJqctzHPHJECAgBwT749Kz5Xz3ZqpLksmQF/LnebPzAkJ9fX8KUAwxqVJDP1+hqHcZHLucZP+fwpxlElwD0CDP49hWiRlJ6EIbbLLhioDclfQ8GgMUkjbPRgaSL5roqQTuUjA9f8ikIyRjqT2rRmC2LTyMpZf4dxpRMTg5/izTR80zlcYyT83Q03zFOf3SdOMZGPfrUlkxnOeverEF35UxIPfj86pGMZzvUqMHOadtTZv8ANG7HCAd89/Sk7FK50/hq/wAa3HJJIkYCudzLuAyDjjvXpL6jba7os1jcBDtBZbpm53Do4HYevtXi1tOYHD7dxPABrWi1ZxKu1WjJUq3PBGOmK56kbvQ6Kb7nq+n+AtPSLdq9155PPlQttjx9ep/StiLT/DunLstdMswFGN3lhj+ZzXIXmtyQ6bb3vl/ehQ5c5DnHJrlbzxNd3RI87ap/hTiuWPM9jqcOsmdf4mi8M3yNA+m20UmOJ7cBHB9OOD+NcTBqV34enFvv+16du3LG/wDCfVf7p/Q1Ta+cjHXFVbq6aWIoenb2rWKezJaSV0dXfeIBeO32oK9tcIDGYZAmMcA45IGeo49qz7rWhIpV4NrumApYMpAHVT1Dcdehrmre6ZIZofkI+8N65x2OKa8zuWZiCzHOQMYqlSSI9ozorbxAbRgYR8rAr+9wxQ+oJ/lQ+sSyTmRpXJY/OCxw31rn4izE56AZ5q7Gm7Zx9cVMoJGsJNnXw6WscEl3bsqSLlmUhlB78Hoao23iU2kYihaf0KIQBjOepz39hUC6rcxsAjttUfKrc4/HtWfcqz3YutgXdJkgc89awjHX3jpn5F271abUpSVty7lifkLOT+Jz+mKli0TxBqLgpYNGvGWlG3oOOWPpXSJcX0LJLHdGBJEZowgChhjjoPXNbl9CV8Mvey73e6iSPLsSRjljj8K5pYpxaUUEqSW73OBfwsY3K6lrNrDg4KK5kb/vlRUC6doluxBkurnBx8iiNT+eTU8nzFpNhGcc1VIGAQDknFdUeZrVmcklshs9vpssyNDbTRJ0ZBLnd6HJHFPaVVgjgSNUjjzlVPr/ADNMClnx3/lS33lfOISDHCAoPdiep/P9K0S2Rm31K3lgtwSR64qu688DFaukJvkYYzxxk1BqUCxzEqpGe1VGfv8AKKVL93zmacnApOBwRzTuQeOD60ojaQEjtXQchCfpTOQ2aeaYRzVEMzrnbby+WchDyjH09KozYBGCOD2q9qf7yVEzwo59hWTyCccVrCOlzCpPWxaI3W+e6Hafxpp+6Dj1qS1mQMfMH3hhlIyG/qDU72UiMWj2upOdpbkUc1nZhy8yuinIMOwHY460MWBU5weea0rewa7TEOxnLkFS2GX8PSoLuzkhKrJG8bK5Vgw6dxQqivYboStzFMbgcjHPFO3ZlGSfl4B9qesTB1OPcc9aaEyxPoTnFXzIycGJcSExImTzziliDAcUy5z5ig/3RSoxAo6DSsy6kUpAJHHualjiXP71wv05zVDc/rSEk9zUWNE0a3nwwRMI8lz3NUnkLHLHJPbNVxQTzRYbkDtk9aaTmldGUAkYBpMcUydRCc9BSYzTsU9I2cgKCT7UXBK5Htp0kbxxrIyMFfO1iODjrj1rb0XTIH1K2/tAMbYyqJEU4JXPPNezeKPDdlqujS2SWsbNbIDbxxkJ5YH938O3euDEY+NCcYtbnVTwzmj527+tNYDFbF7oTwzskUquASBv+VvxHrVB7CWN9khVTjPPNd0akZK6ZzVKNSLs0UjTljLAn0qcQBWIbORTGbaSOx7Vpe+xi423G9M88d6Qc8mjGT81KOKZItPiiknkEUMbSSNwFUZJqxYafLfOSD5cKn55WGQvt7n2rRm1mCwtJLDSYgnmDbNOcF39Rn046Dj69aALtrpGlaLCl5rkkd3Pn5bFWIQ8fxMvLfRePVh0qvfeL9RvYY7W3VLeGMYjSJAoT/dUcKT69fesqG0nvJPNmLkEjJxkmuq0a3tNKkivkt1u3gdGeFkYlkJ5wODnHOelDEvIztM8H6pq9yEeWGGVwGKzyfvNp/i2/ePHtXc2fwss9Os7s6gH1C8iZVQo5jgXPbGN8jd8DGau2s9hpk6X17cObaxlMllNebEkb733sfM2S2ecYCjrmqN78WLG23iztHvbn+CfPlqo69TknknkYNTdvYdl1JdG8F6NcrcWzxXEMzfPbXYtiUZFODleoGe/Wp9V8KWmlXzM8dxcq+PLjsYTtbHBDO5wgPHPPFcjd/ErxdqQ8u0kjs4wCAtrFyP+BHJrGu7bxFeOH1G8uBuXeDcTnBH50WY7nYHTlQXMtxDY/arjB8oS/uo15OAc9RwKxDaRwq4e3JJBClJhwD1x+lc4dHl2BpJnyenyFs/l/nmmDSJsBlkIBBwfUjrRYV/I1bu3giWJBFJJtXLSKhUsT0ABOMDpnvWXJbxledqnGceh9KjaG+tn2GaRWB+7nNNN5dRsPNWOTHcjn8xVCbGPaKBkkqD0z1NQ+TLEcxsR7irC3UDEEo0TeoORUoywBUI6Zzwc/gaYiqt268SruH94cGrIu2liZFclSQxHfIqKZFDYyGxxkciq7RbWJUkY6Gk0mNSa2JmTgg49jUY9MUizfwyfnT2XHI/Klaxalc19B0a81W9jhtlT5227nYDHfgd69LvtMkjhwyiWIYVmJHP1B6GvL7CSS0kSZT83XGf8/nXouieKUnhMF8qzxkfNIR86f7w/iHvXk46NXmUo7I9nATpqLi92c5qfh/A8yyDEdfKPP5GubcENgggjjB7V6pqWmqsC3tqytbyDd8vQfSuavdOttQViSVnUcuB0+o7ijDYvS0h4nBJ+9A45WKMD3pHcucseas3dhPaS7JVwD91h0YeoNVSh7V6UWnqjypKUdGNYYP60r8HA7UhzjOKWNC7bR1qiBMZIx+tKRgCh0KMQe1NbnFAATnAzSZPODTkUHnPeldRkADFAhh55JHSmEEGpJAOMYpmc0xMmtpzA2R1NNllaVyzHJJqI9KO2KVle5XO7cp1Okzx6roNzptw2JbVDLC56hM84+h/Qmucdi7bjgnGPr70xJGQ5UlSQRkH161NbxefMEyfU/Ss40+RtrqayqucVF7oltIxGpuGHPRM+vrStEkkYljUBWO1gOmR3/GpboAyC3j69Dj2HJqBps4AAVWXhV6D/AOvRK72HCy0ZTeMxvg07a5A2LyTjNPmyygnPpTJWZUEK5yDliPXsKuLuZzSTI5VWJ3iJBYfxA55qB23mrwZRGA0QBU59vpVF1CyMF6Z4q0ZMtJJ8yn2xVdTgke9OUkqD701v9YT/AHuaYmKcE4B4J6Uj9F/GjsKax+7QAopaaG9RS596koWgdRSfSlwaAGOxZqkWVcBZFyBUWDyw9aAw6YqiSYiA/cZlP1zTSpAzvB5qPK0mfSgLi5J4Pagc8d+1Nz3pT1zQIepzR7033/On/wANAEs0Plbec5qOnli5G8k03H50kU99CdGGBUcoywx1xzSDIPSk680WBvQQDjOadGm9ueg/Wm1NEeAB1oYJEjsI0469AKrAZapWQkk9xxg0wqVOf1pIbEYAe1JjNObpTlPGKYrDB1p4Bx7UoXc2acMn2xSuFgUbWBodd+WA6daGJ3ZPWlBJJ28DpmkURE47fhUTAk5PerXl/n70yROPencOUakiuNsnDDo/9DTSNpphFKr4GGzj+VMmwNjqKTJ9KcVAPUFfWmlwPujn1NAh23GCxwKDJtBVB160xQXbFSBcUXGkN85gOgz645q7CpVFIBLjnFUWHzYqzEFMe5mzj+HPOKANRNPu3XIRWjcZX94GI/Ks27tHt2yy4jbof7poWF8bg5Cg8etWTczplbj98h4LE7uPrSAzehwaSrEkagbk5j+v3arkYbGfxoGSpGW7VFMwjm8sDBU4P1q1Aw3jPbmqV4Nt7J/vZpLVlyVo3Q9mLsWPU1GTzShsjimkYFMljs8UZpmaUdaLBceFLHAGTV230+QjfJtjTqXkOAKhguPJHyKN394jNSXty0luiM25icnP6Vm+ZuyNo8kVzPVlySIQRxFDuEi5DjuM4qjeLmNW9Dg1pzACys4jw6RYJz6scfpVK4T9w4/GlAdXVmawwc0xualYDbioW61sjmkho+9Th1pg+9Ts4NUQL3I/EUcYpCe4oNAMMZpfvf7w/WgdKOp680MSAHNPAI6U37x9Gp6MA3PBpMtLUXJ75ppxjFWzOjLh1DHGM+lVGxn5c496lO5pJJbMaR3HFGTS44p6OELZXLY4z2pkIjB+lPAHdgKaBk/0qVY8kKBkntQxpXLVpBEzZK78ep2irl9JZrbCIAS3OcmRDhUH90etZgTaeTgd6v2NsJpElkQFf+WcZON5/wDiR3/KsZWvzNnTBtrlSKsltLEqM6MquNykjqKixXXeIRb21raWEUqzzbfOuXAHyuedufb07cVzjW4PK1NOblHmHVgoS5UyltpMYqy0LDtkeoqIrWqZk4kYNPV8HOeaYR2pOlMg0bbUJLcjBOM1JdX8dyOY13eorKzRnNFiuZiTGpklMbRMO3+FVpD2qRuCg9KoyZYkkidWjiUhd27JPP0quhI5BxzTc4570D7o+uaYtyWPhgx6dTUZdiMk9eOKTPyhe55oI9e3GKQ3sCnALfgKTpR35NN70wuO604elNFTRIT9f5e9AhyJxk9v510OnW0MURupg29VJ2n+Fe34mqel6ebuVXwPKDbV3HAJrWuX8jTpYsKWc/OSOc54ANclafM+RHfh6fIvaS+RnSFpvMlZgSO2egpiOQeMg1F79DmpAPl2qw3c/wD1qdrIm93cvfanKsQMIxztHQGklvJ7kxiaV3CfKu45wKqLK0cm08MOoqZvLKhoyTnqT2NTZIu7Zfv7doLlFk6sisSDmt3wXa2N1fzrcRh5lQNCr9Dg88etYup6qdXuUuDDHFtiSLbGMD5RjP49aqxTS20yyQyNHIvRlOCKxnCU6fLezNYzUJ81i/4gt47bXLhYYzHEW3KuMfl7VSCRG3LGQiUEAJt4YeuaR3luJWkkdncnlmOSab82dp7dquEWopNkyacm0iSGSSGQPG7o46MhwR+NOAz0qMVLGjFgDkZ6E96H3HHsDLxkCpxsMQCbiTgnPrR5DsvAFLCAu8Mm4kYHOMH1qG00aqLTE2n0pyIN3Iz7etWdnmRLsjIKAl2z154qS3ijdWBU7zgJzx75rNzsjVQ1G26IWVWU99xJ7dqv2do7XAVVYkoxXA68Hn+dOSOOC0UPCrPICyybiSB0xir1k1y8yzRyyxsqeUHznBxzn0GO1ctSejsdUY2L+jTMj3MW5ZY3icJuPB5/SrtmAjK8JjBZSZN7gBgCRge/esuwik2SLGCwaJtrchSM4NX4QtrcssDpO5BMbEfKDj5hjue1cNRXbsbHQWkM8cE1qQ3lyKEU7gWAJyDn6VzmoacdPM7XlupcfKGLnD5GMg9z7dq6DS5Q9tviUB1Q4DLkJgHgk9QTzXIWvi6RBJp+rWq3NjKxLhBh4mJJLL6nnoaihGTbsYXlGTKoOUKyufLySRHyOR/9bFVFQkDtnuTW5caUsUTXdlP9t0xhnzYzgoeysOxqi0TSMHEYZERSyo39f513RlYrSWqM1l3NwO9EkQWNHDqS+cqDyvPetC4MskcEbeWBGGUIo5UZzye9VhHGtwQwMyKTkLxkVrGdzOUSmWIBGByMGosZqdl3PtUEknAA5Na9h4cnnO+6SWNdhbYAFZsdBk8DNbJmMvMwgMMPXPFWIdOu57hIIrWZppDhECEE+tdbZf2Zpr+S1pcaXeNt2yXQEw69SccfhW7HYiKy+z3EcfmFndbiNixZj3U54HTrSUm2RKVkec3+mXmm372d3A0dyuCUHzZB5BBHUVdsvDWs3hBh0q6cH+Jk2j8zXpdnr8Bt/NmRBdwqQ7Ko5VTg4PoPT3p03jKyji3mRW9y+cH8Kv3erMuep0ictZ/D/VZUAuZba0Q9R/rG/Tj9a2ovB2j2ttNHsN9eqpw05woPbgcAZqpcfESAriCLdITtRRnk0qavFYWwe9dnnbLyKzH5SOxPoKScE9BtVpL3jiPEXiG4Ak0+e1ijLHFysZPDtnd198sPqK4G+WRLlgrNIqfdDddvbj/Cup8YalbaxffbIQkc5BVwuSHHbP4VyU0hYIrZO3GCf6Guin3M5opGUhgQMEHI+tWLyFvMD4IVwHU46g89aidhzvAb36GlS6uYwFjndVHABOQB+NbeaMNNmRAAOp28A889ac85dI0ZflTP1OamN9P0kSB/96If0pPtUZB32UBPqpYf1p3Fy9mVXO45/LParyLC8Su8gSTaB8zYzx9OlQmW0cbfsrIxHDCXIz9MVHLmScg9Ace3AxT3JtY0RDZFBi7ijzwVEhb8TgHAqF7aEoUWaMkDKlHBGfcHBqiVHIGAfYk1LFHD5YEitlgcbeppks0JGDujKoCyKDtA68YP+fWqR/csEf6qfVaI4pYvmgkUnuJMdfTmrfmW99CYzD5UyDJRc5PuPXPcfjRYObW5nvjdn1pjLkg0ssEkIB6oeh6j86h3kYDA+2aLD50OKA4waVVCnNRO+TkUAs3fA707MTkkSvISNo6mhGwVVcE5/M+tR8DCqOT1NSIQp96pKxnKVwQbLhVzgcrn68U9gVJBBDA9B2IqKQc+1WISJgPnCzKMcnG8f40noVFX0AFihIVQW9+fyp6NsQuv90gfU8f40oglUkbJcnocVN9naPb5igHO4rkZ/wDrVm5I2jBkEOQ2CgPsaQrlgByK1YbW1JhM0LgMcMTIAPrwKunTIfs8skFo4YJuVvMLBfXPHp/MVi6yTN1h5NGSkALYJwVA4/rTkRmlIyS3qasxWcjoJGKiEn5mz3Pt1NSJalmBwdo6ZHJ/wqHUXc2jSdtjbh8SSizW0mto5bfYF2MTngYzn1rGdE81jEpCE/KCckClkwAEH3j+lPWNiAByaxTS1Rvyt6EDBu3SoZFwOavGB9pPltgd8cVl3MpfKqflHXnrWkHfYiouVakEKlpHI6BTVy2smmBKjIU9KvWOjv8AZQWfY0g3lT1C9vz61vW1krRJHCoRQu4gnjP19aVSslsKnQb3MKLR5mPyrlScjJAzVqGKSElFBVjwUZePzrel094IAyKSgO1mHr6VLCyIsZUs52885+b0+lcsqzaOuFNRMH7NKZMRxHdnG3qD+NbOl6LC0kUl1Hw5IEZbAz0578elXomYkEpkk7SEPAHetSziW4FvHG3zHgJyPU+lctWs0rG3IlqyzBp0V9fG1jUZQhAy9AB2rV8YFYLe1t4FUpECoB+6MqRyT36mtWK0ttD0+S4nYB34DEZIz2HrzzXKeK5vLigikJZ5ysjIh7nPJ/DFcUG5TSOVVPa1E1sji7kYO1XBG3JCn5R/9eoo7WWfIijaQqC7BRnAHUn2rTsdOF9frartiUqS8jHKr3zQF+xLPH5siM8e0qOC2emfbvXrKpZWW5bjdmP5TmNmVchep9z0q3ZeGZ7uN5ykrxjjcowM+nNLcyxR3CWqH5Ix8xHdj1Nd7fX+n6X4dgtYpFLtH8gB5B7k10xucdR2dkedy2Mdp/qJXSQdietZ1zLJK2ZclugNWr69EjHGMg8EVnCf96Nxxk4J/rWiir3I53a1yMoWHHUUzcUUgcdjVlyWcgAe5qvKuPcitEZMiPQcdTTQNz46dyfSl71FfN9nswvSSb9F/wD1fzFX5Gb2uZF1IHd3HRjx9BUmmW6kPNIoYH5QGGR7mqj5mlVU7nArcjiEcaxr0UYraTsrHPBc0rjFt4UfekShvX0p/f61I6AEbSSPekX72fSsrm9iOSENglPmHRhwRUwuJJMrdH7RGRhw5w5Hb5vUVbg1BLeIr9likfOQ7dRVGVzLIzsACxzgDipXvPVGjaitGQxQ27iIbTBKoOWd/lc9vpT10yczI7xMkdx8pYjgE9/pS44qxBezwbcPuVCCqvyFI9PSlJSXwjhOD+JHPahC0F1sPYDnsahU102uqmt232qKMJeQjMiAAeYvdh7+wrlA5U/0relJyjruc1aKhPTZlkU4VNaw+bgyRuq/3s4q6tvaKf8AVu3+82KHKw4xT6mWRz0qQW8hGdh/GtMiMDEcKp7jk/nTNoznGT70uZjaiiklvJJgMcKO5qytpBjBdj9BVhUBXJzmmgc0r3GtBi29uv8AyzLf7xqZQF+6oUegHFIBmnDgkd6ljTLEZzjmvUZtektNJ0zWYozNmIC4jHAdcbXBPrkZry2EEEDFdvoNx9q8LX1jjc8BLquf4W6/kR+teZj6aaUmtj0sLroyp4k0yGS2hvLSRZLO5k/dPGN3vg+jDpj2FcHqVs8DDcE3AcjnI7Vu2WpPp88tvKrS2cjfPCG2kMM4YHsQayNUmluJ98pEjOWPm54f/wCvW+GjKDtfQMS4yi77mN5bHK5x6Y71Ay7TirbkK4KnODnNV5SNx969KLZ484ojPNXdN0/7WxlmZktYz87Dqx/uj39+1R2Vm17PsB2xqN0j4+6v+PYVNqV6H22dquyCMbdo/wA8+5qzF6ai3+pmcC1tAI7dRtATuP8AD+dMtLUAhmUsSQAB3PpSWUCCQBztyMluuB9O9XUkie08srIrK28Sl8bccZFPYnc1LdlV0tkYNGGBaQNwOuc45GPSi68VfYTKmnMZbh33SXB4Ut647kdug+tYNzeyXI+zW4ZYc8gdXPqantbFIyok+eY9FU52+5FFguC2mo6zciS4kkkYnl5OFX/CtW00S1gufJuJd7Ackcrjs3HOD/KhLqMK6GeaRM7mgt1yFx0ORwPzqeG9cRBotMAECbjJcSDhSeoVV9+xpMaSNw3EdrtMFigs9hRmdQCT/ezyVH+z1NZtzexRFljtjLyXiaNtojHIPBz+tV7i7vRCtzLaWTxCTCN+8O89cg547Ukt2EYpeQrbLKoImhcyR885cdRn1z+FKwyn5omWRVjeB9qsBuyHGcc4AqKWWa4uUicqJGABHp7DFOKmK9aI4/1WFIbPRuvvUSzKL95Y2IdUO09CW6Z+vNMRHcvFZzmGLdNdZ2sw6Ke6j396qtICxDwneRxhs4/Oo0h8yz82P/WKxL4POP8A61Sh1YI5XLEZIU859/r1pkld40djhfbGelQFGiYNGSPcVbZQQ25AHB554qPO4kBeM4+gpiI1uFY4lXa395e/1qV27EDJ6MBndULqGUsfXAI6GmKzQjI+aMnpQA903DDDBA7VGrGI7W5X+VS/KwDJ93Pr0+tMK7gTxgnGBQBYguPLIDHKHofStGGd4XWWJirDoRWEreW2OqmrlvPsIRj8p6H0qJwTNoVGmdxo3iOe2I8pg0f/AC0t35U/T/EV0kkFtrkDXelkLcL80ttj5vqPUfSvMAxVgykhh3B6Vr6fqzxTKzTNDIv3ZV4xXl18JrzQPXw+Mv7szeZFmjeG4jUpnDIwxg+orBv9Je3UyW4LRLzg9R/jXXi/tdZRbbUwtteHHl3aDCue270Pv0NZeoWl9pF0ILkYH3kf+Fx6isqNSUHY6K1KNRHHkBcs3B96ijYJKD2rev7OO7k8xQYpSMbRyCfX6VhzW0sEvlyIVbt6GvSp1FNHk1aUoPyI5W3ufrViazVIPMBPA5zUIjKuC3PqKc7SSDliQOgq3fSxnG1ndEKjmtu80y3FmJYphuwCcngn2rDHJGOtWCCqdQffNTOLbTTsXSnGMWpK5GEXacAE+tQPjd09qcx5ODxSbMg+1aowfkTBUVBkA5Heo3Rcbl/KnAhUI25NRBsdelAmNFX7RCY94OCHHGOTVIqBjHSr9sGFl5nZW/8Arf4VM3oXTV2Psf32qsrH7yN+eKzTvjcwsPmRiKuWLGG5+0OTiNxuwecHrWvNaaczi9mnUjaWXy36kHoffpWbnyvU1UHKOhlSbY1DYJlPCJ79zUMMLhGDBVJPzH+Ij2pbibzJmlA2ZGFXGMCqzyEmtYrQxqPUWV1ztTgDpVZ8bs048U0+narMhY+/50SDIB9KYCVNSfyoGMJyPr1pHB2ij7pINIDg89KYhvNJSng0lAhRxTwxwVzmmfzp8X3/AMKGNDQcDik781M8eeRUZBHUUANyPSjPtS8UmMnAoAMcEUD0p5GCKj6UCFBxj8qeOOKZ3+tKDx9KALYZDit3w9daOfMsNWtk8mc/LcgfPGfr6Vz2PzpwOOlZVIc8bG1OfJK5ueIPDM+iSq+8TWcn+qnXkEeh96xhEmeXB+lbOn+Jriz06bTriFLyzkUgRyn7h9Qaw+D2qaXtErT+/uVV9m3eBL5cfHGfxpuNrcdKZgZoPbnNamRJyWyec0uOKiDGl3HHFILkhjVvY0zYFJHWk6980D0pgPXrg0MrA9BTSdq570igsetAyQLuOT+VTKnFJGqjA3ketTT2sqLuXB+hqWUkREgDrUDkZppY5560hoAY3Ximbeal257ipUgzywOPSncVip0FJT5P9a31pneqIHp0pS2OlR5pTz+FFh3FHX61PA0e8h1z6e1QAU4DB/woEWVcuThRjqBV97x5bWK3eBEMfAdRyR71mLKVACgCnoeQSaQXHyLsbcuADngHt6VAir5g3LuUHBB61K8gHbFQvy2RxmgCVFRjhflx1zUFykcxZ4iPkwPdverK2skx3LwT3bpTNqM5V02yDqBxmkX5MzlbFO3ZFK64Yhhz6imbR2b86sjVDqUUzaf7wox6v+VAXJfMCD39KkhXdIHk5P8ACtQAheg59TUiNnPPJ71LRSepu7lezzjBBXqeScHNVwNzqD0JxTkmWV44x91eWPqx4/QVDeFrZXVwVcErx61jBdDoqa6mfOAkjL3Bxiq5Pr1p7A9cYB6e9N210I5ZO7GjrRmlxRimQJS+3pRijB/GgA6YpdrBd207c9ccUhyR/SnNNI0axlm2joM8UDSQcMPQik3dmpuaM0rBceSfrRuBGKZyOlLuz1FFh3HdqSk47H86dgkAAigByjpUisF6k57ColX1NTxtGh+6XPoOBUsuJZtLYzPvcZA5AzwPrXbrpTWfhJtQkcJJcusVqNnzP69fugYrI8GSGbUrsyRqdlnL5aheFJGMj35rU8Z6sbjU4dPhbFvpsYgTB/i/iP8AT8K8+tKc6qprpqenS5adLn7nPXFlPAm+RMLnrmq1TSTyyqBJIWA6A1GBkgHiuqN7anHPlb90aM5FNeJJO21vUdKnkAGMDBpqISeB05piTa0M+aFo2+Yfj2NQla1iBuIYZUnkVGba2YlY3II7NRzWHyKXUzQtIQAKsv8AZoyQZwSOyjNVJpEY/ICB71adyJJJEX3nA96kI+bNJGmAWPepUaJWzIC2OgXvVtmVr7kO0ninbd3A4A70M+WJwAD2FIzc4HQUC0HEAJuU+xphPtilVscHoetKyMud3amLcZ/KiinonOTyfSgBUTOCRn0FX7Kye7m8tAT/AHiP5VDBC0kgRBlj+g9TXUWVvHYxLgkOw5z1+v1rCrU5VZbnTh6PM+aWxo6bBDbeUWjDRbdqqQOh4Y/X0rF1MIkxgRwUVjj6ds1rXNyssm4ptAO3C8fSsK6Ym5MmNxHJBH8656as7nXVldWK2PpkdMUKp6gdOaeMNyOAT09KmEZbBbjPOexrVuxio3ZG6CeMED5h0Pf8aeiSJvDrg7RgjpTDGwJ2jBA5waseYBAVwODngccCpbLjHW7Fh4gjHtn9acRkCiDDqyZ+ZADj271PGgA3kfSlewWuOjj3FY8gE8fMcCmSR+VKyblYrxlTkU4BpSFRCzMcADnJ9Km1DTbrSb57K8jEdxHjcgYHGRnHFTfWxVtBlskL3MKXMpigZwJJAuSq9yB3rR1vVY9T1MPbxeVaQIsNvH3CL0J9z1rJOcj2oHBpOCb5mNStoaiNuXINQlvmzgU60uljheJ49ytzUeec1ko2bOlyukWrZ0DAuNynIIzjrVy1izNsZQRyMj1/rWYrdwMdq6XQwhmhuZ1/cgmBm34w23j9KwrPlVzek7kE00jJGr7VDKPmC8kds/lXR2Hh3bpUVxcs0SuDJ8vJKjkZHYVgzpFbPLE8XKuCGHOOuAP0zWiZ7s6WbQiUeU3mSEtwYyAB+ZriqXaXLodDT6EM1x9ojgSOX5QjABhwOeg9c/1q1eGVBbFWO2VSwz/ETjJAHTNUrJ2VjuiVlQ4Az/e65P0rTijjleONU2RRSARu7846kH09qiWhaLVqpSN5NzkA+V8zcKQDyPXvxUuqeFU1KwW5iIiu5BkORhZM/wB70qxaxrLewsIhh33rGvqM8nPX+tb93IkNmeGYQDcxHZiOAK43VcZXRzVqjUkkePw3+oeHNQYLm2m6PG4ykg/2l7g1rx3em6zIPsq/Yr7HzWjv8jn1jb8Ohq34mSO/tmhlVPMiA2SD7wYnnJ9PavOpA0U7whhJtYqGU8cdxXr0bVY3ejCacXc9UXQbHTZopNavFEEg+XaMITjP3q0J/EmnaPpQu9PtYVjc+Wjom0se+c8n2rzGTxZfXmgnS7iQyKoKxyN94DsP6ZqpFM8umwiSZyRuwC2QOfSujl5Voc6i6j95no0Hi/Qr5jdyrFa3x+RLiFBvQY+9joaYPEDWjreRshsi2wXtum4TtnOJAfun/GvKFmMDMhG5T9013vhi8ksvDc80ltbz293ITJAM7xGoxkDpzVSXLqQoJ6I6XVvFOljRUkuViaS4cpNbxyA4YADIyOAQc56+lca/imSy0+S1jdpOhjZW/iU/NnH+yQOPSua8QyRRX5itJGeybEkBcfMF5G0+45H4VieYwPDEcnGDWypqSuYOXI7HZR+LpIbwMyKIywaVQxIdWG1xg+xrMklkBliWY7EYqDnqAcCufLl5Rz3NaIdsYzz3onBLY0pTu2bGkajHpl39rkXzpUB8sZ4U+v19Kq3eoT3TszM2CSeTkmq7xukcbF1O8Z2g5I570ig8ZXNZ2W5vrsRsGbqaiaPt/StGG3M2fLikOOuBVn+x7plybcqPV2Ape1SH7G6Odkgz9xenamG1J6dRXUx6EGUedcog7iNSx/PpVyLR7KFCwR5SP4mcD9BVfWLGf1ZN6nFpbvuHyFqlk0+SNQ5U4IzxXaiJARtjRQRjgdaS4aMWxWQAIWX58fcPqKTry3sCw8L2OAFszypGincxAA9c1JcxrFKY38zeAN3sa67w7psVz4hDT4lt4wRvzjjBJ/JQ36Vmavp7m2XVHiIF5I8uR0Ubjgf1rRYhc/KzKWGtFtHOEqrfLu/4F2ojcbd2cMgwB65p/lYBOOB3qIAgkHoQCPwrqTucTTRo6bHbCQXF4vnKvIiBwD/vH0+lXNUudPvYRJaWSWdzE2Y2hJCgenJP51iiUgkkYB9KR5uhOAAc8VRkyZrxwRPEF2y8yxnkFh1+metQSvbyIGjBjY/eQdAfYU1CVgweNzbutRMM5Pp3qrCuGUXsT6dqPmbggL7CpJChhACgdCD6nvTQMDHrQhPQTbtwPXvS5PGKUgcY596FU49KdwSAj0oC8fWnbelTJGG+6D8oLMT6Cs5M1jG5e0+B2tzJvfaCRgNwPrUtnp08wEkakK38R6fnUNmr3MiWkeQh5kI9O9dRGioiooAVRgD0Fck5NNnfTSaQ+xspnYK9pbSYTYREdjN7n3qe/tLuZltYY1S3KZCWzlg3+8TyTSwSmKRWXGR0/wAa0VuUiCTKuZFY7wvBHoQff9MVw1OZSujvg01Ypad4P1S6kaOCywyDcd7hcA9+e1a8vgG6jVI5b6FbhhuMKKScex7n2rU0u6mYrc2z5kRssW5IJ9T/AHT39DXdNbwatp/lTbdzKG3xnJRvVTXBVxNSMjOrUdNrseLyaAumz5nUyqrYBxhSfQjqPpRKxZdsSpBnvEmCPpmvRL3TVWbyLyOOddu0u52yH3z0P41gXGgogkNsPtCLkMN3zrgdQOprWniVL4tzaMk1ocDe6Rf3Df8AH6J06jzG24/DpU+naFDbfv7k+fIuCsaj5AexJ7/SuqttMlDt5EImyMBiMKp9T9KSQkriaEG5VyrnaBlcenTPvXS8S2uVE+xje7MpkbcXDs+CSzfWpo8hQkZOGHIxgZq28KK3lpHuTgltuW+mentSyIXm8iRZBtJHTnHrxUc9zRRIicxYy5H3WwcAnt9aelpIysiDLIeVB5Yn+eKu29q0kO1PldM7VJyx9/bHrWpb28kUiw2UKyXzD5pE+7ED157msJ1bbF6Izra3NovkODIX5KI3Q+n8hXdaRp0OjWr3l95Ubnqf7oPbPc5ptnptnoVv9onYSS9VyMc+g/HNZt9qc988asgiaT/Uwnkr6OQO/pXHOo5s5Kk3W92Hw9WJdXL67q8EMgaGMHKR/wB1eu5vcisDVWbVNTlmiidY2JES467RgYrblI0jSpPtJjjvrtSCMn5Fx/M1jQWh0yA6jesYCvzQA/eP4fTpWlPTVGtNRW22yE+zJp9mylF8+fiTLZYL12j+prDubpGvnmSJFZn+6r7lXt+NRXF+t29w8u8k5MeW6HPf14rPmmYyBgoUKBwPau+lSad5BOatoU55QbhmHc+tWNRjvreGGadG8m4TdFJnIYfX1HpVO7Typ2UEMOGUj0NNluZ5bcQGZzAjFliLfKCe4Hau5X0sccutysXLN7CoHcs2R+FSE7iVXnAycVGp2SBiMgGt0c7LKSZG4nJ9KFcDJx1GBVq3e3uLNY5YwrKuA6jBz6+9aUXh68XS47uKHf5qBxIGGUB7Ef1pXA5+KPzZgp6DJb2ArH1S58+4kYdAdq/1/wAPwrfulawsZpJVxK44H4kD8yCfwrkpj82B2FbUld3MK75Ypdy3pkO6RpiOF4X61rAcY71Fawm3t0jI5xlvqamUc5ok7sIRsrAfmjORzmkABAAGGHenOdzZx+Ap3lCMAseTyAKksgfqcUzrUhG4nHX0qPvVIhhikp1HGaBD4euc4IOQfQ1DJGvmlzGgYnk7RyanjieSRY41LOxwqqMkn0rd17w7FoNhbLdXJbVJgHa3UArEnufWs3UjGSXVmii3E5o0dqUjHSlwK1MxAOM0bTgkCrcVjJLHuQgnsvc1GY2jDK4wwOCDUqSbsi3BpXaGjKgH1FRGn7jsxSKuTimSIDg04kEikbrx2o7UholD4biuh8J6kthrkJlYCCf9xLnsrd/wODXNqDirCdAfWsa0FOLi+p0UZtMua7p82n3c29MuszYYfdbB5wfyrmWnKO6lQ0TH5l7fhXpkxi1zwPLiM+fauH4+gDfnwa8zaFpBKwUlUIyfTJ4rLCT5k1LdaG2LT0cepWPlMehX5cA+pqMxh2VI9zO3AHqfapHA28Djng1bsALWGS9OAwykIPZu7fgP1NegjzJCXzrptmLGFsysczMD1b/AdPzNZ9vD8wzjJ9e1Ny1xcGQgkdhVqI4VlCrnr8x5AHNapWOZu7HKrbxsfa3PzKeg96rzz+cywxZ8oHr/AHj60XMm0GFOp5cj+VOt0VOT1I4piLUSQ2w3CY8nIZUy2P6GrESQzELBMgccBXJUt9M9T+NVoyjyIjcIeCegx6VJHaefiNgWfy8ohOBxyc0gLiXJs2C+QwVMgo42sQevTipxKIJWkRt1pt8v72Su71HtWbb3yGJbe5O+A8IxOWhPqPb2prDZP5Lk5DbWbPBAoHc1rnUZpYYYpnAjtiVTYMAj0Pqe+feq4K3DOzBfs6DMvJCgdB9ScVWE8SEhSyhs7gvOeOnP86jkuIpSFLDaAThRkBscc9/rSsO4+STN2rDcmUbqfxH6VHcEiOK4XIOMOR3z3qIz52kEjy+QCOvrSgsDjJZSucZ6jtTJEW4MEnmqAQfv4HX3/wDrVG58mUqjERnkY64NMETvkRg7exJxx70TMrEqhJCqFz9B/jTAcxGQoGB0NNc4jGc8nrmkYlkDEjBHI96TDMgDAYxkH0HqaBAGUxFVJyxzgDuO9NkCozFiOeir60GTP7qLPzHlsdfembA0zDOAvcdqAGBjG+4D6g1ISGUMvQ03BK54+vrTFYxtz070wHsPl6dutNRsfIfwpTgNg5x2prYzx+BpAaFrNvARjyOnuKsk1lI5BV14YVpKyuiuves5KxvB3Rp2OpPakI6edbnqh7fQ9q6vTNXhuYRbXB+12i8rv4ePjoPf0rhgSYwOgH60QzyQyCSJyrDoRXHWw8ankzuo4qVPR6o6nVbA23+kWh8+yflJAfmX2b0NZ8l4lxbrFMFcKcbu/wD9ap7DWZVjckYYgCReoce4ovdMgvYmu9KOCD88BPK/SsY3g7T+86pvnXNAxZYwp4OVx071SBYZFWC5B2uCMcc9RQYxIrFSNy8n/arui+55sld6FYDPI7UMxbr2pTjOCMAU3jPSrMgVQ3FIVK/SlyVOV4p2CFyep7CmIZvyADTDyaXv6UYpiEq/byRjTpQS3mBvwwcc/pVQREjPepLaGWd/Kjzycn296iSui4NpliyzKs+0DeScDGcjHSopCIfOg2ZYsrI3p6j9a19N00DURHlwqAOzAc/UVkX0gTU3YLu2Schu+DWKknNpHQ4uNNSZHcxSRnEoIkGOD2HaqhYGuv1hLG/0aG/swoJBEi5+ZG7r9B2rkmjI+bB29M4q6NTnWuhniKXI9NUMxSHHanYpMflW9zmsMIyPenJyMdxTeQKTocjgigEK6557imdamPIDDv29KjYbTx0NCBob1HTmkpx55pD60xDalhXMn4VHT4+pxQwRZIA64zTflpnNJikMcNndVpdwXkAD6VHSUAOd9y8+tRNwxFPPSmtgOcjPFNCG0Z5o7UlAi0PalAPXFJjigGpKFIx1GPrSVbub0XECIYgGX+KqlKLbWpUkk9HcMcUtKjbDkAH2NHWmIT0pcV02keCtR1rQ5dSs3hbY5VYd3zPjr9Pp3rn5oJIJWilRkkQ4ZWGCD9KzjWhJuMXqjSVKUUm1oyHjFKOtGOadtypI4IqyEQyN09qaGLd6JPvU0c1SJZNGBuAycdyDUvmSx8BiV9Khj2Z+bFSOEVQykn9RSGhZGEi7u46+1Rhaa3DfXvUlIdyaNh02KPcUM5U4IHFMTqRQTuOT0pDK0xzKxxjmo81JJneab+FWiHuNHrTgOaUDnmjFABTu1N7c0ucUAOGCRTyvpUefQU7kjk8Uh6AWxwetCnJ5pOB2oPrQIsrcPk4OARjHtSP+969R0PpUA4NODUDIp4yOTyfWqxFXGJLfWq7pg4Ix6H1poTQwcnpSUu0+tJt96YhTilUnoOvrSAKPelz2xgUDL9o+AqgDluvrUviLEesSKGDAKh+U8AlQT+tVLdyGXChj0AqXVkiMscyNzKvK+mOM/jg1il+8udDd6VjPaQsc4pm41KYXCbtvHrTO3brWysczv1G7jRuNO7Z4pPypkibjRvPtRx6CjAx0oGG/2FO3gjpzTQBnpS7RQA4HHAprEZOBR04zRtHqfegBMHrS7SR0o6e9KCRQAADuaN+OAKkWRNpVkU579xTxBG4yj8/3TwaV+5SXYgGWIrsvB/h2HVrmNrhd8SnLqDg4/wA81yy27qc7Tt9eleqaDYSaDolzLcKQGtPtCMMHDkEYz9CDiuHG1XGnaL1Z6GBpJzvJHKeHJ30qS91FVBRFMS5I+8WyBjv0rOZmkkLuSzMdzE9yaavyoF/E/Wl/ma0jC0nLqyKlS6UVsgAJOMZzUqw7Rl+vXHpQgKDd0akYsz88e1UZpJA/z4IHengiJMj71NaNgoODTAPWjcNhOpJ9arRn95K2eM1ZwTzVNGRYnZ27n5R1NWjORniNpDxyetAUL7tSls9BgU3HNaGTfYCSe5oC/gPel3AdBz600nJ5piA0UmKWmIKczlwueoGM+tIoyec49qlGBwoBGevqKllJDVQjnHX9Knggd5FijXdI3b+ppIYWlkCRrucngeldHb2sWlwD5keeQfNnsPU/0FZVKnLotzejR59XsS2dra6dbETfPM4yAf4vf6D0qa3WG8voopJ9m87WlbnHHaqi3XmSfvlV1Y4OR1rW0WK0htL+9nG4IPKhB/vHvXK01dvc7bp2S2RS80iR4i6NF938R0Iqo0jRPLhgpcbGJ5yprRGkzS6c16LZnRnYB0BzkVlzxsoCyY3fwuOje1UrMhtogAXBYkArxgd6mjYSLhQBInVf7w9RVfkkqRSY6HOD1Bq2iUyb/WXOemRxQ7DawHTdiovNd2AP+sP8Q71JGCZQMAkEnGetKwcxbWKWx1WOO4QowdSVPdSB+mDWjf2Elr8y/NbsxCuP5H0NV9Qu1nhtFyrSRZG/qcZGAT7Vux36XAPn7GScncuO1RJvRlxS2MfTb59OvYbuJEeWFtyBxkA44P4HmoZJpLi5eedzJK7FndjyxNS3VnJbKsm0+TJ90+nsfeqyj5aVlfmHd7HTafoNtq3h2ae1ZjqMLkuhPBXsAPpXNlMZB4I7GtDRdWl0fUEuY8sv3ZE/vLVfUbtbzULi5jjEayOWCelZwU4zaexpJxcU1uQocGp+RgMCCeRkYqpvCEAkAnnmuj8PXkF1KNI1Yh7W5+WKV+WgkP3SD6E8EVcu4osgsNIvL+1uLqGFmgtxmRh/IeprQ0NlSZo3KCGZSjM5xtz3HuK0dI1e58L3kuk36brZJDyByuT19xU+t2FtZyJq+niOSxm5dAMqpIxkCvOq1JOTjJaPY7aSSKWpy3BcxTYbYSrrjALDuPbBzUtteW9vLEspFwhX525PykfdPuPWr13FHqYWaJVHmxKFycDpjAP97I6elZmmLFFqMIIk3plZMDAycjHPSsE0427HQWrgXGmW01kksRjnKhyhB46hvbNOhhceRcFRs2kHnO44Oc+9PuLVmMlksfyxtmB3ADOOm0+vfH0ptmiRF0DSBUZXGehA4JIrOT90uJ2GmShmeSMbikZC5XG3A6Vdu2jisZgAc7lPqCSKLC3xdlnUBZQHzjr8vSk1B1ks5Fj2Bg4ZUxycdvrXmt+8edJqVRW8jhNReJmkjZEdsYY5PUHqPwrBvbO0uYDCLZYjkkOh5yfX2roL0RrcxyGINnDMCc5Oehx0rKuYXilZdpD9Sv8Ad5r1qLslY9Bow7LR7RFeS6cmaNwqwIp5/wBrPpWfqUiRuYoY9rMSVUfwiuhubdmGASHHccH8DWdJpKq0yZPmkfebsfQ11wn715MznFctoow4bea6nS0gi3yn5VAPc16LevZabodoy3CRrDGF8hT80jAchsdOc81ydtol2kDtBGJnXLO0JyQPWrVvY/vRLd4kbG7YrZ5z/Ea0nNSMYwaOe1R0vLkyxRlYhkhfc8kD2rNMIVvmJ69q9DKQIxmVhgKFzHGAec9c+lPS3sXJ8yECEZG+JRudjyMg01ieVWsZyw6k73POoowkoZwSo/umtm2ht5kOyQbh2Y4Nb0dhaFJImtI3LjGSvII9PT3rV0nwzp0N2l1ISGgPmywvh0Rfc+vtU1cTG12OlR5DmItJnYfJbyyH/ZUke1WIdGdmDXHyDrsXkn/DmvSbm8itfDNzJCvlC6f/AEdUJ7dSfw7VzlnZtbsLgKJF3bbfKkeYx7/QH+VckcTKSuzdJPoQJYLpgVpRgxBt8ecjPYcVmMTnd1JNb3iCAae0Vn5qszDzpVX++fX9awipCg9AegrWjquZ9TOcr7Cklm3YGPQdqlKCIpv5RxuG08gVBjFL2raxFxy4LYPrVXVM/wBl3JXgqm4fgRVyWFoWUMVJZQ3ynOM/1pjRC4RoXBKyAocdeRSvbUfkUrK+8jTZrhFWNp0NtAOwLD94R9F4+pFavjWa3l023trCZJLJIg0QUdMYUH15GfyrnJ4jJftbBCht1CQRMei9SfcnrTJ9QVbeW0kTdwDAx7c8/nSdO81JepV1Z8xiYTYyEY57/wA6pyJ3HK9qtTKQ7ccZ4NRqR8oYcd+a9GLtqebUV9CqTn/69JsGcnn9BU8ka7vl4+vSmmJlONpOO4rVSOdwZEeeaaVLZ4q5BbKwJlOwAdTzzUVxNCo2QZJ7tjGaFO7shezsrsqgfNUmD1x+NRxSeW+du4dwa1oBY3SBVYxSdwxzmnOTj0CnTU+pnBPyqQDoOa0H0/y1bkHHfOKpqvPA68cVn7RS2NPZOO5Ht7YOamd1itjCvMkhy59AOg/r+VDER/KuDJ6+lOtLRrqUqOgGWJPahvqylHojb0O18q085l+eXof9mt02sqWy3G392xwCD0qsihFCKMKBgD0AqUSsIzHvbYecZ4rjm23c7YJRVhytswVJB5z9KlhmaMsVxhhtORnioIyokG8ZXPIpxbDnYMKOxqGrlp2NixuprN4pbSUebtJZc8EdwQe9dboerW052WjGN2+YxF/usOML2Oa4SDO3djPGQKntZpGkKW4wzcsq9wOevauKtQU0baSVmeqyNHdwNBcRIwXBxz8p781mT232ZvtElwHgzw+wFfYkryDXO6bq0shSPcXO07d74ZD16/xd/wA8VtW2pb3aSJxEqqd7xjgjP8UZ/wA815sqUoOzJVJw+HYnhMMjMw8tyy/623lAcj6HrVw6bYakjRXkJEigBZChRj+XFZxtdN1HDyxRRv8A89YH2Mf+AGpYdFvrJv8ARNURRkYMxOenT0pXts9SJ272YTeC180tBMkiZztlBGPpiki8KXCOQWhAPOUYgk1cZdXyqJIjRqM+ZFMCzcdDntSiTVs4Zo/MxyryLjHrxyPSk5ztuSqlW3xIcnhu0t4WE8u1WJLYOM+xPpTv7Rt7eMQ6VDEFIIEpPyce3UmoNl1IzLLBZgE5O6bPOO3+fWpF+zQANcOmQMCOKMKAB19yKm76iab+N3IYLaW6uJHmujdTlfkYJ8qfXtVlLOz0oS3V5NGkkv3pZDtA9hWBqnjhLSPy7GGNABjYxwxP07CuGv8AVrrUpA91MXIJ2r/Cn0HaumlhalTV6Iq03o3ZHc33iSya7KaZbC/umG1XdfkQD+6O9cZrl1c3F5m6JM4Hz59fTHatHwiytrDNnJWM4NVfGJUa25C8sgJNdVGnGFbkSNrKMdDAMpVsimMxaMHgAcVGxxUMkh2kdq9NROdyLUvl3elxmNQLm2Zg/bfGec/UGsmbLPtXJyOlTRuQWPRcc0sxKuBwM8ZqorldiJPmVytsEYAJ5PX2okiZFViOGzgg06RCrYNN25OAPc4rW5k0ORisZA7iu/sdbRLaCJJB8kYUh/QLzivPCcdOTV+OYx2kkrnaZP3an0H8R/p+NKSEjP8AEd8bm4JA2hmMmPQdFH5fzqhoVh9v1VQ+PKi/eSE+3QfnVa9nNxO8nQMc49B2H5VsaLm1swwGGmO5j7dB/X866Pgp2OX+JUudDNp0LAEiP5um04J/Cs+5057fJBJHoRWlaXcLQ72kJkY4LEZIA6Ypup6tFbwrBa4e4ZcvIednsPesFc6WkYzbMYTqeue1RScY5yT3pcXDgyushB6sVpj8lcenarRmxnI5HWnkBgN3DetMbpU4UEDH05qiUQbDnB/OkxzT2BDY6YppBJAHU9KBHX6JPYeG9HXWXMdzq1wGFpDnIhHTe3vXLXl1Ne3MtzcSmSaRtzs3UmoTlMjoackLyglRwOprKFJRk5t3bNJTuuVEQoA7YpQKecbuK2M0jY0GW3t/tFzO4BjXKKT1NZk7tcTySYJLNuqIdKcGIHXislC0nLubOo3BR7EZXBwaFzkYrds/DF1cadJqN1JHY2aqSstxwZD2CjqaxEHzZPAqozjK6XQhwa3IyCDR1FPkADHHSkUZIFUSa+nWaLb/AGq4C+U2QpY1UuZo2nJhGE7VVYuBty23sO1IM9ayUPe5mzodVcqjFGppd41tdqhmMcUpCuP4T9f1qraWwEWtQGLfiMFWB4Uhsg/zquG+XnrW3oN/HHqKQXQUW9wnky4HJHO0n8cVlUi43lH+rG1KopWjI4x4mL+Woy5ICgdyaTVJVTbaxn5YxsyO+PvH8TWvNF9kv7mbj/Rwx/4GSVH+P4VzbHzLgnsOK7qL5tTzsSuR8o9BsTAOD39qeziNTIQu7sB+lMAyc1FMxeUKOi/zrc4ghQs2TyScnNWAr52ZXJ+b3puwiAME+QHLMDQCo69f7wNAD0bcu3OTnKn+dTRuy53TEGM7kDH+R/pVQuocAA4x39adndyeOevXFAFieNdomQYjk6j+6f8ACkaUtBHJj5o225z+Ipqz4O1owY3GME4z71EXCsMZ5bPqQKBll50UnCbpH+8x/kPakhiubshYo2Yk8CNMmpoYra2PmXYLtn5YRyfpjuf0FX08RXSFIxmytf4haqN59i3b8KAKs+k6jEqpPG8e4hQHwDn6VWktrmJsFxu7c4p19c291dGWGEfNk4LswH58nFV5Gtnk3JEYE4AKMTz3pARStOuQ49iQBz+VIHUKyryCMDipFWbAKNv3dFPDGomAYkxjay9VNMQ6MeYdpwqr95j2FNdjKfLiU7B/48fU0hcbAnVR8zY7mgSHGEQAe5zQA8L5Sbyfmxjjp71CCSjH+9zSkFjlyTSBgvHOD+lADcA9aQ81KpSNg3U/y96izk570wFU5Xaeo6UvU+maZnawNPx82PXpSAF4fB6Grlm/JjPT7wqnIjJ161LG5UrIO3P+NJ6oqLszVAL8Dp60/CR9OT60wyZUBTx7Uw1idNyxFePA4eMLuHcjNa1jdpMxnhVIrpBl492FlXvj3rAoVirBlOCO9ROmpI0p1pQZ1Oq2FtqMC3cDJHIRyc5BPoT61zUvn225WXaAdpOOhpqTyRf6uRl9geKnnuTPEI5txwchh/Ud6inCUNN0XUqRqa7MpgPKQACxA4AHapXtJo4RMVBToSDnFR+XLFiRDkDoy9qke6aYEMVQEDcq8BiO9b37HNbuQAZIpzN3qY2sirvUo4PTaah8t3ICoxPbjrTJIjzRjpmrkVg+Vab5FbIBz396lENvEPmId8Hk+vsKLhysjtLOa6OI1wvdj0rQYJYlAhGBke5PvUQ1RhEsUQAVRgEdapT3Pnlt3U8g+9S02WmkXhrLwXouIgA20ofcGsaWRppnkc5ZiST60hbNJmhQSd0N1HJWZPGs8UDSIWUYycdPxqN7uSTAk+bHpxVhLrFrLDIu7coCn056VUbaT6Uoq71Q5OyVmBZGGQMH6VG2DwOlOYhgMDGKbtx1HFaIxbEI5HFNpSoppHeqJHKwUkH7p604jGR2qM/rT4nA+VunakxrsRkbTg0VK69j07VEQVODTuJqw0inLwaWkHB56UxEgyVzR2pQeKbSAKAMminDjB7UAIRxjvUb/ePtxUzdcVATk59TQgYmOlJTu9NpiLdIRzSikbrUlBRQBmjvQAtKO1IKUUDNjQfEV/4fvPPs5Plb/WRN9yQe4/rXcX8WkeP7E3VkVtdZjXLRN1f2P94e9eYA4ORU0U0kEqywyNHIvKshwR+NclbDKUueDtLv/mdVLEcq5ZK6C4gktriSGZCkkbFWU9iKaDjpSO7SOzuxZmOSWOSaBXSr21MHa+hBMuGBqIVZkG6M/nVeqRDJExkHg+1PxhdykZPUHvUaHB+7mnkqRx1piGry4FSU2PqTT6Q0OTrRQvSgUiiGUfPn1pmKnkXMZ9uar00SxQBSgqOtMpaLBcUtnoMUmOeaWlpiEGRTxTcE9qdt9TSGIfQUo96OnSg0AAopM1JFH5jeiigBYotylj+FIVDDBHFWxxjA6VC67WP5ipuaJFCWIofUVHxV8gEYI4NU5ECuR6VSZEkM6Gk9hS4+tGMdeP51RBLE/lsHHXoKjkcu2c5A4FNz7UBfUcClbqO+lh6yuF2A8H2qOlxg/SkXA5IzxTE22H50cfrSjGDxk9KQAjBNMQnYGjvQO/1pO+KAFHWikooAD1p1N70tAA1IPaloHrQMUHnkZpwX0P50mKnhdUYl4w4IxjOMH1qWyoosWs7R4SUBoj13cgfSu1m1Qp4Ygt2EhDI6RurZRixGfoVAxj3rg4pXiPGCD1UjINdJpM8VxayWasVjflon52P0Dqfrx+NcmIpp2b6HfhqjScUykeaBwQacVKkhhyDg0mO1anOx+47gRSZy2e9GOaXHNIZY8wsNrDqMH3FQugDY7U6Lrz0qxKqsoJB3f3h3qdmaW5kVgBgCsjG2Z1PqVNa/Q4rNvoyk+8cB+fxrSD1Mai0M85BI7jikNWvs7T5aNSWHJA71AmEf5h0PPtWtzHlfUjx68UY9BUkjBpCRz7mmYJOKZLQqgHrUnlhQjbg27naOv400Rnuce1OAxwBjP5mkykKwDNnAHsKsWlnNeS7IV4zgsegq5aaQSglvD5UfZP4m/wAKtyXGE8m2XyogMADqawlV6ROmFD7Uy2PsGnaf5VsN94x+eRhnj1/+tWczsxJbkscknvUf3acCRgjsazjG2u5tKfNotESAHGeoHT61oykRQQ2o4KAvIfUmqdqoMvmEfJH8xpksxYMzH5nbJoauK9jdGszfYoLRAUWNCjFG4ce4qjc3ks1t9hDhoFO5QV5B+tZ6ykfdOCO5pVkwTk+9HKhc7Iickt0bOMUg5wTSOQX3DIBNSPKC6hFG1fug1RKY35g4K8HtQ7sxLH7x6n1qzGEhgYscvICPpVVj2oQMmUgMpHTIyauK0i7GGdp6N2rNRssqnAAPetO23R4EgBiz83OR+P8AjUyLgb0UjTaegfayyNgoT+FY8oME0sStkAlMjuM1oKUsrRZM7ppP9UAenv8ASs5VBBZjz/OsomrCJA2SegpsqKj5B470u7acjse1R3km4fKMA8cGq1uLSxVZzI5Y9DVu0m8twh5DcZ7g1TXqKljwSTz9aqS0sTF6noesg6toWn6zjMyjyLjHHK9/x61hNemO1ktYyyws2Suc7vStvwPJ/aOnanpMgD+dB5sYJ6OODj9KwiJLK/KRSKZY2wGUZAPp746VxuKvZnZCWho6XqbWbfZH2SW7nO1+nPUZ7Z9a6O9s3v7Uy2L4mYATRsQGfPQH/aGPxriYYxKH3Nh1GQPWtnRdXaBminCvI+NskmSBgdCPccZ7VyV6WvNHc6YSLLLOq+U7GOO3BXzCuMN3981q2JjmeJ4x5lwOZlIwHH/1uCRVtPsGvQMDMiXir/rBnI9mB6/Wolsr7S7xXYHZKMZiUNGxOe/auKcrqz3NVNbdTqNKmEqRBywki+Zc9SPT6ii9iIkMBUlCfNDEc59BWdYzFUVwVEu4+ZgEhv7x9ulb7EXEUW1uduYyDgE/3a4GrM4Ki5KnMtjgdTtXt2ZFVGSR8oVJ6n+RFZchMUsiAeYW+Vmf7x5rq720eG7eN13xMNxU8bBz/nNc/e2gtiGI3AkFHUfe+p/pXfRqX0Z6MZKSRlzytIViO0bAQhPUc9KrOGTCOODzjPr71aaEH5wQhzgZ7mq5hbcRgk/5Nd0WiJJkcEr2wYoSCwIO1ipxSr9nMUqv5iPtzGUGdx/un296nhtxH5dxcxbod3+rLYL/AOA96jAjC78LvLHEW3gDHXPt6VV0RZjEbblTGH3gDLdjnqKnBAQySxAqzgFy+DkdQAKb9mc7ABhgBk7vXkVpW+hSlGkkRVjIzum6dO3cn2qJTitWNLuU7OGW8lW3s4wryZG9uWPrk9hXUWemx3Hl2NkF8oNi7kUcOwHPX+EfzqTT9CuJkaK1ja0t2X5ppBl5B6Afwit6I6X4fs2VSoXGZXHOa4q1bm0RlUq20jqzG1qyjuLqJpcm2RAIYYz83B5J9AfWsDUbz7HKY42BmK+WSnMcS4Hyp6n1NW9Z1W4vGeWVFW1Hyxxq2C47ZI9ucVzkkg2RKDnaScdua2oU27cxaTjFJkM5BmcqzMpOQW6ke9TXEaQCLpIzxBiP7pNMVTLNtYBR93Kjp7067UCcqF27Plwfbiu1bpEPa5X64pBxUjiPGEOeByB370wKSCQCQBk/StEZsOnOOKcCyMGU4ZTkH0NJycego7Uhog1tEktFuEwsyEsJM42nJYL7kg1hasYrq6E8ahY3RSw6GN8cj8/5110Qt57K4tbsfI3zRPjOHxjB+o/UVxzMlmJrK6DoCd25l5Vsdx6c0qL1aW6KqK6u9mVHBy1rcKFni+VDngiqUsbIdrLgjrzT7l4WI2yb+CGJzz71WeYtjIB/2sV3wizz6klsO3IMbzjFNNyeiL+JpmwlulG3sa1SRg5S6Dtkk3LEke9Me3KjI5X1qxDLHGp3t36AcmoZ52kO1V2jtnrQm72QnGNrt6kKjnpUvk7iB+tQ7SDnnNTJO6feCN/vCqd+hEUuo7zpUGwuWX/apVmwCMYPqKi3qzAvketTKq8scYHcVLSNE2+pJDEJmVYyM+5xj61vWxty8NharvWNvNuZ/wDnow6Y9FBNc2AZW4GPSul0aBVikmUbScRkZzkjqfzrGrsdFFmqB0J79hTmYbFAVQAe3U/WmKATg0vtmuY6Bx+bHHvRnjpyTTc4wKMnIxigZagkAj2N05FTWVpNc3iW0H+sc4znA96qIAXVSwXnGT0FaerXlst1FHpgKJBH5ZnXgynu1ZSveyNYvuO1C1jsbx7aG5FwY0zI68AN3A9cU+31mUsUkj84bdoPIcAe4rFzyDUsU81u5eKRkYgqSD2PUVLpJqz1KVQ65Nd0+VFjm3BsAgypuwcY6jtWnb6hYbRFFeQ7Bhh5kh49eDXnuSV3EEqvGR61I8wUx+ZtmRV4XOMD0rmng4vYfOmtTupm02WXeb6yt+h/cznkVSN9otqHWS+8wMfu24Lt+JNcR+ApCwGOePamsFHqyfaHXP4tt7ZDHpdgI2Py+bK25iPpWLd69fTgIZDEUyDtPzE98msps7c5HXtSRzGOZJcBmVg2D0OPWt4YanHVInnEL8/MefWmMeRyOfSpr66+2Xs115UcXmNuKRjCj6VWPHHeuiK0IcjU0fVv7LvmuPK3gqVKg4qDVb99TvnumXZu4Cg9BVJRnNDGkqUVPn6ic21YjfJIqvIcg4qweajaIg8c+lbIyZWkk3KQB160+fLwofbNRSgBsAY9RRvxHyM+1O3YlPdMZ8zc9e2TT4y0bMQeWGD704YYZHSkf5Rz3p3GlbUiIJkAB5LcVFqM+1CkbHb90f1qXBKtJ0Ve/uelZl8T5pQjBUdPTNaQV2Y1JWiVEj8+dYxxuOD7CugjfYGwAFxgCsmwTMryeg2j8a1o8Z3ZOB361VWWtiKEdLjxIY9vA+XJNFoF88SSgNzkg96hYnIXnk5NSDOeKyZskdfDcRzxkIwVuuD0NZF5psNzl4AIZu6fwt/hWbHcOmME4rc0a3m1q+EMfyog3SydkUd/r6VGq1Rbs1qYMGnXdzK8MUDM6nDdgv1NSzW1vaHZLeBpO6Qruwfr0rodQu01Avb2ObbR4W8syJ964ce/p71kzR21om5gsMX90Dk/41pzGHKkZUpgzlFuMerKKjWSJWyS34rViSdWP7u3k2+rHFVnlBHzQMvv1qyGK+HbcCMU9JnRCinAx0qurBW3Rkce1SvKHIIUKT1A6ZoaBPqNxjk0AdqVRkE0J94UwFrR0rUINNmed7GK6mA/c+cfkQ+pHes9lwAfWgHg+lRJKSsyotxZe1LVL3V5/PvZ2mfooP3UHoB0FUAMN/SpFk2ptA5J60w8niiKSVkOTvqI2WwOppwTYMjlj+lOjHBNN3FZDn8adxWGM7Fvm5oyCB2pDySe1N70xD+hqW3lMV1FMACVcHB6Gq/WnAEDI6g0pK6sVF2YviC5fyZJHXZJczNIQBjhflHH1LVzMY4+ta/iO68+dVByI40jz6nGT+pNZkLRJ/rVLAj8vet6EbQRzYqXNVYDAyecD+lQxZL5J5J61JIcRsAc9hUajKEZA+tbHMLFK8EpZTgZ/CpWjUyk/diPIGe1Qs42KgySPbvTwpeMxg/Mvb1NAhfPCf6uPj1NKSNokRcAnDD0NRggKf1FOQdYznD9D79qAHbsKcg49D61JA3lK1w3LD5YwfX1qu2QoBGD1qRsl40UhSq8GgB2545N7r87ZwQen0pTO5Ztg27uCoPX60xpCE8vOR1JI5+lXLC3UkNKAR1x60DK4SeX5wjcf8816fjTGR0ADBtuc4YYFev+HvEWi6TopSW2imldW3wuNhA7BfX/APXXBXnkyyvtwuSSFU5x3xSuOxzYbaQyk/Q9vpTsGTDgAEZ+Yfyp91EI5CU456VV3YxyQP60yRzc/OByOCKOB9KUoVwcg5680xdoB3DIB6etAChWfOOnrSkL/FKBz0AzTWct1OAOgFJtAUHjnpQAHYePMYj6UEDHykEig84XBB703aWyQMYoADTgflB7imk569e9Cngj8aAHEkgZNSW7dUIBzxz2qL8OaWM4fPtQNPU04D+6APVflNPzVe0ZpDJkZOc8VYKsOorFrU3T0Eo68AZ+lA65JqbeuMDj6cUDIxGwZSRjmpGTJHODmmFuc4oyGBPApDH7GWKVlB6YJ6D/AOvVbO4cg5HU1ZgkZiYm3FT+OPf8qrvC8bFflPvQnrqU1dJouW98IoVj8vcw6Z7U2e/kKjgLjO05qoCU6jr3zSyKZFUBxxnjH86OotbDWvZmXbv4zk4HeojKxLZY9ajx2oxn+taaGWo5XIGKduNM29+/pUiqSpIUnFJjSE75ozRhiMge3FKFxyetIZetGjkUQSBQRyCeN3sTTr6xSMrJbtuRh0PX3H4VSUFmAAySelSbZPKkYhlZT0+nWs3FqV0zaM042aIDC4AbYdp5HFNYqEA7/wAqeJJh8wkbI7ZqF2ZmLE9e/StVcxdug5mBUcDioyeKAB15OPSlCfJvyo+tNaEPUZnPQZowe9OZx0GSfyFNOcZ6fSqJHq+AA3SlKjp2qHilV9vB5FKw7ikY60U/ORxjFNxjpQAAkHinZDDHegFNhB+92pmKAsPHJxSk9qjyQaM5oEPJwp9TTKCc0lMApKWlAzgCgCxijPNWsQnsaXZD6GouXYqCk71d8qA+tJ5EB6P+tFwsVKWrX2RCOJKPsTdnFF0FmVqcBmpjZSD0P40n2aUH7n60XQWZF14o/nUphfP3CPwppjb+6fyouMZVZhhyPerexh/C35VWlH7w8UITGqDmpME8YGe1Rj260/ORnPI9KokdHkZqQdKanzDB/MVajjiSFjL17HOPwqWUiFRwaSpnUKBkYGMjnqKix6dKQyKU/KBnrUHNSSHLc0yqRLEzSjBo60celMQ4L6fpSZx1pAB64p3zAc4I96Qx2eKdwcUzI/ukUoI9fzFIq4403pS4z0Io2H2/OgARdzge9XFUKMAcelRW6j5sDmp+QeaTY0gxxSMgYcdRTs5GO1HQipKKrDFV54yy7gOR1q9MuRuH41BjtTTE1czqQ1NNH5b9MqelRBdx4FapmTQuMDJHWlOQo68/lQcnHt0pCSeCcAdBnpQAh6A0nT6UpIz1FJuWgkCwPOOaD6mjK+350nH4UwF/iOKQ8mjHFO2ccmgBmOlGPelHalwM89DQA3Bp28lQpA4796TAoPHagAqW3CmUbsHHOCetRYpenUUmNOzuWr1o2mxH0A5PrUIpgqQKcBux4qbWVi78zuTwRiWRUyAWOAScCrptbmwVLpVYJnaG7H1FUogcgjPHpXWRMbjwrfMXDB/l27eFK4K4/M5rCrJxa7HXRgpJ90U7zDXUjAYD4b8wDUO0ZIx17053Em1ghT5VBUnPIGKKUdEKVnJkeMMQaXHNOYA9KbVEWLMZtxaPnf5+4bf7uO+aZ5hB9TmohSipsXzMkLhhjYM+tQzxLPEY247g+hqTjAx1oo2DfcyWZrUNG0e2XOQ4PQe1Jc3jXbBpo4ywULuVcE+59TWw1us6bZFDD9RVKTSRn93LgejCrUo3uyHGVrLYzPk7KKu3t+l1bwQRWcFtHCP+WY+Z27lieTVmHRgzDzrgKM87VzV8WFtZznyo97Lj5n5x9KUqkb+Y40p27IxrbTbi4w23y4z/ABvx+Va1vaW9k4aL55QPvuMj8KlJaR8uxPNEi7WBz17elZyk5bmsYxhrEayB23OS5J6k1BdYUrtHAqzldnfdnp2xVe5BKBgenBoQNlYkMvHarNnEk8dwpbEqpujGPvY6j8qpnrUtsxjnWReqHIz605LTQmMtdSzIPJhWH+Jvmf8AwqsznLAYwRin3EpeR5cn5jxnrVfNNCb1Hg9hRg4zSrhW54p8s6bQFGW9aL6gkrXZCxpy/M2cAYFRjcCGJGc1NCyCVWlUmPPzBPSmxLUdu4x6VHnJzTpGQyHYMLnge1N9DSHYAp9Oat2krwTrKOSOoPQj0qFRnFSxkbqlu6NIqzN26s0khW8tR8hGXQdRVAjpitnTp1Nnt6le1V7+wMX7+EZiPJA6qf8ACsYy1szecOqMsjb171BcEAqMds1abBPSqVx/rTjtxWqMJbEYq3ZPCtwpnz5Y9qpinqOh7U5K6sKDadzqPDOpGx1VGjk2iVjGQO6sOn8qZqC/ZtUmQDAV8gfrWHBKYZY5VPKsGGPY102pxxT6mJpZRFHIgI4yWPoBXPJJM6Yu5UW5d5kaOIFxx8o+8Kv/AGuC3dFjiVpE5L+57H6VLbz6ZpSSywyG5mJxCpXBU4xvf0I7D1rDHJwCcH1rDlU3todHM4nTaZey/JKGifa/3G+UqD3BrpdJ8TGNRFe/uwW2lgdysO2V/TNefC5lS3FuMeXu3Yxzn61f02WRrqGNVmfbkhYhls/1rlrYZNNs1UozXLI9WtVsbi3MlrcJsc+aEboD06dQK0orfCovloOMDacgY9K8/sriHZeLHsWRY9siHKMMdTnpnNb2mXl3HbskpJKgSIcZA46cdeK8qpScWY1aEre7I6WeyWVWDKGRhwncH6+9YUvhtkEgRiYWwREUB5+lXBqF/JNHJBHvtmXDIy7Sh7U+4urmJgkLRZC5yX4f157EVmm09DGm61PRNHOS+EpZGBVYgg5HVWP59KiPhQpK7b4GbOVSR+PfdjsMV0MuuwQRKbt0RnGCFPmIarNqGgMjSm3RsYJMYJPPqM8VtGpUN1VrdV9yOf8A+EWHmu93qtmu7OQMkgfnV+38MaewLGee8ygx5YCjHbmrn/CQaCpKrbxZzjHkk5NJJ4rg5W2gkcr93y4Qox365xVudVjbrS2TJbXQgiblt4rYnq0riRwexHangafbXWE3X113kc/Kn4/h2rOn1q+nUny1tk27t0uD7456flWe2pCdZEubl5EjUOwhwiKAe/cmpUZPcapTl8b/AK/rzNzUL5S8n2idJFEZP2VW24x1JNcfq2rM9/FdQyb9qggMPlU+gHoKrX19Lf8AmysFCxnoB1yep9TVTMawtFcIVYrvjYKdxPYfQ12UaCjqzSMFFWRFLdSyyM7tyxywHGaWON3ZRgHGGAz1BojQtEVSPeCMuSuNnpz6VoWlqIrW4eQ4QoRkcl8c4HoMc5rqlJRWgWb3K7BoMytj5WO1fR/8BVPdliWP51JPObhwcBVUbVUdAKjUbtqqMnP51cVZamcncmvLya9lV5ggKqFARAoAHsKgX0554pd2FZdoJJHzdx9KTJ61aVlYgd8oAPX1zSdKTjNKfSgC5YR2128mnzkI9zHiGT+44OePftXI6/pj20x5ZgWx5jnJ3dwfcGt26it7q2aH7V9l1BD5trIxwrkDlc9jWBqOqXT7k1OAqT8pkToT/e470qUZKfNH7ipuPJaRiG2/dFgQWX7wx0/xqsQR2yDU3n7NwSThhg47ioC5PTr3NelG/U8yfL0F3+UcZJz0pjM7Z3E/hTdvPPfvUyAyISOq9TV6LUyTb0IVwp54z3qU4GCBx0pHVR95hUW4jgA7ae4vh3JiPlPHPrTD0FNaZiMMMUgO7BPAoSYNp7Dgu76CkBwcr0zTmct8oGB/OjAUZNAGlZSW6QmTaXuc4jX+FT6kfyrqorcQr5IH3OD7nufxNcpokJutTtbaONpXllVSi9WGen/167e6jRLy4SNw4SVlDL0bBxkVx1tJWO6hrEqYwaXAJqe3SNnYTNtXaTu9D2qIDn0rK5tYEhdwxVSdoycdhV/U9NXTHgiM6ySvEJJFUf6snoD74qmkzxq6oxUONrY7j0prMWbJJJPc1Ot/Ieg5AMEkj8ad5cmCQjELySBkAe9Q56elTrd3C2rW6zusDHLIDwT70O/QEyE04jgYGMdeaMb2G1QM4GBTOcHPrTAcCSvtRGjSyrGilmY4AHUn0ojmaKQsuBkYORmnxswVsKuGIO/HK49D2oY0I9vKty1uYyJQxUp3BHUU2FbclhNK6DaSpVc/N7+1NmY7uSSx5PNR9aEroTYjDuOnrSHbtGCd2TkY4xQScYzxnOPeggBNzd+lWRcaCAQcZAOaJmRpGK5xk4z1pD2FOlg8tEkDZVuPx70xakYBp8YBYk9vWoicn0p3Ibrz9abEmLNjj+8f5UzPBGKXIB3Hn601scnHfpQhFKQ7pcnvTMcEH8ac4waRhk5/GrIGKxjbrwelI7FuT07e9O4PBFKgyd57dBQHkDqUsJ93XKN9OTWJNkucklicn3redPMsLxv7qoevX5qzobXaTI4+c8qPSrpytdmdWPNZIbaxmOIqQM5yanDkEc4ppBU7l59qMhqb11EtFYeWYkE9R3qZZV6Hg1V3bcc0hc//AFqXLcrnsX8jGf5V1KStp/hmDSbXAvtVbM8mP9XH/wDq/ma5Cxi8+9giOcM4B+neujW6zrtzckFvITyowDjk9ahqzsVfmRsS/Y7GzXy5gIIICCI+xz69yen41ysgkus3sqh+wVTxGM8CtTWLqO6e1tY2Co53M2T91eAD+OfyqjK9rbscKclfmjQ0IllSQhgVJG4fwjkj/GqxGDsbGT0we9Om5CupO3qCOo+vvUUzZkLng785HetUZshdRuBHBPemA564z/OppQq7RwWOTn27VARnPcjvTJJo36rVqG23gu5wv86oKe/cVb855EVSeBxSd+hcbdR8gTqoOOgyajVc/SpzC8qgIpbHXFRtwQMYxxUplNPcYAAvPU9KvaPpsmrapBYxMqvKcbm6AdzVGren3s2n3kV3bnbNE25T/Spqc3K+XccLcyudH4l8GSeHrKO6W5WeIttbK7SCf6VxzEkknua6XxB4uvtfto7aeOKKJG3bUzyfU5rmj1rPDKoofvNyq3Lf3Rp6UdO1KBk89KMHOK6DEApJ6c0oBBwePf2p6Nt69P5U44KlMctxn2NS2Wkc9qjbrl8YxuGMVWyNoyOan1NBHdyoOivgGq44xXZD4UefU+NiSH92PrSIQrBiOBSyf6tT70i5ZdijJ6mqIHIcFpT26D3pillfcOT3pzEEqg6D+dJ3zt560CJGeOQ7jwe5HFJ8mRiTLZBBJ4ph4IIHOfSkK8ccenvQA4/6/rnLZpxP70nnIxjFR8hlJGOaeM+aQOCeh6UDEJLOSepbmta3vRb2skJjjYyhSHPVfpWS6lGYEYOc09envSY0i613vY7nYsffpUS3LRyK6sCVPFQfhg00j0ouPlYs0rSOWY8k5qv6j8alI4qI9TQhND8nGSO/WkGPMwTgU4srMMLgZ7Uzq9MQ75GPBI+vNIwIxkcDvSEegx9KUMV+U8igBGJJ6k/WldxkKoGB39aQjac9QRxRtbGdvHrQAhznLZzQuSx+lL/Dk0ife/CgBQcAcUL99aTtSjqv1oAs2jlZmA7irhJNUrb/AI+PwNXazluax2BRmjGDTh04pDUlAemKQdaUDPFIR6UAOSRopA6NhhT55BM4kAG4j5gOPxqLFHvSaV7lKTSsJzxxQI2ZSVxuH8Pc0Y5pQeRjj6U7BcjTb/EPm9akwoI3jPHalfa4Jbh/UdD9aj5Xgj/61AthVxuPFNz82Rx9KexHGOmOtMx0pkgST1J560lKBk4ApzJsxzyaAJLWBrifYhAcKWAPcjtUj3C3VzulVIZEUAgrxIfcfSorbP2uHawVt4wxOAOe9XNUtpnhN24xKrmKT168H+n4VnJ+9qb003BtdCjfhBcMY44o1IyPL6H3Hp9Kqnk5Ylm/lQx+YH05pR8o3d/61rFWRjJ3dwIPcjg/dzUGDux6VIeDtIIx1NMb71UjNhxuGODRjGaQ/wA6KYhM0lL7UEY60AAOOlPDA9RzUdFAEmKT6U5CGGCOafsB6GkMizSVJ5Zo8sntn8KLiI6XAqQQk/wmnrbkkZU0XHYhCknAqVU2/X1qUQNgfLgU8QHPJApNjSFDdOBU3yAZHOe1VQwpQ4HXmpaLTJqXdjiohJ70vmDHB/CkBLuH8Q/MUoKnocfSogwJ6ilGD1I/OgCUMwPDN+dL58g6MTUWKUDHegZMtxJnnBH0p/2jnlBVegHjp19qQFjzlJHycexqlfKHIkUEAcGpCylgucH0qKSSPBXBb1FNIUmVFUk4HWpUjHfn+VKemSAF9BSM4OAM7T2/xqyCXfhfkwSO/apPI80KS2WIHfNV0fCFRxmpUuCE2NwOuQKl3LSQqyPCxikXcF6A9jVhnCpuUcYyO9U5pC+0nqOCfWmNKxQLngUWC9hjHLE02lPFJVEB3peDQelHvQAUoA9KB+tL6ZAoGC9Rmlxk+powARSgZb0zSGiWCIPMqY6nHWvRLr4YSro/2m3ug9wE3mMjhh14rzpCQQRxXpOi/EpbXRxa3sDyTxLtjZejDHGa87G/WFaVE9DC+yaamcEIDFGGxjJweKQ9Aa1LiIXFskzMA0kjscDGO9VPsh6bua6oTurswrQ5ZWRWxk0Y96sGzk9f0pPskg5Aq7oysyHaCMetVmG04NXjbSjjbVe4iaOJpGHQetNMDPuXydg7dargHtxSnrS/dFarQxbuyNl9TUdPc9vzpAO9UQxMUgGac3pSgcYoENxS4xTsUhFAwXGD60EnJJ7U09cUYJ6mgABpTzSYpKAHCgHqTSZ7UGgBwPGKcCPWm0UASx7SwJxx6961o7+2W1eKW1jnZyWVFGzYf724c/hWL0GacjuhyDz1zUtXGnY149MuiN0aLMoAJELgkfh1rZtro/2HcW0mRMZgcMNpUd+PwFYFtrdxCArgSKPXg/nWrL4jinjG2JUkI2NvG4EevPesalPmOmnW5RuOeaX2qexlt9SnihcQ2gH3pkRmJH+7nrVq90S7soDckxS24OPNikBA+oPIP4VOw07meDjBIppHNB5ApTkkE0DExS0qjJ4oxQAqrzg8U5l2uRnPvSsU2gKpDdzmm0ihQccin5z70wUoPHNIaY/cRxQHIOQBimHrQQQcUrDuSE45GQaTduyT971pmcde9L0OaAuOCMeMVBdblG3I6ZIqbLetV7kHAOecYNNB0KtSfdQL3PWmKMt7DmnMep71RCEkfeFXAGO470wc8UYo6dKBDthwDSrFxk4/E0gJxikJJxRqVoOxzgc+9KuFIyMjvSJnJHHNHI4P/wCukBIkfmPtj5z61aktV2DZ94D86SxjIVpCBg8Crg4GahvU0itDMAKnB4qQVbliEuDgBvUVVZCjYIwaL3Haxcs7poXG3JNdJ5v2ayeabaVA5GeTntXJwuI2DDGRyM1avNQe4tvL6DIzWUoXZtGdlqaCS2dxKyGO3i2/fkYHAPooH8zVV7WwM0hM5woBIGTjP+HpWWkjeTjcQN3Ix1pBJIwILHnk+5qlFrqS5p7o0rfRhdyEQT/IeVLgZI9SO1Rz6XPbSmOQjB+4yjIf6UQ3PlrGy8OMZ5+8PSny6jdXJEYbH8IwOTn3ovK4csbFYIqYUnMgJyvpWkyOUgundnlkXPP8ODwBWS6PFMFfrWvvBsLcDqpYH86UgiJksckkk96epxj2p9nbi5u4YHlEQlYLvYcLnvRcQSWtzJbzLtkiYqw9xUXV7GivuITk54ya0dM1S60qSWS1ZFeWMoWK5IHqPQ1QKBBwQR2PrWromhXmuNMtq0YEKgsZGx16Csqjjy+9saRdhNPmP2wqxBE4MbFufvcZ/PmrdtqEtpKS0pwUMbjd0HQiqUDT2sstsQFO8JIpAycHpk9OamufMlWJ5BhtpjOFH3h9Opx3rnnFSfkdUJNI6W01OW1MnVoivzYfl1IwG57/AMq07OKS6tZomlSYhN0ITnBPb3NcpZZeBIZkkG7LQsV5Ze4X+dOkNxaylYLt3WH5lw23jHXHXvXFKgm7It2auidb82riBQu0t9yZQwB+nbniok1OATKWt2THBMTYyfXHT8KiuHF6ZJ49qM5zNEq52nP3l9j+lVULQyeeioxQ9SmVb8D3reNKNtQcmblleQXNxj7a0e5uk4A3ZPPI9qLx4rd4gl4s8RBx5cx9enHtWCkYS3lLpIG+XyiOg9d3vimW7mOdWblc8gDOR34o9gr3TFz6mk+ol3COECscsxXcw6+tW9FisdSeaC+v3gPBTOF3Hvyev096xVMEofBMbdgOc8/pVhbVI7UtNJEzy/cyeFUd8+p7CnKCSstGJttbmhqmjz2DyQrcQTW4UOCJAMjoMj1qlFFAZQb65Z1PylYvmYY6YY8VFuiA2tKoBIyqJmo3vEi+WFTuBwHcDIH9DmqjGVrCvbc23ntbW2VJbYRQuQ7QrIS0n90k9qyZr97u4jGcRqCqoOigjGKzzIW3FiST6mlj/wBejAEKGHfNXCio6shzvsIBxipUzH8w4ZgQPb3poQb2LcKp5/woZiTk9e1bbmY0gg44pd205wPSlIb7xU4zjOKTuOKBABk0v8NOxgDpSIu8lQQCehNAFbWJ7V9DEHlxSXAlIy5+5wOnr1rlNRP2d/Li3xqMBoy24Hjr/wDW7Vf1yaS31GR/NRtx8wNHxjPFZihJYMGIFmB2uG6e5HvW1GHKr9CK07+6tyhPEUI8yPaWUNx6EZqAAZ+R8H0NXZ4mEex9qSRk7gfvH2xVdwJFJON38J6DjtXbF6HnzjqMO9sLtXPqOKjL7GYFiex2ng0gfbwc4PBpQm9iw2qo6mrsZX7Dd7H7ox9BSEOeuacz54Xgd/em4PXBxTIYmWFG4HquD7U7LDB7eho44kGeD+OaYDjuU7WO30460ALnJLN+lMLbj8xzzn608MQ2R932pFJm/wCH5THdrjfDbjBuJIly3l55+bsD0rsdQkZ9QkleJIvMCyBEGBgqCMD3FcrpF35wnjS3VIZVTzY4huLbDnKg5APBOe3Ndjq1zBfR2l2jxNM6bWETbsIMbN3Aw+Ov0rzaz/eHqUVaGhnb8rjAGaTjHFPjQyMF7/SkC8EdxU3RdmPurZrSYROVLbQ3ynOMjOKiIGweuae0LqCWXAUAn2z0pgICkEc9jQtgGGnKcEZ6Zp8SxmVBKxWMkbmAyQKSVU8x/LLbMnbu647ZoAN4UHbwfWkQ4z8ueMfQ+tLHGrPh5AgwTk80i+9AAwBfB6Dk0PKRwppM/MWphHemIaSTyetJT9jdlJpGI3k7QBnoOgpiYzOW6AfSmHJ5NP78UoJKlAOM80ySMfrTTzUjVGRTFYbikOSc8ccU4ANx3PTmhVLkgDpySewpiEwOScAdTmnOgih3vncw+T/GnbopLaRI26EfMR1P+FVJ53kfEn3wPwNAyFzuNIvKYwPSlPIxSIDvAUZJ7VRI0oS20Dr0pgzuII6dauraySIWiBYr8xwOlMkUTMWXCy8BhnrSUhuDK59QeR0qPHHueTT2JU4YVGWHaqRDG/d+hppVTyOtOyOtN4+lWQM2/jTcU8/Wm00Q0aehEDVYnYcIGY/lU0EuZJ3U43SsT7iqFg2y4zjPykU6NyquM8bjketS1qaJ+6kX5pyL8uuCY41VPbj/AOvUEspTJMKMx5IA6fU1EsqLNJI4yMggfhxUbXOeREFA7r1/OhIlsRnVwWUY/vJ/UUnl5QyM3yA/L7n1qOV8/OFxnjOOtTSyJ5kQbhFUYUjj/PerIKrN+8LE7iT6Uh5x3yakncykttATOBgYqJSRmmSKBg1ft7G6aze7ELG3QhWfsCelT6Bo7axfrAW2RIN8jnsta/iXW7do10nTlC2sOAxH8RHpXPOs+dU4b9Tqp0VyOcvkZWn3n2WX5huU8EU/Umt5WEkJGW7Vmq2aU+lV7Nc3ML2z5ORgvLACpHARtqnkdTUQPNKelaGSZpadp8Usb3t6xjsoj82PvSH+6v8AjVC6lSa5kkjiWFGPyxr0UUSXU00McTuTHEMIvYVB35qYxd7sqck1ZD413d8UjLtYigdsfrSE9zVkdA60BsMD3BBpKTuaAMvX1I1e7yMEybsY6ZGazxjGc9Oa1vES5vxL/wA9YI3/AB2gH9RWODwOa6KTvBHHWVqjFk/1X0amglcHODmnEZRgfrTF5xmtDIft6sgOO/tSDOeehoBOPRhQee4HtQAu8dB8x700AMcMfpQeOhyPUUnX86AFfnPIz14pScqGFAVuuPz4pB8jFT0NADjhhwvzdeuaEbGM9O1Dc8YAHqBSAfhSZS0JuwoJGO1Q5KnH8jTeScYNTyl84524wOtMHc9cUoHzYOAO9OKYwSMDqPcVSIeoFiQSQPQUxTggnpmhm3H2FKAcE4ORTEGCQCOSO1N6nAxSjIbjvTt4P3h+YzQIaOUI9KF3sMAZxzS5+8cYpvO3Ge/SgAYk4B6ilTqx9qTGADSrwjH1NACUo+8PrQBnilT7w9qAJ7X/AI+PwNXqqWSlpWxycVeeJ42w6lT71lJ6m0E7CqvyZphqxLAYoInLxsJFyArZI+vpUBHNSnctqw0U8Y2Hj60neimIZRinEUvGKAAAbPemYp2e1PWGRhuCNtHfFK4WuRHk0Ebhg/gal8mTONjY+lH2ebshp3Ar4x160c1Y+yy/3QPqaX7HJ6qPxouKzIEcLnj8qHO4ggVY+xucfMtBsn7NRdDsymelbkF4GjUzANjCEEZ3fLkZrO+xkD5j+RqxdxpDY25RlYmUk46r0ABrOolKyN6DcLsxj0Y4x7UvRQCTUs8ZjlcY9cY+tTQ2dxNA8kMDv5XzOwGQBWnMkrmPI27IpFQQSPxphxwDxUjdS2cEnJNRnls449KtGTQh7DA/CgDP0o4Dc9KCS5x0FMkM5OEBx3NMUZbmp1G0YAqDkE4pgLij8aTk80UAORtrA5rTUwsoYbcGsoVLFJ5bc/dPWk0NM0cxDnBP0FG+PqFNRAjGRRkZqCyXzVH8Ao8z2FR84pM5xxSGS+Z7Um456Cmc9OtLQMrUU4DvS7VqiBtGaeFB4o2jvQMbRTsL60DZ6GgBAxB4pwdvWk3KB0H50nmgdP0osK48O9BkYDPX2FRGX2ppdiMZosFxzTEnPGCc4ApzyoRkjc1Q96AuUJ75piBmLHn/APVSCgAk4AyamSE9W49qARGKeqbulTCNR2obCDJqblpEewKp3GoSaVmLHJpKaJbDrS4GKOlJyeTTAATSjHUUoHzCgr3FABjilz64poPOadkUgD2pfWkHrS9KBjh+tOB4FR7s9RSgk0rFJm/5x/s+2AKsAGPTvULzZXkDr+VUbeUIpRz3456VZEvfYDmsVGxtKfM7k63DDpjmnC4bP8J+lQbwTnbx3xUUl5bxjGdx9F5p2uTexc+04PI5781FPcKYm8zG09S3SsubVGPEaKnueTVMyPKxLsT7k1apkOougrhBIxQ5XPH0qJ2705jmomOT9K2SMGxAMnJp3QUYprHtTEIOWp9NX1p1AC0lFI3AoAaOWp2KRBwaeKBCUmKdRQAwrSHipMVG3WgYuT0ozzSUUAOzk0A4pKUe9Axc0o5pdpPvSEcUh2J4rqWIDa2ADkfWtKw1SSGdJ5VS5x0SYblUew7GsY9MU4EqcgkGk0hptHdQ3/h/VeJ4m064b+NDmM1Jc+GrpYxLaSRXkJ6NG3P5VxC3HGHH4ir9jqN3Ytvs7l4/UA8H6jpWbh2NFU7mi8ckMhSRGRx1Vhg0laVt4uiuU8nWLJJlPWSMcj/gJ6fgRVpdK07UY2l0u9Xd18pz09vUfrWbTW5qmnsYvGanQQG2fcxEw5X0IoubG5s3CzxMoPRuqn8ahxmpepa0EpaXHajFAhO9LjjNOYLxtB6c59abnFA7AME+lHSgCnkBVGevpSHYacdMc96rXHEg9COasZOaglZWJbjOeBTAhxtGO/eo2ILe1OY4HuaiNUiGx36inrtMZJJDDoKjzU8Nw0McyBY2Eq7SWXJXvx6GhjjbqRAgdacGAbODim8Uv0NIByvjovQ9aQZc9MtRyx5IpzJt6dPUHrQM07cYhX5ccVJngAVXtZC0WCc7TgD2qfrWRrcVcgjB5q2Vjv4tr4E4HB/v1UA/KnZII/Q0mik7FWS3dOVGcdR6VERnjpmtRQrEs744yOOpqJgGOSozTUgcTLUlWwQee3vTlxt24Gc5z/Sr/lxkjegPPNVrpQjjYNqkdBTvcnYarDaOlKW6YABHcVXBPrTgxx1p8oKZNI7NIGdsnFaNu5xGpP8ADwKyU61q2XF1H7L/AEqJbFRd2TDPTkGrFzdTXs73FzIZJmABYjk4GP6VHMxMgLAA+q96aD0rPfU18iWOVkRkGNrjBBFXNN1W+0qSR7G4aFnG1sAHI/GqSAAFj07UoIqJRT0ZSZNJJJNI0ruXkcksxPJJ61Pbzja0LAKGwQwHKkd/xqsB8oIpQB71LimrFqTReMrZRtz+YmB83O3HTHt7VpGaHURHHcMIpSPkm4+b0Vv8aowLcardMQWmuCuTxy2Bjj14FLKsTzFVdFIOBkbRj29PxrCUVfzN1LQP31leDfuSSPuD7djV4LHcxrLHJHbSZ2YVsK7ew/h/lVaKC5G2NomkiHIX73XuMVJHYzOx/cTMF4wEI/U1ErMpDriGeNEgMDqysW3Icl/fHt61BDbPJJtZCeQpC8Pn2FasMhsoiJbyJEHJg4lJH06Ckl1e1UFPsckG8fNJBINzg9c8EY9qzUpbJDdjPaO2sGDOVnuB0iHKofViPvH2H41UkMlw7ys4ZsZZiRVtl011JScqewkg9/UGoWgt8krdxgAfL8jZ/lW0X3IZWdwVwRlx39B6YpI2i2ESRsxOcMGxipFW2GC0kpHcKgB/U04SW6AiK13f7Uzbj+QwK0IK6QvITtUkDqewq08zyW0MeyNUhHVUwTz3PemSTzXDjzZGbjGOwH0pOgKjv2pvXcVx9y2ZMAYTqB9e/wBaYjIGQsuVBG4eo9KQkNt45Awamt5IUSSO4UmNhwR1DdqWyDqT6hc20rgWkZijKgMPU/SqBK7gARk1bW1EWJJ0LDGQnIGPViOg9utSh41KyO0KRbTmNBwT75wT+GaIqysgk7u7Mua7igkEZjuJpCM7YkwP++j/AIVQurwzwyRsBZSqR5ZVmdvfd2x7ita+m09Tuih3unV0L4auZ1DUSyyAOilhjbGuAPY9zW8IX6GMp2MW6lk3ss2C2c7j3/GoI5xETiNGJORuGcUsi7+Sefc1WYgHGcV2xirWOGU3e5OHZJSNzYBBPPQ0+4kQxlU2nnn5eMnriqwkIYNgH+tG8thjgnP3TVcupPPpYYxGTkDOO3albiJFH8RyaYQWJUDqeaeTlFP935aoyGDG75hkduafynBxxyM804bVj+bGfSmAFlyB8ueOaYWEAZsjPGc4pE5Yr6ingqcq/HPUUxP9aM9uTQIFwRT1P7vOBz2qMDB3EfKaeGxxgdPrQwRsaLeQWd55tzCJ4jlGjDlDtI5IYcg/5xXcQ20L+HkkiNuptmUfKhDTq2QG9OMY9cDOK83t3Mbb8gHkZIzxXR6NqslvDLCUkFncEAsQcbhyG9Mjn8zXFiKbfvI9DD1VblZ0ljHPPcxxWqkzMcAL3q9qejpp2N2oW8kp+9EmSynvWdJIGIkt5MhcDK8VHu6seSe9cdm3dM6+lgm/1z8k5NGxdgbcOuMd6c2CCxODgYGOtM6npWhInGeKDgjpgjvVmO8lis5rVRGEmILnYCxx0APYVWzyGIyM9KEAgGQT6UU7ILlgoUZzgU7YCCQec0XCxEABx+tDDGQO3cVOI0e3OFbzFY5OeCPTFRbeM9KdwsOtbqaymMsLBXKMhJAPDDBqB2DODtVQABge1alvFBPp8pABlhBdgxxu9CPXHpVCWNCwEbhsgdtuT3AzUxkmxyi0rlc/K2KVXwCMDk5zQylTggg+9CFVkUsMgHkVoZDWGfpV2Z/7TeEMtvbtHEI8oMb8dz702a6jFo0MaKdx5OOR6VUNtMqiSSORIzzu25/SlvrsVon3Enia2lxuViuDlTkVTu5mYMgwvzZOP4qnluYoYmETh5GH3xwB7YrN3NkEHkVpFdzObXQVJSmQDgHqKG+cZ9OhqM8HtU0NtJIM/cHqe/4VZCvsSWjxbnSdC25SFYdVbsamjQRHPU96I4lQYXOe5708j5c9akq+hLBeyafI00IVlIKsrDgg1nu5dixPJOc1a+9lTj0qiTtJU9jwaSir3HzO1jUaOzvbINGUiuUHzIxwG96yjsPG38anK2zWu9ZCs4ONhHBHqDVUgZyDRBWuOpK9hjbAcAUqMiFi0QfIwMnoaD07Uw1qYbMlgtzcS7FAB96Lq0e2lMbgZHcVseGtLGqzTxxXYhulTdEhHD+orIvHlM7rKcurFW/Cs4zbqOK6G0oRVK73I7cgSr+NP6O4/wBrioYj+9U+9SuCJSAf8itepz9BGI3ktz0OPWnM4XG1OQMZPOKibsR9KQuzLtJ4HNMQ1wzHkkn1zTckkMeoGDTic4HoO1ISM8HB9KZIvylCSTnPAph9j14pQrsrMOVXk+1J16/hQgZYtr2e1WTyXKGRdrEHqKgzk0h4Io9KEkncbk2rFmBS+QATjk09unvS2LbXY5wMYq0FhyRzj3qW7MpLQo9xSmrmyA/wmgxwquQo/GjmDlKQ6Vo2+jXE2nyX0hWC2UfK8nWQ+ijvWnpP9jW0D3d8gnmVsRWqjg+7H0qLUtbn1KYPKqBFGEjAwqD0ArJ1JN2ivmaKnFK8mYPlv2Q/lR5Mp/gb8q0DO56BfyqzcSx6cImndbmVxkW8Zxj0yep/AfjWnMzNxXVmVFY3MrhY4mZj2FEto9up+0vHBzjEjAH8utJd6lqEqmNpxaQf884R5YP1PU/jWUbmyhyVUzS9m68/U1ajJ7mblFFnW1il0+wuIWDqnmW7uM8kHcOvs36Vzo449K6k208uhagk6YlQpcDA4BHyso98Nk/SuYkAD57GtqL0a7GOIWql3BTggevWo8bXIPanClkGQH79DWpzhtYqWGOOKVAHBJIUew5pF+YjDEev1pGJJ2gFccYpiHl4k4VNx9WOaQySMMZCjHGKQLjtj3NITlQpHINAwClup5pCMHBp7HYMD1pgU9/WkAoYocHkClG1jwcGg9j3ppAPSgZJsYHgrn1zigoSxJK8++ajIK9CcfWk+rE0APJVepyfems5Y89KQDHbH1pdpB+tACALjv8AnS49DkelKOecD6U3oeaADsRRtBzz2zTvvfUd6aOcZ60CDBwQRzSADjpz3pRwTn6GlIUDA5PY0wGngUp4VV/GhRubnoOtB5OaACnIOSfwptPAwg9+aQF6wRtrOAeuKvGOaU5IY+5pbL9xaxr0JG48etTmYnrWEnqdUVZWIBaykdAPrUi2ZOMsPwp3mnuAaQvzxxU3Y7IeLOIfeJ/OlEFuOoFQkknk0EY70aj0JttsP4B+VKGtgR+7H5VXxwCKOOOOaALf2qJf9XEi/Xmke8343Ekeg7VVIJ5pCDRZBdlg3C+h/KkNwMY2Gq+Tg0nvn9aBE5uB/c4pPtBPRRUBI9vzpD9RTsK5N57dgtNM79iKj3KPSlRWlcKgyxNACmaTB5P4DrUO9w7NL8yvw0ft6/WrqW7PP5UXAI+aQkdO9QTpHF8qYb+82c0wvqauneG59XuAIwRCJPmkbspGa7a/vdJ8K6G1pGiEuhXYOS5x3rD/AOEoi0XT/ssUe+Qp2PQ46muGvb6e9uGluHLyN/e7D2rzFRq4mX7zSK/E9WdWlh42hrJlWU+Y5IGATnFMYBR1+Y1Yht57pnSCIsVUs2PQVWK4z7V66a2PGkn8XcYRTkHGe9BzSDsKoyHg5571F/GfrUnQ+2aYPv0APxTCMfSpKQ0DsREUU49aaaYixBLt+U/hU2/npVKp433DB6ipaKTJt5pN59qSj8KkoXcaNx9aOfSigBhfmjzPpTKTFUSSb+OtJv8AQU3Ge1OCMe1ABvPtSZJ6mniI9yKcIV7kmi47ENKFJ6AmrARR0Ap4pXHYriFj1wKeIR3JqXFLjnFK47ERhQjAGD601Ew+1hU9GASCaLhYQgLjAA+lKFpG7U6kMMVWmfc2B0FTTSbEwOpqpTSE2FGfzpBzTwMVRI3HNOAoHWlA4pACj5ifalHehR1oxxQMTHOKTBp2KMUAJRR0NOA9OtADcVIMACjYFB3uE9j1/KmG6RBiNMn+83J/woDYsqvAkchVzkFu/wBB3psl6kfCDJHdv8KoPK8jZZjk/nUZo5e4OfYsS3kkvDMSPTt+VVyxbqaSnpFJIcIjN9BVWSIu2MqT7ox3pXheBgJAA2M4z0plMWwjHApiignc3tTqYgPSoycmnMcfWmUASKOKWgdBRQAtRv1xUneojyaAJF+6KUUDjFLQIO9BpRSUDEziozyaeRzUdACiloXmlxQITpS0tGKBjxIVKkHBHet2znt7rPnQxtvQqwI6MBwR6Vz5HFSW8vlvz0PBqWrlRlY6FdDtbuFBDL5Nw6Bky25G9Qe4NVP+EdvmWQwqshjfZIm4Kyn6HqD60RXzRrlQAcH88YBH4Ve0/UvPjUuf9LhTYwJ/18fp9R61HvI0vFmDcWlxaP5dzDJE3pIuKiAKnIJBr0aK8eeDyVEN1buoIVk3bT3HNVNR8I293Yi6sont7jBYxAEo6jrgHkH2qfaW3K9nfY4pZyOHXPuKnjlIYPG5DL0KnBFJLp88Wfk3Y67aqlSD3BFXdMhxaOls/FF5AhiuMXMRPO/7w/Hv+NacF5p1+/7tUSQ9UYYriRKw4bkVKkgJBBwR07GolTTLjUlE7eS2t1ALRKB0z2qM21ucHYMezVgWeuXVqQrkSp/dbrW3a6hZX2FQiKQn/Vtwfw7GsZU5I6I1YvckaxhwDyAe4ak+wwZ4kb6ZFTSxvsGCGUenb61BngYrO7NbLoOWwiJ/1rD8RThZWy9ct9WoaUEDagDDjNULi6VDhTuf0zwKSuwfKh199mt4ykY3Sv6nOwVlE9zTy25izHJNEiRhCWmG8YwqjOfxrVKxm9Su3OTTcGg0uD0zWhkJUgiPll8rgHGM8/lTBT0XcDjtSZUQVc1L5LKcMn4EYpYH2OrYGQQeRxXr9t/YvxE0dYpFjtdahjADKoGceg/iX27Vy18Q6Vm1odFOCaueRCASACLO/HKHv9KiG5DgceoNbGs6Nd6JqL2l3GY5UPBHRh2KnuKJJLW/05vMEUF9AC3mdPtC+h/2h+tWql0mtUN0/vKllhncBQqkdz0NaENv52/DBAiFiTWbZzNbzCRApI/vDIrXt7uGTBkXY314NKd1sOFmtSp2orT8mAnPl/rTPIhLHCNgnjmjmFyMpLypHpzSDmtA2sajdsxnpk1NLaWskKNENkmMNzxU86RSg2ZBHf0qtdjKqfwrX+wcZ8z36VWvrFY7VmWTcRzjFWpK5Di7GLSjg0YpQvNamI8YL8DA7CtK2+WcnA4GKoQjMgz61qWdtLMjugBG71rKbNoEhbJ5FOXGRnpUosbgkfu/1p32K4H/ACzrO6NRpA4wQR6UNGVCk45GcZp4s7gf8sjTxaznGYzU3KREB82K1b7RTYWizvfWUjsQPKil3MPyqktnKSF2kZ7twBTPs0in/Vn8BWbd3oy0gR2iYOjFWHQqcEVNC8e2Qyby2PkAHBOe/wCFRiGTp5bflVhCosXga2zMZA6y9wMYK/yoZSuIspUAAbcHOQeafJMxYrvYqOnNRAbd2UJyMDPY07aGjIYEMOhx1qGkVdjobhYpQxhV17qT1FHmR7WbaRJuBUfw471Fg+h/Kk/OnyoXMx27mjOaT0pyEKwYqDg5we9MVwA4pUxg57UMQTnAHsKT3oAUEg5zzS55FJ3oFACj19Kv2Fr5pkcLvkTljkBYvqTxn69K52/121sXMQiNzIOSgYqoPYEjk/QfnVOzt9f8b3gtUcR2qH5tq7IIh9B1P5mrVJyV3ojN1VHbVm3d69oumSO0l217c5+5ZjIBHHMjcfkCKwH8bXIlZ4LG3x0Tz8y7V7DBOP0r0HTPhdoNtCrztLfS45MjbUHqQF5/WpNQ8GeGBaypDpscbYIjk3sPmA+vOa2hGmtlc5p1JvqeW3Pi/WJxt86KEAYxDAq8flmseW8uJTl5WY10Wu+H7PSrd2SV2kkP7tZRtKj29fTmuVYFWwa6oqPRHNOUurFaR24LGo809TkY7jpTTwa0MmwIZacGBI3DFK7ZfjimMOOlAD8c8Dr2zQhXJXs3amKWCgjpTgUfgjDdqB3AjYfmHGeoqTen8LZAHAxjNN3MvBGaT92f4WHtSAaeW4HJ54ob5eM8nrS7jj5Bt/nTMhT6mmSOLdccZ6+9JnA4HNNbIPNLgbST1zTsFyWJo9w8zd+FdVo2oxKjRLewKHADRTLhW/MY/lXJA5T6VND0GQD9aznFNGkJWZ6bC5glMyqLS4YfLIq74XGOhXngjHTP4VBLG6svmeWHcbgI3DKR7Y/lXGWd/d2KlLW9eJScmJuUb3IPFb2neI7S4/0bVAkIJ++gJTd68cqfcZ+lck6PVHbCs9mbcUSumCfmqF1COyg5APWp1hMEgjnYsjR74nUg7/oRwR7iomXJwmSK5tU9Tr0a0I+OKsQQJKsrPKkYjTdgnlvYVAUK5GRmlCk5x2Gab2FsNHykHGfanKPlz23c1Jb2s93J5dvC8r+iLmo3Ro3ZHGGU4I96Lq9gAMFGAAecimMc4Hal6CleMoAWGMjIpgOhEqZnh3AxYO5f4eeKlSa1knDXsTFGPzNEdpPvjoaq5OCMkZ6008jk80nFMFKxp6xDYxCKSxuhPG3BjZfuj+YrHYoeqsn05FP9qYU54HPsacFyq1xSd2Sw3EVuSU2vL13NwF+gPepX1OJYX2qxDZI3jJJqk4UM5ZAWPTPbNV3iAxwo7bs07JhstCtOzSyvKcfMdx2jAFSR2oKqztwRnC1bitBcr5US/P1OOSw/pSrHucIoGR0H0rRS6GTjbUaI4o+I0GPVhk01gVNTLH8obGeelRv82MUJiaG+U5VnUHYOppBkc4471MpkMWwZ25ztx3pmxyuNhzn0p3ERBcjPaqEkhZy3HpjFaLRSpGxMZ245JrLJ7GqRLHBsHAAyexNNLnPQfiKXnGDimt0FMTY1txJzgUw/nUhwR0waZj3xmqRLFSV4mDI7Kw7qcGmEknJoxRjtT03Jbb0EBKkEduasy/MqSjr3+tF3bLayiITLK2AW2jofT3qSJQ0G1vXBpXTV0OzTsyswBBwcDqBTOtSFTG20jGOlRsu1sjpTRLExxnsOpoVdxGOveg09JAkbAAbj+YpiViL2FHc4pwwOuSM0nr6UxBwTSHkj61LEivnPXtTFX58dcUrjtoWrQYDNirJ5bp7cVDE/lxhdvPel80nsKh7mi2JMH0oYDueR2qLzG7EYppYnqaLBckjHycHjNO46DOagGVGRxWhaaPrd6itYqIUcZ86XCgD1Hc/hRp1ESj+z7LTpbi+nWObaSiZPmN6KoHr3Y9BXMfbL7Upyun2hQn7xjyT+LHpXVjwrY2jGbULh765LZcsSEz/M1VvdatbJPItEQ7eAqjCr+VVGaWkVcUqbes3ZGC/h65Cl7q5RWxwoO41Y0TSFW5N1JsaJG2RtJ93f6n2HX8qga5u9SukhVi8kjbVUdKsalLGkC2sDZihwqEHh26s3+farbm/dvuQo0171tjQuNasLXbYQNLNaAkSsq7Q5OQzZPJFclfWxtrmS3J3eW2Fb+8OoP4itLzogJHeIGZyFXb0x9O1Vro/abZJh/rIf3bj/AGf4T+HT8qqnHkZnUl7RamXnI9KepB4PQ9aRl2tx3/nSZ54roOVDcbGKn+dKeT6+/c08jzF/2h09/aowcDnrQK1h27PPPHTmjPzD86THYDBH607dggkANnPFAxOC/sP50vZTn60EcnJ4Pf3pD064x0oAAw7ijvgD5jSknI6A4pPukjqe9Aw2jnPJ96F5yx7f5xSnqfT6UfwD60gG9TjFH8K+tA9+lKc5AHUcUAIO49aTg0vGM9OeKDg89D/OmA0cH9KVh8x9M0YwwBHejqxI9aBCHtQTSH1NOUZO5ug/WgAxtTHc80lKSScnvSUAKo3MAfx+lWLePz7hV7Z5+lRKNq+7fyq/ZxbIy5HzN/Kpk7IqCuzRyB3FIWXoCKhpKxsdFybevrSb1Hf8qiwT2pdp9KAuP80DtSGUntTQpo2GgBTK3TgU3ew4pdhNGw+tAtRDI3rSF27mnbPekKAD1phZjNx9aTOaeVApdooERdqKkCj0pyxtI4RFyxPAFFwsMjjeWRY0XLMeK0kjW3cxDDKnVgfvt/gKnFibSzIUbp5B8zD+Fe9ZV3dR7FUMMDj5fSpT5mXJci13LFzc+bGFjXyrct91TxnvknrWRcTjJSPBAPLDvTJbhpOFyF+vaoSOK1SsYNl8yBo135zt4PqaEx5asQAAo7e9QEkKo9qeH/0faQMqTU8ppz66mlo2tvot3LOkCSpLE0TRtwMHvWK5LOxx1OTipMZjOR3wKZjK++acYJNyW4p1JSiovYYeaEHANOxzSxgFfetDETGcccVHj95VkLkgLzg1B/y1oAcR3ppqXHFRkYpFMaRmmVJSYyaZIzGOaUEqQwpxH5U6MBsoe/T60BYnDBlBHenVXhbaxQ1Y96lloKKKKQxnbpShQOwo9KcKBAKXvRSjGfagYntSilOM8dKBSGSrBI67lUkD0FM2kcHg1csr9rRhxuX0rX/4lurLgjyZvUcH/wCvWM6soPVaHTCjGovdepznajFaF7pFxaZbG+Ps61n4rSMlJXRjOEoO0kFHWil7VRA09RTsgDJPFJ1IxQVyeeg7UAVpTn5j1PQe1R4zT5W3yE9ulNxVIlgKkA4poGakA4oYJDMc0uOKVRzVyKxadfk69s1MpJblxg5bFMD5fxoxirEltJBxIpXHc9KrNIgHc/ShO+wpR5dxf4ce9Jjjk4+tQmc4wvFRlmPJNVYi5O0sa+rUxrlyML8o9qh/WjBJwBn2qrCuBbPU0lTJbO3J+Ue9WUt44ypI3euaV0gUWynHDJKcIhP0q5Bpu/BkkCj0Xk1bUbeOx/SnI2SfXOahyZpGCJ4rC0iUMsW8jqX5p1zJDbwGQgDH3QO5pnmhBuLYUdaxru6a5lJ/hH3R6VKi5MqUlFaEMsjSOXY5JNROcDFOzgZqPqa3RzNiqKWgUhPFMBrHJoHWkFOHWgQ+iiigYjdDTR1FK3pQn3qBD+9KKSlz2oGLSdqKO1IBp4BqMU9vummimAq9cU8AZpnepMcbsj6UCExRjBpSOAfyoPTNACYptPxzimsCG+vNAye3lH3JOh6H0p+94pFkQlXTpiqlTK+8DP3hSGdBZal5UYuFLGFj+8UdUb+8K6u01ZoXE0czGM8/Kdwx6/0+tedWlx9mn+bmJ+HB9PWti01GXR7jacvZTZ4HOM9x6VlKNzWErHa6pptvrF1NNZKkdyAGITiOTPIx6EjFcndacDI0VxCUlXggjDCthLsrAlzbThUdfK8xRjcORhh2NbEUlvrsP2HUWSO+hQCG4AwTgZw2eornacdUdMZKWjPPJ9IkXJiO8eh4NZ7xMjbWBVvQiu5vdMuLC5a3uU2OvI9GHYg9xVKW0SYbZEVx79aqNbuOVC+xyauye49DUiyK3+yfeta40Pqbd/8AgDf41kz28tu+yWMofcVtGalsc8qco7l+01S6s3GyQlR2bmtuDWbK7IW5U20p/jXoa5FWZOh/A1Kswzz8v8qHBMSnKJ2FzZ3TRb7ZlmQjOY/vf/X/AArFZSrlWBDDqD1qtaX9xZsGt5Co7r1U/hW2mt2d8oTUYAH6eav+PUfrWbg1saqpfcy8qDzk+wqJm3NkitqTQzNF52nzJcR/3c8//XrKkgeJykiMjj+Fhg0kURKFL/MSB7UYzTihBpdvemKxGRTgMYPanMBkYJx709MFNpAGO9K40hENXbC+uLC4S4tpXilQ5V0OCDVLYVwex6U5TmolFSVmawk4s7vxN4zs/Evh+2gnsWXU4mH78EbcfxY78+lcS6ktU1pLDEztLB5pKkJlsBW9femtlpDuAHPQVjSpqn7sdjVtNCQQyyMNn8q1odI1RlBSBJV6jkA4qrauIyB710thqSoVLnJzTnNjhBGUoazQpd21xBz98ruUUhJfDLKrxnoyniuzSZWVkJyTwwYf0rNvdCs7kNJEot5T/HH0P1HQ1kprqaODOb4yRvHHPWl3Lx84Bpt3ZT2UgWZMBj8rjo1QbTWq1MndFkPnjcPzpGVHVgzDkEdarbSKMGiwXMwrhsfhQB0qW4ULKcfWmKM4rW+hjbUlhXmtq3SSCCPO5Nw3A+tZUCZOMd60AzEAbmIAwMnoKynqbw0RoJLKVHznHqaf5so/i/Ss9Dj1p+SO9ZNGiL3ny9N36UCeU4y2PeqO4+tOyfWlYdy+LibA+f8ASrVpftDcxvKodFPIwOayg2EzuO7PT2pwkbPWolG6sWnY7W9jS9tPtFs67sZBAHPtXPC7lB6DP0qnBeXEKMkcrKrdQD1oV3YMRg7Rk1jCm4aNmspKWxd+1OTyqn8KctwSwGxTVL7Q2R8q05LgqwO0cGraJRcMpU/cpPPB/wCWQq1cgSWwlRQcc/hWZ5xz90VMHzIqUbFlpY2JxEuD09qbujz/AKsU6wWO6maF8K7L+7JOBu7fnULExyMjphlJBB7GnfWxNidfIIJaMfSkYxM2TFn3NVxNj+EU5Gdw2yMEKMnFG2obku6JRgRDms/VdRSwt98cSGds7Cw4XHVj9KsG4Knp+taOkaNHqd1Fe3qKbWE7o0bpI3qfUD07mrjZPUmWxgaD4Lkuyl9qiktcfNDA/BIP/LR/Qeg716hpOkQ2NnHaWkflxICPlHU+p9/esTUvENhpM0hmJnupP4IhkgdhWBK3i3xefKtInsLDkFixjVvqerfhxWybm7s55Ky0Oy17XtO0a2NvJf2sUzDBBfJA+gya45/FukiVRBeI7E/NLJkFR325GBzjFV2+Hun2UUj6hqMk0nUiEBFHryck1xuqaRFbSM1rMzR54WTrit4yhsYSpytcNXvnvbySe5meYfdVn5yB0rn3wc+nb2qV8qcMMGomwa6Ec7RCaCcgH9KUjH0ptWZsefvUhJPJpT1pO9AMT+BaMZpR90UdCKYmNVmHAPHoacZB/cx+NJjb+NAAOSaBXGsSc5/Sg8dqVsYo9/emSxD2ooPQ/nR3z6GgBegNSo23FRsd3PrRnApNFJkjSEjA7+lT20e5uqgnsxxVeNctk1aXp/I+lRLsjWPdm5petXGkj7PJGbmwJ3NbOcNGf7yH+E/oe4rttJu9Paza6tn85CQquRhgT/C6/wAJ/Q9q88guVdWWcZyOHxzn6/1qa1uLjTL8zWP7wMMPEy5WaPuCB1H8uorkq0lUVnudlKq4O53csEckrSO+NxzgcU0WsOOpP41Xtb21vrUXFqW8oHa0bnLwt/dY9/Y9/rUheP8AvVx2a0OzR6luN3ihaGG5lSFjlkSTAJ98VWNtGT1x/wACqPenY07dEI878tnG3Hb1zQlYYGzTGQ+AaRrcOQGlHyjApDKCBz07UhlUYGeKeorAbWIAgyEn2qWOytTbzO8rCVdvloP4uefyqDzgB2/Kk+0cdKeorImFpa4Od+cetPhtoRJiOMsxGOeRVX7RxjH610mh2YMf2mVOT90H0rOrU5I3ZcIXZz81rbhyHUj1GMVWazt93y+YF9Ca0tduEGpOEw3r9ayTcHPC/rWlNuUUzOa5XYk+zwk/NvY/WlVYIzuWM56ZzUS3JR1bYpwc4boaa1wSxO1Rk9BV2ZDLH7oHiMe/FN81V6RqPw61WM7nuKYZnPcflVWEXPOcDoMenQ0yWfADMdqjqQapNcMi5ZsAVRmuWkPzHI7LTUSW7E15qMkoKIdsZ4x3P1qj19/ahiSc4pXHIx2rVJIzbuJgYGMZoOQd2OM0memRz60pKnJzTENbBbj1pMAc/wA6XdzwPzpuMnk5piYhINIRjHf6U5gMrSgDuBTFYjqaGYqdrnKnv6Unl7j8v40eSfUUNoLMsSRedtAxuPAOarOpRijjDDsafGSjbH6Gp5UMiBW6r91u4qb2KtcoFcHik61Kyshww49acIGddwGfoarmRHK2QUCnGPBxk5pCgHfNMmwKCXCg4ycVdEIgmwjhyv8AEOmaqxxGQgKOO5q8iBVCipky47DNoA6daTHoKmx2pMVNyrEe0VNaWNzf3K29rC0srdFUdPc+grR0TQbnW7krF+7gT/WzMOF9h6n2ruYl0/QbMwWqBE/jlY/O5+v+cVnOqo6dS4UnIy9L8JWmmos+otHcTqNxU/6uP/4o/Wq+teJYLdGSJsLjHuf/AK1YviDxcZWMUT5A/hU8fj61xV1dy3UheVy3oO1OnSlPWQTqRp6R1Zoalrs945VWKofTisgtn60gUn/GnqhLKiDLscD3JrsjFRVkccpSk7s1LA/2dpc2oNxNMTb2/qOPnb8jj8azJ7ldwO4YHFTaxcq8yWsJzFbr5SY7n+I/icmq99tgt4bWMKRjfJIB95u4z6DpRFdX1JnLSy2RG824jHPoaSC4MUm5vmRgVdfVT1qDBGF6kCkGCfpW1kc/M73JJ4RG5TduXqrjuOxqAErlelSmZSnlOOh+Vs/dHcUjoc4PDDpQuzG9dUMHXrSsvmfMv3v503Jzz1HFKOD75oFuN3A8Ef0xQcdAPxNPKh+ejetMIKkBhg+vrTCw7JDe5oLH/ZB9cU0Hj0zRnOOmfpQA4El/m+tIPWj7ox3P6CgcN2pAH1HsaM4PqKMjHfPagYA5/IUDFxj5uo7e9IOnP1pCST6fSg9jnnPSgA64/WlxvPbHqe1NoJyMdhQIXIAIHNIf0NITzn17U7b3f8BTENVd3J4UU4nPGMDsPSlJz9BTSeBQMSnxqGJZjhR+ppFXefRR1NSBS7KiL7AUC3JLeE3EwB+6OWNawRR0FMt4BBGFH3upPqalrCUrs6YRsh6RBkLUzHoKUEgYzx6UlRqaOwlLzS44q1aabeXzEW0Dv6nGB+dJyUVdhGLlokU+9HtUkkTQyNG4wynBFR96q9xNWEPWjIoIpMUCF6U00tFMQwjilAyKVuooHbFACpG0jhUGWNbNnZpb4ZiDJ1J9KjtYltEDPgyNyfYelNlumQbuAO1Zyk3ojeEVHVkOpTTyhlgyFfhjngisF4WViH5rQnui55NU3ct3wBWkFZGFRpu5CQBimEU9jTDWqMmSPJvxxggYpqMAxz6UM2ABxTP4hQkS3qSqc5yeaToT7c0zPNKx6U7BcUensadBjv60wH5qkt/vHnoaQIleVYI8hfnycZFU05cZp0zGRyR0HA+lCCmG5LUbCpBS7MjNIbRXoqRk4zTKZNhO1JyCCO1KaO9AEkgziVfxqbOefWmINhK9uop4AH0pFIUdaKBRn86QxtOFJSigQtFApelIYUopB0pRQMKcrEdOvtTRS0hp2NKHWbmKIxkh1IwN3as9jliabS1MYRjsipVJSVmwo70UVZADg5xTJW2xnHU8CnjrUExy2MgAe9CBkIpR1pN6Dq2foKaZlHRc/U1ViLkq1J0HJAHvVUzSHgYX6VGTk8nJosPmLfmxqeu4+1TQapJAf3agD35rOz7UZpOCe441JRd0b39qW9zHtuOvo3NY1x5fmt5ednbNRgEnjJ+lSCIk5Y0oU1DYupWlUWqIaesTOeAfrVhY1XoOfenVVzKxELcJw+cjt0qcKFGFAH0pCSRk0/vSbKsOBUIRjk9DnpSt9wj05plPByp+mKQxwYkAZ4pQdrfpUSk7Rj0pk83lx7R94/pRa4XsR3t15rbF+4P1qlSk0h4FaJWMpO7GscnFIvWkpy9BVEi96a3pTqY3WgApV60lOXpQIdRSUp9KBjG605KYTyaevSgQ6igUUDCg0UUgGt0/GmjrTmpq9aYCmnr0FNpV6GgQ8YII70nbFHPbrS859KAHIMin3CfJGePl+XIpsX3qe/MRHvmpZcSuV7ik6HPepB0oKg0XHYaWBA4rRs5VuLZrWU5IHyn2/wDrVnYxSoxjcMhww6GhgtC/b313pkhjBBUHlWGR+Ga6XS/ElnOIYLoeQ0eVjmxnYD/D9P5VztyVuYUuYwAR8rqP4apeWCeTgfSoaT3NFdbHtShdctY7S6lWeYr+5lXG7ABwwI6g9x2xXK3tjPY3DW9xGUkABH+0D0I9q5LS9c1HRJVMEmUByEbkZ9R6H6V6tpmq2PxD0l7MKkGr2yb4dx5b1X3B/SuGrTcHzLY7aVVSXKzjcAcU2SJJU2SIrKexGameNo5GV1KupKspHII7U00kzVoxLrQkbLWz7T/cbp+dY09rNbPtmjKn3HBrs6p3YDsEYAqByCK2hVa0ZhOjF7HKKSpypINSLN2YfiK059KR+YTsP908iqE9jc26h5ImVCcB8fKT9a3U0zmlSlEntrya1fzLWZkbvtPX6jvW9b+J47hBDqtokydPMQcj8P8ACuRwQc9PpTxMw+8A1NxTJUmjtho1hqab9JvkLH/ljKf0z/jVG70e7sYd9xCyEHBBHGOxB6EVz0U+1w0bsjjoQcEfjXR6Z4v1GyASXbdRdCkgHT+RrKUJLY2jUT3M5lyFzinKgzjP410sb+F9cOFc6Xct0B+5n6Hj8jUd14R1K3j863RL2DGd9udxx7jrUc3c0Svsc+IwcDP50LGS20VOyMjlHUq4OCrDBH4UgOw+tFykkT26QRTp9oVmhDDeE6kd8VObJbi3u7+CWKOCGQBYZH/eEE8Y9apMxYdMUm0GNmI5B4PpUWe9zXmWw4P8/tmp0uGBAz0qopwKmjcZGQDQ0CZrw6nO0m9pCznuT1rXtdZVtqSgA55NYEKW7gfLwe+a0IbG3b+JsnoQawkkbxubzm2vYjE+14z1B7GsHUdPNq+9BmI9/Q1aW1ng5ibzF7Y4NSx3aSBopgGDcHIqU7bDcbowhjr60YFWbq2+zyYU7om5RvaoFAHbIrVMxasVbiHemV5YfrVNI9zACthkCkFT8p5HrTDCjnpjntVKRLhdkdtF8u/t2qyFXvilUAKAO3SlxUNlpDkVen5Uu0DtQnBGad0qSxAoP4U/YOOKQe3WpDz82AKTGhFRcHJIPYetOCjFAHQ0+MoG+cMRg42+vapZSOm8KeH7HVkmluizeWwXy1bHUdar+JfD66PcK0DFreT7uTyPas7TdUutKufPtX2sRhgejD0NWNW1y51hkM+xVT7qqOK5OSqqt76Fa38jMWMtkDsMmlAzVzStOl1W/S2iIViCST2Ao1C0Wwv5bVZlm8s4LqOM9xW/Mr8oBb3RiiaNhkdqrFST14o704GhJJ6DbuMAZSCDgjnIpSWdixJZicknvTqVVJBIBOBk47UCGBSakikltZN8Zw3Tp1FJ7VbsrQ3bjecQqeT/AEFD8xrQdpmkvqMpkcFbdT8x6bvYf1rpkKQhYYlVmHHA4UegqO1j+0lbeA7I1GMjgACrzvBpsQYsrADnH8qaVzOcilbaRZ2snnTKpmc5ZyvLHOetW9T1VILddsiopBJx6dsVzlzr/nStIWXBJwPQVzGqa09wz/OcHjGa2j2Rm49WWta1kTblDMFGdq5zXJXVyXJyetJcXRcYB4qhLJnvW8IWM5zK8p3GmCOpAuTmlIxW1zDlvqV2QegxULrg+1WSM9elRsKtMylEjb7xoOSQTjNOYZY/WkJJOT16VZkxqnAFAyFxQO340Y4piBm3Y4wBSE/LjHelXv70nY9PagTGtzinKu9wvrSHt9aUZByOuetMQjLtLL6CkHIH0p2MmkT7v0NAAB296QZJAHbinYwKfEuXz2pNjiruxLHGMYqTay9RxQgqdT2NYtnUo6EStitKzumjCqJNoGdz85CnqKoNHzxSI5XoBxzyKT1GtGdFEkuky/brcpNC6hLhFBA2tyAffuPQ4rdjaOeNZYX3xtyD3HsfesTwtqq2t60d3++tZk8qSNvu7Sa6R9IGjyukT+baTN5kEn+zjoT6iuKro9TupbAli0uBCwkbYXYDjaB1qAJUvTof1ppGaxVzVkZQEUghLZ2gnAycdh61L9aVZGRGReN33iOpHp9KdxWK5Tg0hQhQO2cirCRmQkKMsBnFMd2IVGPC8AelCYNEUSp5qbj8uea6e61WG2sQkLBmIwMVzB+mKaTkDrx1qKlJVGmyo1OVaDJCZHLsSSTmoygqU4IFMIx1rdGT1IygJ60mwetSUmOKZNiIpjoacLd3QsOB0zVm1tTcSc8IPvH+lWZ8Y8qJc8Y46Ck5WKUL6mM9tGrFmy/oDUa2gYsSAozhQK1PsuELnkjqarv+6Bx1PYU1IHBLczJI1UkenvUPygEn73arM7fe9+3pVUitYmMtGN201l6GpCMCmHoc1Zm0IBgCjgHj1pfwoFACBdzAU/y/Slij3yqo6ngVqT2tvb+UsU4nk25kIHyq3oPWplOzsaRp3VyrHDhRwM1NbwRNOiz8RscZz096uWlsZG3YqaezVlO3r2rJy6GqhbUparoN1pmGlAeF+UkU5BHaqUTZTB6rxWnLq18NMfTXkBtyfusMkfQ9qyl+WUeh4p03O3vk1VG/ujmjVhyOtRm1GPkYrVg8UhFaGRUNm5GdwI+tKloP4jVzog9M9KTrjijmYuVEaoqjCgCnU7FBHagdhuK0NG0iXWL8QISkS/NLJj7q/wCJ7VVgt5bmeOCFS8kh2qBXV3up23hDRvssO17thlj6vjqfb0rOpJrSO7LhG+r2NLU9R07w/p6WsZEUar8kSnlvc/X1rzTW/EtxqUuFYxxAYCrVDUNRudTuWuLiQszdSajtIotxkmwQOgq6VBR96WrIqV3L3YaIqhJJTwOPWn+QIxuflu1XJLhOdgCqOgqlLOWOSa6ldnK0kMZsnjgU+znW2uTO3LRqzIPVsYH6nP4VWLYPWoy3WrSuZuVhEPz7yMgH86JpDKc9h0XsBTM4XbRjOM/gK0sY82lgVmTJUjnjNMZtq4HWh3APvUfU5PWmSIBViKQNhJDxjCn0qHGKOlJlLQnkjIbDcMO9RcqcEYNPWXA2vyv6inlfl/vJ7dqXqO3VEWQKcD/CQCPSkMZHK/MB+YpoOelArimMH7hwfQ005U/MuKcCT9KduI7celFwsiIEH2oz3qUhG5KD6g4pPKT+8w/DNO6CzGk4AIP0GKacE59af5Q7SD8qPJHeT9KNAsxucmm5qXyo+7sfoKNsY/hJ+pougsyLOeAOacI26sQo96f5hHQBR7Cmkmi4WFGF6Dn1PWm5yaTNH86BBntSqm8nso6mnCPHMnH+yOv40O/A6BR0ApgDMMYXhRV3TGjLuCP3nY+1ZxbcfanRu0bh0OGU5FJq6CMrM6Gj2pkEyzwq69+CPQ1LiuZ6HWtRpq5p+mz6lceVAo45Zj0UVUNOWSSMEI7KDwdpxmple2hUeVP3tjp0tNA0bm8m+2XA58tOQDUN54vuGUxWMEdtF0HGT/hXN5orFYaLd5u7N3iWlaCshXdpHLucsxySe9N7UUHrXSjmYlB6UHrRyaBCdqB1oo78dKAEJy1WrOEkmUrnb90e9RpAWb5iFHbPWtm3iW3iDsBkcKP61E5aWNKcLu7BbdYgZLg5bGQorMv54p2xjJHAI7Cl1C/MnyIeO57msp5OOtEI9WOc1shJSo4XH1qszE09myajJrdHM2NptONNqiGB5NIfWl7Z9aQ9OKogX0oPT8aD0FBoGLnv2oLFGbB6ik5HAokHAPqKQxM4HHenp2qNj0p8Z6UMETohY8CnKMHB4qxARtxSyxcjHXtUXNLaFdk/I1A6EGrvlOy52N+VQuvy8gj6imS0VDRSkUlUSWByAacaRfuD6UtSUApTSUuc0gExyKUDFJS0wCloo70hhTjgngYHakxSlSMZGKAsAoo70H8vagAoyBzSU1olfrn86ABp41HXJ9qhe7Y8KAvuaebYdn/MVE8DIMnGKasJ3ISSWyzEn60lO2nsKAhPaquRYZ+FFSeWfUU4RL7mi47EOKUKWPAJqyqKDwop9LmHylYQMeuBTxCo681KTThGShc8AdKVx2RGBjgcUtFHegBaWk7UUAL2/GnHrTaWgY7HftTlPNN3ZAGeBSqcUgEBwPpVCRzI5ar7gBmB6dazj6+tVEmY3gn2prHJpScU3vWhkJT+wpuKd16daACmdTTj0NNoAKeOlNp3SgQvegnPJpeM01ulAxlSDgCo6f1NAh3rQKM80UDCiiikA1hU93ZT2M4inTaxUMPQgjIIqFuCKu3uptfWtpDIg3WylBJ3Zc8A/Sk+a6tsWlHld9ylSL97FONN/iFUQPHalPX2pO1B549KBFjytkSSblO/IwDyMetKdu0g5yRxUCHBye1ODbpFz06VNi00IKWk6HFOFItCEZFNIxxT8UYzSuFiW1l8qTsUcbXB9DT3jMbtGeSDx71XHWraN56r3dRj6iky4j0XAVXHysO/enRCexuI7uxmeKSMhldGwyke9LNMHjhj2YaMFS3rzxUsTfKPToR7Vndo2ST0OpfV/wC3AL+SLy7psLc7VwjuP4h9R1HrTCMVseFo7bUfD1xpOQJQxkhzxhu34dqq6V5S63YpdQh4/tCRyxN3BbaR+tcN9Wjtt7qZnEgAnsOaok72J9TWvr1n/Zmq3en5z5UrID/sg8fpissDg4HNXF3VyWgjXJqaWQtarbEAoHL498YqaxszcuUBxxnPpSXltHBcmKOXzAOpx3pcycrGii1G5jT6TDINyZiY+g4P4VlXFlNb/fXK/wB5eRXTO3AyeB0qo/zGt4VJI5qlGL2ObI/KnK7LjB49DWvLYxSnONjeq1QmspIuQN6+ordTTOWVJoRbhTw42n0PStPTtXvtOdWs7yWEjkANlfyrFI5oUlTlWK02kyU2j0CLxut8gi13SLa/Xp5qfJIPxqUaZ4c1b5tK1ZrOY8/Z75eM+gYf1rz9bhhw659xwasJcBiCr8+jcGs3TXQ0VRnV6h4b1bTk8ya0aSDtPAfMQ/iOlZWMxt6Dt3zU2l+KtT0px5U7gf7LY4/ka6RPFGiayAmr6ZbySt/y0H7iT8GHBrNxkjVTTOPU09TXYP4W0O+ybDVJ7OQ8iK8j3Ln0DjrWVqXhefTxMYL6z1A26q862jFmiU9GI7j1x071JomZccrJ0NXIbwqQc/rWcpzzTwcdKhq5qnY6S1v8Y54q6XhnIcgE9M1ykczJ349K0Le8KnKnI7j0rKUDWMzVnsiylAcoeVPoay2RkJVhgjqK1ob2NeGZfKbpntTry1jnQyrjgZyD1FTGVtGOUb6oxgSTWpYaBf6lZTXVpEJI4fv/ADYP4CqrNEIkto0BmPzSORyT2Uegx+tX9M8Q3+i21xb2pULP97euSpx2oqOdvc3M0ZQ4PpS4oBzz610D6DHc6fHc2Em9to3Lnqe/40TqKFuYuMHLYwlxwacPQ0hUoxDAgjsaX0piFQfOB0ye9SbdrFeODimqCaeylGwcDikVYMEcetAFLjIBpQAR15pDAdeadgZ46U0CngVJRNaXlxYz+daytFJgruX0PFR5JOSck9zSYoNKy3Ad3p3GaZTxzzQMQmnBmXoSM8HB603NUtQvJLeNY4XVJZOkjfwD1+tEVzOyJk+VXZpE28Q3Xd5b2q/9NW+Y/RRyaux6x4eMHlprJjVRy32SXb+JxXLafpFze6hbQW9pdXM9xht5fYMZxuJPOK1Nf1C28JrJpWhapLcahJ8l9I5VoFX/AJ5AEcn1NdUcOmcdTEtbHTvqwttOjntHgktZSQk8ZyrkdQfQ+xrndQ11liYbw2/Iz2Ge1cNYa3PYvcIB/o1z8txAemeoI9CD0pbi7dztZu3GOhHrVOhZhDEKS13NGTUTggNxWbNcNIeuBVcyFhTNxJwKpRSBzbHM/pUWMn2qyLY+V5jEAe9REdhVJroDg1uNAwKYeamWMmpFg/8ArmlzJAoNlQrxULDLYq5IVA2pz71XK/MPrVxZnOJCR8x+tNHUCpCPmP1puOc+9apnM0Rj7o/GpJNg2CPB4GT70wDJH40vamIaByPypOvanEHj60qRl87eoGadxWI2Hb3pR/WgjkfWj+H3zTJaAfrTUHLD3p4UnJAyB19qQD94fei4JDlAIY85HPtT4gMkUwDpT4+D+FTLYuG5OhxUgqIVKDWLOpDgeKngtxK4ycc5quKnikKEbeDSY0tdTTk0qVYRc2+WC/ewOldN4Z1yK6h/sfUTtR/9TIf4GrD03UvJxzgHIIrSuNLtrzE0JEZcg/L/AAn2rlnrpI6oLrE054Ht53hlGHQ4Pv7j2qKp/NluLNVugftdsu0t/wA9I/X8P5VFXPsbLUZik+lPxmkIwOlFxhHM0MySx4DIQRxnkUXl1JduGlCbv9lduaYQc00jj3p2V7iIsU3GKlIB6n6UiPs3DarBlK8jp71VySLGeOKYQKeRU0dnLNa3Fymzy4Nu/LAHk4GB3qrisVafFCZSVDBcDPNNNWIEOD/tdT7UN2BK7Ldt+5QbT8uCCD3z3+tCqCQudozyaBwCeuBUE8gbABworPc22GXjosuI8iLHIJ6msyVixzUs0gZ+p/Gq0jjGO9axVjKbuVpRlgKiYEqalY5YU2QgqAB0/WtUYNFqw1FbASf6DaXDt0a4Qtt+gzVCVvMZmwASckAYA+lSYHpTHHHFNJJ3E72sMxx9KMfzp1TOkAtYmSRjOS3mIRwo7YNVcmxHHxMvvVxeGFUSOlXI33r7jrUSNIGnA2FXHFW1bjP41mwSfu8elW45U2EMSD2xWLRuht7YvKgljTJ74rEkUqTkYIPIrrLaQGFo8jIORWfq1oJh9ojjIJ+9joTVQlrZmc49TJ6ijGSAO5xSIflwRyODSk5rUxJJEMR2Egkc8UztQmK2fD2irrl/JDJKYYYYWkdx19AB+JH4Ur2AxwOM96kgtpbmURQxl3PYdqkuI4NMUPqMmzIykEZHmP7/AOyvuamOqNbaQJ440glnyIo4/wDlnGe57lj60O9roas3YtG9tvDUMmx1lv2XDSD7sfsPeuKv72W/uTJJIzknqauXUNy8IuJ1wh4Xd398VmiPZ8x79K0pQS16mdWbfurYjlYINvemGbChc1DO+W61EWzXSkcjlqTNKT3qIvmm5pM1ViWxSabyTxSgE9KHwgHcnrTJY3IHWmM5bpQeTyaMVVyLDQtLinYxRSuOw2kNOpDTBiEcD60qSNGflPHcHvSHoKaaZF7Mso6P0OxvQ0rxjPzLz6r1qpUiTOnAOR6Gps+hSknuOMTfwkMPyNMyQcEYPvUqzRkfMpU+vWpM7hwyuPQ80X7jt2ZBu96M1M0K90wf9k0wwp2dh9Vougs0MDYpMn1qTyQT/rU/EEUnkc/62P8AWmLUZn3pM1L5K/8APZPwUmjyogDl3PphQKNA1Is0AFjhQSfYVMBGPuxAn1Y5oaVsYLbR6LxRcLMb5OPvsF/2RyaNwXOxdvuetRmQDoKYWJ70aiukPZwPc1EWJPNLTe9UkS2KKeD3pg5pw9KALun3IguArH925wfb3rfZQF6jNcoPStuwufOg2MfnTj6isKsOqOmhUsuVlrvTaXvSVmahR3zRSkYPXIoENopaSmAlABJwKU0mKAEqWBBJPGrHClhk+1RirlrEv2W6ncAkIVj/AN7v+n86mTsioRuxIICmoytLxtb5ST2PORTtQvwy+VERsXuO9UPtG6Pac715Qk9R/dqq8hbkmnyXd2LnsrIVnyeahZs0jNmmE1okZNgTSGilC1RI3FIwwORVtIAFDv8AgPWoJW3yE+lCd2Eo2QzAApp6U5himkdqozFAytIevpVuCHaAzDnsPSqrjnFJO5TjZCZ4pTyMelIKVeXA96YkMNSQx7mPsOPrSSLtYirEC7Yx6nmk3oNLUWOQocHt1qSS8kA8uPAweWA5P4+lQSjDhh3qJsktjt196SVxttEjyvu5kdvfcaaZ5D/y0bHu2athhJprR4UmI7seuarGD5FYMOffpVEEZkJ4YA03v7UrxlGIOCPUUzPAoAso4OFPUU8c1UBxgirCOCcdDUtFJkncU9BuYCox71ZhTkMaiTsjWnG7K1LTe1OqzMUUtNpaQx6HawPpWkscVzB8uM96y6lhmaF9y9KznFvVG1Kajo9hJI2jbaRyKZVyeWOeItwGHNZzSjtzVRba1JqRUXoSFsDJpFbKBj3qBnLHk/hSBtpB64qrGdy0SAMmqzuXOT07UM7P1PFMppCbFpKKUDPWmIBThRjApO9IY8cUE03tip4oejP+ApDQRQ7vmbp2HrUkvETflUlRzf6o/hSuVbQqjk4o70YzR3qiBTyaOtJSigBe/wCNOYfMafbrl2+lPmj2gMOn8qV9SraXIacuO/ShCATn09OtCqWYKO9AIkuiqWxYgbiMCstInlbai5P6Ctma1E7JuYhF6gd6hvWSCARRqFLdh2FEZdEEo31ZjsuGPOaAtPI5orW5jYYaAcHNK3am0CYHpSYpcZ5oxTFYAOacBk+1IODThwoODk0AKylQOhyM/So26VcSPfFI7DnFU2pJ3KlGw2pB0pmKeOlMkmnh8nbhlYMMgg1F3oycUo4pIp2b0AgdgfxpO1artaPowGB9oVuPWsljmohLmuXUp8ltdxp5NA60UY5qzMf6Uhqe2MPmp54Yx5+bb1p95BClwy2swmixkNjH6UubWxXI3G5AOKFXLkE4pvH5U7aCMjrTIEUHr2xSjk0q8A5P0pBQNC96UUlLUmguaXNNpQaQx1OQ4I5pgNKDQM0Yis67X4bHDUmGgfa44/mKqRyMhB7VqwtHdw+U3Dj7rf0rJ6GsXcv6Fqj6ZqEcyH7p79xXStH9u+J+kQ2zD7NdXEd1kdMD5m/9BNcAWeCUoeGHFdr4TldbWW/cgXIV7KyYnkFx85/Bc/8AfVYVIqPvm8ZOS5C74zKzeJJrpCCs6K4IHXqP6Vz5Qr1Fdv4wtYzp+mzqhjeMeSVYAHbtBH5c1yr4FvtC85zXJRneCOyUdSmJCFwCRnrjvSZAGT+FK6gNnoKiZs1siGxjsTRFCZGx0XuackZkbA/E1dRAigCqbsTa5myACVwBgZNR4zV2ODz73y8gBnxk1t6tokNtpyTxYDKBx3YetTKtGElF9S40JTi5LoclLaxTY3KMkdRwaqSaaw5jcN7HrWmVw2KQit1No5ZU0zCkgkj4ZCKjK5roNvr0qF7SJycoAf8AZ4rRVO5k6PYx1kkToePQ1Ktwp++mPp0q2+nN/wAs2B9jxVWS2dD8yEe+OKrmTIcJIuJq1ysJhjuX242gc5Ueg9KbZ3tzYXKXFpM8MqNlWU859/UexrP2EcjpT0MmcIzE+g5oaQJs7O3k0zxH/q3g03Vz1ic7be5P+yf+WbH0PFUbqyubCcwXcDwyj+Fx19wehHuKy7ezvpcZgXb380YzWxFb3a2whlvXeMfdiJJRfpnkVzzST0Z103J7lYU5GKMMU54XUcrx6io6g02NW3MV3C0Mh2uOVIqCR7qz/cmRvLbjGeCKqRSNGwKnB9RVi4u2uI1D4JU5ziptZlXuiUtuLuzkEt+Jq5HKLsbSf3o6H+8PT61m5Dng9DzU8bpDJG4cls5yB0pMEWURmJAB46+1aFhqFxpku6M5VvvIehqASFD5ikYmTJA/X9aaMytx68VlL3laWxrHTYmvLj7ZdPPsCbucA1D161NsURnPbpUTAbuORSja1kOSe7HoYxG4ZSXJG054HrR17U0DjryKkRmQ5U89M0xDgwEZXAySCDRjJyOPamipYigZvMBPynAB79qllI3PDWm/bLtnMCypGvQ+pqLWrVbS9khW3MWR0P8AMVa8I6jHYamUmO2OYbc+9dH4xtoJdKNwcCWIja3rntXnzqSjXs9mU5Wko20Z59tUqMHnPNMYEU8EBjS4yPc12phYYvK04HbxSLgZz2oPNMQMQMnnj0rAa7Rlu55eJz8qDHK84Cj3/wAPetK+vTaNG69Y2WRj6AHj9a4w3Mj3TOpON5cfX1rpoQ6s5sRPodTeeKJtE01rGxnP2+4H+kXO3DIMfdU1xryNzli2e57n1pk7tLMWZizk5LHuaiIJOB1ruirI8ybdxzOS2489j71NG7FdvUr09xUG3j2qSHg4P8BwfpTk9CoJpkoznmpEGMUCPDfTpUqR55P5Vg2dkYjsu+B2HAqSK3LkADNa+m6Bc3oDuPJh/vMOv0FdBD4atlTa80rj0XC1yzrxjodUaTerOQaOKAfMwLf3RUG2W6bZFGz+iRgmvQYNA0yLkWiufVyWrTihSFQsSLGvoigVj9ZS2Ro6Vzz618JanckGSNbdP70p5/IVa1Xwta6Xo0101xLLOm0LwFXJIHSu5K1z3jJtug7e7zKP5n+lKGInOaRM6MIxbPOUKCQFuAP1phAyTjnNTADaR3zSFfkJ44PSvUTPMaKoGaftXYWz8wIAFNA5FOA9q0MrDMYPPrSgshypx60rc/nSkAE5oCxERgr9aAMAU5hgr9aB90Zp3JaDc20qOhpuP3w96d3ppGMGgQ9RwePxp0Y+YfSnEYz6E9aVRtYY9TUt6GkVZj8U4dqdtBXIpuMVlc6bWHCnDg0+3jEjYJxUkkJjOCKnmV7FKm3HmFjc5HPTpWxYam9uQpJKdx14rFVth6gVKrj8alpSGm4nY2uspDOjMwMTcENzt9vpWhc26xbJIjugk5Q/3T/dNcPGxkQpn6fWug8N6yjiSxvOY3GOTyD2I+lYTpaXRtGrrqaajnNPZV2gkinvE0MhjYhiOQw6MOxFRNjHNcvU6lsQ5I5HFMPIqTAFMIq0QMIGaYf0qTAJpCBxVXFYhNJjPTrUhHamOpMbEA4HBI96dxWFTywsjyRyNEvy71xhWPTPqKmR1EeQcg859aqXThFS3jKkIcsQfvMf8OlVopSp254PT2otdBexoPMMEA8VTluM8A4FRSS7uB0otrt7O5EqIjkAgpIuVYHgg1SjYHIhZzmomzTz8zE4xk5AFSpbk8t8o9O5q9iCoevSmsDjPvViZNspAGAMYqJh0HvVJmbQwimv938aefTFNccVQhnpUtu0aTo80ZkjDfMgOMim4+X3pB06d6GIeAGl+78pPQdqc0bRncDkURrmQVaFS2UhLSeJZkMyM0efnCHBI9vepGlUFthOM8Z64qu8XO5OD6VEXZSBjBB71Ni+bQ0I71rUkxt+9A5JGcfQetJcNfTW7XbecYS20vv7+4FZqyHzNx55ya0LfUXgBSP/AFJXmNjkE02rbE3uZ3nkNlju98c1OpDAEHOarSYExKY2nkA9qBJ5bZ5C9x7VoZFsDJ9q6bw2PJ06/l3bWnV4U56kRM2B+OK5uJGldY4lLu5Coo7k9K66/EGjWul26kMtveRLO4PUyK+4/pj6Vm9WkU9ItnmdjFJqd401w7uud0rHkk+ldhHHFCTcT7GkAATA+VB2xXM2pbTtUutPk4WOdlYDnO0mrF9q2VCocY/St6kXJ2RlSlGMbsn1W6FywLNgAcL61z08+5jjp2ps10XJ5yfrVRmLcDpWkIWRjUq8wx2yxpuaVuKbW5gHNFFGaBDi+WBKj6DimMSxzRmigbEwaMUvNGKBWA9MZ+tNxT9tG2i47DMUbanjgklOI0Zj7Cr8OjStzKwjHoOTUuaW41Tb2MhhgfSo6s3UYiuZY1ztViBVetE9DGSsxKSlPWimSNozSkUlMB4ldejGnC5fvg1FSUrIfMycXJ/uj86PtA/ufrVcUtHKg52TGf0Wk85vQVFSjpRZD5mPLse/FMPNOoxQAylxS7aTHamTYPSkIyRS96XqaAG9DT8ZHFG0EUDIODSGOQAthuB6+lWE8yxuhvHI6j1FV++e9aqoL6yTP+sUYDe9TJ23Lgr7bl1cFQQeCMg0oH51SsJGG62kGGTpmruSM89awas7HSndXG0UtJSGHaiinyGMqojVgQPmLHqaAsR0UUGgQnrT7yZ4wlt91Ihzjgknk5plSzmF9W33W/yGcF9n3tvtSe5S20MssQx9+aY5zU9wirMwQgrnI+lQ8Vqncxas7DDSYpaDTJFVSxwozVlIQvJ5NVo3Mb5H4+9XVYMoK80mVEinbYnB5PAqrjHFSykvNgDOOBSrbuxycLTWgndsg6CpIIfMYk/dXn8akMKg461YRRGhUd6HIIw11ExWe33j9a0TWe3JNEQmNpyDMi/WkqWBcvn0pshIkePzGX26/Sn444pRxR3qTSxHIuU46jkVUPX8avEVVlTa/Tg04smSEjkKHgnBGDSbyDg8gGmkY57UnXmrMwZixyaB1pB1paAE7GnAYOKQU4feFAy/aWs0gyq7gOanZgmF6EdRV7TLjyrYsePesi8mD3LOowCa5FKU5tM9GUY0qaa3ZFS02lHSuk4BaXNNpc0hjgcilLDZyelMzUbtk4FFgB3LHHamUUoFMNxMetFP2n0pCPWi4+UaetJSmkpkigUpG00ClzmkAmaUKWbA60g5qzDHtGT94/pQ9BrUWOILyeW/lUtJS1BaFpkozEw/GnjrzRjII9aAKOOaB1pTwf0oUZJx2GaszCgUUUAWbVfvH8KsFQylT0PFV7Q/eH41ZrN7msdigQVYg9RVm1TJL+nAps8ZMikfxVZjUIgUdqbegorUcWCIWPAHNYk8pmlZz36D0FXdQm2qIh35NZpqoLqTUl0E70UlKK0MhrdqaBmnnmjFFxW1G4pQKWlxRcqw0jijtT8ZqOhEyQ8SuilQxAPUUxVLHgE/QUuMkCtqytpLeNSEB3jLMT938KUpKJcIuZm3FkYLZJGOHY4K+lVxW9eWpuQihtoByxrFmj8mZ4xztOKUJXQVIcrI6WkxWrY6dwJpx7qn9TTlJJExi5OyGwWZWymmlHzGM7VPb3rKrp7jm0m/3DXM1NN3uzSrFRskJRS4orQxHDoKVWKOGB5BpB0FHpQBLLGNolT7rdR/dPpUYODx0qWJwqFX+6/B/wAah/lSQ5Jbjz8xz2NIBx+NSW8Mk7+XGuWxnFOeF4jtdSp9CKTeo4xdrkOKWl20YoKsJRRRQAtApKWkBKh5Ga0bQDeMHj+VZQbFWIbgoR9amSuaRlY1bu0M80QTbmQhQzcAH3rodMurdpzFBIPsFpGY0fHzNzl3A7Fj09Bj0rj7i+aYLED8uc571La3cijyoshpCFGO/NZVKblCxrTqKM7nrcir4hS+iBLPaQbonJzulJ3HP/AcDHvXISSoYMY5/U1q+GtRi0+OVZpSl6LnzCrH5WUrwRz34xWbr9t9j1q5hXHl790eOm1uR/OvOhHllyHpOV1czZGLGljgZ+W4Wpo4cfMw+b+VTqjMcKpP0Fb3sZ2uMVQoAUYFPBIBHrSEEHHelA7mkMqPI0E7sm3JxyRnHuKnuNYu7m38iYhsDbuI5C+lQ3KHIbHXg1XCkn2HJp8kXq0LnlHRMYeSfWk6Z4HNLRgVoZDkdVRwUDFhgE/w1Go5NLUgXEStjuRRsG4zGTQo+YemaXGBSgcj60AWG060Z9zW659B0qxHEkQxGiqv+yMU+gGs22aKKQpBzR1xzxTpJGkfe2Mn0pOtSUNxVS4iCvuHQ1cxnFRyx+YpA69sU0xNFDbQwwv1p0qTQSmOQFXHUEVHyzZJzVol9iYNkZB6jBp7JJH8rqVPXBGDUCttPPQ1ammmuH8yaVpGIA3H0HSk9xq1i7A5a3VSeFJA+h5q7Z4DYPU1n2wYQgkcFuKsBiBWMlfQ2i7alq4I34HFQj+tNBNPWpSsrFN3ZLGxTcARgjB460mMmkXORTl4JwevFIAHvzTh29ab/FT1680mNEwZPLULww6mpZr65uI0jlnkkRegZs1XUjOCOM84604YBIxx2zWbir3LuN61Zhj3rz0qIpVmCQKu1u3SlN6aFRWupBLH5b8dKjClmCgZZjgD3qaZvMf27VB9pFrdWzEgMZcLnnoCf6VcE3ZGdRqN2czq14hOqQhsswjjX/gL81zwbYjt3AwPxoeVnnmB+8XbOfrmmSZMYz/Ec16cY8qseXKXNqNVC3zjt19hTSq4OANw7jvTo28tiCcZ43UrABuBnv8AWtL6mdlYRTk4yOtCHNxxyppOXwoH4CpkTaowcsT+lJsaVy9p9rNezJbwpukbp7Cu003w/bWeHlxPN1yR8o+grmtC1WHSZZi9q08rqFUqwGPUV38JMkSOU2FlDFTzjPavNxM5J26Hp0Ixa8wAwaeoxigIBVgzbrVICo+Vs5rhbOpDEzxzwOKkApFAwKkA6YpNgNwNpyOfWuV8bt/odpF/ekZ/yH/167GGON5QssnloerYzXHeOYtskJHzxlGVGHHIOT+laYd/vERV+FnDYGC2AAW4NRupyO1ToOADjbuyc9KaUeWUBAWYnAA7/SvZT1PMcdCljkfSnso+U4wOlO2bmwO44pzO5iERQZDZLEc/StLmHKQMOmKQ9acR0qRGUK5ORngY9adxWIOpX605ULFV9TTo03Og6ZI/nVq4tJIJZIZBskjkKsPQjrScraAoNq5SdcNjpzikK5OKkcb2wCcds0vlsCARx1HvVX0Fy6lmKyuGsGuzETbrJ5ZlHY4zz/jUSQs0oRULMT90DJNej+ErRV8MRB0VlmaRmBGQQTjn8qqxeGX07xLaXNopaz3lveL5TwfUehrh+trmlF9Dt+qu0Wjh1Xaw9DT2i4yP/wBVehap4ZtNQDSRAW9yf4lHysfcf1rjrmyuNOnNvdxlG/hbqG+h70oV1Pbc1dHl0ZmwSG3mV/Tr9KsXlwkzDYMLTZoMcjp61VIKH2rVJSfMQ3KEeXoOB55pwbGBmoS2OKTdWljFsvwXIhkXJ7jmthTokkz3t1qJtSrAJHawb2kI6n0FcqzGRtueOpNDTDcMD5R0XsarkMnM7pvFmlJAqQ2t5MUJAaaVUO36AUz/AISqynkCf2e0C9d63BkP5GuNmSeN134wRkbBwfpWlLZm2t7efzy8UqhvMAyB7EfXPNZyowZUa811O14I45B7ikIqrpE/2jT0yQWj+Qn19D+VXCMGuBqzselF8yuREc009AOM08g02gZGRiopn2xlf9oH+dTmobqOSKMO6MoboWHX6U0Izye/f1pjHgNU4ljWJl2Aswxlu30qBuc1qiGNbknFOjhaU8DjuxphYkVoWzkwKMLxkU27IS1GpCsY4GT3JpxHtUmOlOxwMCouVYz7hCHz6ioNo3AenJrRmiLoR36iqLx7Yckcs38quLIaIjtHTk5pIoxJIQR/CaQjmprMfvyfRavZE7lcjjNIOSQaklXDt7E01QPNXHTIpk2JY0wwPtU2KUDmlqblWG44pjx71wevY1MQNoOec8im4yaVwM1gVJHvyKPmUDkjmrFymDvH0NVc4JzmtE7kNWEJyMH8Peljx5n0BpD07YoVgNx74xTJOr8HWqmeXU5wRBaAAMBnDHqf+Arn8SKxPEGufbUEatiFvm4H3irOFJ/BhTtVu5LLRdJs7ZsGWJ5pxuK7izEAH1G0CuXuJTKI4yeUQA4GMck/1FFGnzS52Z1p8q5R+o3rzakl4xw8yK0nuwGD/KqkkpZj71HdSeYUOehOBUsS5IZq7LHHd7DVTnJpjuAMCrE2MBV71VdGJoQMjLc03NKVI60mKokKUCm59Ks21lcXX+qjJH948Ck3bcaTexDgUAVsRaC5/wBZOoPoBmrSaHbr993b9KzdWKNlRk+hz+KkjtpZTiOJm+grqItOtYsFIVz6nmpguBgcAelZuv2NVh+5z8OizvgyMsY/M1fi0q1iwSpkPqx/pWhjsKSodSTNFSiiNUCjaqhQOwGKKcKQ1BRymoL/AMTC4H+2aqEc49K0tUhMWotIfuudw/rWcw5Ppmu+DukeZUVpMbRTi3y7ccZzmjpVmdi9NADo8MgHKnJ/E1nEc10KwE6OIsfN5ece/WsA9qzpyvc1qxtYjpKkXAznnigLkE+laGNiMDmlqaSDZDDJ2kB/MGoiKdwasJTlGVoYjtjkelSxIShOOhpN6FRV2R4oqRl5ptK5VhO1OSPzHC5xSUqsUYEdRSBW6hNAYjzyD0NRr1qWSRpPvHimAc01e2opJX0FoIzRRQACr+nzBHMbHhun1qhT1OKTV1YcXZm40amVZOjrxn1HpTqgtZ/Pj5++ODU9c7OlPqFHeijvxQMDwaSl5J7k0lACUGiigQlPuY/OtUmHLJ+7ce3Y/wBPwptPhl8tzxlWG1ge4NJ90VG2zM5gR7VEen1q1MhaVkClApwQTVYkFsfhWkWZyViOloIwaTk1RmBP51LbvtcAng9aiooA0AuOgAoPA4pI23xqe/el71BqRquWqVsdF6UAAdOtHpSBDTVHFXjzkVAsAB+Y59hVJ2JkrkKRlzx07mp4o9me/NShRx2oIxTbuJRsJikPWlNJSGIaY6hhg0+imIqMpBwaaV796tMocYIqBkZOnT1FNMlohIxSU/k9gaaVPpVE2FA6VZt4DPOFA71CiE4P4Cul0iyVE8xhWNaryRudOGoe0l5EF4Ba2gQdSKwmJJ5rT1ecSXBA6CsvvmlQVo3ZeKknPlXQl6UdKSl79a2OQUUdqSgngmkAjtgY71HmgnJzSUwFqa2MYnTzc+XuG7HpUApwOKTV1YuDs7nrEHh7wx4h05Rp7CGZVADJ97P+0O9cXr3hLUdFYvJF5lvniaPlfx9KxbW+uLOUSW8zxuO6nFdlpvxFmitjb6lALlCMFvb3FeZ7LEUJXg+Zdnuen7ShWjaWjOEIwaYetWbyWOa7lkiTZGzkqvoKr16cXdXPLmkm0gpyoX6D8akjizy35VMAAMdqGxJDUjVOep9akpKWpKFpaSloGLxmlpKWkBUlXbIfQ8inRr+6kb2xU8ib0wOo6ULHiLae45qr6CtqU6Ke0Tr1H4im0ySzaD5WPvVmoLYfuvqanqHuax2CmyzLDFuY/QetMmuUhHq/pWVPO0r5Y/QelOMbkymkJJIZHLMeSc1FmjNJW1jC9xaKSloAKWilpDAUopKcKBgBUbDDkVMBU9tafaJ1yPl7+9TzW1ZXI5aIl0uxMjec4+UdPetbrzShlQeWnCqB+dHeudycndnXyKC5UNxWFfqft0oHc/0rexUC2qC6edvmYn5R6VcJcrM6keZWKtjpwjxLOMv2X0+taPeilqZSb3HGKirIgvDizmP+ya5yug1E4sJPfA/WufralsYVtwoxRSitTEuvaZ06K4QcjO4D0z1qlXR2iYsogRxs5BrFvrb7NcFR9xuV+lZQnd2NalOyTRWzxRRWlp+mi5haSQlc/cx+pq5SUVdmcYuTsi1ottsiadhy/wAq/StVkVxtdQwPYimxosaBVGFUYFPHYVxyld3PQhFRjYqy6TaycqGjJ/uniqM2hzLkwusg9Dwa2iScDGDT93FCqSQOnFnIT209ucSxsv1HH51ATXZybGiZZQDHg7gfSuOkC+Y23O3PGfSuinPm3OarT5NhnvTgaQDmnquelaGIClwQM44qxFb92/KpWTcNgHJ6ClcqxUiBZsZ5PAqdpNrkDqO/6UxgIcDHzMOM9RSxqrMq4zuIHPakxo1rG4ayv7Vph5kkEoOwnIIHIGa6aZrm+srXULsjLvKqDHzbd24E/wDfRxXFQOyP5gG51bI7iu1jLtoNizSGQNJKUYj+EbRj+dcVdWaZ6OHd4tEQoDugIVioPUA9aMe1Ie1ZGoDrS9qSrFu1spP2iORgehRsYobsC1Kske9Cp69qhKCO1fP3j1q02M8dKjmUtEwHXFNMTRn5wCOOab3pxBBwRg0KjMwUDJNamQKjNnAyQM1ZVM2Y+uanhiEa4HU9TUgUBcADHpWbkaKJnliwCADHTgdatRW4UbmALfyp8UAjYk8t/Kpe2KG+w0u5baWy/s4IiN9pJGSR0HsapY5pcUvcVCVim7ijaRgj8aPXsKQc0o5pgIKVgA3yE49aKXHy0gMydpJJmeVizk8k1HgVZuo8S7gPvCq+Oa1Wxm9wUA5B4NPQyxBlRjtYYIHemKMsRnFSBgcAkfWhgi7YSbhLGeScMufarWc46cVnQsYbhHPAB5+netEja5UdjxWUtzWOxdtbeCWzuHabZNHgxqejjuKuWGltdIWXJO7ArJVip4PXrXW6Rq+nWdkqvJiTGW+XvXJXlOK906KdupmalpTWCq5Iwx4xWaBzWlrGqf2hONvES/dB/mazQx7HtinS5uX3twna+gpIzxTuMcdaYB3pwOMVZI8AU7rTM8ingc+1IosQkN8rfrQy46dO1B2/LhdrAc89TVhQJI/cVk3bU0SuVSOK57XLlGt1lU8214ISc9QyH+ua3dRnFjYzXB/gX5fc9q86kneS3mjZzlyJPqw//Wa7MLDmfMcOLnyrlKs0m27kOOCd3FOc7vLCEHApjgz4eMZb+6OtRCOXHCMB9K9CyZ512icxlupXdSFdvMnT06UxY7gjALAfWl8gLzLKB+po+ZXyJFffwoAX0Hep7ZgRJIVyeg9veq5b+CEYB43Y5NX7C3aRljVQWdgFA7noKzm0kaUk3I2PD2kNe3is+RHEd0je/pXfqOKrWFimnWaW6ckcu395u5q4BjkV49aq6krnq04KKsAxjFC4yc/hSgc07HtWBoOUAcVKANo9e9NhCkMWIyBwPWpAKTYCAZrF8U2Ru9EkZc74GEo+nQ/of0rdxTWjWRGjcZRwVb6HiiM+WSYmrqx5CwEbOg5BXHTua6TwjpHmG51F1yI0aKHI6sVO5vwHH41lS6dN/aX2JATcCTyEHvnr+XNekW9pFYaeltCP3cUZUH145P4nmu+vW5YpLqYQp3d30PGQowox1XFObDINoO7PJ9vSrkdkzRqXVkDrlGZcA+/0qoytHIQwwynkV3KSZxyg0QbArgMcDNPAMbkA/KT3GQaf95gz++TT0ie4kwACev0FU5dyFDsRBMsrDpuArtvGWjfvDqUAwrFRMPRsYDfj0Ncx9idDH8jbX5UkcEA4zXq88KTJJDKgeNwVZT3HSuHEVuSUZI7KNL3WmePqioxRxgPjt0+vtTGjOdwzsBO3vitzXNDfSbvYSXt5OYpO59j7ioNC05tQ1q2tWH7vduk/3Ryf8+9dKqpx509DF0teU9E0q1+yaRZwEYKQqD9SMn+dW8VKepOKQgGvFcru7PRSsiEqccVDPbQXURiuIklQ9VcZq0F7CmkYNCYHKXvhMBWaxk46+VIf5H/GuU1DTLiyl8ueIo3UA9D9DXqhFVbyygvbcxXEYdD09V+npXVSxMovUznSUkeROuDULZArpdb0GXTn3rmS3Y4V8dPY+hrCMBLZPavTp1FJXR59Sk07FYjau3PJ5JqMZPJqXG5sZ5PJpSgKk8Db/Ot7nM43JYriR4Bbs7FAcoOwNC3MsamIM20ZwM9M9aijwhy2R6MO1WJl8zbMMfMcH2NS2kxqLaudB4XuyjC3ZvlclR9eo/rXTsK89gma3iZ1OGRww+or0FJknjV0PDqrj15/+vmuHEQs+Y78PK65RpAppFPbtTSBXOdBGRVe7LuibmJwcDJ6VYNVrjPy8nvVrcRS2kcnaPrTSEH1z1NSlTjnB+tNMbBdxRsHoSK0uRYgIzz0q7Z/6k+zVWKEDGMGrlqpWEZHJJNNvQSWpLQDjirVhJbxXSNcxebB0de+D3HuKjukhS5kWCQyRBvkcjBI7VlfWxdivjI5NVbsfcHuatmm7Ax9+3FWnYl6mUUJ5qxaIQXY9MYq26K/DdO4HrTQqqMKMCq5ronlM+df3z/WmRj96v1qxNEzTMVBPqRSxW5Uhzx14q76EW1JMUYqVUz2oMRAGRUcyL5WRUh65AxTyvNNIp3FYjZQ4IPQ1nOuCQ3Va0yKqXKYcMO4qosiSKeF9R+VNc8deAPSpmXBGRjNRyKQpJ9K0RBc8TskM1iyybnito8rjIQ4/rxXLuzJEXJJkkPH06Vv6+oudUKY2xRxxmV88ABB0/p7msQRvqF08sUZESKdiDnCjoPc1rh1aCOfEu89CtdQtC0Ktj5kDD3zVqIgKB/FT9YxiwcYwYduQMDg54/Oo4slhgfSt3qjmWjJDHk5YfjUcke1RnrVpJY8AMy5z0Jp1yoMYIAqL6mltDKdc1Wf72KuyDBxVWRfmzWiZk0aWk6cs4M8wygOFX+8a31UKNoAAHYDiq9kgisoVU5G0HP15qzmuScm2d1OKjEfHgdRn0p4wSefpUIwMVIOgrJmqHKSue9NNKGxSDpz3oGNxTT0pSaaaYhB69qDiijNMRUvbVbyAxnh+qH0NcswIPI5HBrsT1rn9YtvJuvMA+SXn8e9dFGX2TkxELrmRmAZq7ploLu7Ac4jT5mP9KqhSzBVGWJwAK6SxtvskCqAN/Vz6mtakuVaGNGHNLXYnOAMYHviuWuoTBcvGegPH0rqjWbqlp50PmoPnQc+4rGlKzN60OaJgnqKO1LVixh8+7RT90fMfpXU3ZHGld2NCSyMmmRxAfvEG4fXuKxSpVsHOehrqiKzNTs9wNxGOf4x/Wsac9bM3q09Lox+9a2kxq9tMGGVLAY/CsqtvR1/0Rj6vV1X7pnRXvla6szCcjlD0NUmXFdKyBhtYZU9RWXeWRhbcvKHofT61nCfRm86fVGZSVIyc0witkznaEoopKYhaKSigQ6gdaQU4UgJoJWikDr/APrrXRxIgZTwax0QnkH8KtW8phbDAhT1qJK5rCVi+KUdaaDnBB4NKQRwRj61kbC8547UnpRRjOOOaAE70E85pTwcUmaAENBo7UUCGXgcRowcYkGSB1445qgRWjKN9sRgZVs/gaobSxx2qobCqau4zrx602nk46fnTT1NWZCUUtFAFq2P7s/WphVe2IAIJGSeBVjpUPc0Wwoo60CjvSKGkce1JTiTjntSUyRKQnmlpD1oASg0tHemIbSd6caTFACU0jinUlADHjDDj5SOhFVzvU85Bq2aayhhg/nTTE0R23MyZPANdJLdLbWOAeSK5oqUO79ac8zuAGORWVSlztHRQr+yi11Emcu5J71GKXrTlXPJrXZGGsncKDRikqjMM01m7UpOBmo6AFoop6qTQ2UlcZS08pSYpXG4tDc0bs0u05wBT1hP8XFAtRgyTjvU0cW05brTlQL0FOouFhaWkFLUjClFJThQAdqWigUDFFKKSloAKWkHHIpcknJ5NIYUx41YdAD602S5jiOCdzei1RursyKAFwO3NUotkykkXmlSBMDHHXmoPtrSKR0+nes/ezHLkkCn78j5elXyIz9o2SSMvPrUBpSaSqRLYlFFFAgpRRRQMWlptLSGLThTRUiqTSZSHIAWGelaluvlxjsT+gqtbwBQHcfQVcOQfrWM3c6Ie6PQ8/hU/WqyfeHpVlegNQy0w9qKWikAnP40d8UuKMUAZ+sShbdIkQ4Zslz7dqxK3tSgaa2ynJQ7vrWERXRStynLWvzBQBRTkGWA9SBWhmjp4l2xIMdFA/SoL+2+02xA++vzLVvGOnajFcidnc7nG6scvBC08yRL1Y4+ldUkaRRqicBRgVWhs4obiSVRy/Qf3fXFWuadSfMTShy7gPSndxSDilFZmo4HtS5yQBTMnP0rO1e9e3jWKLIaQHLeg9qIxcnZBKairsbqt/Gsb20bbpGOGI7D0rCNMJJPek/P8q7IQUVZHBOo5O5YjRScswAq2qxqBhlP0rODY7j8qlDjjKqfoabQlIvybkTIIz6U2W5EKFUH7xuWz0B/xqOOTbGZGy2D8gJqu0bqPMbqTnPvSSCUuxGzPu35Oc5JPerUaecBtHJ5GOagI3A+nSp7J2VWIJBQ84PY8Giew6esrMtwxxK+1SzsRg54212LRfZ7DT4CxLC2V2B7MxLfyIrnNO093v8AyJBhk+8cZwD0P5HP4V0t3P8AaLp5FJKZCpn+6BgfoBXBWleSSPVox5YNsgHBFIfWloPNQUIM049BTR1paAFzR3oUKT8xwPpQxUt8uQPegZWuYS37xevenQQ+WNxHzH9Kno/lRd2sK2txwFTW1s9zKI4hljUAPPFaGjzCLU4mboTtP41nNtRbRpBJySZVuLd7eZopBhl61H2ra8Qw7bxJR/Gv8qxsUqU+eKkOpHlk0IVKnDAg+hoanvI0jAuckAAfQdKZVkABnJz0pepqeazkgt7edsGOdSykexwQfeosGi99h2ExTsDFOiKDO8H2x2pOM8cClcdiG4QyrwACOlZrct71rNzVS4g3Euo57iqiyJK5TxnjpQBnrS8jjH1pRyOnSruRYUMcbTyK1EYtDE/crg/UcVljmtC2J8kqSOCGH49aiRpAsA8e/anq3So1IyMjinCs2aIlU7qlRQeMgU+wtReXkVt5iR+Y23e/QVPqGmXGm3bwSgMVAO5OQR61m5K/KWirgZ4ORS44zTQ3rTwenFAxV5qVM4xk461GoweRUwADYHIzUsaJF55NTwtsb68GoVFSKKyZa0Oc8Z3YCQ2inqDIw/Qf1riudx55BrW1m8+36rcSA/Kcqn0HArJJAT3Neth4ckEjycRLnm2V2Z42O04Hpik+0yn+L8hVlHlCkKq49dtIsLtjgAe2BXRddTn5X0K5eaTgs3509Lck/N+IqfYFYBnBP1zipwDHjacN24z+NS5dio077jBiEqCMnrgHH/6q3dEVjrdjGg5aXe3GcAZNU9G0qXVL/wAtOije7tXoOmaNb6aWkX553GGkI6D0UdhXFiK0Yq3U7qFNvXoaI9DTgMigCnAcV5R3FmyltYg4ubYzZ6ENjFJcNBJJmCIxJjoW3ZqHFPXlcYHrmptrcLa3BRyalApiDFTI2FYbQd3c9qTYxChXj9KMZp2KdtGfapuIyI9IA8STakwG0xAIP9s8E/l/OtTbkY7U/FS28CzF98gQKMinKberDRGPqOlW+o2X2VwECj90yj/Vkeg9PavNNS0+aG6kt5EIuYjtYD+Ieo9eK9e2Da3PIxgetc/4o0prq3W9gBFxAMNt6sn/ANbr+ddGGruErMipBSR5mYZC+AhH8IUiuk8O6A2ozEPlbWM/v5B/Gf7gNNsrNtV1Fbe1BRnBMjgcKnc/0r0O1tYbG2jtrdNsSDAHr6k+5roxGJaVluRTpJO5Tv8ASba/tUgKiIRY8ooMbAD0HsauMMsSehNS7eKQjkd689ybVmbooajp0WqWMlrMMBhlWxyjdjWP4U0WXTvtc10m2Yv5K/7o6kexOPyrp1O05xkUrhTgqc+uRVqrJRcOjE4pu5GRTMYqQ02pGMx6U1utPPXFNPJpoCM5IAJ4FMNSEc03ANMCrLDHKjxyKGjcbWBHUV5lKnkXklvJwY3Kgnvg16hcxSSwssUnlydVf0Pv7V5vrHnzatO11Csc+P3gQYGR3H1xmu7CPdGFfZMyHQR3LBuBnB+lMMZLdRjr9BVmQCdu28dCehHvVY/KduRkdQeK9FM8+SsxWVCoG7henHWnRuFBQ8jOc1GWAI6Y+tCsoP3hVWFfUfJlIGTPJaur0C/EjG2Yj5IwM/jwPz/nXJ43ybiPlX+VT2d09vJLIpIZsAfXOf6VFSHNGxUJcsrnoRppohmW5t4p1xiRQ3Hb1H50przdnY9HdXGpFJPII4lLMegFaEfhyaZlM0gRQOQOTVCG4ltpRLCxVx3FRXuo3dxJskuHK46A4FTJTbtFlJxW5vC30PSeZnR5B6ncc/SszV9egvbb7PBb4TOdzcH8BWG3X370w8nFOFBJ80ndilU6IPmeTOMn0rQUHao746UkUYRAvfvUowD0zWrZCQzBxnjFJ9e9PJ7UwikhjSKaCVORxViO2kljldBlYhubJ6CoW6YxTTJaGu3mNuIHpxTCPWnkGkbNUIZgk4owc4pckUhkJPT8qA0Ol8H2um3GoyLqO0kJmJXOFJzV3xdbaejxw6fGm4cyBOg9K5HzdrDtW3ayRPEGyCQPmye9cVWnJVPaXN6cU3e/yOfdcZ45FREVpai8Uk7lCuB0x3qg4UbcHORzXbCV0YzjZkZHNRSx71wOo5FS49KbWiMmZrhg/wA4596jbOCc1pyRiVcHr2PpWe6+UxD8BeT9KtO5m0Ra+PMvWtInJXYkk7enyjC/59ar+dEogVnCRxYO0cbzjvj/ADzVmKPZBFc3ChjcyGYh8/MozgfTj9aoTT+dM884jVpQ2yKOMKoyOuB0HpXRT2t2OWtvdkOrH/Q7ANjIU988cH+tVFkQKMz7Tj+FelT6mT9ntkz90sv5YFV7e3RlDOBW6Whyt6j/ADYhjE5b17U0upY7Xb64qwYoU/5ZqR9KieOFhjy1X3HFFkF2V2lYcHBo8wMMUx1IPynI9DUWadhcx1Oky+bYKD1jO01e9PWuY0u/a1m2NzG5Ab2966b2rkqRtI7qU1KI/IGOPxoBplOH6VmbXHA0pwAPemZ96TJpWHcdx61JEkLLIZZShUZUAZ3GoQas6g1qbrFnnydijnPJxz196T3sC7lYcnNA6mm54pOM1RNwPLVU1K3+0WbqOXT5l/CreR1pKpOzuTJXVjH0mzGPtTj2jH9a11YL1Ab60mABgAAD0o2sTwCfpVSlzO7JhDlVkNNJQaQmkNmDqVn9nl8yMfu3P5H0qzo0P7uSQ9WO0VoTRpPE0bj5W/T3qKxiaC1EbcMGOfzrZzvCxgqdp3RYYHdg9qbTuDSVkaswtQsfs7+bGP3TH/vk1qaVHtsY/fLfrU7KJEZGGVYYIpYcQoqL91RgZq5Tco2IhBRnzE7qAATVdvnJBGQeoNOdy30pmSOnWoSNJSTZm3dnt+eP7vcen/1qz2XnkV0Has+7tQBvQfL3HpW0JdzCcL6oyyKbUzLjgioiK2TOdqwlFFFMkKcppAKWkMswthutXUYFcNgg1lq+2pPtJAwDj1NJopOxfkIjUgS7Seg61Sa8uVnMjuXJ4+bnIqISMxwOvqadlU+Xbvc9qEhOV9i9DqEUmA3yMfXpVusRreUgvsC+wqxa3hTEUmSOmT1FTKHYuNTozTqaa0uII1eaF0RvulhjNVwwIBByD3qWa6nnVVmmd1UYUMc4rF3vobrltqR0lJmkqiR2flZfUVQfg4H41dBwfQVUlGJDmiO4paoiNIetOI6etNPWtDIKKKKALMEYADnr2qemqNqgegpahmiF6CikoNAwJooooEJSd6WkoAKQ0tOTbvXfnbnnHXFAbjaTFSSqglYRMWTPyk9cU3bRcfKNxSYp+09KXYaLjUWLBay3LlYlyQMmomQq20jBHUVOhkjbcjFT6imlGZjnknvU3dy+RW8yDHFRmI/wjI7iryWxbGRxUhRY+g5pe0S2GqLe5miLHJp4XJqy0W4lh071DI6oMLz70c1yuRRK2aSlqNzjitziEY5PtSd6SimA8da6Hwtp9tqOprFc48sDJGcZrnRU9vM8Lh42KsO4OKxrQcoNRdmdGHnGE05K6O/1rwIBC1xpr71H/LM9fwrihZSrOY2UqwOCCOldDpHi3ULXh2Mqe/WjUNSGp3iz+QkZxglerfWuCi8RTfJU1Xc9OpChVSnHRmK9iET5R0qoVwcV0YjDLwKzby1x8yiumnVu7M5a2HsrxM2lpcdqSug4Q6UtFFAC0opKWgAp6Rs/3VJ+lNqSGV4W3KcGk79Cla+o0qVOGBB96K1rbUoG+W6hBX1xmq+qPYDElrkLj5hWam3LlaNpUoqPMpFBmVAWY4A71QuLsudqHC/qaiuLlpG9B2HpUDNt6ferpjHuccp9EOZwo55J7VHlmOSaQDJyakyMVZkMwfWgE596U008/WmA8NmimZpQc0hpjqUUgpwFIpCYopSaMZoGJSgVLFA8hwqlj7Crsemyt97ag9+alySKUGykqeoq7DDtO5x9AauwWUcOD95vU0lwu2QH1FZOdzZQsR5yaU/WmZpw96RVx6nofQ1bXpVIGr8RzGvpipkVEMH0o5qUDpS4qLlWIcGjBrWg0W/ubfzoIfMT/ZYZ/Kq01nc25xNBJH/vKRUqpFuyZbpySu0Utp9KrS2aSROgjVSRgEL0rQ2mjaatSsQ43OXFlLJcPFGu4qT1OKsRaVdLKjMg2hgT81bscKxs7Dq7biTUmK0dVmSooiKntS4NS45pRj1rG5tYhwadipKMH1ouMYBS5JwKdjNGKQDea5nUbn7TdsQfkX5Vrfv5TDYyuMA42j8a5Ynmt6K6nPXl0FAFPVV6kD8qYCO9OzitzmHlIyPujP8AOo5I1VgFP4elPMnGBTIzlyT0HJpgx7MAwTP3V4+tOlmJQDP3hzxwKjOHG0/ePIPpTVIOA+fl9KZI/aA+COh5qzYRj+1BAxwJcx8+pHH64qDbucEPuLHk9MVZeOSOZbxUYRpKo3+/UfoKzm+htSWtztraKO3BukUq0lugH+1IwIY/gufzphWtC6CGxtdpyQ8v5ZFUwM8Y5ryYO6uz2qujsiML70bRUhQ5Ixg+hpMc1oZDAlLsHrUgX3pdo9aLhYi2Cl2D1qUIMdaUIKVx2IhGOtLsHapQnPWl2dOaLjsQhAMn1pyrtII6ipdmR1qSOLcwXPWpbKSLEMF3q8ixLmRl9egFQ3WmzWc5hnTa/atXRLgaZqKtL/q2+Umr3iK7tb2SPymDFerLXN7SUanKlob8t1d7nKeVjg9aPL9a0phEy9BnGBgVVK+9bqVzJxsRs8jQJCzkxxksqnsT1pvl1OqDqDzTgnvRewrFfy896PKHrVry6Tywe/6Ucw7FYw+4pUjKNuwCKseSD3pwiUj73v0ocgsYmoIRP5oUKG7CqQ4Nb17CogYMRjsfesE1rB3RlNWY4Ac5P4VZtJMTbQOGBH51Vz0I61LETuDDqOabWgR3NVEHepVQDmp44kZFYHhhkcVOtuD7/hXO5G6RVVRVlWLHlzzwxJJqUQgcUohwahtFq6K5iBY4Ix7DrThEas+VgZyMUoSlzDsQiPuana3aNgOoIyCO49atG3jNus0bZ/hdT1B9foaZywVSSQvAHpWfNcqxBtHJ6VS1i5+x6TcSg4crsX6nitPZ7Vyfi+6G6K0U/dG9/qen6fzrSlHmmkZ1ZcsGzlDkyjaenOaa7oDu2jGcA46/SlY7I2b14FV3O4BfwAr1krnlN2JBMzkKigHsTyaWSNwQJGyx7U2OQxdVp0khlbIGPfsBR1C6truRBQzVYQu/amxKPx+ldVovhR7pBPfb4Yj91Bwz+/sKirUjBXZdKm5PQ6Tw9pA0rTwJMG4lw0p9PQfhWyBk0iBVVV7AAfgKfxu46V4s5OTbZ6sUoqyAAdqljQtlkPzDnHrTFFSDIxjgj0rNjGhcnNOCjilAHrT0jLZxzgZP0pXAQDmpOopAvFSY6ZqGAmDinY6U9WIGOoIxz2pCKm4DCDS4pxGBnpQoBUk9qAGkUYJp2KccZxnI9aAKVtp1rZvM9tCsbTNucjv/AICrIWpAoOct9KAvam23uAwLmm7asoNmT1yCMUwp8u78Km4XK/SlJBUcYIGM+tSlMgDIyaYy4JGOnFO4EZHHt0qNj6Vacj7Kse35t5bPtjFQhOOvFUmFyEjIo28e1TeWAParQiXylwOMU3KwXM4p71GQc1ZmUo+wnioWX6VSYyIj3rA8SaOl7bm7QHzoUO7b/Evv9K6IL+NJj8R6etXGbi7oTSaszx91YMHU/N06dqhaVGwJYxkeldB4i0d9LvSUBNtKSYj6eq/hWGcMfmAbjo1exTmpK6OCpFp2KrLAf7yj6UKIQM+Yf++eakkSMPtCcYzwajxCOCjj8a2Tuc7VmK0yBSkQOCc7j1NBAGFHbr9acrW8RBAYt6MM0roAdw79M0BY63wrc+dYPbseYmyB7H/69bkmWOSeelcX4euvsupQ7jhJT5bfj0/Wu3Yd64K8bTud9CV4WK/ls5CjqTgVRnAE8g9GI/pWq0IMTHDk4yWxgL/jWVKq7iEJI/vetZxdzVor4HU9KfbqDcpnpmkI9BirenxKzuzAHbitG7IgsbKTbzkVa8tDQI1HOf0rLmKsVRGXcKByeBSopVseoxmrOxR909eOlNMXoKLhYheIx5GcA/rUbRAHqDkdjVyRFbHzscAAZFBiDR8AYTk8c8mhSBozzEPWn28cAuE88t5QOW2jkj0qcoo44qNlX2/KrvcmxFOElmd0RY0JyEHQD0qNUwDjGa0bma0ktraOGARyRqfMcnO81S98/pRF6AyHy+c55o2kDANSe+f0pPxqibkJjz1NIYx61Nj3pNo9aq4mVzEPWkMYqfaPWkKg96dybFcxjHaqd5bNcyW1rGMvcSiLj0NaRX61NZxRi4Nw4ybdGdPZj8o/9Co5uXUOXm0Oe8QyobpI4AVWMYVP7o6Afpn8awBtDEkfM3QetaeqSiS7mkVSqscIOuKzQyKWy37wjgf/AF+5ruoK0EefiXeoyHUGBaNVxtGSAPc0kb7VH0qG4bdPj0AFLu5rfocj3JzISOtRs5PemluMU0nigBrGmEZpxpKYFjTkV7+FHGVLiuu255rl9JGdUtv97+hrrdorlrvU7MMvdIguaULmpdo7Ucf5FYXOmxEUz060wripyoJzSgLghlJ9OaLjsVsUoTPep4oDNMsajljir9/Zw2SRqvMh5JzUuok1EqNNtORktGRgMOaYQKsvmQ5Y5pmxatMhpdCDHNG0VNtX2o2CncmxDt4603GOhNWPLXNSLalhnGKXMluNRb2KBFJirkkKpUO0VSdyXFogpMVMQKMCncggxRipsCk4p3AixQEJOAM+wqUKWOAOTWnGItNi8xsPcMOF9KiU+XbcuFPm1exjFSpIIwRTcmpnYySF26k5NMxVoze+hEfpSH6VNim4piM26tBgug+XuPSs10I610mKqzWUcoyvyt+hrSM7bmcoXMEikxVyezkiPK8eo6VWKkHmtlK5zyi0NB4waWkxR2piEJx9abS9TRimSOUt0XrVmICPnOWPU1XXK9KkD0DLIk5zuNQTru+YDDDv603dxRuz3pASW1yyD1A+8P61oo4dQynisXO18irVvP5T8n5D1qZRLhK2jNE0nX608KCM5yDRtFZGxGagm+9n1q1tFQXC9DQtwexWNIev4U4/rTTWhmJSrywHvSUA4OR2oEX880VHC29MnrmpQKg0QnailK80mKBhSUuPejbQA00venbacE5pXGkMxT1iLdKnhtmlcACtm304Iu5h+NY1KygdNHDOepjJaMexqT7MFxmtScpGMACqJJc+1ZKpKWp0OjGOhEIkUUoiU9uKk2YGWNNaTso4p3bDlSE8pR1pMKvQU3cc8mhmCLub8qeoXQO+0ZzVZplzzUcspY8mq5Naxp9zmqVtdCZ5yeBwKijhe4mEcYyzdBTakt5mt50lXqpzWlrLQx5uZ+8VGbA9aiJpT1pK2OYKkG1hjoaioosCY48HFTRpnk8CoB1FW14AGallRNbS0SRvLNdRb6EJFDD0ri7eUxSB17Gu/wDD2rxzxrGx+YcV5eN9pFc0T2sFKElyvcq3GjS26lkBx3FZU8YZSCOfSvR/LSaPsc1zetaPhTLCACO1cNDFXlaR2VaKa0OBuIdjnjiq/wCFadyMkqRyO1Z7DBr3Kcro8GtC0hn4UtFLWhiIPpS0uaXNIBOlLRmlI4zmgYmcDnt1rMu7nzGwp+QdPepby5/5ZKfqazycnNaQj1ZlUn0QhOPrTRyaOporUxHZxRmm0tAC5oNJS4pAJSClxRTAeOadnsKjHBq5a2xnfA+6PvN6VLdi4q+hHFA8rBVUk+1asGmIgDSncfQdKtQxJCm1BgfzqUYrnlNvY6Y00txFQIMKoA9AKcBS8euKPxrM1DHvVa4SQsTxtAqz2oIyCPWmnYT1M2g9qTocUZ/KtDMep9elXbRxtK8ZHSqI5+lSRyGJgR0B9KmSui4uzOk1CxW1W3ljO6OaMMD79xVHArbtnTUfC0iZHm2bb1z12msX3rlpSbTT3R01Uk011HxTSwsDFI6H/ZYitKLxFqUcZjeZZk/uzIGrKyKXNVKEZbolTlHZiyMZJGcgAsc4AwKZinZHWjIqiRNtLgd6ARTgRQAbcGk2/Snde9KPrQADgk4BzxTcc08AZ5pdvHU0hkeM0dKkKjHXmmsOO9FwMnXXxaRr/efp9BXO1u6+f3cA9zWEa66XwnHW+IKXpSUVqYik8UIcK/0ppNKn3GoEP4IP97+lITnDdx1+lAIYnHBFLnBz+BpiHxj06g5FdFfRmPw7PG2SRPAVBHIyjcVz8C/Pjvziu1t4Gl02ykl2mOVy4X/rmNoP5muSvLlaZ6GFgnCRcjZ/s0KSNuKL37E8n9acrD0+mKaPqKcMkfeArjsdl7iltxyQSfWgn/Z/SnlcHkgDHHvSDGPvDNIYgUZ6UpwCFIxn1qWEB5Qpbg/hWhbWST31vG/CPIFIzUSqKO5cYXMvAU8jipI/L8wEr8n0ro/E2mwWT27wbgJAQRuz06Vz43ADFRCoqkeZDasKI0Sb5x8nUcckUzbyeAPrU0QLMQ5Jz061M4UJx29qfNZ2Hy3VyqE/3aUIysCAKkB5APGfalY7GKlQfencViUMJIyrEe2Rio2ZR6flSBwD0HFG4Y4AqVEpyEJDdhj6U3Kg4wKcWAGSAAO9AnQ/dwR7GqJBdox0+lb2maZDd6e8wP71W6Y7VheapYZHHtWnptyInIUsueuD1rGtzcvumlO1x11ZII2IUBh0wKzigHBFdG6h1zjr1rKuIdjE4/Ss6VToy6kOqKG0dBRgVMSo6mmbh2A/Ot7mViC5thcwlQSrZyp9DXPXNrNbEeauN2cHOc11O5dw5HvWRr0m54EA4Ckirpyd7EzimrmL+NS7SGHIweRt70zGenWgdK6DI6HSZRJCYiRvT19K1EXjtj6Vy9oZS4eI7XU8H1rct9TZiFnTaBwzjoPr6Vy1I66HRB6GgqqRjGfwpwTPYjFKrIwykiOv94NxUgbGPu49jWFzSwwoBjGT+FLgZyRke9ShozjkfnTjtBDAgA+lK4EOQTgK1Lj/AGT+VShhngmn7xj7351NxkEjRqrOQURRuOewFeY6pdve3sszcF2Jx6Dt+ldx4q1IWul+SrfvLg7eD0Udf8K8+J3SZ79a7sJDTmOTEzu+UgnbLBeyjNQAbjTnO9yexOacg49/WvQ2RwPVjvTJLGnxxPNIqKrMzHAUDkn0FHCrk/8A667PwRYxf6ReSxkXCMFjLDhQRnI96xq1OSPMbU6fPKxLovhOK3CT6hh5Oogx8q/7x7n2rqxt4p6oz8hadkKMcsfYdK8ipVlN3kelCCirIaNme1PAT2qQEGMBYhnuSKUBiOIhWVyhoAHUCpAFxSr5hwfLAx06U4bupUdalgLiLaMAg9znrSqqjGKcqtx8oHenYcAHYBn1qLgKsO6NnwNq9aUAYAHb2pcOARsUDvU8QIXcVUipbERqq9yc/SkYL7/lVg5AHy/pSZI/h47cVNxXIOCCP4T7U1QB0qyck/dAowSeVzTuFyAIPQUbMHjH5VP0xkLgetJ5inIwp+houFyDbz0FSRKGkAPCk8mnqwHKqMU/JJyFGfpQ2DYx2y5YilkAVzsOR249acT6Ae/FBl3KAwXAHYUhFYqVYEDPPSmM7ljvC881fLxIN2FyFPBqmt0khVHibaeFYYOKaY02+hFnJwVAB46dKaV+bHBA6H1qx8uSCp4OD0p2AACgzxzxTuO5X2qx7DHFS+ZtXGOOwpQMchf60qjJ+6CfTFMRScbmJPeoynbP6VdcccIo9zTDGpGCFNUmO5VMZz2q21vbjSlkUgz7ufmphjjHGBSbEHpTeoMz72ygvrV7e5QPG3buD6j0Nec654dudLkJwZLZj8koH6H0NeqEDPCmqeoWMd/ZTWkm9UlXBZTgjnj9a6KNd035EzgpI8cJKFRkHb0OKY0pJy0Ubfhiuh1fw1f2DO/kNJCDxLGMgj1I7VgFcHB/lwa9aE4yV0cM4OOgwSQngxlf905/nSjymIXcQfpTGVd3HGe1M7Y7itLGV31JslOM4KnivR9GvIr7T47xyCVGHH+2Ov8AjXm2d6A9WXgj1rV0TVGsJ2jYk283Dr/Wsa9PnjpubUKnJLXY7O7upJ1VMkIe2etUZB1GKsLjaHUqynnIqI9K4o6aHc9RLixlt4IZZAAkq7lxU+k8SyjOPlHb3pJp/MsYYCvMbMQ2exxxTtLyLwBccqRyM0XfK7iaV9DS2DqSB+FL5Y/vj8qn8qUjI2fiCKYYpcZyij1ArLmHYh8sf3j+VHlZ/jAx7VKYpR/GMH8KYYW7uOe2adx2GiFcY3jNRt5Skjfhu/NP2Sxktw390E9PrUD+crmTahJ6g4poQgSJiSrfrSGEHvx9aU3bKAWhQAj+8KWKWSZ1CogXOGOegqrskiNuuMl8fQU0wLkfOT+FTXF1DBcPFwSpxndULahBjGPyaqV2S7DTAo/iP5U3yk/56fpSG+gPQ/mRUZ1C2PpntzVpMm6H+UnZx+VIYkH8Q+mKge7XnEgA9kzSCYsfv7R6tg07Mm6JWRccED8Kmj8lIGUsCW+9x+VVQ5Y8yKvuDkVKqR8bpN3vQ/MaI8RnPI/GnSFYdNupFPzEooIPvn+YFOY265w4+pNUNZuFj0Ubf+Wkxb8Av+NL4rIa01OP1CfdOwQ5OSoPr71VCBCB1bqT7VIgDSsTztQkVDM/DsO/Ar1oqyseNN80m2Vt25yx7nNOBqMHBp1aGQ8nimk5NGaSgANKOaQUopDRp6HGX1RGHRFZj+WK6vHTNY/h+28u2e4I+aQ4X6D/AOvWxx7A/WuKtK8jvoxtAcUCxhiRk9B7U3PtRnHTH50bz6A/jWRsHHpWhZ2ySQmQgMM4x0xVAvn+E0okcLjLAelTOLa0NKclF3aJLlUin/dHp0xUMkjyNuc5b1NOUM5ACsWJwAOprRPh/VjCZjp8uzGTkc0uaMLczB3lsZOOO1IeenH4U5sjgx8ioy5HVB+daoyYpH60Ypu989AaQyP/AHf1piJoyinJH6U97hQMKBVQyH+7+tN8w4Pymp5L7lKo0rIe7ljzUZAxSGTj7mfpQG3DiNh9a0SMm7hjg0mKXjuD+dGB6UCGmkOO4p38qTj0NMRLBMkO5tuX/hz2qF3MjlmOSaOKTApJK9xuTtYZSHFP4x0pODxVEjDSU7FIR9KYhtFLxRQAw9McGqdzZRuhZPlIycdjV7ANJ+HNNOwmrnNMmPpTcZOO1Xb2HyZiABtblfaqvCiuhO6OZxsyPbg1IkTHnHFKgywLV7f4S8OaE+jw3ECR3LOnzM3O0nqMdq5cZjFhoptXudGHwyq3bdrHh5TFMPFd14/0DTtGvI2sn2+bktCTnb/9auGatsPWVaCnHqZ16PspWEzRnikpK3OcD0pynK/Sm0A4NAGnYT7gYm6jlau1hoxjkDKeRyK2Y5BLGrjv+lYzVtTenK+g6op8bRzjnFS1XuZPl2DnufapRb2KvekNITmjJrQyEooooEXoVUICvcVKKq20nOw8g9KtDpUM1QY/OjFL3opDExS4pcU5VJ/Ck2NIRVBYCp0g3yhU554pqrj610GiaeZG8xhxXPWqqEbnXQo87sT6bpgSMMw9zUt5II12rWnMQibV4A4rKkjMr5615cZucuaR6/KoxtEyWjMr5NBi2jCjJrW+zBF6cntUcqxWsZkkxnsK6FVvojF0rasymg2rvkOB6VSkkXOF6UXd49xIefl7CoAQg3E12Qi7XZxTqK9kS/Ki72/Cqk0xdqSWYufaoSc1tGHVnLUq30QhOaXY2zfj5fWmmjccYycelanOKil2CjqTgVqT6R5Fp5rPlsZIrLRzGwZeoqxNfzzoFd/lHas5qbatsbUnTSfMtTLIxTalcYOKYfl+tbpnNKNmMpKcSSaSmSKKtKeAfWqoqaNht9xSY0WFIz1q5aXjW0qujYIrPDCnhhWcoqSszaFRxd0ekaR4gEsChjk96u3WqJLEQOteb2N61vMCD8vcV0a3AeMMp4rx62DUZ3R7lDFe0jruZWqf8fDMO5rPkeMxpjO8Z3VrX6h0z3rEf5W6V6NDWJ5uKVpMKOKYXHcYpA64/wDrV0HESil/KowynmlDLQA78aiuJvKjOCNxpzOqqSW6VlzymRz6U4xuTKVkRu25s0wntQeOKStjBhR3paSmIKWkpaBj49u75ulWWtcruibcKqU9ZGToSKhp9C4yWzQhUqcHrTSKcWJOSeaByaZOgAbvrU8f2hv3Shj7DirljaBMSyAZ/hHp71pBj6is5VLGsafUjtI5IrcLIxZuvXp7VZUqeCcVHkHuKeAB6Vi9ToWgu4CjevrRnA6il3DGRg0hhuX1FG8dyKblT2P4Cop2CwnA56c0WBspk5JPvQKSlzWhmKDxUiY71FT1bHtikNF21unttyB2EbjBwe3oasiUY6Vmq5J5+lSxysnAJZfT/CocS1LSxe81fal81c8AVWEgPIzj6U7cO/T1xU2HcseZzj5fzo8znqKhGG6P+lLjj7/NFh3Jt/P3h+VKH4+8DUHzY4YU8K+fvLj60WC5MHHtS7vQCocNn76ihmcf8tBj6UrDuT5OPuj86XP+7+dVwXI/1gx6kU7D5A8xD+FKw7k+T6iq1zdiEFVAaT+VP2yckOp/CsiVyZGJPzE5PaqirilKxV1FmkTcxJIbvWaTzWncHzImXPasomuqGxx1NxaKbmkqzIUmnJyrUzNOj6NQAHIOR1qVWDY9+tMAJOBSqNrketDBFu1AMyZ7MAa7qJw2j6UgwgS2Y9e7SMc/oK4SLhS3tXb386Wclva4J8m1iQ899uT/ADrhxGskj0sNpFkgfAz5hp2+PH3zWf8A2gij5Yzn/fpf7TG3iP8AWseVm3MjRkmRkXc+V7ACo96AdT+INVU1LAOUwD0warPeSM24tz9KFBjc0aXnlTlY2PerR1CYxDy1eNlYMSD37H2rAN3If4zS/bZvL8vzDtzmh0rhGrY6C71bUL/Z9olMmwYXIAqr5kxPIX65rKjknlcJHudj0CjJNI080bFWJBBwQe1JUktEN1G9WbAkuAfvD86leadmG1xtP+1WCLqUfxmlN1J/eNP2YlUN1vtIwcqAenzGpC7kBmdQT15NYiajMqBC25AchfepF1NgynYCAc4J61LpspVEbIkjIAZ8n86cTEqB9rlT1welZL6ou793CAP9rFWrLxB9mcgwKYm+8o71DhK10i1OJZF7FyqxKeOdxpReIuSIQMf3AKi1DWbSVozawbWH3js2g/hUY1tFXAhB9zikotq9gur7l0X0RAG2Q/VamivwpDFGHvtrOGvsOkQp3/CQPj/VLSdNvoUprudXZ36SLgnB9xT7hlI7EVzEPiKRDu8hSM1oJ4lMi48lQa5JUZRd0jpjNSVh00oRzwOvOKhNyucKufaoJtfk3EeQlR/258gOw7ieQBxit4xlbYybVyyLtcZ8kmsXWZ/OulUIVCIOD71pf22OpRyPoBWRqVw9zeea2RlQBn0rSnFp6kTehSwc+9X9O0i+1QSGzgMgjGW5xVI5JyavWGq32mpIlpO0ayffA71pUcuX3dyIpX1Id8kWYsFWVsH1Bq5YtGGzLJhe6knk1QLM8hdiSScknvUi9sGk1dFp6m1BdJDKfs25u5H8JP41sxXoyPOj2Hjqen6VzVnIsb/Mu5T2zW1azTzROofIOFyRkKDXJV0OqnHmRq7InGRkg9wBzTWNup8sFs/SkW3Fk0aFhtfhsHIJx+lTI6hdoRz6kL/nNYKV9hyhZiL5YHVj6ZxUVzPb28DzzyBIk5Z3H6fWrEYnYKI7aQ7jhcx9R/SvOfEV5cX+sTwtP/o0EpjjGRtXsT7nrzW1Gn7SVjGrPkVyjrWptqV887DCD5Y1P8Kjp+NZEso24UHJGCat3YCTkIoYYwCKpNG7HOeTXsQikkkeVUbbI15IGanXrgn61EUIGCozTlVunarepEdDb8PaO2r3+6RT9mhwZPf0X8a9Gt4Ut4VhihCRoPlByaxvAj3Y0eURQ2/lCYgOQdzHAz+VdcjXjKQVhHp8x/wrxsVVbm49EepQgowT7ldZWitShRxIx4x029+KSOFmheVRtKEZUjk59BV8SXP9yHHfLHinKJ+oWHJ6kA1ycxu2V0gac28UIQOyneT69f5CoQZif9UePQVpokyNlViU46heakVbjg7k46/L/wDXqOaxNzMDTLjCNt9SKmXzN3KvtHXataISY/xrg9toqzbWjyvhmByODjpUuYnNJXZkJ5oYDD4P+zRJK4k+VWC9vl5rbktHhYEsvI/u9ai8qbORICOuCKnnuJVE9UZfmeXx8+R2K9Kmin3KeoI5IIq/5cn95MfjQIpPb9aVw50UxIxOSGx0HSrO5mhVsEgEjPGKk8h/7qH6rSi3kP3dm3uMVNyXJEBYfWnjbkdfmHPy9KsiByMBUI9DTpIZoU3okeSNuDSbIc1sQNFGED44I4yOtQ7gBwvX26VYi89l2TRRbF+6BVRXuNxxEu3PT0FCZUeo8AYw2M+tWIEU4557cdKrs86E5jY88BQDTTNL3jkxj+7TbBptEjAFjuGf+A1FiM5AyP8AgNNa9coCQVPbPB/GmC9O0kyHjrladylFk4Vd4LrweOADmozCgY4jVV7EEA0+S7CRRu7Da/TC8kD+VDXgvL3y7cCNSOjLnoO9CYLmIzAqnIJ5HXGTSMgChmYfVhUL30pcowVduQeOlIly4YIoQ5zhieD+dO5ajIlAIJbzEIxwoQ0o+clSoAHO4jAFV4r0iRmkLCInCnGCKsR3CSL8hkxjHUCncHFopfaCzlVhGcdzUiCZ2AS3jGe9STSq7qYyQwB+ZRkinrM7Arsl/wB8LzTuN+hXMc4cjygMdwuc0o81V+ZUz3p/m9VKTZ9SopvmkMPlkA9cf/WqriGNvJyUUj2phGefIXPuRUhuQvVJCM4+7R55wdqOR7jvTuOxXIKnIix7iuA8Y6GLWb7fbQ4gkP72NR/q29R7H+dej+YzLxuH4f8A1qy9e0mPWtPW3adonR96OVJHuD7VtQq8k0+hM480bHjrDHGeKhJGa6DXPDdzo5V5SssDnassfTPoR2NYhjTPGfyr26c4yV0zzpwadiIMquChIHepn2owkT7p7ehqF1VSCufoafGyjKuflPtWj7kLsdDotxdRIkrMHtGbY/Gdh7Z+vY11/wDY128YkWMFDjBz61wmk3ctqxEFyysOQojLq3fBHpXpmh61ZaughnKw3nZB8wk91Pr7V5uK5ovmSO6jL3bGcNDvWBIReByCwzT4NEukl3CXyyP4hXTLaqH3kKQARjbjNVzZE/duB9Cori9uzo0MU6XqAG43ROPUmo30q+cljc5zz3xW2LFyPklB6cgCmPY3H3VnCj/c5pqqOxiNpmqADbckgdOSKiOn6wMFZiQO++tc2N2px9tfp/cBojs7yKTe029MH5GGBVKoLlMJrXVwSS7ZPo9Qvb6v33n6MK3DZXw4F0PxUUw2V/gfvozjpxWiqEuJzr22onrFIT+dMR9Rty4RZF3Da3y9q6M2V8ucOg568037LeDkmM/V6v2qJ5DlHE+eUb8qhZpB2I/CuuMN9saNhHsbGSD6e9Q7bleHtCRzyFBrRVUQ6bOTLv64/CgOwOS3HpXUNJHGQ0kDqevzQ00zaexOVQseuYqv2vkT7PzOZll3vlE2D0BzUZcjvXU4sHxhIgT/ALHWmtb2QYZiHPPABo9quwnTbOY8xhzWtY6vbwosV1EzRrk/JjOfetTUrWxjuAi2hAVQMquc+9UzaQkfLYzHjg4qXONSOqLjGVN3TMKW5Ms7bCFDEkZ6DmotbnP2SGNjlghJ+pNbx09NpWSF1XGTkAVyeryb5APQKPWt6VpSVuhjVvGLb6mWwycFsAj+VVpjkAZ96tSkHYRjOD0qpIcyH8q9FHkyI/Y8Ucg4pxFJyPpVEhmjqaSjpQIdU9rD586oThSfmPoKgXmus0vRwlkkpKM0o3Eg5wOwrKpNQWptSpubLkdxZoionCqAACO1PF7bjAXH5Uv9nhQSGXj2pPsqAchWI9TiuK8Wd9pIct7HkFfzIqQXi47kfSofJUDiNM/73/1qaUUdEQD2Josguy0LhSM4YduBS+eG6Zx74qrtfICwAgf7dIYs4/0X/wAfpWQ7s1tK1hNNvluTbLOEzhSQOa1dQ8fajeKyRxQwIePkOT+dcqEwfmt2/CSlwOMQD0+8KylQpylzSVyudjmuSzk7V5+lNM7/ANxTShUIwYWH/AhSFIic+U/vhhWysiHdiGZsfdX8+tMa56ACPPcFqUrAB/q5OnqKaRbZwUk/Sq0J1HCVmP3UA9d1NJLjDBf++qAYAPvSZ9yKQmHp5rg/TNACAFegGP8AfzUq20so3CNdvdiaak0MRLMS5HQEUyfUZZeNwCDooFHvPYdopXYj7lbG1fwNMLH+7/49UZuWJ5Xn1zTxOhOMnj2qrMzugLnHI/Wk3/7JH40eYh6N+OKNyt/HTEIX/wBkj8aTd6A/nS4Xs5oI9G/WmIbuz2NG7HbNOJb2prFlxwKAGFz6fpSbz6U4se/8qTcf8mmIbv8A8igsOwNLkg9qQucdvyoATcewFG71oLn1/SmmT3NMRUvoJJlUqM7c8DrWUyMeSOnGK3i2e5FUryE4MqdM5Yf1q4ytoRKN9TNBxirtnq17YZ+y3U0O7rscjNUm65pma0cVJWaM4zlB6Ms3V7PdymSeV5XPVmOTVUnNGaSqjFJWRMpuTuxKKKAxAIB69aozEpaSloAcDkfSrdlNsfYT8rdPrVIHBp4OMEVLV0VF2NZ5MDCn8R2qEuNu0dD196iWUug5570E1nY15rjCMGkpxpKogSiiloAcjbXBHY1fBzWdV6OTdGp74xUyLiSCnc00H2pw57VBogGaeoOaUdOlOUc9Khs1jEs2kBmnVB3NdzaQC3tlUdcc1g+HrPfJ5hHArqvL3HArx8bVvLlR7OFp8sbmdMpY4piwgcmr8sYBqvkE5/hFcylodVitKUgjMsnTsK5HUr9rmY8/LWlreob2Mat8ormZHyeTXqYSjpzM8zGV/soVpcdKiaQk8mm5p1wixS7VfeMA5r0UkjynJtDM0hNNJFJkVRncdmkzTSaQsKYrjsmkyc03cKTdRYLlrUBA1/O1tkwFyUyO1Un5OcYpyShS+4E5Uge1RliRiiMWlYqc1J3EpKKKsxFpQcU2loAfvPrSiQ+tR0opDuSiU1qafqJQ+W5+U1jinAkGonBSVmbUqsoSujqnYSIRng1i3atG/tTrO9IARzkVbnjE0eRXNFOnKzO6bVaF0Y5kb1/Sk81vX9KdNE0bYOaixXUrM86SadmP81vWkLk8UzmmSNsX3PSqsTcbNJngVXzxmlJyetNJyatKxk3cKKKKYhKDRRTABS0gpaAClzSUtIBRVm1h3tubhR696jt4xLJg9ucetX1ifHAGKiT6GkY31Jw5z9+nLI/98VCIn9BS+XJWWhtdlgSt/eH5U4P/ALWPwqt5UtOEco7/AK0rId2WQePvH64pQcd2qtsm/vfrQEnHQ/rSsO5aH1qK5HyDkdaYFnH/AOuhkmcYK8Dkc0WC+hDmlJBAwMetO8iX+7R5Ev8AcNULUZmlzTvIl/uGnfZ5f7lAajAaeJCTycD2oFvKf4P1pfs0v939aWgak64IysmKeJ8HDKD7qKri2m/uj86cLeb2/OpaRV2XU2uPlcflS7EB68/7tVUgmUkgL+dSBJgOq/nU2KuTbE7E/lSiJMdqgMUzHiRR+dN+zzn/AJbc/U0WC5a8pB2/SlCpjGOOveqy28458wf99GpBDMFGJAT9TSGh+IxzkD04NQyTJhlRQzHvtOanSF9+XdtvsRmtCO3twFIu2HHIwOKlySLjFyMTfO4wIn+qrUclvdSYzE59yOa0bqe4gm2o6SoeQR/KoBfTsdvlJnvVJvdEtLZmFfCWAiJ1KkjP4VQrZ1KCe7uo2CfeXHsMHvWdc2xtZzEzBiADke9dUGrHJUi7lfBNAXPWl70tWZCYApY/4qKE6tQBIgHJJHuDSEgyDHQGm0oHI+tAzQsovPmt4R1kkVfzNdBqdwLjVLqUHIMhC/QcD+VYui5/tGFhgmPLjPr2/Wtz+zxuPzN78Vx1WufU9Clfk0Ke4DGOtIG9Kv8A2FV/j/8AHaf9igUDMi575qOZF8jM7eTTvMbYV2g55zjkVcMUKHGR7ECmkoMc/SjmDlZTAcnhTTTkdauFhn5Tx9KN/GCy/iKLhylaKaSGRZI3ZXU5DKeRUxDSszvIpZuSSetDrCw/hU+xqSK1iZcmdVOelJtbjinsQmFyeNv4GnC1nI4jJ+la9xpkVqYy0uRIgYdaZHDtYeU+0epU1CqJq6LdOz1M77PPswYG9c4pvkTf88mrdQKMbpgT3+Wp1YD7sn6Gl7QfszmxbznpE35VKtldE/8AHvIfXiuhN1FGMPMR9Upw1K0BP+kE/RTSdSXYapruYC2F4R/qGp4028OMQn863f7Vs8gmdj/2zNOXV7Q8LLI4PUBKh1J9i1CPcqQeFL+4iSSKSAqRlgXwU+tMuPDWpWkqrJGrKf4lcc1r2niC2tZshiCwxhguMfSmT+JZLuUsYnY9FxHkY7Vjz1ubyNOSBn29hfW5OyNdp6q2GFPbS7gTboI2jQj7hycfSrY1O7dggspg3bCjmpkvb0hVks2z1wQRj6npSbluaK2xC+kmePH3Hx8pY1TbQrofdIY+xFbwu7xkbZBEuTxvwCB7VGsmpMFAWBW/i3Efpis41JIuUUzHOjSELtR1OOSzDn/CmyaLISDLKo44LNXQodQI/eSxA4/hyauRLeMPvIRjoUz+tDryXUPZo5BdFUkAXAP0FTLoAYgCUZ7g9a68CWNeSu4H+6AP5VYEMU8RZs7x2CjH16Vm8TIfs4o5KPw7A6D9+4kJ+6U/rU6eHAmMYft97rXSeR0AkcemF5/lSfYCSS0szEjnnH8hUOvJ9SuWKMNdBCEFoxtPQlxV2PSRBCThQSR0bORVwadjBJLsOm4GrP2QeTwQCDk5PGPoazlUb6lJpbGcwt4iskrAgdMknH0FSJPbsMxXC5zgLg4NWPLRMlm+X12ACsjUdctbYNFaPG8wX75Koqn15604py0QSl3J/EniU2elfYYZVF/Ou12zgRIerH39K84mt9PCNAt4jPxiaRSv1C1szQo4a5uPKupGb5i7Egn3boBWHeqChjidgpGSrnIb/d9K9LDwUFZHFVMi6jkt3ZA7Fc45qocn7xJNTyOwJQgjHG09qh716MdjzZ2voKuQeCc11XhXSrPU1vDeICqKqod5XDEk5HrwK5dBzXqPw3gC6RdzMBh7gD34X/69c+Lm4U20b4aN5amrps0WmWEVpbwwmKMYBI5bPUk1dOqt/DbQ/jn/AArU3IFJLfKB1NOTc6lkwQoycHt614Tnd3Z6ei6GN/bLkDEcKMc8MpOMfhUlvqdzMSGitsjnhjzWpuUnhhn6U3eOcMBjpxSuh3XYqxXl0T/x7wAdeGzU7T3gZR9k3KerKOB+nFPVgRlpMAd14pAVyCHIH+01SxadiaKSXJMiBfTbyfxp8d3dISACPbGc00SMMcgfgOalEzKOWGKhohryLT3Uk67dpUoeCeAaZE05cBTx1Jz0FMFyc8Hr/tU8XQETjJ3N1OB0qLWMuWyskK0wLsYwSvbcaaL1e+P++c0zzec8D34FKJj1P6Yp2HyrsH9q2/GWc/8AbM4p6atbbuGP4Rmm+cAMkkD6ClE2ejEfQUrCcI9iwupQuAUfIP8As4qQagCOCp46dKqecob/AFn6UGVAM7Qc/wCzRYj2cexaN93wMfSo/tAbn7oPtUBlOf8AVgfgKb5oPHljBHYUWGqaWyJxOmCfNAx1OKablAcCcZ9hUaspB/dYP5ZpSdqt1C4+hFMfKiQSjPEuc9eKXcCcZ/ArWSZNkm6S/HlMcbTgDI96kZkwsiThBjqhzuosX7M0jHGQQVX67KYLS3kONiAnvtxVBdu7Ek0hz2ZiMURNbGc7JGVxkbtx4/GiwuRrZl6TT7VBuO08YGMjNRfYLNiDtOB70kR2yh9rSkZwC3FIy5OS3llux5zQC5luxzWNoc/IuMdc0oYQfICmz3I49qrzJcRcrLGu44AEOc0kayMoJuASR0WIcGmVZtastCVSMhoRn0NOLYwQqkeucVVCLnc87H6KKcI7ZiQJZM98A0C5UTBxu9PoRQXAOAx59qgFvbkkZl98AgGlNtCy7T9oK467yKYWRNkDuAe9IWA6uox74qq2m2Rx8krDrzKetKtpZADaMD08w0DsiV5okxmROfc0xrm3VctOgB7s2Kb9js2ySgZe+ZDzSf2dZSkRm3hbHIBJI/nTK90w/E93pl34ev7f7RG8phYxgDJDDkYrxpyyt1Ir3x7HT9hV7aHY4KsFAyQeDXiOr2Tafql1ZMeYJGQH1APH6V6mXzWsTCula6M1nYjGc00etKeDQK9U4+pr2E/2do2jLZPAVerGt+3nN3cOGh+0Sg7mSNvLjiPbkdTXIwFjIse7YW4Le3pW7ZXTRReVA3kQr9+cLk/Qf41y1YdTsoyO4g8QzWcYGq/ZGxgNsch1+uetdJA8dxCksDQyRuMo6vkGvOEC26idhHakp81xeEPJJ6bQatad4je0J+xm5u9+DJGsAEcjdyPT8K86ph7q8TouegsuzIM0RXr0xSAqfn88flWZpevWeoSrbyG7tLxhgR3AAB9gelbRV0j2h3YY6YH864ZKUHaQrkDXMIX/AFikDhsrj9arm6gH8ceD0z3q2Ru3KDn/AGWC8YqqxL8RxRnI6nH8qIstJEJvIhndswP9oc0w3tts5ljH0NNdlPP7pQO6xjr+VRMrnhMEEdSgrZWKsEur2cLZaZc9c4JNV38Q2eOHyD38uhxMpyZXUEdoxj65xTGLh8G4ULjjbFyP6Vokgshkmu25j4BJ/wBmM1WbWBxiGUg9wuKmdpck/b41A6fJiq5a46i9U8dN3etIpCYw6lcSEhbaUHvlCcU7zr6QgfY3wfVB/WlLXQ6SxE/75pvmXDEZMY57OTmtCSM2N3M2cGPPYRgVNa6XcNKFFy+R2Kj/AApp3EfNDnPdWP8AkVc0xoWuTmHBzj77VE5NRHGN2XbjS7xkBFyuQO69qxrmO7gba4Q++8iuslZI4uMAYz1NctfXgadlbIUerDH5kVhQnJsuWxk3s220lJVyNh2tuUgGuD1F83T88BsdfwrudYkzZYjOY2IAAAwD1rz6di8p55JzXs4RdTzcY9LEJI+8OwqrnJyanlbEf1qAda9BHlyFooopiE2g0m2n1La2sl5cx28Qy7nApXsNRvoJHZ3DhCsEhEhwh28H8a9C0+BbTT4LfccxrgkL36n9ahtrS6gt0gjCrHGAoA5/GnN9uTjy8n0C5rgq1faaHo0aSp6lsjngn/vmomGR05/3ahaadACyOfYRUfapNhIQnnHCHNZJGzY5gCOQ4P8Au1G6q3JVs+oFKZ5gPvIfbp/OoZr9YWAk5z0GapJkOwCNo92zkE5+7S+cRxkfQLVY6nFnowx/tCj+0IGUne4Y9sg1fKyOZFj7Q2zJK8dttKboggEjJ/2aovfR7vkkYfUCk+3HHDL9NvSnyi5i99oPXK4/3ab9pJHVePQVSW6aQ4OcnsEp4MhwPKfn/ZxRyhzFn7SSCcnA9Kia9RcjnI7k4FQtHIcDb054FQm0nLcLkk+tNJCbfQke9feAijP4EGla7woDDDHp2/GmCxnC7mCg9hnk077E5TdI43emM8U/dF7wi3LPLtBxn/ZzU+B0yDj2FRiCSP8A1eB655zSbJ+T8pH0xQL1Jc9vl/75FJuwOAv5VCfP6YWmlbgjBOPoKdhXJ92P7v5U0uO7KPqKqtFcE/639OKj+ySbiWk59adkS2y4ZI/76UwyxDPI9+Kri3kBzuBpPszb+vB96dkK7JhdRK2ev4cUhuc8k8egFRG155cg/SlEQUY8wAd/lp2QrsXz1OCSw/ClEqsPvUwxw9Nx/KjbDjucd89KNA1JVO7o2KNuejfkagk2u4O5jjngUhXOMMw/4DRYLljavc/rSYHoKrlW6+aQPpSDeDxcL+IosFywQPQUhCjsPyqFXl5wytjqO9KWfj5gD3GaLBco3lntzJEPl6lfSs4it0sx/iOfpVS4s/MyyYDd+wNaxl3M5RvsZdFPkjaNtrqVPoaZitTBiGkFLSUxBS0UUAFOHp602lpDJEba386mzVcHIq3bbXG0gZHP1qWXEaTkYxSVb8gc8LR9nXrgVNyuVlSirf2denFH2cego5kHKypUiSugwDx6VP8AZx7UfZx6CldD5WME757VNHI3WkW3GR0qzHbAiok0bU4tsi81vWrFqrzSqo7mnLZ5NdT4f0T5hK4rlr14043O2hQlOWpsaRZmC0UAfMRWsIhFGWc1KixwRjGKoX1wdh54r55ydSVz2ForIpXV1ufavrWfqN39ntSAfmIp6NulLVz+vXW6QoDwK76FK8lEyrVOWDZi3l0ZJDzVFpD609wSc1EUNe7CKSsfPVZuTuNLk03cacUNNKmrRi7ibj60m4+tLtNJg0yQ3Gk3GjFJimAbqMmkwaKACl4pKKYhaKSlzQAuaM0maMn0pAOyaXJpmTS7vpQA/NLu9qj3e4pd3vRYdyUPg54q7bXoTCseKzg/vSh8dKiUFLc0hUcXdGzKEmTIxWbIu1sU1Lkp9KJJg1TCLjoaVKkZq/UaSAMk8CqMjl3JNSzykjb+dVya3ijkkxD6UUd6KogKSlpKACiilHSgBKKXFWIrYsAzDjsKG7AlcijieU4UfjVwWaeUQW+Y96eEkAwMAegpwSTuazcjRRQttbiFic7mPGcVcX05/Kqyo2R8x/KrIQr83JrOTN6aFwO54qMuoPWlPOePwpu1f7o/KkhslEisnDCm+eoP3hQgA7AfhQyjd0FAO9rgLlB0b9KX7Un979Kbt9P5UAEDgD8qdkTdjhdp/epRdR+uce1NG7+6Pyp3PXav5UrId2IbodQAB70gvFxkrke1O25/gU/hSgY6IoHoKNAuwF3GTjkfWnfa4+zCk2gnlBR5KH/lmKWgajxdRnHzD86eLhP7wH41AbZWHI4o+z8/ePNFkO7LP2hSfv8A8qd5o6Bv0ql9nkHRxj3FOFrKWxuBP40rId2XPNBHB6UeepPBH5VVNtKvUqPxNIYpuzD8DRZBdl0SjHDDH0p3mj++azSs6DLbvw5pPMbGQ2fwo5Q5jUDj++SaUFTnLdfas1HfBOQAKerOc4k79qXKNSNDdH3/APQaUND/AJWqYz1LkjvipFODjg/U1PKUpFklcfdB+vFM3KeqoPYnrUWXGAMHvg0HzePlPT0FFh3JSsHdc+vFYWsoq3alBgFBWxmXbjnPWsjWQ/nQlxj5T396un8RnV+Ey6KD1pK6jkFoTq1NpY+poAkxwKQck/WlHQ5pF6fjQBt6Im6R225yQv4df8K3hGfVV9MsaxdGUmM/Ps4zkd+a1vIkB3CUFvXJNcNT4j0KWkUT+Qp6yoM+ppPKtwSGuFB9Aarm0LZMkozjgsM0otFUZDIx98VFvM0v5FlYbVukufcVILS2zgs5qGGI7eWZSD6/0qTYcH55D+FSykSiytsfdB/WpFs7Yc+Wn/fOaqiI5J82Qe2KcLaRiB5zDtytS/UpehdS2iXO1U/74FTm3RT0UfVaqpp0w585sDtjGKJLR2AxOUx3GTn86yck3udCg0r2LjKpwGm7cDrTGEaY+cEkYxt61mtb3Icqbp9vqFxmkFq4HLlvwq1FdzJyfYvSTQwpuklVAPQAn9KkiAuUDwyvID/dOMfX0rK/s5zg7mGOygVELe+0+YS253dvl7/UU+VdGTztbo6FLWRlwXI4xjdQbGJhhkJX6n+lc+uvXqtiWPcScAMCuPwqT/hIJsH92Bj0zwfep9nMpVYG8umWYyAnFSR6bZITsgjXjHINYEWr3UwJBGMA5xwK0op7xhu85FQ4OGYHFRKMluzWMovZGulrCgG2OIdOkYqVcfdV1+gUdazWuF+zBVb9+Dy5IIIpn2h8YLxP3+b/AOtWPK2a3SNYHkDzMnHpSiOMdZFAHtnNZC3D55mRcf3EJ4qzHcHd/r5DzjISk4MakjUQKoGSSPYAcVIhUDv7VRWbnO5jx6CrKyOH2gk8ZyMVlJGiLkUwU4iY/MMHvV20uPJiIA+cnIYoTgVmRyuQCqPjHUEZqzE8jMdgIOOd2RWE0XZNFyYv5oYBiCOSVxSDzB/y0YfoKYWbgzOoBGAKn8gokbts2uvBNZXSFsNJYn724DsDTvKwcAjnnlzmoleVSFDBF9sCrYAYea20/wDAeDQ2S9CELKNoWYqX4HzAg1Mkv2JXknliMSA+a0n3R71G8TGT5HAIGMhc4rkPE+s200gtXH2sROTtBwrPjAHHXH5VVODqSsiZarUfrHje2uPMt9Ol2o4KvP5BJbPBC46fWuaSS1xmOK1kZeTui2vj2DdangkNqZJpiC8iZOOAn+79Kr3RTVGUPGwQL+63HBA7sT/IV6lOnGGkdjFt2K1zBFK0v2dWtDwDECdrn0xWRPOXYpLGY5hx7Gr93DJZLtjnM8R6K33h9DWZdSm5QNySO/f8a66aOWo/vKsrlz83X1qHFOzzRkHiulaHI9R6cV6/4ZtF03Qba3kz5xBlcbsYLc/yxXklrGZLiNB3YZ9hXejxBOVxI2VxwABiuHGxlNKKO3CWV2zuEmTlPMc5HruqWFkiBQFxuGH5xke9cdF4oKgkgcn7oQD9amTxKjFceUmeCSM4+teW6EzuvFnWK1vsC4BJPABzTxJbbgVC8f7BrnRr8SyqizwupH31G0frUza9F52xJVlz3QZAqHSl2CyN4vExDBMg5OSvNKs6L83lt9Auawhr0LZOC2OMqvcUn9vxjbiN/Q8cAfWl7OQuU3TdQoPukAf7NCX284hUO2OuRWE3iKNBuCsR+ApZjcahbfaFBhI+ZRJ0f8vWl7NrcfKjba9kTI2Bm/uBgD+OacL59gZomXPUBQcVz0d1cRIzSy28Sk58tjnA+tV31pi53XdoFU9VBxj0o9k2DgjrWu4wCQw2j1Xmq0utW8ZOzMp7KFHJrk38RRxSYaR5s56YC4pG8YQxD5AM+gGKpYeb6C5YLc6WXXLlDlNNkKAZznBIqJNav7nJi03ag6mWTBA+nc1zY8Zlidlv27uQKafFyu4L2oOO5k/lV/V5dh+4dL/bF6/H2Bd5GcNkZH+NOttUur0HZaxRlCdyuGH61y48WwoSyWbBj/01NKfGrDH+jZwOP3ho+ry7CbgdcDqEnKtYKp/6ZMxH51Mi3OSpuoAp/hWLGP1rhm8azbiUtYRn1YmoW8ZX2PlWEf8AAc0fVaj6EuUT0IRMv3r1sHPTApPs1uzbjczO3fL4yK82bxbqRJKzKmf7qAVC/ibUn63rj6cVSwcxc67np629gDkRxuR/f+Y1N59smCGiXsMAV5G2u3rDm7kP1NRHVbg9Zc/hVfUpdxOUe56+dQs1PzXEfPHLCmNqVhyrTR+43V5F/a9yBgSDHsBTTqlywwZT+VP6k+4uaB64NU06I7xcop9QxpY7ywnYGOZH3ds5ryE6pcHrKaRb2YtlT83qBzR9RfcfPE9lZ0lBQTsykfdxgj6HtUTTQJIsH2oLIw4TzQSffHevJ21W/t3MbyOGGMgtmhdcuUbcGUN6gDNT9Sl3Dmij0+W3Z3LHU5wOmEKj+VBtA2P9MuRgAcP1+vrXna+KboDCykeuFxSnxLeMh/evyPWj6rUL54noRiaIf8f0+B/ewRSgysRsukcL1DL1/XivNv7evVGBKefUZph1i5dwzPyPTin9UkHPE9TSdB9/ycj+6c/pT/tEHDsYgOxIA5rzi1vb66zFCryMVJIRecCq51SWNduQcdPasvqzbsW4q1z1L7Ui5DmIBuACcbqUzxs/lfLuI+7jFeYxeKLqAY4c84LnOKavim6SJkGzDdSf5U/qdQj3O56hmPzdh4bHyrtwDXmnxE0d4NU/tWMZt7rAYj+GQDBB+oGagm8WXcqIGKfJ0zk/lWdf69d39q1tPMzQkg7AMDI6V04bD1Kc1IyqOLVrnOkZNAp7xkt8oOKTYy9QRXrXOCzuWLeNJGIckcZwByfatSGZpHSKFdrp1Yj5UX6dzWVG5RWAxk98VYjkIXbnHOT7/WsZq50U3Y1xbR2kwuGVrqIDa7S87D6j2roLSZFaeBlG2aPYMrwB6g+tcqmozjg42cjbjjFT2t9KisisCqj5BIfu/SuWpCTWp1wnFG7Do8DK6tJPG+AyyBiQcV6J4flN/pCGXc9zCfJmwc5I6H8Rg15ausYg8qKXaQcjIznjt6V6D8OWmlstQknQqryJskbKl+PevPxUZcl5CxDShdHQm3RMMwI/CkazUxgNggjIbAyKnllaLjgjPzYGRVVJlmlMaHaB2FeapMwi5tXM6eBYnO0AA/7PaqTQwjIETfhkH+dXb6VlGchVXjJTrWNPqzpuYT2+0HGWibmuyleSOuN7XZKQidDIfXMhprSoDjBx7vVQauk+dpib12bv60037HA32+09CST+ldCiyiw06jJA/wC+mGKhaVD2UE9MN1qnJqeDwYzg44QnP+FQnVJTkgORjosf65NaKDFcuvJH3iX/AL6qOWaBPmeMjngrnP4VV/tRgmdkuccqsOaqtrF3z/oTkHoWB/PFWoNktouO6kb0SUjH3R1P51Np2pwLOyFyspI2oyYIrB8zUZXLxW+zjIO0jJ9OaniF3H96HfK/Leac7aqVNNWYoy1udVfazD5JCzcjqMY/U1iGYSHL/OhGcEZH41UdLuRgHEB46q+O3vUL2Ery72O52wBsIH8qinSjBWKlK+yKHiOW3t4AkCqPkLNtPGTwP61w7nn3xitvX7syzMhYtztBPXArE3jj3Nevh4csDycVPmlYrzn5gvpUY/WldsuTTfcV1o4HuPBzS1Hmng8ZoBC5zXV+FrEJG99IBl/kjz6dzXN2No99dx28fVzyfQdzXarYSpEscdxtRVCqpXoK5sROy5e514aF3zGllc43fnxRzuO1nOPTBrMWzljZQbpic88Y4pWhlzgSs+eck4xXHyrud132NEySIRgdf71PaG58oStFJsIzkDoKoCSaI/uzGo6DPJH41Exv5Q2LklT94c80uUHIvfMwz6+ozTCqn7wTj1ArLMV3nlgADngEc+tO3Xp+UnA9SoxWnL5mTl5F8xRN/DEf+AimNDGBkQxEeuBVJhdDrOnT+5TFE+4kyIT65/pT5fMXN5F9kj28iIfgDTNqZ6RY9gKolrkn5o1wPbOahna7Y4WIYX8PyqlHzJcvI0y6rxkdOxAphljJ5kGfTdWURfBQz5XHGDio2kug2UVxkdl61Sh5k8/kbBlj7S8+1J5oHPmMKxftNyD9+QN04Shry5ypDy5B6N/On7MXtEbkQNxKI4f3jH0NaMmkraRCW+uUiz0QHJNc5a6ze2WWgOHbuF5FQz3t7O7SSF2c9SVrJ05t72RqqlNRva7NGSZTkLwO1RGVeSWXPYGsrz52J3FwP93Apn7xmBBkJ9c1uoWOd1LmhNcMm1gqgE4P/wBanLcKVDAj3+tUPKeNhJJlgOT3qyJQgwo2LnkdOadkJNlgTrn74P1o89e7rn2NRAxS8sFDfSl2Rg/dH5UrILjvNjxkt+O6mmaI9XA/GgpH/dH40bE/ur+VGgDfPjH8YpDcL0Uj9KdsTsg/Kk2qOgA/AU9BajTcpnlvyo85D91x+ApSF/2fypML2x+VAagztnjP1qSC3lumKxknHUk4xUJA7Y596TBH3SR9DQ720BNX1ND7JZW//Hzd7m/uRjP61XuZrNhtgt8Y/ic8mqrKT/E350mxh0dvoaSh1bLdTSyQ7C4xtGPrSbUHYj9ab+8HcH6igls9B+dXYyuOyvTJ4pNq478+lN+c9/rxSfOPf8KLBcSSGOQYfJ+pqjPYbQzRsCBzg1eyR2P5UhbPGB+VUm0JpMwyMHFArSntUlfcG2568VSmgaFsHkHoa1UkzFxaIqKWkpki0UUvagBAcHNSxuY3DCoqcD2oY0a6gMAQxwaXYeu79KqWk4A8tj9Kth1J+9WLVjdNNDtp7N+lIVbPUUhcA43c0b1z1FSMXa2f4aXa3oKQOCcAigkeo/CgZIik+lXreNiBmqcYBI5/I1u6dACRXPWnyo7cNT5mWdN01ppAz/dFdXC6QqEjA44rNQ+UgC8Ves4y3zHpXiV5uerPYhBQRbDZGTWVqEw9a0Zm2pWJcjzJcdqzox1uUyB5VhtmcntXG31x5szEmtvWrsKvlK3ArmH+Yn5iTXtYSnZczPLxtX7KGM4z1phf2p/A+tIT9a70eUxhf2ppapDTTVEsj3UhY0+m0yRu4+tJkmnUYFAWGUmafgUYFO4rEYpcUlL3piDFLigClxSHYTFGBS0UAJgUuB6UUUCDAFLSZpetABS5pM0UALQWVRkmo3faOOtQsSx5600hNjWbLEnvTTSmkqyAopKWgQUUUUAFORCxwBzSohc4FXEjRFwM59aTdikrleeJYyu0kgjv696swMTEvT0oMUbdc/nUixqi4RuOuDUN6FpajsmjNN5/vUZb1NIZIDzViGYDhuQfWquT604H3qZK5cJNMtvECNynIqLA9RT4ZiDgnIqSSIfeXvWd7aM35VJXRGoGe1KQOuKTp2pc85wDTJtpYT86Wo2zu4JApu5x/FVGb0J6UVAJG9f0pQ7E9efpRYLk9Oye1RJJuHXmk80ZxuOe/HSkO5MGOOlLk9KhD/8ATUfjThJ/tj8KLBclBH40uc9AKj3j/noBR5qDq4zSsO5Kc+2KVWKMGBOfaofOQEjeBj0pPNB/j4pWC5c80H7+MdKjLR5+Rl+hNUHnjVuOT7jrUZmLNlFbHf3pqAOoaRbGPmANRMyDJYg+h6VUzJuxu2+5FG5UYM4J5wcjinyi5iyAm7jJP0zUoLd8qO2DUazJ03c08MMjikNMepUHPH4mpBLk5/lUW9c+lG4AcE49hU2KuTBj6igtjjIJ+lRb/rS+Yff8qLDuPL9+PyrI1o5kg/3T/Ord3ei2jBxuYnAFYt1dyXbAuFG0YAArSnF3uZVJq1iFiM03dSHij8K6DmDtntT4+/0pmKfH3oBD+Tn0zQOBSk4GMdaVBudR6mkNHR6QDHbsQAeQOR7f/XrT3ngfqFrP0/5bUfMRlicCrg5ONzflXDPVnoR0RLuHTJ/Kjcuep/KmY5+8aXIBxuP5VNirjwRk/M/PvS4UDgsM+9Myo53c/SnBxjrSsVcdjJ4LHPq1WofkkRt4wRnk5Aqp5nPBBpwlwR0GPaokm0XCSTN3zzs+Vl5HYmoJOVJLEn2bFZwvBgAvn0waje9jJzvHvk1gqLTOuWIi0WnK7wSTg8/epPMXGA7Z7c1Se7gA+aVfrkGoze2ijaZY/r6V0KDORzVzR8xRyWH4ml8xSM5zx2rLE4ORFdIy9hnmnC6ij+d5NwA+6M/yo5Bc5pP5cn+sXPoT1/8ArVWms7aTLea4YZOeuKqfbJnyIrVwOuT6fjSg3jNuYxxnHGDijlaFzJkclpcwkGK5ZwemODj0xTUub5MjdkA461I1jJM3725Ckd0yf5046dC5Um9lyBjgDmruuotehP8A2lcQqpmhiZs8sT/QVcg1WF0GUVHxlgBz+dZ40223B/PnZsewo/su1z9+cH6g1m4wZopTRrJqlnjKylQfVsVahubeTPlzM+Bltsma559MtyQRNOCOucU3+yYAQRcTj0wBUulF9S1Vkuh1zX9nblB9ptpCeGGfu06TWLNXQxyKPl7LkE1xj6S4BeG6O7uHXioZ7q+tWGSiALjKHis/qsX1L+tSW6O6TXQJR5MOQRzxj8auLryGUEySRxlgMyDj3rg9M1K4v9RgtXulgErhGlc4C+5r0zVX0HwxoTSbIbqeRdse9g7St6+w71y4ilGElG12zanibq5WOoxyYMbGXsdp6e1dJo95/aEKoHH7nAO9eSK8ih8RMVbfJNFnqExjFXYdfuRKrWd/gEEFZWA+tZ1cDJqyHKtCorHq17DDHbzXJZDg4+TnBqgk3mMVedsgcKRg1wtte6jOzI8gFvI37zyW++R9KmkvJgmySeYhSQATj/8AXWMcJJe62XBJRu3c7S/WWHSrwxCQuYXKqMcnbXiovNjjIbjjHQ//AFq7UahN5exJ5tp4IVyDVG6tbe8I86DzDjhjgEfiK7cLD2V1LW5jU12Zytxe+ayH5sL1BNJJqLtjGfclupreOg6dn5llXj/noaYdC03Od0uP9+u1VIHO41DmnuJH43HHWoQxUjHfqK7OPQ9LjLFoi/HA3EkVd/s/SI2Dx2x3YxsKArQ8RFaJAsPKWrZ5+YWbLAELQIvU16E9taMOFjUH+HyOBVY6Lp8xBUyD+8VXP5ULFd0DwvZnEqNnKnH0p4kb1rp59BjU/u/MYdiU6+lU30dwM+W+PaPNWqsWZujKJjrcSD+M08XMn981ak0uUH5YZv8Avg81WOn3ZPEEpA/2DVXiyffQfa5P75NOF5KvIcj6HFRmxu1XJt5QPdcVGYLhesUg/Cjlixc80Wvt0/8Az1apl1e6ChfOP5VmbZP7rD2xRtk7q/5Gh04sFVmjVOsXX/PwwPsKa+rXUnL3UpPuxrMw46K5/Cj952RvyNL2UOw/bTL5vpH6zt+LUn2pj1laqO2TtG//AHyaXbL2jfP0NP2cQ9rItmcd3JoFwB0b9Kp4lHVG/wC+TR+8/un8qfIhe1Zd+1Z/i/Sk+0/7VUiW7g/lSEv7/lR7NB7Vl37R/tUfaP8AaNUct6H8qTLD1/Kj2aF7Vl77QP71H2gf3qo7m/yKMtT9mhe1Zd+0f7VH2j35qnuc8HP1xQGb1/SjkQe0Zc88+tBm96qCQjuc0eb7H8aOQPaFrzc/xUebz1NVfNPYUecQfu0cge0LJkJ7mnR3EkTh43KsOhHWqn2gDqCKPPH4e4o5A9p5lrzCTktzT0l2OGIVsHOGGQao/aM8AAn6UvmyE8J+lHINVS27BgdvX0FMW4aPjOV9DUAaVh049MUBJCfmBA9M0ci6j9o+hcS4V8A5H8qmSVOPnANZmyUAgAgHqKUB152D8al00ylWa3PWfBuoaTpOjXOoT3MRuSCpQnDBR0AHvXA310JrqWQKI1diwVegyelY3z+o/Glw33twxXPTwihNzve5tLE3WiLZk3nhhRgnqRz6VVzJt+8OehxT4/NI67Se9dHLYw9pdluOAueoAPfBq/BpaumXkcOR8iKmd349qrwQagF85IxIo9SP5VIJb1XUyQsPdcGsZcz2Z0QcVuidrBbeQCSNh3AkGM1bFnFcSbo7e1hz0TJx+FCX0eVE4kJAwQ6f41pWOp21oT5QX96MMZE3H8PSsJOdvM3i4C2fhq2l+W4tSJPYcYq1J4X0hMEKoJ6Kzk59sULqcLyAyTK20YBIOcfWnf2pCVCJJlR0OQP19K537Vvc2vT7DhoOjyuwjs7ePA/iY496lj0TThhorSyfH3tpzj86ge/syoH2ol2zkMwxn8KRdUjhUKlypB4OxQQP8+9S41H1Yc0F0Ny0igtlBSC1PAOFQcYrTl1dVt4oQCyFdxxg4I7YrjxqMGA3muzAdSnTn2ps2uwzcluR/GWKk1jLDSk9Rt03udnaX32pymJST/eXFXZfsyW8h+aPjOc4rz+28QCHLyTo6qcrljnNR3OuvqbBWuZZAB91V61jLAz5r7Im0W9GdNJqdkyuv27kjoT1x71kSapYRrl7qJR6hixNYlzLGY2UM+4fLhiBj1rGlBhcBiApB4yMceldtHDIqpNQ2Oqk1RJZGECs+MfM3A/LrT1CyfemlPGeIwgH9a5ixCyM08kpRR024D+/4Vq/2pHGNmHCjke4A6mtZUraIzVRPVmoFSNQFHHU/LkfjT5ZI2ijKEhySGHQVmRawkgzEjOMZJDZx+dSvfygcY+g4qPZyuUpxsTmR+MCQL6jpTd0vBVRjsTnmq4vGYfNIEHUZk7ULqSxg7JTIcYyTn9DVcrFzIthzICJmICjIKiqrOx6A9PSomuS/wAogJ57HaBULTgfKzeWR1y+aaixSmibzXQ55A7hhxVLUdS+y2xkAjyThWxjafUU6a7Cxs4nUgD+tYms3Kxa+nmoHiijGxG5GeSM+1dFKlzS1OatV5I6GBdu0sxkYYJ6A+lVWYbSR2FW7p2luZJDyzkk/WqMuAnHQ9K9OK6Hkyd3cixmkIx0pegBpcgirMhn6U4E0HGaRQS21QSTwBTA6TwvGh+0yAjzAAuNucA//qrpBkthSSfTFc54dgng+0M8TruCgZHXGa3BJJHyBg/7tefXV5ux6VB2grkz5RsBCT9cU0PMOy8+xNRGV2bOHJ+mKb5jdN315rNRNXItB4yhYsVcdAq9ahYsejP+dR7XPQn8uKaY26s3/fOaaiJyuScg/eekyrAZJ49RUeT6MfpmkMgA5U59TinYi4pdAcHB/EijzM8ZyOxJBo3owwXA+opA4PQJx3AqrCuKWHHzOM+mKYZtuP33J45NKJip5VfwoMiY6f8A1qLCuM88fwyZ9wP603zt3Jzj2JFSFlx2FMZ1XncKYrjTIvZj9ab5vzAgE+hpftEYGGkAphvEPAlB9aqzFdDzcFezEewqNrhs9HHf1ppulALFxjvimf2hCM/vensaaiS5LuPM+ecMfqKaZU4yD+AqJtTgTP7w8exqI6lD/CN3rhapRfYnmXcsMYiM7SfwqIiNgAC49OKgbVACNqfnUZ1GZzhE69OKaiyXNE7KIV4YH0yO1Il0FAXAKnmq5Sd/nk3k+m3NQkOhztb8sVSRLkagmU4O5QDzml3A87hj61mcg52sSOTxT0cyDHmDd6daOUOYv5P1H1oyfUVU3+X17+lKLj1Ug+4pWC5Y3euc/Sgn/OKgWdTx09yMUedyeVyO1FguTZ+lJnPXrUfnDHUZ9hSlvbiiw7j+B14pPxpu4eppC340WFcfn3pGYM2cfhimliKQsfWnYLi49gKTA9f1pN3vSZPrQA7p/EfzpvI6MaTPoaTPFAXFOfr+FRuFdCrDI9Ks2s0aMyNna/BPanmzYMSXAT1A7Uuaz1KUbrQxJoGjORkp2OKhrflNqsbRqhkYjBY1izQmJv8AZPQ1rCdzKcOXYhpaSlqzIKWgUUDHA4ORV+GRZV5IDDrWfTlJBBB5FS1cuLsagVcDmkKr/eqCGYuQHznsasKGb6e9ZPQ2WuwBQepxT1jUn+KnKnq2akBA6YqHI1jDuSwRrvHWun0yMY6muYhYeYOa63SR+6z7VwYtvlPTwiXQvKm5hmtW2ULFVCMfMK0YT8ntXkVGd7ILjgYzWHqFwsETN3NbF02M1xus3O9yoPArowtPmlYzqz5Y3MS8mM0pJIqoRnpipiuTThCAMmvdi1FWPEknN3KhXimHNTyHnNQsa0TMJKwzn3pDTzyuajJ4q0ZtCcUlPCEqDyc+lIVOeh/Ki4rCBSTinbNvJNKpCjjr600sSaLjskBFNNODYppOTQDI6kjTc2KZirNqAXFOTsrihG8rFiKz3L0olsyB0rXt0GwUssYIri9s7nqfVo8pzboVPNR1pXcODkCs9hg11wlzI86rT5HYZmjNBpM1ZiLmjNNzRmmIdmgt3JphNRs2aLCuDtuamUUVRAdaKSlpgJiilpcUBYbS0uKcIyQDxQFieEr5Yx+NS5HrVZFZenenfN71DRSZYyBSg57mq2W9/wAaXc46nFKw7lnIzwTShuetVN7e9Lub3osFy2G96cD71TG8nofxqURkrySD9aTRSZaU89atxSfIVJrNWI5+9VqOP3P5VnNI6KTaJuD3pAQD1pAnuaQpj+I1Bq0Nkbkk/wAqiMw/yKfIg6kmofJXPVvzrSNrHNO6Y8TDAIP4HtSeap/j4NMMEZ5+Y9utKIYv7v5mq0M9RzNgHAJx2zUbb2Occ+maeI4x0UUoSNei9aBkIkZeMYP0p3nE/eH0qXbH/dGfpTtif3F/Ki4WZAwJG4McHrzxSZZe6N/OrKxoTjaPypXijU/cQ/hRdD5Xa5WE5xwoHvSmdxyf51OFT+4v5Uo2j+FfyouKzKwxJy2S314FSq42YIJz0z0qYH/OKXdx3P4UrjsQeagZlcY9MDimSbn+6PlJ+tWt9G4daLhYpKCrZOOvGTirkJZlOGIGePpTuD1XP1FMaKJh8wx9OKG7glYmRnGckfXIprXAT7xAH51Xa1Vhw/HoRSGGQfwg+m00rId2WPtURUfNu9gKXzlP3Vb6McVULOjchhn2oE5AzvbPrRyhzD7q2kuyuWRAufU1m3UH2eYR795xknGK0Bd+rL+PFZk8vnTM57nitIXM52GYFFJuo3VoZCmnR96Zninx9GNAx5OTUkQ/fR/nUaDLDJwKtuoEluV5ypH61LGtzYt5o0gjQvtbFSiWFuknPfnFUPsqMTlTnHOTwDUi2UfGQpOO+TXM0jrTZbM0akdeaaLuJSVUtkHB5pi28ScKuM9gKeEUf8s1+uKVkVdgb3k7VZj3yKUzysMKgBxweKcMA/d/IVbitZJot8TEkdRipbUdyoxlLYoq90eW2/QHrTjGHwrnI78f40ruUk2vuBHqKRgWxl2/KnuLbQettbr1EmOo+bGKPLtBlmTOTj5mpgiU43MTjuxzTiM4AbPpmkFx4jsx1gjH4ZpwFqDgWyD321CI8EkyKD7Yp3kswIExx9OKLDv5E4lQHAijA9doqVZD0BTp02VV8hv+e2PXIFNNvnAaUkemKVkNNl3zdp+/z6baabnehi8wBc5+Rc1XWJVGQTkjkk5p4GOCwHGMhsZpWQ+ZjiSTgPgdvl5FO3ykE7mAx02fzqHywH/1jqO2GpRt673JHck0WC5L9pVSAx3djk4pftBKqVQFSeNpz0qEysW4xnP504Syhsgj+VKw+YsCdznA5/2gaUTy9SG56e9QCR8ZIAPryM1IXOeuVxwSKVikyRpWY8BR+ppVUkZYox/3BTVV92A/BOMYxWzc6EltAJftuWC7sDgZ9BWU5xi0n1NYQlNNoxmSB9ytFDwMZ2Co2sYXbOI8YxnLA1PuQHlmY+9PEgVcAjHpmq1JKT6ODJlGCoexJpyaVKmFMsWzuAOtW1mOcjHHqSacZpM53+2OBmnzSDliRxWs0RV0kiQryNoNSJBIrbzdBWPUgE9evWjzCDgs6n1x/WnqwPWQEH2qGWn0F8oFQPtLhscuMDNLuuAm3zMtn7+8cj6YpryKDiPkDsVAoErMD8wX24H86Vh3JlmuVJJkBB5Gcf0FTu1yIFeLy3BJBByCDWfukJ3K7AHsQP507fdKoUFSOuTk0OI1MlW7v4yQyMuemxc037fdo4AicqT1K4P6U3dcZ5dBnvzkU4SSqAAyEj1JoshczF/tKUEgpKR0wUxTTqsqj5IeAM/dJP4VL5lzsDhU29M8jmohdna24YAGTgbhQkuw7vuNTWIXAVgN30wR+dP/ALZhjADCUHIBJ6fpUclxZuGDtGSvcpkGqUj2H/LLzFOcHy/lzVKMX0Ic5Lqag1W3ONsmfQc81I2rwRghygHcNuOD6Vz8FreCdZ7WGUSg7g7DGOetSnRL65laSeaNSSSctnPqaHTh1YKpPojprGawninmnniSGFdxcEAk9hg+tZz6rYBgRLGByNoX+tUf+EchB+a4fB/2RUyaBaof9ZIfXgVChTTvdlOpUa2LDX9pwdgxjIOz+tRnUrHODJED7AVG3h2zZcCe4XI7NkVEfDNljaJ5fxAzVpU+5DdTsWG1KxTkOpP0GKF1C0Y/LLb/AIjBqqPDNqpJ+0zZ/wB0Uv8AwjNpn/j6m5/2RTtT7k3qdi6LiLbuElvgd8igXkCgsZIvrjFUh4btc4+1XH/fIpRoVqpGb2bB7YFK0O47z7FwXduTkSQ8+lSJNEytknHtHkVRXQ7dclby45GDgDpT10ZY1IjvrxQeoBGKGo9xpy7Fr7PE/KlRgdNtQvDar8zOi/UjFQzaSJXCte3hA9warvoMcrZW/kA7eZGCP0oSj3E3Loi1/op43wcdckCoJpLSIKQ8W0nGev8AWoz4PmkQtBeJKB1KxHNRp4WlyC10Aucfcq17P+Ylup/KTfa9PDYV1JPbb3qB9QsA+0pJ/wB8rVkeF4zzJeOT3+SpF8M2I4aeU8dtoovT7itUfQyri8sDjy4ZRzz8wqq1zb54R/pkV0i+HdNAyRcHty4FOXR9JBAFtIxGQf3maaqwQOlNnKm4j6CM/iaja4BzhQK7RdL0hSV+xjp35/nTjp2mZBS0XOOhAo9vHsL2E+5wplJ/hpu5uwArtZ7C1jUlLXP+yEzWfJZwbyPs46dkAxVqsn0IdCS6nNdRyc+1OBx0xW++nWn8apGfQmm/2NZnDeYBnpgdf1qvaxJ9lIxBLjvTxN7/AK1ryaJD/wAs5GbA5x2qjPo8sZ/dh5B1yFzTU4sTjNEAl6ZNOEi45P6VFNbS2xUP8pPoM0sceT8z7fc9KdkJSlsTK6+v6U4YJAD/AE4qxbaZJOTskTC8Nhtx/wDrVox6THGAXJc++QKzlKKNYxkzJ2E98ds4p4i6jkkdcCt1bK3C8D8CeKni/co6KsTK4w2Rk1m6nY1VPuc8Ihu5QEHjGKkRBwFXBHtxW7tTtGPqtOBjxu8p85/u1PtClAyY96/xOQe2cYq7CyhCrrIRnOCat+aowF8zp0xSmVwOElxjstQ3ctaEfmQnhkPPXK5p6vZ5wY1PbO05ppuUQbndh6llNQf2rZ8gTgn3BA/Olyt7Dc0tyaWC1k+5K0Q7AH/GmNbRPgG+c44HCmoU1ISOxtog5A+8W4p3mXUmN6xr7RrT5WieZMcbKdnIjvV2AfxqBj8KRdLkJP8AxMEU9MLCc0pJVQrJkDt0FON0FIByQOpUUe8P3R39kvt/5CMwHcKuAR+FM/sRWUFriaTjHLYFTrdxHbtnZMDGOlPLAgOsv5HmpvItKJXXRYt+4vMWAAIFTW+mvb3iXIkLsp3DzMAfpSidRwXbn1bNHnAgFAjEf3yal8z0ZS5VsSXOiLf3MkvmiNpCWKkZAP4VRfwyQ3z3eO/EeavW1xLE6vlFwT0HBq7c61aRwKzygNyCFO4j8qz5qsXZGyjTmm2YP/CNhsgX8ROcnKHNSDQ7iNSqX0ZGMEMpxTbnWUnOIbbJPCvIcHPtUKeWHzcTlnzuVS2AO/8AjW69p1Od8iegPot4V2i7gII5IG3P+NINKvUk3K6OwHBEhH8qfJrFunAH4sefwzVOTWVkXAVfTjOKtKozNumiaWy1F51dwrAf88yBTGi1NQwVUDE5I+XFVW1R1XjaVPTj9M08X1wE3tEqqRnLDGfp61fLIjmiOZtTRQuWz3ywxSfa9RKmNpYvx6j2zSpdXU5AQEYHJIwAPf3qxt2DJm82UxlhzwO1Fu6C9+pVWKY27TzzEfu2Kp0B6is7XHJvUfJO5F5J68CpGu0Nu/mOSQuxB1x6mo7oRTxxvPKV2oMKoyxGPyHSt6as7s56sk1ZFBImmf5SOnzE8BB71SuWUy4QkqOBmp7m83L5UQ2Rg9B39z61UHU7uhroS6nJJ9BtGaD1OKDxVECZPrU9mskl5CsRxIXG0+9QU5SVYMpIIOQRQwW50pg1RuPMz/20o8vV9oAfpzwwqa0vxdWyyHIbow7Z9qsGduwz9MVxttO1juSTV7lUtq/AA4PXLAU0jVwRsyvHIyDVv7SRztP/AHxTftDdNvX/AGelK77Da8yqTrPTarr+BNMa41hODCePRAaueecjJPPolIJGPSTB75Bp38iWvMzn1TUE5ZdmP7yHimnWrsjDPFke1ahkkx95cHsaheOOTh0hY/7uapOPYlqXRmc2r3XYR888JTG1O6wCGKv3wABVx9Ptm5AZD6rnH61GunorZwrj/ayKpOPYi0+5UF/eSHaZ3P44p4hvn+bLkj/azVgwiL5vsgPb5eaI5WQ/JG8ajqMYzTv2Dl7sqta3hOG8wD1zQto/WTgZ5yxzV/zgyqGOc9Mk8U8hckkYPftS5mPkRQazQHG1mGPfrTozFuCNbNk/3jiro2dQo5pcj+6Pyo5mHKVgtnux5IB9jTGayB5hxn2NXMjPCj8qN47gflRcdisHhbhIiv0WpGkXACpu7+lSlxSBx2xSAgDgE7YevfFPMkv8KooqTfxxSFhjqaYiMeaBngH2zTf3pz+8XHfjNShx60hZCfegREQ5zkofwqN4FcHIC5/umrG9PWk3jtj8aYWKZsk6iQ++actsqn7xYn1qxnHTH4UFj6indisiAW6gk5c5qQRqOmQaXJ7nJ+lBNILCFFHdvzpu0DjJFO59qTpQAc46j60g3Djr9aXPvSZoAaWcc449hTfMI5PA9MU/P1FG4dT/ACpgR+aSOv04xRvyPv8APoBUmQeuPyrUl0cQ6Il9NIqSSHMaZ5I+lKUlHcai5bGRuz1c0nyk9c/jSlTuyCeevFMIPcZqiR/40FmIALNjsM8VHgAdCKAPRyPxosFx3b7x/OmOA6lWOQaX5v71NyfQH6UAUXTa2D+eOtNq5ckvGCV5X+VVK0TuZtC0UUUAKBzV20064ulLRp8o7mqajJrUt9SngtfIQqF9cc1nUcre6dFGMG/fKyxmOTHdTWgGUjIqjuySSeaBKVOQazabNU1Eu7gBTd1QrLuGR+VTxNCI3Mhbf/DiptYpPmY6JvnHPeux0ZsxAZzXFRv89ddocmUArjxi9w7cFLWx0MQwatQuC23PXiqobEeaZbTfvT9a8Zq6PTHasjwBlJ5x27VxF4paUnnGa7+7iNyhY8setczdafsckjpXVhKiiY1YOSMCO1z8zcAVVu5FU7R0rS1GdbeLAxk9q52WbcxNetRTn7zPNxEo01yoR3561EWppfJphJ9a60jzZSH7sU0nmkpOlUTckWQqMc/hR5nbJpgIoosF2PyTSgEmrNjZyXsyxRLlu/tXaaf4MVQrXEo5HIArmr4qnR+JnZQwk6uq2OFETkcKfypjKQea9XXwxpypgoT9TXDeKNOi06+8uMjaRkCscPjoVp8qRvXwLpw5rnPEZFSQtscUwc0pFdz7HAtHdG5a3IKgZq2WBHFc3HKyEYNaFveZADGuSpRtqjvpYhNWZZuEyDWRPEQa2SwYe1Vpogwp05coVqakroxyMU01YlhKngVXIrri7nmyi0xpNITSmmMasyYjNnjtTKU0lMlhSUUUxBRRRQAop1Np4GRSGhQuSBUwx0qMAipBmpbLSF49aXg0mSO1Lk9zikFheP8AIpmdx6HHtTto68ml/EUAN8vdzninbQP/AK9LketLn60AFOBPakBNKG96Q0TIrVZRTjFQRSDuasiVexrGbZ10krbjsH1ppHvWjZ28coDE9alutOQqTGeaw9rFOzOv2EnG6MSQcYzUJxnrU0wZGKtVcnmuqOx59XRi/jRx60zPp/OlyasxHZHYfpSg5FNBxzmjNIB/r0paZu9zS7vegY9XKnKmlyzGmbsd6BJj/wDVSsO48bqcM+tPtYZrydYYlLO3AHSr1zompWiky2km31UZqJVIxdm9TSNKUldIzsH+9RjHQ80rAqcOCp9CMU3IB6fpVXuS1Ydu55o3cj0pu/ngfrRvPoKZI4HnrSg/ifpTN5//AFCjec80DuOBJPXbS5YdyfwpgLZ4OBRk9yeaVguPLOV+XI/DrTSu8DemD/Kkx/nNKOuM/rQBTvhFHGfmJkboKzaknZmmZm6k1Hmt4qyMJO7CjNJRTJFqVVPlk1FUsWGG3uaGNBnpnpViJsNG2PuuM/Sq444I4qRCTkY4IxwOaQI27syRSMU6o/I7FT0qFb9+SV5HHJ4qcFkt3kun3TTYAQ9OP8KiFsoYFXIPXkZrCy6nTdvYlF2vcjHsakWUN91gf51We083ALAY7heTSCxwQVk5HOcUrId5FrzVH3mx7kVPa6mlvKMOMfXGapfZ5f7yv+OKa1s+OIhn131LjFqzLjKUXdHSGS11Fcq4D+oqhNE8D4O0+mKyU+0wS79mfTaelX01AyRmO4DA/wB4gGsvZuG2qN/aRqLXRknORnqfWjkD7v5cVnPdOjNtJZR6Dihb8D7ynP8AsiteVnO5pGlk5wB+VJyO1UjqKdBk/hTvt8T8l2BHqOtLlYc6LfJP3gPwoLMDw4A9c81V+1RgZ39f9mlN7EoyHyPZaOVj5kWl+Y43k/jTiqMBkNjvzVA38ZxjeT0xim/bo2OQrce9HKw50aIZVB27h9KdvVSPvelZou93ARjntup4llb5fKP/AH0aXKPnNDzhnBIB7etK06t/e/Ks/E3Xyvpl6BHck/6tf++uaOUfOzRE6EYAA+goE6EY5/HiqHkXJYnCfiTSPa3G3+EsOw5pcqHzvsX/ALWm7hjx/s1Ob2WUDdJIVxwOwrKEM5cExlR33N0qT7E2RtkIHpjgflUuESlORdEmcfNz9afHskbIOT245qh9jcAfvWB9QackUsZys545GT/9ahxQ1J31Rq7gR5Z3Agfe2/yqMsEIJdz9RVV2nlADSnHoKgNrKSSszDPfGcVKj3KlPsaQmUH7xz9M0ecob/WdemcVlGxn24+0kfVKhksbjGftisfcVSgu5DnLsbi3Mecl9x7YP+FOM5I6j6d65x4NQMeAVZc5+UioWW+En3ZCc9OoFP2S7k+2fY6o3AI+ZyPq4pPPUgbSPc561zAjvZGDNHMoAwewNGLlTiORiO+1uPpR7Jdx+2fY6fz2wcybe336ge/jUZNxuI7AZ59qxEhLsfNlO7+H5SRj61owWsMZBZQ56jdz+lS4JFKo2W11q4mhEUNu0mzjIJqEW15Md00ojB+8B1P4CphO38CHPbAxSCeU8HI9uKlRS2Rbk38THLZ2YI80zSED1wPyFXYbm2gyILdE9yOao/an7nA9+tIbhiOW/Sk4t7jU0tjQOoHgqR07jNL/AGgrIFKjPqFrPE2erD8KPMBHyjPrS9mh+0ZoC6ck4PA6cUn2hz16fSs87cgFSM9wKcrR5wRn05xRyIOdl7z2Hr/3zTfOJHOcfSqe9FOdh/KlExPHNHKLnLZlXryc00zDttI+nNV/Nbp/WkL/AO5+VHKHMWhOMnDD9aUXI6Fx+dUJZmVC0YUnHQUxbnkZKg45AzT5Bc5oiZTxvbH+8aPNQcFmYenJrPN3ERgNhj6k8UfaIuuwM3sxo5A5zQEyIOGIB7ClM654ZgcdKzRcxnniNsc7sU03CKg8uRASeecn60cge0NHz2BypbOOpbFKLqZfutjcMH581RWW3DfMyyOfUZz7c1ZBwMiPb9UxRyoFK49bucsRvUnuFJJqUT3JI4B4zhqriSXOVAU+xIpxlmPBEZHu1JpFKRbW5uF5CJ+AppnlJJEEfPoCCKqmSU9QOPRqDNIcAx5H1pciHzsstc3GDthUfQ1Xa7vevkg/hTBLzna4J9CaU3IH94ge9Pl8hc1+o/7Tf5/1Lc+jACnebef88yB/v5xULXZzgB/qRTftTbj8hC465ot5C5vMZKb0yHIjaPPRutIQGjCNCF4wDt6fT0pxvCo+VhgVUfWQr7AVB7YOc1aTfQlyS3ZY+zwhgwQbsckPQ3lqAPOlXHQCSqu+7ncMqhVIzlzzTW02SZf30+P91efzp27snm7ITUp4HhCgsr5B3jqce9ZLlydom3gnA3jGB/StxNNto8biz4HRzkfkKmS2tE+5GAT3AzVKaitCHByd2c/Dc3NrJujcA4IAPTFWI7vUcqys5DcAAHBP9a3VaMZGd49Nop6yN0CkD2pOouxSptdTIW41ESNJucM38JXd/wDqqxDeakARLAGxyS6Y49BWhvcYy5/PrW9a+HLy604XkUobIyEzk1jUrQgveNoUpPZnMHVZEfb9jlY+seT+FK2uJEMfZbgHt8mPzq5IZUYqwcEcFTUfnHpt5+gqlyvoJ8y6lX/hI4+n2e42+pHSo3192J8pFVOu+R+fyq6WXrsBJGOVFMaNJPvW8f4oKpcnYl8/czv7V84t52oSLzjCJgEU6FtMYtuaR8c73Bx9attZWzn/AI9o8dPuimNptpggxKoPUAmqvEm0iQX1mo2iVdvTAUCkN/bEfI0nHJznp7Yqs2l2XAEL/hyKRdMtwuEaVcD7oYjNK0AvMsJfW0nCu4J7tkflnrUpvY13b5kUe/X8qoHR4ywO5xxxufNN/sUbs+eSc9dgxRaHcLz7F1dQsw23zGyf4iuAaR9Xs4SdsjsTwdp4qhJorsf9eM46bKgfQrkHiRD9QRTUafcTnUWyLj68qnEUMf8AvElsVC+v3DEYkCD0VBVN9JvkBxCrj/ZaoTYXijm2lDfnWihTM3UqE02pyTMSSxz1DHI/D0q3b3e5FwijIwxCg9KyzaXIGDbSj3KmlijJXayTDHPCmm4RaCNWaZqtdxp8qqxzw3HWoPNjJJW2P485quLm4tW2+YUxztAqzFrDY2yr5jdjux/Kp5LbFe0vuLvkPCQbV9x+tO/fs8cRYAMCcL3FSf2rEvBRx9GrNvL0zXJlBKgrtAz29Kai30E5JdS9bzOjnY6BcYMhHX6A0y4nURlwWZjn5nPJx/Kss3bsVBPyr0HpSSTKQQARnrk1ShqS6uhrwamYo1XaTgEn0JqnNevI+CcAgKAOBVEzcD37VG0jMc56dKpU1ch1Xaw9peD9TUctxJKAGPCjAFMJ5+tNrRIycmJ3pKXvQfSqIEpMmlpMc0AGTSg5pMUUxHUacQunwgL1XJ475qzvAwdnX8ax9PuVW0UF9rKSvuavfa13bN2Wx0PeuSUXdnZGSsi35yDI2kY9RSeahH3fzqv9qIYYX36Gj7QT0j7dhmp5SuYn85Dj93+tIXT+4ah+0E8CKQH/AHaZ9rbdjy3H/Aadgcix5iZ4B/A0GUDqDUAuwO5H1GKPti8fOPzp2FzIl8xe4wPpQZB2OPwqI3GTgEZpPOJ6fzosLmJfNx3/AEpDNnruNR+Y2M7TSeYenzCiwrjiV5O1iPTpTDw2QGB69aC596aZfcn8adhXBsgZGQTxSKSQDuyP92kZ85zkA+lQyvLwEK8e+KdhXLQ25Azz6Vpx6RKbNrmZ/KjAyM9TWdpN1Fb3qtephBzlRxU+s+IZL+XYiFbdfuqD196xn7Rz5Y7dzqpqkqfPN69iqXwxwSR60b89/wBKqi5Dchcn2oE5bOFP/Aq3scnMWN59T+NBYj+Kq/mn+IqP+BU0zAZyRx14p2C5Y3Dsf0pC2e+P+A1SN4Bnapo+2D0NPlZPMi2GAPDfpRu56mqv2tcZ2tQt1GT/ABCjlDmRa3k9zRn3NVvtKDuaPtKkZyeKLBcsbvTNG70quLhMdTQbhM4yfyosFyfdRuqD7RH13H8qBNHn7x/Kiw7k+6jJpiShiNuTWhbWjzYwhIrOc1Hc2p0pT2KeD75pCD3NXbm1kg4KfpWe0r5PQCiM1LVDnScNJCk4HUn6Us9zNNtEjs20YXd2FQNOe20+1Rmdyfp7VaRi3Ym3ken4UhmUDkkVDvkJ6E/hSbXPYVViLk3nKehP4UhmUdz+VRhX6kZ/Gk8tz1x+JosF2P8ANU9D+lNLjsxFCxkHnGfal2DIOeB2FGgajdyn1NV3XacYOO1W+O1RTsOB3600xNFelHWkpaoRKuO3SnhqhBxTs1LRopEpek3VHmlzSsPmJFfawNWQVPf9Kp1YhkGNrHp0pNFRZOpGeCa6jRJOBXLqR2Oa6HRSQRXFileB6GDfvnWFv3XFFpCTIGNMj5AyasxPswK8SWisewjTAGzFY+qRgIxrRSU4HNVL5N9uwrKnpITPNNVkMly2egNZjY9K1NViKXDfWspq+oo25FY8DE353caaaaUmkNbnIwzSZopKBC596KSjrTEa2iaoNMu/NZN6kYIrrT45tY1/d28jH3NeejIpd9clbB0qsuaSO6jjalKPKjsbzx1eSqVgiSIevU1y17ez3kxlnkLue5qsXphNaUsNTpfCjKtiqlXSTHIasIMj2qqKkSQrWskZQkluPkXbTFcg055MjFRZoS01CTSehft7srgE1eVw44rCBxViK4ZD1rOdK+qN6de2jNCWMNWfNCVPAq/HMsgpJEDLURk4uzNKkFNXRjsKjNXJocHiqzDBrpi7nBODTIjSU8imYqzJhSUtJTEFFFFACinjtTBUg7GkxokBFSAA1CDUit6VDRpFkyYPBoaPbyOlJ71NG2eDUNtG6ipaFfH+cUfnVh4cjK/lVdsqeQaalczlBxCim78dqTef8iqMyQc9DTvqaj8wgYXk9zSbmPqfqaLAShgDT/M96r7mH/66NzelFhqTRpWt8YDjPFaSamGA+aud3HvSiT3rGdCMtTpp4ucFY0b6dZX3A81S3Enimbz70b/fFaRjyqxjUqObuO596OfemZ980uR61RmO59aAWpo/GlyBQA7JPc0ufc03P1oyPWkA7IpwY+ppm6lyKAuSpI0bBkJVh0IPSti18T6nbAL9oMif3ZOaw8ilyMZzUTpwn8SuawrTh8LOrXxLY3Y26hYK2erJzVHUo9IeAy2MzI//ADzYVhZ9+aXd71lHDxi7xdjaWKlJWkkx/wCVGfembvel3e9bnNceDzS5PqKjJpc0WC4/d70bvembgO9G4HvQFx+c9zSFgASTwBTc+9V7t9sBA6scUJA3ZFCRt8jOepOabRSVsYBRRS0AGKVTtakooAsMMjcOh61atQsK+e5+790Hn8apxSKFKv0oklMjc9B0qbdCr9S/5klzMru2COAB2FWoLgsApI3ZI+uKy4Ztpx2I5qxZuBKvfcCOaiUTSMjUBb/PFOD4H/16qNExXfDMy+2cio4bqVJvKnIwfusB1rPlNOY17eNpi3PGOuOlSPEsSHcefyqlHdvH90bfeh7hpDlmJPvWThK/kdCqQUfMeXAP3jSFlb+EN9RUe8f5NG/PUk1djK4rQwkcpt/3aje1Q/dJ565p2T2BP0FKHP8AdP5U9SdGVzalTk78e3NN8on+Nz9Ktbseo96Ryh+8oJ7Z4p3YrIri3/3sHuakWFEPzLn3pfJUfcZlJqT96Bnfx9KLgkCiDP8Aqxn6ZqUGIdFH/fNQYlI+RkJ/2hUbi7Xnah/3aQ9i6JV7YxTvO/2qyDdzIcFDnuCtN+3S5+6B68U+QXtEbXn8/eo87/b/AFFZH28YyEP44o/tAH+A/pR7Nj9ojX3nHPNHmsBwCKxWvsfcB/E0f2g+MY9sdRR7Nh7VG35rYzxj3pTIxxtVSO/tWGdQ4HyLx0AqVLt5G2pDuPoSTS9mw9qjYEyqPnIz9KPtkQHVvwWsf7Q6v84Cse1PEkQAO4cjnHFLkH7Q0mvUHQMfw4prX3XAwPfNUTMgPyjkdDjimPcog4Bz3B4p8iBzZeFw7NhsDPrk0efuUhvmUcbQKyXuCoXax49805ZpZH2ohOR6U+QXtDT89UIwxwOOecUn9oFhtVXb2BqG3s5HkVp0JTOSm7GRWk0YglZYh+7P3R7VDstC1dq5AkdxKPmwq9t2d1TpaxqMtuY0gZ+7UbieSTU6lKw5oiXDeYyAcABuP1p4XjhyPoM1GD65PvTXnCe59AKVrjukT7Tj7xPrx1oKkc7mH5VCJ42XPUfnT1mC9FYZ5osx3Q/djgOf0pN5Bxu59lpn2kds/icU8zYPrx2FFh3GvIQoxvb2ApguJVbAVjUvn9/mpfOB65/WgQgnkJztYe+Qf504StnJ8z3zjFIZEx0em4iJ5B/A0rDuTeY3o2MegpDcc/cOPwqPMTD+L8aQSIeBGB9B1osFyVJhn7pz24FKZi38Lg1GZHQBthAPcZ5qFr0g87to7gGi1wcrFrewPUDPvmlLtjgqfrWf9uToC5J7AVEbyZ2IjEoI9s5p8jJ50ahd2BzLx7U3cCOWkf24rP8AtF0ekMxI+7xSB753+WCTHoxp8gc5ogx5yYgOOu0UGWLk8D8BWcY79wDt2/Vqd9mumxulQDuOuaOVdxc77F1pbZsDZn3I/rUZCsf9awx05qFLRUIJkH02mptkZ6yN6mlZDu3uBlKqdsx/4Fz/ADqS3upJNy7SwXuSBzVdo4ONzP8A0p29FHygkfSiwJsurOw6gD6EGnGcY5IrPa5UAFl+X3WoJL5UUskQ9sjGaShcfPY1ftPGAyimmZuDlcey1kDUGKkFhG23IAxzVaS9lK7d3PrnrVKmS6ptT36wZJOT6ACs6fUbiTJVlVVOCc5qn5VxcEko0h4O7HFPWyufMDMOPbtVqEUZucmWkCStm4lyvXG7k/n0q3CbWLd5KquPx/GqP2N87xH8x/vsDTvsEbIC/wC7bGPk5pNLuUm+xoi5VslZFI7HFO88kcOCfTbWclpOjDZMcKMfMuaeIpjw1zJx/dQVPKilJ9i+Hb77SYHpgE0vmPwQSM+1UhHMBxcE8Y+dBS7LlcFJI2HfqKXKiuZl5Gk5A3EDnpT52EUjJuEm3+NeQfpVHdOo/hJ9d1AkuBn5fybNLlK5i4H3HAA/75ro/DevnT5BbXDH7O54JGNprkBJcc8DI6HPX8jSfaLsDHkkjHZ6yq0FUjysuFbkdztvFdpCJFvoWGH++Af1rlmuEBJ+fH+7xVV9U1CSJYXhcxDopINVzdTKTm3IPr5fH6UUKEoR5W7hVrRk7ovC8UnhGP8AwHFO+0Nn7rgH1Wsw6gF+9Gen9zFC6pEG2FcVvyeRj7RdzS37upbPTBp4YgctWcNSiI/1jKc9GFL/AGgo6ODnp8ppcjH7RGgZD2B/Dik8wkYOR7dazW1FUYq5Ab8RQdVjDYZ8D15o5GHtEaW2IDO3nsCOKuabcwWt0Xng8yJkZSoHfHFYa6hBI2BIc+9Si4J6bv5VMqd1ZlRqpO6Le5ge/PpSFieefzqr5s2erfnTPPm/vflzT5Bc5oTXUssgduDgDgYHAxTzFcC1Fwynyidu7cOv0rME8o4IGewNOM9yFwFOM5IHSjk7D9oupbEz5xgkezUvnyD+9/OqAluiduEJ9gcfnSh5QcscDFPlJ5y20pcAOuQPUVG8duw+aBTx3UVDul4GeMfSgvJ6/nRYOYHtLI8fZ0H5CsXUYo4bpkjBCcFa2t7HjcfqKhnhjm4mQN6HPNXF2epE1daHPH60ZOK1G0pSf3UpHs3NKdGnjTcxQ+2a19pFGSpTZkdKQmrM1rMGP7lvwFQmGQclH/KrTRm00RmgHBp5Rv7jflTdrDsfypisNNJ9aUj1pKZIUlFFMQUUlHXmgC7Yr5gZcoMEH5q04VhTowZ/VhmsFSQOuKeJGHc1nKNzSM7I6Lzfl4z+XWgS8AA546VgLNIvRyPxpftMp/jNT7Mv2pumYjqRg/jSeafX9axBcSn+M1NMLu3I8wsu4ZBByDS5B87eppmU9c0hkB9/+A1j/aJB/Gx9qDO+Qc4p8hPtDRd7Ycuoz67etGID0j/QCs0+Yy+Y2SpOMmgSkADsPUZp8ouc0SuV+Tg+h6Um2TuxPtuqkLjaAAP1o+0k9gPwo5WHMi6wCg43hvZ80xWkB/1Zx61X+1emPypftI/ug++aOVhzIn3seNwA9+aVXYn77Y9lqAXIxwMUG6/zmiwXRYIY/wATUmw+rfnUP2j8KT7RRZhdEwjQZAGM0Mu7+MioPtHtSG4PtRZhdEjRMx5Yn3AFIbcEAF349qZ9o/zik+0e9OzFdDvs4HSQj8Kb9nI5EgH4Uef70ef70ahoILds/fWjyD1LD86Xzs0vnCjULIb5L9sY9AaQxOOinFP80Uu8djRdhZDNrjgKfxFIEcj7jVKH96cGNK5SiRCKTH3evrT1tnOOQPxNP3+4q9p9ubidQBxmonPlV2a0qXPKyLuj6I1y6sxBHXpXfWGjQ28IJGOPSoNHsVijU46Vev7xYITzjivncTiJ1p8qPpKFCNKJzfiOKCNDzk/WuHlKBuAK19a1I3MxAJxmsJnJNexg6UoQ1PKx1WMp2QbhSbwKYTSZNdljzSTzB70u8evNQ5OetJk07CJ9w9aOPWq+TRk0WEWMj1pCfeq+T60ZPrTsK5OWHrVVm3MT60pY80w00hNhQKKBTJHClpBS0i0FOpKXtQMUU9eopg61NAypIC4JWpZcVdlm3GPnbt+tdFpD7nz2rnN+9uBhewrb0diHA5rixCvE9HCtKVkdbHLgD1qUOeDVBCeKsoxOB2rx5RPXTNGFxtFEzbo/51BG2BillbC5PSsOXUZxOvw7Zia5pzzXSeILlXkIU9K5puTX0WFv7NXPDxtufQaab9KWkrrOAKSlPBpKYgoHrShSaUqFHNK40gds4I/GmZpCRSZppEyeoZpKKKZItGaSigYtFJS0ALRnFJRQO5NHKUNXopgwFZmakjkKnNZzhc2p1XE0XQMKpTQ46VYjmyOtPZQwrNNxZvJKaMllxTCKuTRYPFVWGK6Iu5xTjZkdFKaSrMhKKKKBCinK2KZSigaJcA9DSjINR5qTdxUlD1bFTBsHOaqg4qVG7VLRpCRcjkyOtSMiyDnFUgxU1OkvSsXG2qOmM09GRS25XpyKgKtmtIMGGKryxY5FVGfRmdSl1RTwfSk5B71IeDSZrW5zWGEn3pwDH1FL/Kjn15piFCAdcmpAccAfpUXze9Lk980hkuaXPtn8KiBIPDE/Sl3EeppDH8enNGSp46Uzc3vS7mxjFADt5AyeKN6+v6UmfbikwD0oEP3L60m5R3NN2/X86Nh9TTAcHX1pfMXP3v0qPZ/tUuz/AGjSAeJVzS+aPeo9o7sTTgAPb8KA1HCYen607zP9k0z6n9KX8aBjt59BijzB3YU35eppdyjpigA85exJPsKXzSekbflT2VlQP1U9xUfmD1NJajaa3F3SHov5mjMuONn503zF9RTWlw2MnFMRIvmj7zj8BVa8JOwZJ4PUVL5wx1qrO++TPpxTS1Jk9CKiiirICiiigAooooAKWkooAduwv1qeFtp/QVXHX6UoOKTQ0zTgvSCqEHb0+lJO6NHjOfT2NUN5BBBpxbIyTU8pXMaMU25VYgnIGQDUj3Hlt935fzxWakwWNRzxQ1xnoOfU0uUrn0NaKZZV3I+R0PtT/MUHlhWTZNiU+jA9q0A3ov6VDjZlRldEwlGeNx/Cl81jxhgDUW8+4/Gl3Du2aVirj957A0pkIBOxjiovMTsSPwpd4xnd+lFguSLK2OEI5+lKJD7CmB8nvSbs9QfxpWHcm3EnkilLEdCOlQh+M5o3+lFhqRIS57j8qYYlf76Kfwo3n1pQ3sKNg3FXT4ZASFIx6GqrWKAnEpH4CtPeIrc8/kaovcoM89OtTCUncurCMUiq1kV5Uh/XtmoJMoQGVlNWXulKj5SR+VMWWeT5QvB77c1qr9TnduhD9nlY5A6+oo8iZeiMfcc1oLCv8Qx34FOEMXXaT+NHMPkM358hZQ5HbI6UBXLhQOTWqBGo+7+fNODAcAce1LmDkM5YJG5w4b07YpxsyBuLHPfAya0A2Og/WlDH2H40uZlcqKaW8aLloWbPGTS72h/1ULLzzjvVvcc5z+tGen+NK47dip9slJ+4w+oNP/tFs/zJWrIPv/49S7+e34mjTsFn3Ky6oBj5Tx14p/8AagGD5ZII+lTbx/dFGV6bM/8AAaWnYfvdyH+1V469cYpw1KPHzbffvUmUI6Y/4DS5X0H/AHzRp2DXuMXUIiCUHA644pw1CPsrk+gFL8v90f8AfIoGMf6sflRZDuw+3oeNr591pPty5wFJ/wCA5p3y45XH4UEqP4cn6UrId2N+3pnG1s+wpP7QT0b8qdujH3ox+QNLmMj7q/8AfNGnYLvuMN+gOMHPvTTqCZ4Un9KmwuOcAdhjFJ8vbIo0DXuQnUE7I4z/ALQoa/T7o8zB6gEVIUBHX86a0PzfeBPsBT0FqEupRNHtCvkfxbhUIvoi24oxI7lwKk8n0P6CgwHj39FFCUUJuTIxqMQztVx+VB1YA/dkwfQila3/ANlfxQGo2tkzkxoD+IqvdFeQ8awMfdk/OlGsEkYjb6BuarPCq8lmUfU4FRvGwTIkP44xRyxJ5pF06wAOEbPoTikGsDPzRsPxrPyxJUsSPUgEUphVlGD83baKfJEXPIv/ANrntGSPamNq7Yyo5z0JGKrLYSkcEAHuwqaOwRDlpGIPUKMA0Wih802PTU52bCoM+i5JqZZL2YcsiD0PJ/KnpHGgAVCKftUnJBz65xUO3RFpPqyP7G7/AOsmkYegGKVbKFcZ3kjplqkyR0OKN5X+LFK7HZAlrCOkcYz325qcQqvRlH/AcVX8xm4yMfSk3E/xDj2pWY7osE475pN46YNQ73HQg0CSX14+oosO5NuzwAfwp2AOSXHvUG9+z498U4Nkff6+lKxSZL2JDcfSkLf5K1EVx1Yj8aM7ej8UWAeHAP19CRR5ij1P40wuwz8wP4Uebxjac+tOxNx/m5/v/hinecRz8x9yah87j/E0ecueoosHMTiYk5w2KcJGY8Z/nVfzBjrmtbw7rg0XUDM8Ec8TrskQjnb7VE7qLaVy4NN2bKW9h3H5U3ewI6fiDXVeJLHQp9N/tbSrxELEbrfocn27GuOMoHG5sVFGaqRukVUXIyfzG+v0FNZt33kJ/AGoPPHQZP4UhuGP0razMnJDzDE4+aAc/wCyKjNtb9ocfiaUynocUeb78fWnqK6IzZW7jmI/991G2nwHnYw9Pmzip/MGPvUnmZ707slqJELMoPklYYHdRQYroHClWGOpANSlx3z+dLu45FF2FkVfKud3zMox0KmpY5LlOCWI6DJBqXeAeB+VJ5gz/wDWphYjFzdjIMTEepwaaLy8GAbc59dp/pUvmjsf0o3+/wClL5Br3Gf2hKfvQyY+hpJNQxgqsn4ipPMOOo/Ok8z/AGqdl2C77kS6gWOSCB/v9aebxgcneBjPQHigyL1J/QUhdG6qG+oosuwXfckW8j+8Dn86kS5RyAD+WKq7YSf9Svp0xVm1hgzvKgYqZWSLp3k7GlFsij82Q8+hqlcaikjbdxHoKhvJRM20M6ge9Umic/ccH2YVEKf2pG1Wtb3YbF3zl7E/gKaboDqx/HpWe8cuMFTx0AOAKYwlAIAfHrWqijmc2X/tn/TPAHfrTTdRt/Ep9iAMVnF2XjLZpF+c7Rk5quVEubLjXkZ48oHj0FQPLC3SJVHqRmnJbDne5X2UZqYW8GPusf8Aep6IWrKDoj/dUAfSomhcdq2F8pPuooPsKUkHooNHOLkMTympfJatgqh6imNFGeh5+tVzk8hlbSOgpK1PIUjgmomtQenNHMhcrKFFWms26io2tpFp3QrMhqUTyeSYd2Yyc496YY3HY0hB9KYJtAaSjmkzQIcWbbtycelJmkzRTFcKM8UlFAC5oz6UlFAC5oz70lFADgaNxptFAD91G7NMopWGPzRTM0uaAHZozTc0ZoGW7S5W2kLtEJOMDNQu+92bGMnOBUdGanlV7l87ceUdmlBpgNKDg0xI7Lw74Pl1ONLmd9kJ5CjqRV/xRb6RpmnfZYVTz+gA5I9zXMp4p1SOxW0juDHEBj5Rg/nWVJO8rlnYsx6knJrz1h606vPUlotkj0niKMKfLTWr6jlO5wB3rtPD1kAFJ61xEb7XBrrNG1mNFALYI9arGxm4WiVl8oKfvHd+cttB1xxXGa/rRYsiNS6r4hDRFEauPuLhppCxOa48Hg3fnmd2MxijHliLJOXbJqIvTM0ma9hRseDKbbuP3UbqZmjNOxNx+aM0zPNLRYLjs0UgqWKMuwApN2KSbYwKT2pCpArah08CPc1ULtFRsCso1VJ2RvPDuMbsokYptPIpuK2OVobS0uKUCmFh4YeXt2jOetMoxTgKRW4gpyqSacEp4wtS2Uo9xAoFPAApB604DNSzRIkTrxW7pKncKxoUywA610+kWxwDiuPEzSid+Eg3I1o14BqeMEkU9IjtAxUwVLeMySkBRXjykerYeoCLvY4A9awdW1gHMMJ/GoNU1pp2MMGQvTisS4cQRFmOXNdVDDaqUjCrWSWhQvpSznJ5qiTzT3YuxJNRmvahGyseFUnzSuJSUpoAqzITk1IkZP0p8cOeT0pJJAPlWpvfRGihZXkIzLGMDrUDNk9aCc8001SVjOc7iUUUZqjMUDJpSvFIpwaVm7Uilaw2iiimIKUdaSigBTxSUZooAWikooAkSQqRVqObpzVGnK5FTKNzSFRo0GAcVRmj2mpY5sd6JXUioimmazalG5SNNp7YzTK3RxsSilpKZIUtJS0ALTl600U4e1IpDqUHBptFIaLAO4fSkBwaYjYNSEZ5FQzZO6JEkIqYOGXFVKkRsGocTSMhJkwScVBmrp+dcGqki7TVRfQipC2qG5o3e9NoqzAduNG403NGaAHbjS7qZmjNAD99JvNNozQA7eaC5z0plBJJyetOwD95pQxPeo81NAMmk9BxV3YTLCm72HetRLRWXpVa4simWXkelZxqRbsbSw8krlMyP60hdv71DDB5FNrU52Lvb+9Rvf1P50zNBNOxI/e3qRRvb+8ajzRRYLlgXMgiMe47T2qPeTUdLmiyG5N7jt5pNx9aSjmgQu40006jBPFAWI6XNL0pKYgzRRRQAUZpKXmgAzRRRzQAdsUtGD6UBGPQGgAzRnjFPEEh7fmacLWQ+g/Gi6HZkWelHNTi0buyipltUHVmP6UroLMSyHzluuO1Xs+xqBAsYwoAHtT9x7Vm9WaLREoPOcUu48cVDvPvSeYQev5UrDuT7j6/pRnPr+dQeZ9aDIPTmiwXJ8/7IpAxxwB+dV/PUdx9BSG4Tjk/lRYOYtbsY60b+epqkbpRx81NN2cfKv50+Vi5i/v/ANrGaFmXd94nHWs4uWHLHntUsfA+Ykd6TjoVGepaubtmwkec1CsUkg+clcnkHk0B8nKjpTw5PY0JWVkOUuZ3Y9II05wSfepg2OBUO9j/APWpQW74/OlYSZNuJ70ueeTUW4/3vyo5/wBqlYdyXeMYyaN+exqPOKXd9fwosO5IpPoacckDCdKhDehOKXJ/vfrRYLkmTjGD+dGfaowT/eAo3HONxosFyUMP7tLuH+RUW89eaN59DSsO5MDnocUbgAahDfNyTRuA7GiwXJSVOCe3oelOXLdATjvioN4Pcip0umRAoCt79KTT6Di11EMm0+9G+mM5dizNkmkz7inYTZJvxwAaTcc5OPbmm5HHOfxpN3vRYLkgPPJP4UhJP8VM3D15oyOuKLBcfk54b8MUZYj72PqKZvH40B+eM/hRYLkgY9dwpd30/God+T3pd2ewz9KLBcm6+g+tG76VBkemKXf9aLDuSl/Q4+lRswbpnGOtML896gkudrFRwe5oSE5DizbmVmz2zjrTGTChXHOOuajWQF+QdxOTTyBncSc9ck1diL3GSQNkMpyw7Y4qW2Uq5d35JyFz0ppfDAckZqFyclmLY/hwcUb6C21NJXHTIOevNP49eazon2/KWYN9KsGXC/M5XHHSpcS1IsBvc/hS7uepNVhOpOASf5UGRcckAe5osHMWd30/M0ofk8gZ9Kq+ZFn72fxpQ6EDGfzpWDmLIf8A2jRu7c/lUGRjqfwNLx1DdPWiw7k29s8Uu71JqDcvQmkyoPp+FFh3J/NUf/WFJ5xz0bHvxUQIPc59qDjrnP60rDuyXzN3U4P1zSFuMg4NRll6DJ/DFN3kHpTsJyJQ5/vE0bm6lc/QVFkZHA+lG8nt046U7CuSeYg4PB+lL5i4zu49jUYLehH4UrZHX+VINR+RjvRuAqLfR5n+cU7CuS+ZxtH5U3zTUfmfX8qPOPYGiwORJ5jev4Um9/UH8aj81jj5TQZDn7oosK5KHb0JpN57j9Kj3/QGgOemc/hRYLkm/jlf0oLk9qjD89aTd7miwXJQx9OPpRvPXb+dRbvQmjcfU0WC5LuP92jkDOKi3N6mjecc5/CiwXJNxHUVtTQWi6Mrhk3bQQ3ct6Vg7/xpDIcYycelTKDlbU0p1VFO6vck3e9GQO5NReZ70u/3q7Gdx+76/nSFjnGPzpm+jf70WC47cf7uPwp3nMo2gjFR7j9aTI70WBSaHb6N/pmmYX0pOhosFyTzT6Cl8z0H6VF+dBYZ560ikS7+x/UUh2nnap/Cot4HSkMoA70WC6JNq/3R+dJ8o6Fh9DUJl96aZD2NUkQ2WOR/EaT5+Crn86reafU0ecafKLmLG+b6/iKQzSgZAXHrmoPPpPM46ZzRYXMWDM+cYwfc8UCViOSPwGaq+Yo56fSmMpY7gcHHenyi5i9vGcZPuMUfQ1mHcp5H4ilMh9CPoTT5Rc5pZzxj9KaRn/8AVWcZT2Lf99Uec3qfzo5Q5zQMS9waYYVJxziqfnv69PenfaX6Ek0crFzIsfZ1PQ0z7OP71R/aPQEn3pRcseD09qLMLod5B7GmmE0/z/XGKPNPUjAo1HoRmLFN8upt5PYCk3+1FwsQ7CKTaalLjuDTS49DTFYjwaOacWFISKAEooyKKYBRRRQAU4CkFWbW3e4lWNFJYnGBUydldlwi5OyIhGT0BppGK9DttHtNE0pri9VWkK9G/lXBXUiy3DuqhQTkAdq56GIVZvlWi6nXiML7GKberK9LmkozXScQuaM0lFA7js05XK9Dio6KVhptEpkZupNNJptHeiw3JsXNLSClIxQIKM0UUDAGnCkopDHjrWrp8AJBNZS9a1bW5WOPrWNa/LodWGtzXZpXEgiiwPSufuH3uatXN0ZOBVE81FGnyq7NMRV5tEMxSYp9Jiug47DcUu0ilHByKU8nmi4WEVc1IFAFNGRS9allrQUn0oFKFzTwoFK5STYnJPSpFX0oA4qxbwtK4UDJqJSsjWELst6damaVQBXc6dY+XEuRVTQtI2Rh3H51e1PV4rBDHFhpPT0rxMRWdWfJA9mjTVOOpJd3Vvp8ReVhu7LXH6jq8+oSlVJCdABUFxNcahOWck5NSbYrGLe+C3pW1GhGnq9ZEzm5eSI9iWsPmSH5vSsS6uGnkJJ47VJeXj3MhJJx2FUzXpUqdtXueZiK3N7sdhppKXFSRwNIeBW97HIotvQjCkkAVajtwg3PUyxx26bjgmqdxcGQ46Cou5aI25I01eW4TT5+VeBVYmkJpK1UbHNObk7sCaTNFHWqMxKKDRTEJRRRQA+kpSKSkUTwQiU43YNWG0yUDKjIqirFTkVYS9mTo5rOSnf3TeDp2tJEUkLxHDCo6mmuJJuXOahq1e2plPlv7oUlLSUyAoopKYC5oJPrSUlArgaaaWkpiEopaSgkKKXHFFAC0CiigYtLSUuKRQoqRGxUdKDik0VF2JqcpwajU08VDNky/Kbd7dZIztkHDL61Skw31oNMJqYxsXOXMREYNNqRhmmYrVHM0Nop2KTFArCUUuKMUxWEopaKAEpKWigBKfG5RgRTKUdaGCdmbNrcBlAqzIVZayIW281YMxA61ySp66Howq+7qVrtAGyKqEVYmfdTIghkAf7uea6Y6I4qi5paEJFNrbutLgFr59tMCAOVJrFIwaITU1oTVoypuzEooorQxCiiloAKv29os1m8gPzL1FUQKu2N19mZgy7kYYIrOpe2htR5eb3tioeDikzUsmC5IHGaAtVch6MgxS7fap8AUoIHbFFxWIBET2p3kNU28DvS+aB3ouwsiH7O1L9mb1qQzY6Gm+caLsLIb9lbswoNrIOhB/GlMx9aTzmx1NGoaDTFMv8ACfwo8yRepI+opfOb1pGlLDDc0xCiVu5NHnN/CTj3pny9wR700jng5osFybz5ByVzR9oc9AKhyR60bjRYLk32iQUn2iQ96iznvSfjRYLkxnc9W/SmmV+zGoqWnYVxxdj1J/OjdnqT+dJtY9qeInJxigBmST15pakFu7c5FSi1bH3h+IpXQ7MrjNPVGPI4H0qX7O4PY+4NHkuT9z8c0rjsPZIlj5c7/QjrTPOAGCox6UGGUnp+ZpPs0hOePzpLzKbvsiQXKdMMKX7SnBO6ovszkdRj60n2aQDpn6GiyFqTi5B6Zx9KT7Ug/vGqbKVPzAg+9NNPlQuZmiLodsD8acJ1OMgkn05rMp6sFH3mB9hRyhzs1BN3AOPpR5r9l/EmspmbGd7H603zG/vH86XIHObCyHHzYz7U4yYHOaxvNfpub86cJXzkM/1o5B85r+aAPvYpRJnncPwNZHnMfvc/UUm4H+Igj0o5A5zY39OaXzew5rJEr9BKcf7VSfaJcf6xT9DS5B85pB27gUeYf7v5Gs8Sy4yZlB7elIbmcHBcZ+nFHKHOaG8/wox+hoDr3BH4Vnm6kXHzY9aabpjjJ574FHKHOaXmJwMMM+1PDLgYrKW7kU84weM45pWujkbXbHc4o5A5zUDD3o3fWsr7Sc58xzj1FO+07s/vH/HpRyBzmkZMd+vvTfO9xWYZ5FOVCnPpzSC5kzgnj2FHIHOagmB79O4p3mA1mi54Ixn3IxUZnccr/OjlDnNXzB2JpPNPZufpmsk3EnZiPxpftcv96jkFzmoZW9c/hSea3rxWb9plx/rDSm5f+82fTNHIHOaG9v7xqoGRmJGc859MVXM7ngMT7YqSBJPM3bcDoc0+Wwc1x5BOHU5J4IpB5gYcMT/dHerCwqFwzbhTwigcE49KVx2CznWN0eVQVDAkYzVjW5Lea9M1su1GAwPX8KgZ0wF44HSmHy+NwqOX3uY19paDgVG3IRgtjrjNTLIM8jDHjk8U2VOcq24dSO4qs3DdfetLXML2NGSXyWU8EEdPapUmR1yOPY8VnrIpZQV47U4yKvUd/wAqXKVzGhvUdMfhSeYOm41SW6T7pzipFuIzwGpco+YsbznhgKUyP/DjPqahEi9utKHA7mlYLkgklJwUGPXNLvqPdS7vr+VFh3JVfnjtQ0jdDmmhsd/0pu4A+tKxbdkKXNG49ORTNwzQG+tOxFxwY9KUsewP50wt9aXJGRg0wJFdlbPNWDIGXpz61S3fWlDkdKlxuXGdtB5I3e3rSbsfxU0sPWk3c5yc07ENj9zHpRuPpmmbhRv/AM4osFxwb/ZNKGz14+tR7xS7h607CuO3f5xQWOeo/LFM3CjcPWiwXH5oLc//AF6Zuo3fhRYLj8+9GSKZu96TdiiwXH5NJmm7vak3cd6LBcdmlB9TimZzRkU7CuOJGfvZpWxxtBPrUeRRkUrBcfu5wBj8aNx9KZmjNFguPyaMnp6UzJ9aM8daY7j8/Wkz6GmFqNy/3hSsFx+8+tNLUgkRWyeR6E02SVGPyjA9KLD5tNxGJ96YSfegueuOKjMvXAH41SRDkKSabk0hkY+mKjZjnqfeqsS2SbqQsB3qIsepNG7n3osK5IX9KQsTTPmbsacEfHTFACljmk3FehpfLPc0oQdwTQAB2zyeKdlM8AHFJ8o/hFO346AflQMTah6YpNqHjB/CnbzRvNIBmxe2c+9J5R9vzp++jeaeoaDPLYf/AFqcBgcg596XfRvpAJjngA/hRk570u4UbvegYnOeeaUsemDRn3NJn3NABhj24o2mjPvSbjQAbfejaO2aNxpNxoAMY7UfhRk0maAFopKKAHqMnFdz4X0+GygOo3WMAZGa4ZH2MD6Vo3Gs3NxbLb7tsYGMDvXNiaU6q5Iuy6ndhKtOk3OW/Q0PEmvvqlwUQkQKcKPWudJyaUnJpta0qUacVGJhWrSqy5pBRRRWhiFFJRQAoooooAWiiigYoOKM5oopDFHNLt4zSUuSaQ0FKKKKBiinhj60ylpFJj80oA70wU6kUheKMUlKKQw20BacoqeNM4pN2KjC5AEParMNnJJzjA9TV21tA7Dirt06W8Hlpjcetc8q2vLE64YZJc0jDZNhwOcUmDmpSCx+tSw25dgADVuVlqZqF3ZDIoi7AAGur8P6MZJA7rxUekaK8rqSvFdpFAlla8DHFeVjMX9iJ6eHw6j7zKOo3gs4PJh+9jFco8L3EpeQ9T3rW1GdFZnkbFcxfauWykXA9aWFpSt7ptWqRgveLVzdwWaYTBesC5unuHJYnFRSSM5yxJNMALGvVpUVDXqeTWxDqaLYSgKT0p4UDrQXx0rW/Y5uXuPSNV5Y09rgKMIMVXyT1ppNLlvuXz2WgryM55NV2OTUhNRGtIo55u4lJS0lWZhSUtJQIKKcqFzgdqaRg4NAW6iUUtJTEX3tiB0qs6FTXQyQjbWPdLtY1zUqnMd9egoq5SozQaSug4haco5xTaepwaTKRJ5JI4qNoytXImBFLIqkVnztM3dNNXRnGkqWRcNUVao5mrMKSikpkBSUtJTEFJS0lAC0UlLQAtLTaWgBaWkpaQxwU7d3bOKKTJxjPFLSLHA08GoxTgaTLTJVNDLnkU0Gnqag0WpERikxUrrxkVHiqTIkrDcUYpcUUybCYpMU6igLDcUmKfiii4rEeKQ08im1RLG0UUUEk0bc1MTlaqA4qZX4qGjaEtLDW60ypSuelNaMgZxTTJkmM8xwu0MdvpmmGlNJVIzbbEopaSmSFLSUUALSg0lFADg1LuNMpaBliNQwyabIMdKjVyvShmLVNncvmXLYbk0maWjGaozEzRTsUoX2oAZg0YNShacE9qLhYhwaXaTU+ylC0rhYg2E0eUferG0e9LtFFx2K3lGjyW9c1b2+9Gz60XCxV+zk9sU4W/vz9KsYOOtH50XYWIREo7jineUF6Lg+p5qT8P0oyR0pXHYhdJTxjI+tR5YH5wcfyq3k5/8Ar0c0XFYq+YQOMHFIJSCDg5qyVQ9VB/Cm+VH/AHcfjTuhWZELhhj5Qad9qP8Ad/WneSv8LEfXmk8kgcHn1o0DUVZnboopfOwcH9KXaAMYNLtU9RxSKEE6k96XzgT90n8KNo7L+VIc+px6UBqIzK4w2SKi2JkkDOKbITn5TgGowxyMVSRLZZIVWwABzTwkQ4K1ArOwICk5p6xS4PGB6GkMl8qJRyM/U0COPsg/KmiN/wDZB+tNdJ1GeoPcHNICb92BkkCm+fEtVlL7sAnr0qdIAeWPJ7CiwXA3S/woT71G0iyjHlde4HNWBEi9FGfen5I9BRcdmZ4glY8Ixp4tJT1AH41dyRjrQDzzRzMXKiutmQOWz+FO+yR++e+TU+4DsaNxJ6GlzMrlRCLZP+eYP40vkRH/AJZAfjUqtzjoPpSgscYzii7DlRD9ni/uH86PssXQI351MfU5oLKPU/Si7DlRB9li/wBr86T7LDjPzD8amyT04/DmkwBnPJ9aLsVkQi3XPylvqelP8gNwWOPbipN2OMmgYx92i7CxH9miHUN+dL9mi9D+dSDj60ZY+tF2FkRG0h9GH41GbIfwyEfUVYG4dT+VGSO9O7CyKv2Ju0g/KmmzkB4wfoaufnRRdi5UVVtnHoPen7Jh/wAtB+Jqf8aXOOoB+tF2OyIAkuP14FGyTj5SWqfjHIoyMdaVwsR7XIztbNRukh6K3tVjI9aTP1ouFiq6SMw+V8VH5b4+YHjsavZ96M+5p3FYo+WeQe3Smuxbr2q+cEc8/hTDFEeSlO4NFDtSk89asm1Qn5WI+tNNoezindE2ZBuJ7k4o3H1qY2p9/wADTTbuOmfxFF0FmMDt2J/OniaQfxmk8pxyBn3FGxueOlGgK5KLmRepNJ9qk7nJqPZn149qd5KEZEhpWRTbHi8b0WnC8XupqqY2B4wab0607InmZoC7jx94ipBMv4e1ZfIHQgUBvWjlHzM1PMU8Z60F19z9KzhOQMZ6UeZkdTS5R8xo7x70bs/3qpjONxYn8aYXbJIf9aVht2L+73oyPWqPnuf4j9aUXLD6+pp8ouYuBh70oPPeqhuCR1yab9o45U/nRYOZFzd70bv9r9KqfaR6Gl+1Djj9aLBzFrNG6q32kf8A6zR9pXpxmiwcyLORRuqt9oXoDzS+cMcsMe1KwXLGaN1VjcKD1zSfaAO3507Bcs7vak3A1WNwP8ik8/jr+lFhcxZ3HsKNx9M/jVU3BHTrTTcP7UWDmLm8+mKTeT3qoZ2HuPWk89/71Fg5i5n60hdVPJxVQNI4wM/41IkTfxfrzRYLkrOvdm+oNMZx33fnSqiDjGTUmFH8I/KgCuX44FKN3YH8BVjI9OaMjvmi4WK/lytj5T+JpfIkPcCp+lHP/wCui4WIBbHqX/IUv2dO7NmpfpRlvWi7HZDBBGDwM0ojA6KPypefSlzikGgm2jbShvXNG/06UDG7aTaKfn0pMn0H0oEN2j0pNg9Kfk9sUZOcAUAR7BSbKlNFMLEO2jaaloouFiLBpMVNj2o2/Wi4WIcUYqUqfSmlaLhYZikxT9tKEJouOxHijFTiA+9NePbS5kVyNakWKSn4pMe1Mmw38KKcQaQigQmKKMUUAFFFFAwoJoxRigAooxUigKNxouNK40oQuabTmJY8/hSYpA7dBBS0uKMUwEpaXFGKQ7CUtLRQOwlLiilpAFFLiigoBS0ClFIaCnCkpQKRSCnAc0Yp6ipbKSHIKtxJ0qui1YQkDArKbOmmrblxJ/KXA61A5aVsnJoRC5GBmtWw0t52GRxXPKUaerOuMZVNCjbWLzuAqk11GnaGse1nHPpWjZ2EVog+UFq0rSPfJmvMr4ty0Wx206EYK7J7K1SGMYFZ+u6lFZQEs3PYVqXlyllatK5wFFeV61qUmoXbuxO3PArHB0HXnd7Cq1eSNytqGpS3crEsQuelZxOacaAuBuPSvooRUVZHjznKbuyMjAzSA4pWbJplaIwe+gpJJpKKSmK4pNIoLMAOtIasWsyQy73G7HQUnotBx1epJd2QtbZGdv3jfw+lZxqzdXL3Mpdz16e1VjTgnbUmq4uXu7CUlLSVoYhRRRQIASpyKQnJ5paSgAp8aF3CjvTKcjshypwaGONr6nSSTKE61i3b7nNDXZI61WeTcSawpUuU7a9dTVkMNJRSV0HC2OzSg02lFIaJVcr0NP8AONQilzUtI0UmDHNNxSnpSVSIY0im1J2ppFMlobSUtJTICiiigAooooAWlGKSigB2MUUmaWkMWlFIKWkUhRThTRTgKRaHCpkGeKhFTR9aiRrDcUDgg1CwwatyJjDCqzjmlFlTVhlFLikqzISjFLRQAmKKWigBjCm4zUhHFM5B4ppkNDCCKKexz2puKpENCUooxSgc0AjoNN06G5td5OW7+1Q3mnmHOOnrVCzvpbN8xtx3FaMupC4TkYNcco1Izv0PUjOjOnbZmLKm1qhIq5PhiTVbbzXXF6Hm1I2egyipmt3VQ23INR7ad0ZuLW42inbaXFMVhlGDTwKXFAWGAVZisppYy6ISB6VEPpV+w1BrQ42hk7iom5Je6bUYwcrTKDRlTggg03aav31xHczF449o9KqgD0xRFtq7FOKUrJ3IwlKEp/SjPSquRYQLTgKM0ZpAKBxSjNNzS7uO9ADqMmm5ozQA7Jo3fWm5ozQFx+c9Mikyc96bn3NGeOaBD/rRznvTM4oLj1oAfk0mT6mmb/T9KN5z7e5osFyTJ96PxqMtz94UE5/ioC5Jx3pMj3qPOP4qCwHrTsFyTn1pPm9QaYW9B+tR+YT0BosFyfcw6Um8kcMPqe1QFy2ASaBGzH0FFhXHmUA8FifyFIDK/A6U5UUdsn3qTcM4oAjEH99s+wqVUVei0Aj1oHPekMUNS5JpOgzR+FAxQaMkHIz+dJ+FHWgBwAbkAA0hUjqDx2ox708MCME8UhkWD2BJp3zHpmhuCc0me+aYh2W9TS5PqTTcn609Qx9aTKSuPCs3FWoLGab7qnHtVjTLF7qUAA4rv9M0OOKNcrXn4rGKlp1PVwmB9ouaWxwR0OcqDsqrLYTw9Rgewr13+zYtv3RWdf6NG6H5RXFTzS7szsnltNr3TyhoyDzkn600g/3Tn16Vt6xYG1lOBxWM2a9inUU43R4tek6UuVjPm9Bil59sUc0n1NanOO9OKMjNMGfVfwpCxBwMH60ASZGOlGaQZxkjFITjvQA4Y7ilBGDgfjUe760Z9qBXH5FH0pmaXNAC5HvRSZpMn/8AUaYDuOcn8KDgHgYppJHv+NJknjGKAuKCeO9BbPY0maQ0AOzznmjOe9NA+tHFAh34nNJ09fzpMCg+386Bihx70obIpv4Cj3NAhdw9aM+hpOlLn2oAM+1LSZpNwoGOyfWm9+35Um760Z9uPpQIdx7UnGc8flTck9qMk0APz759qaQD6Z+lHvRnigBNg6FAfwpPLjI5UfTFOzikP40AIYkIHy8fWmmBMZyw/Gn5JzRk896YOxEbdezGm/Zv9v8ASpsg96M+oouxWRAbY/3h+VNMEg9D+NWc+lBOf/rU7isimyMPvA03BPTmrnQUworen8qdxWK+w9qNrVKUPYbsetMII5557U7isMwR2p2D0JoyfekyR04oAXHHU0YGeSabmp1jjlGFyrD1PBpMaVyEkds0malEI7t+VPWNOy5ouFivyegzT1hdu2PrVkcegpaVwsRiAYwWJHoKeqIvRRS9aKVyrC59/wAKKSlzigYY9qBn3oyx6GkyaAFpcjv/ADpvzZ70hJPrQA/PpR39vemc570uTQA7n8KOabk0bj6CgB2fajjPem7s04jGM55FIB0cQkdVAHJqW8hihmCx9hzRbkRkuew4qCRy7ljnmp1cjV2UPNiY9CfzpMt7n8aOfejJ9DVGQuW96Mt/k03P1pcntQAZPpRn2NJzS5NABmlpoNSxpuPFDdioq4irn/8AXVmG0aTBxV2y05pSCQcVvQ2KRJnFcdXEqOiPRoYNy1kcy9iVXOKpumxsHNdLfMiqa5y4YF6ujUlPcjE0ow2IeM9DUiFR1qLNGa6GrnGnZlgyrjioXbcaZz60c+tJRSHKbYv50mKMe5pMe9USGKTApce5pMUCEwKMCikz9aAFwKTilyfWjIzwKAE6nApcH8KN1LkZ6UDsJt96XGfWlyKMjrSHYTFGKdketKKLhYaqZPNKU204HBpSc0rlWViPFLinUu3jOKLhYZijFPxRii47DMUuKdilxzg0rhYbijGKmIUKfU1Hii5TjYbSilxS0BYQU4UCnAUhpAq1Kq0KMU4dazbNoxsSqtWYYC5GBUUI3MK3LCNOK5qtTlR3UKakx9lp24jIrpbWBIEGBUNsihRgVaxngV5Faq5vU9OEFFaDgxdgorWtUCR5rPgjwQa0A2FwOlcdR9EOWpz3im4d4vLB+UV59MpLGu+17DIa4qaP5jXsYBqMLHHioXsZ5XHNROxJxVmVdoqqa9SOp5VTTQbTadTe9WYiUUUUxCUqjJwKSnxHDihgtyY23yZqmww2K0pJwIsCs1+WzSptvcqskthlFLRWhgAUk4p5iIFPiwOtPkYBTUuTuaKCtdlQ8UUp5NJVmQUUUUCG5pM0lHeqFcWikpaQBS02lFAx4ozSUo60ihwUtTvLPpU1uoJFaAtQy9KylU5Wbwo8yMYqRSVpS2ZHaqTxFe1VGakROk47kBFNIqQ0w1ojCSG0UuKKZIlFFFABS0lLQAtFJS0hi0opKUUDQ8VJGATg1EKeDipZpFj6enWm9eacvUVDNluXQu+H3FUnXBxWjbDcuKrTxYY4rKErOx0VIXimVMUlPIoxWtzlsMxS4qRU3A4FIFouPlGYpMVLimsOaLicRlNIp+KaRVIloZikxTiKSqMmJijFFLQAUoOPWkooAUsTTaPwooE2Tw3LRcH5l9DU7xwXKbkO1sdKo0BivIJFS4a3RpGrZWlqhzxmNsEU3ipVlD8P+dRsQG4PFUm+pEkt0JS03NLTJFopPxozigB1KDg03f6ihX56UholVc9KcYiBVi0UORVuaABeBx61jKpZ2OuFDmjcyCMdaSnyjDe9RkN6GtUzmcbMXvRmoyWx3pu5vWqIZLn60mRUW4+tNJJosIn3fT8aaTj0FQ5NISadhEvme5pd+e9Q0lOwrk+/3/Wk3j1qGiiwrk3mAd6TzFPWoqM0WC5L5g/yKTzBnp+tR5ozRYB+89qPMamdakWM9W/KgBNxPB5p4jJ9qcqhegp2aVxgqhenX1p2abmjNIY+jNMpc0APyfSjJ7imZPrRn3oAfn3pfxpmT6mj+VAx+TRgn+I/hTe1LSAXbkjOanWBjyAahQ/MK2rWFXQH1rOpPlVzoo0vaMyHQg5K03kdq2rmxyvAzWTLEUOCOKVOopBVoODGA1LECzD3qHpU8BxIufWqlsTTXvI7rwxZrhWIrt4wFUAVyfh2VRCvSuoWQYr5XGNyqM+sopKCSLGainI2HNJ5wHes7UL9Yo256VzQg27It6HHeKnXeQOua49ia1dbvvtNywByKxmPtX1eEpuFNJnzePqqdR2Fz70mfSm5+tGa6zzh2aCT9MUzNGcUATqx296YxwaRWNISc9qSWpTegufc0mT602iqJHZ7UuaZmjNAh2fejNNzRn60AOyaM5puaCaAHfjR1puaTdnvmgBxHvRTc96Tf6ZoAfzS/So9x9KM8dKAuPo49aZuo3HPQ0AOz9aXJ96bn2NGaAHZ+tGTTcikoAdmjNNzRmgB2eelGfrTM0ZoAfmjNNoz9KAF3fWjOabmjPNADvf+tHFNzRmgBaM9s0mfWjNABz9aM89TSZPpQeRTELmg9qb9OlGaAHBivTg00gE9MfSkzRmgBGhzwDTDEwGcZqXpSfWmKxDj2pdwCjA56EmpTg9QDTCq/wD1s0AKvIB5wfang468VCjbTj1p+frQwJc0ZqMDvzS4PbikMfk+9GTTQTS5oAXJozSZNJk0DHZ+tAPpmm5/yKX8KQDs0Zpo+lKBmgEOFL+FOSPNTrASKhySNY02ytikx2q4bc+lQvER2oU0xypNEFKSTjjpQQQaTcaozFyeO2KACTRvPTtU0B3SKCBSbsVFXdiWG0kk6Uye2eL7w4rqtNijMeSKpauI1BwOfauOOJbqctj1J4KKpc1zmiKbtB7GntnNHNdlzy2hmD70YP8AkU7B+v40YOadxWHJGWOP6VtafYbyC1ZdtjeK6K0nWJBXJiJySsj0cHTi3dmvBBHBHmqd7frGpANVLrU9qkA1g3N20pPNclHDuTvI7q+JjCNokl3emRjzVAvz3pGJNNz9a9OMFFWR4tSo5u7HbqM0zNGauxmO3UZpvNH40AOzRketN/nR9aBi5FJuFJzjvSc0CF3emaTJpQpNXrfTy6iSUhVqZSUdWVCnKbsihgmlxirNyIlbbFzjvVcCmndXCUeV2ClC0Y96XmgA2ijHuaKWkMTb70YIpaWgdhuDS80uKeVwuTSuNIjp244xmj8KXFAxM0c0uKXFILCUc0oFOC5NFxpDeaMVObd1XcVOKixSTTKcGtxuKUClxS4ouKwAU9RSAU8VLZcUOoFFKATUmhIjkHitbTXZpFrLjjyRXRaRaHcGIrmxEkonbhoycjoLYEIKtqOelRIu1RUq14cnc9QsxsAw9KmZsLVWIktip2+7WTWoGDrB3Zrlp1AJrptVPJrmLtsV6uE+EwxFrGZcHmqpFTSnLVDivWjojxKjuwSNpZFRRyTgUk0TQyNG2Mr1xTkLxtuQkMOhqNiSxJOSapXuZtKw2kpaQ1RAhpASKWkNMQFieKZTqSmiWJRiiimIcOhppOacDgYHem4pDYmKMU4KTUgj9aLgotkIFKRVgwkAHFRlKXMU4NFOlpKO9anOLRRTlUk4FIYlFOKFTgjFJQO1gpRSUtIZZgfawratZVKgVzynBzVqC5KEc1hVp8yOuhW5XqdC0SuvSqFzajB4pYb0EDJp0twrLXNFSiztm4TiYkybTUBq1cEFuKrGu+L0PJqJJ6DaSlNFUZCUlOAzRimFhKKMUUAFLSUUALSim0tIY8U8GogacDSaKTJ0Pangc1ApqZTkVDRtF3NKyPIqe8tyPnA4NU7M/NW3CVmjMb1xVG4yuenRipwsc80eajK4rUurNonPHFU2iNbxmmjmqUWmQDigDJpSpFAqzKw549gBznNQkU8k45NNoQpW6DcU0jipNtIwqkyGiA0lONNq0YMKKQ0lMQuRSbqTmjBoELnmkzRg0mKYC7vakyfajFFAgz60Z9qKMHPSgAz6UZ9aNtG2gQbqNxxS4oxQAnPelBIFGD70uDjrQMmgmaNhWmsjzJ1rGAwavWk/ltg9KxqRvqjqoVGvdYy4VkbNRrOV6jNX7ko6ZFZjdeKIe8tQq3hK6JxNGw5WmsIG+tQUVfL2Mvat7oc8K9VP4VAykHpUmaM1aujOTTIaSpSw6UnFUZjOD2o+X0NKdtN2mgAOMDg0lOCnOKNtMQ2in7aTaewoAb1pQpNO2ZOT+VPHFK4CKuBTqKKQxaM0lFAC9aKTNFADs0U2jmgB1Ln1pvPvRj/OaAHZozTc0ZoAeDRg03NLk9OtAx4ODWpYXYjIBPFZPP4e1KjlTms5wUlY2pVXB3R2SMkycGs+9tAcnFULO/aMgE8VqNOsqZzmuDklTkeqqkK0Dn5EKNg0itg5q5dx7skdazzwe9dsXzI8yceSR02j6yLchGNdVDr0RQfOPzrzBWIOQTUwuZFGAxrjrYGFR3PQoZi4Rsz0afxDEin5/wBa5fVdfa4yqE4rn2nZurGoy+e9VRwMIO4q+YymrIe8hY5J5NRk896bmjNdyR5UpXFJPpQT7U3NIaZI4k47Ubm6AE47im554/Ck3nPANMB+455BFBY+hqPe2eAfxpcnPpRYLjgc0uabnPYUUCHZoz7U3NFAC5pc+opuaKAHZpAaT86PzoAdmkzSfnRyPWgBeKMjtmkz7GjPtQAval/Om5PccUme2KAHfnRntSZHoaNx98UAHXsaX6cU3cfT86PpQA4n1pCR3H6U36UDNADsijimZPTHFLn3oAdketFNzijPFADs0ZpuaTNADyaTPvTc0uTQAuaM03JpNx9KBD80Zpm4+lG/8KAH0U3NGQaAFpKKM0AGcUbh60fhSZ9qYATQfxpn0FHIoAdntSE9Pak65waT60AD9uPxpoOO5p2QRgt+FNIA6HNMRIrH604N71D0PvTtx7/rSsMlzSc+lNyCODyaQtRYB+4U7d9Ki380oeiwEmRRmmBhTgR2pDQ8VLGuTUannNWYACaiTsjWnG7LUMOe1XEhHpTYF4q2oxXFObuerSpqxCYeOlV5YOK0ccVFKoxURm7mk6aaMKaPBqA1oXK81nt1rug7o8utDlYlORtrAim0c1RktDVg1MxJjNQXV6055NUsmgGs1Sinc6HiJyjyti5o70UlWYsM0ZpKKYEiPtINWPtjKuM1SzRuNS4J7lxqOOxO87OfWoST3FSWzosmXHFTXksLACPrSvZ2sNrmjzNlPNJmkpK1MB1Lmm59KKQDqMU3BpwoGhVUEgcVIyqvTrTQM1IIzjpUNmsY3RFn0pM09lxTKaJasGTmpGnkddpY49KjpKdhJtC0UUUAFFFFAC0Z5oopDFpaSloGPRthzjJpCSxyaSipKv0FpcUClAoGApQPypQue1OxSuUkNxiprbaJlz0zUWKcvFS9UXHR3NnULqF7ZY41APtWMaduJpKiEFBWRpUnzu4mKAKeFJ7U9Yye1U2Qo3IwtPAqZICe1WI7NmI4qHNI2jRk9imqEnip44Ce1acOmsxGEJrUtdEkcglcCuapiYx6nXTwj3Zl2Vi0jj5a6uztRDGOKuWWjeUo+WtJLEL1FeTXxXOzuhGMFYzFU+hpxUgdK0pIQg4FVvKLNXOp3NExkKEnNTSD5akRAgqte3CxRk5xS+J6Cvqc7q0gDGuUvJMsQK19VvN7kA1zsz7nNe5hKdo6nDi6vRELdaQcn2oPrSHpXeeWwc9hUVPNNNUiHqNopaSmSJSYp1ORMn6U7glcjxxmmnrUr4HAqOmmTJWG0YpcUvamKwmKcqZ5NAGakANJsqKF4HakLE07Zz604IO5wKi6NbMaCxGKmSAkZNNDqvTrQZzUu/Qtcq3Mmikpa6jzRakjYowYdqjFKDSZadjWAhvYuMLIBVCWFonKsMUxHZGBU4q6JkuUCScN2NZWcH5HTeNReZQpKlliMbYNRVoncwas7MWlBxTaKBEqyMOhp/ntUFFKyK52PZiaZRRTJbuJSU6jFMVhBwc0rsGxxg96QiigBKKKKCQpKWigAxRiiloGGKWkzS0DHCpENRA1InapZpFl+zPzitbJUBh2rHtD+8FbBGYq4q3xHqYZ+6W4ZY7uPY2NwqrPZFTwOKzvPaCfKmty1uo7uMAkZrCUZU9VsdEJxq+69zEmgx2qoRg9K6S4tMjIFYtxAUPSt6VVSOavRcdSkaTNKwptdKOJk0a5xxSyR4HAohIBq5sDpWcpWZtCHMjJYc9KZirssBB6VB5RrVTRzzptMr49qTFStGR2qM1aZi42G4NGDS0nNMkOaOTRn2ozQAY9TRgUUlMQtFJRQAuKSijigQfnRk0UUAHNLmk4o4oAXjNODYPemZFGRQNEpkOMZNRk+1Ju9qbuPakkNu4ufajd9aYWNNzniqsZtkm+ms3SmZozTsK4u45pM0GkzmmIXNPVvlxgmmDJ4xTgDjgUgH7h06GkLdqTaaXGKAFGT1oxRmjNABS03mjJ70AOz3ozmm5paAFzRSZooAXNFJRmgBaKSigB1FJmigBaWkoyKQxaM0maKAHq2KduTuOajoosO5MHRTwDVmG9KDHb61Qpc1DgnuXGo47F97rdVR2yc1HuoyaIwSHKo5bjuTSjNMzRmqsRceSaaTnvTc0ZosJsWkoopiAg9eaTkUUZ+tAC7j6c+tBJpvPqaXtQAuT6Yoyc0lFMQuaXNNzRQA7NGabmjNIB1FNooAXp9KOaT86KAFyfxopvHpzS0wFzz/jRmm0tABn/ADmlzmm0fSgB2aOab7n9KPwoAdk0lJmigBc/SjrSZFHFAC9qMU3INGaAHYpKTNHagBc0UmaM0ALRzSZozxQAvNJnmjNGaACijIooAKTP1o/WkJoAXNGTSbj6Um6gQ7d60bqbmkz7cUwHZpCe3ak7ZpKAF7UZwelNJNGTQAp56cUnSgU4HPqaAEz0o4oK96Qj3oADSjGOaQnigE0AO2r70YX3plFADjxSg03NAoGTIGPSrULMGqvA5V844q9sVgGWsZvozppRvqi7BKcCrazZxmsuMkGrCscda5ZwPRp1NC/54qGWcY61XLn1phDP0qVBIuVRvYguJM1UOSatvEc800RYroi0kcM4uTK4B9KMGrGwCmFfaq5ieSxATTd/NPfHpUZ61aMpaDw2Rmk3U0Hig0WC4u6kzTc0hpibHbqTdSZpM07Ei5pCxpM8UlOxNxd1LuplFAD91KGNMpRQMeCacCaYKeKllIniGWFdvZWOk2eh/a7j55mBwretcPGcEGrJuZZECMxKjoK5K9KVSyTsejhqsaabauyO5KtMxUYBPAqvirq2U80TSpGSi8luwqmetbxa2RzVYu92txtJSmkqzEKWiigAooooGLS9qSikMWlpKWgYtKKSlFIaHAVct7MyqW/L3qO1gMrjjgVrkLBGPXHFc9SpbRHZQo3XNLYzZIDEcGoCKnmk3P1qBiKqN7akztfQQcGl6nNAUmrMFq0hGBTcktWTGLloiFIy3QVZjtHbHBrWtdM4BIrSjslQDj9K5KmJS0R30sJfcw49PJxxVuPTenFa6wqvapFQHGK5ZYiTOyOHiijDpyAjIrYtNMjbGEzTra2LMOK3bODbjiuOtXfc3SUUJaaRHx8orYh0+KMfd5p8KhFx6U2a42jAOa8+UpSZzynKTshzqi9BVZnUdBUElwWNVpLkKMk0KDKjAtMwPJqrJOikgdapSXhbgdKzLq+IBCnmt4UWzRRtuX7rUliU85NczqOpvITz+FRXN0Tkk1lTS7j1r08PhktWY1atlZEE8jOT71TYHPSrhXd0qJo69KLS0PMqRctSrinIm9gvSnFKbjFaXMeW24x12sR1xTCKkaozVIiQ2kp1JiqIEqUEKhz1qOg80nqNOw1uTTcU/FAXNVci1xgFKBzT8UAUXGogBTs0oFNNSXawbvSkzSc0lOxNwJzSr1ptOXqKYkUKKKK2OQKWiigaHA04NiiipLTJRLvXa/PvUTDBoopbFt3Wo2iiiqMwpc0UUDCiiikAUuM0UUAgpMUUUAJSUUUxBRRRQIKKKKAFzRRRQMcKetFFSy4lu2PzitsH9x+FFFcdfdHqYX4WY85/eGn21w0LgqaKK1snHU5+Zqd0dJZ3SXMYBxuqG9tARkCiivNfuVLI9aPv07yMCeEo1ViKKK9KDbR5FaKUtBysQc1dt5uxooomrodJtMslA4qBoMHNFFc6k0dkopleSLjpVKRNpoorpptnDXiiI0lFFbnGwzRRRQISiiimAZpKKKBBRmiigAozRRQAmfekzRRTBiZ96UGiigQZpDRRQAlIaKKZImKM9KKKZIYJpwUfWiikA7ijNFFABRRRQAUUUUAFFFFABRRRQAZooooAM0ZoooAXNGaKKACiiigApaKKADNGaKKADNGaKKQBmlzRRQMM+9J1oooAWiiigAzRmiigAzSZoopiDNFFFABRRRQAUUUUAFFFFABRmiigAooooAKM0UUAJmjNFFABmjNFFABmjNFFAADRRRQAZooooAKKKKACiiigAooooASjNFFABmjNFFABmjNFFABmkoooEFJRRQAmaTNFFMBM0ZoopgGaM5oooAOtGPaiikAYJpcMf/10UUBYNp9aXb70UUAG0Uu0UUUhhhfQUvHoKKKAD8qUGiigY4NUySsO/FFFS0aRbRKsmamWTFFFYySOiMmO8zNWbe5VOCKKKiUU0bwm0xJXEhyBioDRRUrQqTvqMY1CzUUVpEwmQM2e9MoorZHMxaSiigYUlFFMTEzTTRRTJYUlFFAhaKKKACnCiigaFFPFFFSy0SjGeK6HRtEFwn2u8by7ZecnvRRXFi5yhFcvU9LBU4zk+boJrOtRyx/Y7JBHbLxx1auf60UVtSgoRsjCvUlOeo00lFFanMwooopgFLRRSAKKKKBi0tFFIYtOXrRRSZSNW0dY48jrTZ5i3eiiuay5rne5PkKbMTQoLGiitXscy1Zo2di0hBI4rcgt4oFHAzRRXnVptysevRpxjG6JTeKvA4pFu9/Q0UVHIrXLU3exMsm6rtsm4jiiiuarotDohqbNvGqAcc1sWkfGcUUV5tRiq7FmWURrisuafJJJxRRSgiKcUZ098Bwv51Racuck0UV2RikjYrz3OFwDWXPKWJNFFddJIzmzOmJaqjJk0UV2wZwzVxVXikZaKKq+pNlYjMYNRPHRRVpszlFFdhTCKKK3RySWomKTFFFMmwhFGKKKYgC5qQKMUUUmxxQHpgUgHNFFIY4njFRHrRRTQpDTSYzRRVENCgU4Ciik2NI//9k=
- data:image/jpeg;base64,/9j/4AAQSkZJRgABAQAAAQABAAD/4gKgSUNDX1BST0ZJTEUAAQEAAAKQbGNtcwQwAABtbnRyUkdCIFhZWiAAAAAAAAAAAAAAAABhY3NwQVBQTAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA9tYAAQAAAADTLWxjbXMAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAtkZXNjAAABCAAAADhjcHJ0AAABQAAAAE53dHB0AAABkAAAABRjaGFkAAABpAAAACxyWFlaAAAB0AAAABRiWFlaAAAB5AAAABRnWFlaAAAB+AAAABRyVFJDAAACDAAAACBnVFJDAAACLAAAACBiVFJDAAACTAAAACBjaHJtAAACbAAAACRtbHVjAAAAAAAAAAEAAAAMZW5VUwAAABwAAAAcAHMAUgBHAEIAIABiAHUAaQBsAHQALQBpAG4AAG1sdWMAAAAAAAAAAQAAAAxlblVTAAAAMgAAABwATgBvACAAYwBvAHAAeQByAGkAZwBoAHQALAAgAHUAcwBlACAAZgByAGUAZQBsAHkAAAAAWFlaIAAAAAAAAPbWAAEAAAAA0y1zZjMyAAAAAAABDEoAAAXj///zKgAAB5sAAP2H///7ov///aMAAAPYAADAlFhZWiAAAAAAAABvlAAAOO4AAAOQWFlaIAAAAAAAACSdAAAPgwAAtr5YWVogAAAAAAAAYqUAALeQAAAY3nBhcmEAAAAAAAMAAAACZmYAAPKnAAANWQAAE9AAAApbcGFyYQAAAAAAAwAAAAJmZgAA8qcAAA1ZAAAT0AAACltwYXJhAAAAAAADAAAAAmZmAADypwAADVkAABPQAAAKW2Nocm0AAAAAAAMAAAAAo9cAAFR7AABMzQAAmZoAACZmAAAPXP/bAEMABQMEBAQDBQQEBAUFBQYHDAgHBwcHDwsLCQwRDxISEQ8RERMWHBcTFBoVEREYIRgaHR0fHx8TFyIkIh4kHB4fHv/bAEMBBQUFBwYHDggIDh4UERQeHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHh4eHv/CABEIAZABkAMBIgACEQEDEQH/xAAcAAACAgMBAQAAAAAAAAAAAAABAgADBAYHBQj/xAAYAQEBAQEBAAAAAAAAAAAAAAABAAIDBP/aAAwDAQACEAMQAAAB5UjDCAYkklQg0I0kAyAS1CMKAaUtll+XDl6MoMpA8RQ4pY0pYxpI0q22xs6oW1IQOrVlmoK1dIkFAEoARVoYCksEIZFjhyWMtIxalNkpAxg2yw0r1EVqsRypLMhjVBZKx5fXSS1aR4aybsPMyquZXnWEL01mlQEFLKySRpISWGVkBhShmqoWrRIclDyg62SUKxLFNOFEmSwq2ydiHWD1fYS4SfoKquCDt3hTymnate1mixnqiXrSZtRzoVVql1BqRIy6KwwquGUGWUQ0pzWae2rIJa7UlXaEDYKrD0JCp0EhhjNlDVuO09E568L328YvXPJtZbvqfOdlfRNnCtsrpGse5mlwfW/pbl7c1ly6FWREFqUlV+MxQqiLdVEUiYJKJEpotlWZeJnZaxcw1u7DUt6RhU5FPTKMLIFscbew+D1XnuyDlJZ/LExthAXebCsp3ohe32LguZjX00uqbTl5nzn6U4euroyI9ZRK0vVKIzJVRdTSghg6NRMlCytquy8G8cqVjLktiivQwTTRrg1mMYx9TzOo4ejZTLjeocS9zW95AWbyYYUDV0Soawhq9T6B+aum89db1/YEy/M1O16nssASsil3HGORVrOLj5FCKCGWQ0WRqhU1bk4uaN7WXc9YiZiti4+Tj6zWltSRg9Xd94R9J41k69sWhjxjHvo6ZWNKUMICurRlNNFNP7niZmNfTUxMvDzjkXeeF6sdhNZsyK7heg41U0vXoBBRYTSuLqoINPmYWQPtrS3LoKrcbWBRl4zVixEDu45H0n81fSOXK530TQo41jZONsAUI8UswDUA4JXZZtycbJy/Qnr4eVjXhcE7fwxKSrbzkCxMteDn4OhK3TRJJQZXp7YRwyCjW1mszL8/1ee1xbsFPaxcmjG8QXrrKyK1ve+CdOzdN8H3IXzNi7np+zGFy6zVGRi6WDIrU8lpDYPH6xnXQVhy875FtOsazUwOjJet86qwc/A0IrLrIDCnvDkIrzgFWQupq70vLuy5eEVr05Vk51WWUpVfJo9DBRz9JZHI+vZdf4d9J6i3CU9jB0YaZNaAuRx3FyG47DnVva8fPwzWva4k2ug36EqeDcGpGrz83D3hVI3mKwq+zHySVpB85lbRbFlWFWoujjm5eN6PLdCXYwvAGSorrJ6NzvIL6Pu4L1AvS5X2kV82YXY+TriGytFyk7jGr9Kyasr4Go80r0/FxHUuikGR9DYeXhVXWy6zWrhAWahkU2SqFax4wRmWymDii6W5c/Kwc/n0tZei5eXjt+kJos9PCYVulVEDWd26/wAA7/h8/gf0b8+V5MsGzI+jOJ9wypwnsPB6oW92xbbbh88+l66avldK3Mvnzz/f13WUBmxCTRuN2WqjLxqqQjRWCUjy0iCwrbW9Xen5GVnXs9A5t0bnvfHhcinILeZV6xrxJ7BLzvRIpuI9r5i3OCs1npPUdD3vLX5frmfGf1pXkWZRJmU01V1VcF1jYNf6YWFNT3V3llY+VjZ1TTZRrKwRkemxLLKrBZ6riVxbQsJyvkY6mvcyNcYfWHjonuXeHbl9Svy6k9geRNHs+bilGEFZ2T4xj2J5Jn1x5AL138Z59ZPLJeqvjhjReqVR4ld1V42hHHEpvp1mqRmocMheu0TvuidSy7A2vajz10TRsHqtYzab5DbP5HWdFLxdP6VzTRvvk7lr2X3td6fpFa3rW86Rop6zyr6Erk2/aznl6/n866/XKek67tNY2Hz7fK570jzd8nj/AKLezXMNr1DoqeRuHhdMy8S8Du3G9HtbHt/nYeLUlOhMOyrWVdCysxhLSsv1Tl/UMa3TB8XVsOy+9oG81yybht7DWOgczK/m3ZdGbbdf3XRi6dpO66TWJpPUNYnUfoDivaE0HfdA2Erfe5V0StB6nzvZayfQ4d3CuV9V4d2xucez4e7lxHpHh7umu9E510MdT2zg/QWGxcj62XFamx95rBOgJZVV8XKqhcwjj7brJHpbcxhdK03yDXUH5eg9j5h5jV0PO5ca6BodQTo/ga2o9MHM5W1+zzw172084Suk4ehRM/ZtJE27ZpsTZNi5ySt3/ndldPwefVDl7vz2tDXYNF24aLXVqLdFSmpgpRLJXGzcvzb8vp0uee6GEaC6DVYDG57dg7wOsDa9LC2zy93bWztngDgPrW2JRNpOXUJpA0b82ykdXqv05NvGyXFqtXr8/wBG12bHbnWocq+geHJrxQ7nqSpya5NDsHKlGpRlUM0jVZk15eW51bn0FeQg2tmUZcNsmhuk7zxTZLPTNW16NN+58XPTde1MD6fo64a6UeZwfSHlFOmjmgHa/BwgnRsjmMLonPVZugZnNIPRuFbNo2s4pUbFVbEV76qVK1qUtToIWI71ks/0PEzsb9CyjI59K6cerWduuWvy+keZ6qaPEovx+/CxXCUOE1m1C1Ro41l6hUBtZBii6iI2QmZlx3bFmyohK4CkxcrDQZ2FnUcG3FqRVQVlNBBlNBBaylozvR8VsbzKqXTecTGxfN6di8z0aue/FXOnbl56eoHPlVeph6zSbY1NgapSy0rhkWPkDgzMoSzKxny0UtRoIrms2UrW1li5JRkpGlQNZaq2pkV1QSSjIKZlgu1Zi41WjnNgZGdbQ/nX+fvlY9dSLbjTpj3fM9Wjj1wJnMni1ev53TnjXnJStDkiqtjUXRUtxqK9FlQrRVM1lZeZhaslrsppKwmsuoLQMtCA0QZQhlRoCZ6zVxkHI9bxL869OgTOlsoCe/6Gs5fLp7mV4ewcuniYmx4OjzLMq9PIycqRV51/nbzf5709MAMEqR60Z63pzWKYUynw7atCwqgIlFYakkqB1ovWRMMpZIlj0MV9mK85d2KcuQuMKzrMC2vYyvAyOe/Xu8izOvZPn251n0eaEqxrqOvOtAms3mlaiOlFK0S+oIxgFSCJAJUElRhKMBppCKBggIlWSskQ4kGSmAFWNSYtlZmxqWq98WFm3+YR9arBFZq4jVctSpYKQ19KiIAWkMIFQzJJUBlAw1IYQhE//8QAMhAAAQMDAgQFAwUAAgMAAAAAAQACBAMFEQYQEiAhMRMVFjA1FDJBIiUzNEAjJEJFUP/aAAgBAQABBQJ3f/FwrCxsfbaFj2Cj/oa1YRHuhUk7vzko/wCMbgLCCyjzBO5gmuRCwiFhYR2J94cwGxTRynbG2EAgEQiNsLG4TMroinbE/qR94coHJhBO5A1Bq4VwINXCsJ2+FwlcKaOoTnLiWcp2x2P+IInfKzuGprFCs82Uo2mGqjYraweWQGp1tgOVWxW56kaZKuFpmRUWrG2VnOxf0/JX4Ox2PtDcb42dzYTG5Vps0iYrfaocMbkLCxvcbJDlK52mRBcRjkO53PuAI7AIBY2PNhMplxsdhawNG1wuMWE2XqasTWvVxqIzZDkydJao99uNJQtTByiSaEqmqjWvbfLH4QcMHlcjvj2Qggi1cKaNiijyBBMbladtAjsCJwL3qHgVaq+o7PJlcShy6serZLwyaNtSWgU0R1I3dsUUAn+yEAhvwrCwvwUdhs1aUtviv/K1HePGNR/XPKdgVQrOY7T90+uopzQ5uooH0MzPIAnbv5RyhyacrKyuJNOdnHrlFAb2+O6RIjUGR44WqJ/00V7vbhSXx61tlMmxFfof1kCoOF2dx2cMrCwqnt0thuHOR5W9VoyJmqicC9SzLmnlzyDYLRUvhkIrUkX6e4rK/Idtw7VO/MNwqQ64QanNXCijy0h101R8K0LUFb6e1VD1RWPZCtVU0Jo21pRyx3fYJq4uhTu55huFSQCwsbVNjsEFQGXx2inHWs34gPQ5TzBM7wn+JDWqmcVpeOuzNinOWUeYDdqofes7cSdyDaJ/M3stbf13+xjcIJv3Wf4pah+Iqd1hdkU7tztHI1N78eGNOQVTGUW9CFjYBEKj0fQIdSWtGZgvR9tqp/dDZ4cRapfwWmoeqHdyAT/t5gghyBZyG9A44bQP6sdCE7vjdn3WCt41qV+oGTa6gR2x7GEArNH+onod9a1sUnd0ExBO+3laEBzsTO1dNOC1+WP7lux2atHShxDbUEL6Oc4dccg5QE1vXSMPgpDbUUr6q5IoJoRVT7eXCJ52d+LCkOyQm/x7BYRbja3SXRpcaqyvRV7gCdEkUnNeQsLCwgERsAg1MCs1vdMk02NYwLUU36SA7u0ZLmhqA6oqtyFDbHIN2riyigqCCx12dvpm6/TvHXa+2ds0SKD6VQtRCxseyATWq026tNqwYtKJQUyRSi0LrMqTa/5b+kO7hZRcAqxzzNQ7LOw5go6wsorGxTkw4VhvfgCm9tRiuNvjTmXGySopfTwiMEJyCosdUdadPVKio0adCkp0uhDpXW41Z0hf+TjyVO57coX4JQ5RuFH2LUVnkA2tt0kwXW+9w5SztqiDSFCsOoCKa1adg0osBVHtY256ipUxKl1pFRBZws7BFP5AsIBBqdzjYbUDhgK/DI76yewjbhXAh2KKDsLT1yr05YV0pePbq235i0zUrsbwtqOFOncp0iVUKKAWFjbCoUKtQvGE7mAwE7vzBFDakf0sC7LR/wBlwtMSWpWnpVNV4cmkuErBRRTWqBlktHqJ7PDk4XZaYo+Ldwr2/wAO1uzkNXCmsK4Cm0XPUezTqqiaca1RqFGOy8jguB5abVhFP5RyDYH9NJyxlaRH/HthPo0nL6GGUbbAK8rtyFrtypwITHbanpeHdgdtGUv+wqlNlRhtlvXllvC8tgIwYQTI0ZpAA2O2ovlTyBOGBlErPIENh32CCa/DaFTK0i8H3NZMb9RjG2jW/wDR5CjlDkKvT+O47FNTe7uqIRR5gm/cdhsEOio16lFzbnOXmc7BuM1eYzF5hMQuExeYzV5nORuU9ebXBG63EqtXqVXZztHnSowN1uBXmc5eZTl5lNXmc1C6Tl5lNRuUxeZTV5lMTrlMeH9VjbC7JiBVT7UeQbBM7rCDVjk7LJR2bsTyE8nCsINWCsLCwhthHmwgEO9Q9MJ3INgm99MW6NOXp+2r0/blNscClDtFtqT6jNOwcenrerrYDHpWGDRmytRW6hBOFp21x51C8xGQ7hOsMOjC09baE9X+FSgzHLCdYIQhacg0Jsv0/bl5BblL03HdTt8QPuvp63o6dgKtpqM5s6LVhyI9ghVYmn4dKdM1DbaEAOWm4FCdU1DAowZFDT8B9G9W8wZeFp61idUu9mhRraTjYlO5ggtE9tVSpNCd5hORnTXN0ywNs96us366ndbgHWyuZUDTrQy960Weui/6mq/mbp8ZovvrH5EhYT/jdF/3dX1pFKp9bPWn3yqlsdwu1lqWtVoWvzK4rSc2VIfrVmKlv+O0eP3LWn8RK0V/JrL+7Hw2LeIbbhBixKsiXHpUYEXUfwp7lO5RsEO+iO0y4Qoj/OrSr7crfIt2nD+z3j5GlbpzmacP7NYfn9a/ctF/09V/MXL4vRXfWHyBHRf+u0b/AHbhcI8FeobaqVanMiwqD4mpZNCjIpeT2xR40WDT1FcGTpNr+N0f8nrX+FaJ+7Wn9zP7dpOf4tKlEoUpV0uHj3vUXwpTijyEIJwQQWivt1HbJU2V6fuSNguAZpeo2paLvYpVSZZGzqcU+FQpaartfedRW6rOp+RXJaeg1IMTU7mvvFw+M0Z92oLdKmSvI7irhb5MMd7dpA4uGpIEicvILirHCdAhSnh2rtTki0xpNehIaaU+3zaD40i0fGaTc1l11DAqT43kNyWmrbWgt1k5rpo+Mj1nx5E3UtF0S2H9z1F8M9Hc742wmqxXQW0eqKa9UMVTU7XMtc+vArM1PTwdTUeGheYEmFXdTozIupCGepoyl6le5pqF1STqGhWi2W5C3n1NTXqdivd0FxazUTBGtM/y+V6nC9UBSdTVXMhyfBm3S+tmxMqy3r6CjfJ9CfVhaio0IYqOa+JqV4Z6moKRqZxbWrPrVfUbBEztFq+DIuOoPrIbjthZR2CaAsIsXDjbG4KBTim74WFhYXVdV1XXbBXVdSuFY2wVgrBWEBsUdigERsUNieTKDk0prwU3tU7rKOwRC09aqM1gsFuXkNuXkFuXkVsXkFuXkFvXkVvXklrz5Bbl5Dbl5Db0LJayjZLYELDbl5DbkbFbQvJLUvILavT9tXp63LyO1LyC2ryK3Yfp+3kXGOYssbZTnIlFBFHlCBQQOQeqx1CCxvpD+iNtUV6rRWgafivjeF4BV+rvjWpsC3eTacrvkWna3VakKdc69SbPWVqg/ssFunn0abRTYr0K7rXa6dhqspMZTpIrUB/dllEo7tTkUVnkaNqfREoDrTGUwJw6/laR/rjbUUKrLo3KRcpsO3sdTgrUNN9a0MssM2nTVKrQte1ng8cS8wPDh7ahp1K1phzp1CLQe99FS6r6Ue6OmXKlCpuow1lXs5uux2DcrhWMIlFE8tMIBDbs2B1qVAEGkpzeitlyrQH+p16nK9TuXqkr1S5eqHL1Q5ep3L1MV6nK9TvXqd69TvXqZy9TvXqh69UPXqd69TvXqd69TvXqd5XqZydqWopNV1asnlZTQgnnpnZ3NScm9gm95DxwwHcMh7MuHCBUGQ8cKfudgeYrKzvnYdw1cK4FhHfCd3CaOhOA89djzA4TavSkQVjCk/yM7tdld3NCrhrlUb1WUURy8K4UdsctMdVUOEXLiRIRTU8o9dmfa87lHnBVB3DUq1ApBBe1Uvsj/rrcOFXwsLgXhlcJCIWEBt+V+Nz24ehGzOzE89U47F3TiOwCaxPOETu72WonYKPWP0sWritnJqUS5GmVw4WSuiqU0WrhWEO+V3WFhFNBQanMWEOgJw07FBO2aMnsiU5Hc+1lDanUxToH/kcU2qVxNRqBOcUx2S3+OoOoanMRbgu2a3YN4jjCceFE5XDgcQVQ7OR5KfdFFFZWfaGw3pu/U9+xCJCc5NKoO6Oo/qxheGSnUk4dWDqRtTT/ANK7poVVyyiVlO2wg1cCHTd7kT77TsE1xQrDL35R2aVFqhViwKjUBTmnFXLlwINXDlFmFRVdmVwhE4Dzk7HcbnYnoeU+8EwoYR6LKymPTXpj1Grs4CykVVpkLw3EMYAqrQ5MphSHdclF5PPnYolZRO598FZXEgVlcS77fgO6sehVwvFchWKFV2TxE5Y1Va3R56nKPRZQcEUeVx/0NKy1ZXEUUHELjCDkKvQVMrKbUK8VydklPIyamE45PIUTtnlz72Vn3criQehVTay8VGouJZG2VxBZXEif/gZWdsrKysrKyuJcSDlxLiWf8v8A/8QAHxEAAgEEAwEBAAAAAAAAAAAAAAERECAwQAISITFQ/9oACAEDAQE/AcMfgojRgggixak3vBFyo3ZOaRuqo7k6PCiKOqwKjwomyNVD+jtdyo9KLFax4UrFWLVV4kO5WQQRR4kx/MzyTqrCsUXLSkWzOCME4JvRHpBGKavAmIn2nJDwpWMV6dO/wfp1IGtWRMbo14dRqLZzpwSSLn4cWPiLidfTk/R6i5HY7HbYkknJ/8QAIBEAAgICAwEBAQEAAAAAAAAAAAEQESAwAhIhMUFAIv/aAAgBAgEBPwHTei/6WWX/AAWdjsdhOWULdY3FFTeCzZeTcJYNQtTihKXHFZNQpvJllinloccdLKhRY4WThSs2L4KXCeTcKVm0LO8G8ULS3g5ThualanN6LLLLFqa3qVpoqFprTyj4VClDj5h+j+QmX7Cw5fBUMuEz9hMcOoYz9G4aH4LFlKKKKUUUUUUiiihlFRV4tTeioRcqKyYz8LLKj0pnpTPSmUymKymcVoaGdf8AMceVC0tnsoYsnxjp9OPjOx2E4Yosse6ihIoTpnYTsuFFb2rKKHw9Oao48x8jt4cV4LJbKKHxOp1Ogor+Siiiitf/xABIEAABAwEDBAwLBgUEAwAAAAABAAIDEQQSIRAxNJITICIwMkBBUXGTweEUIzNCUFJhc4KRsWJjcoGh0QVDg6KyFSREYFNw8P/aAAgBAQAGPwL/AND1/wCy09B1ZCWt9Z+AX+4tB6GBeQv/AInLRIvksbJH8lhG6M/ZcvEzg/iCrJCbvrDEeib1Nji9dy3Ed9/ruz7yXBuxSc7f2W7beZyPGb0KAEJra2p5I/3VMnj5MfVGdHwaNrBzuxKxtcg/Cbv0W6nlPS4rcWiZvQ8rSHP/AB4q7aYfiZ+yvwSB4yFrmhzTnBRtFlBMfK3lb6EFqtDfG+a0+b35Kk0CMNhPTJ+yL3uLnHOTtxJG8tcOUIRSUbP/AJZTarM3cee0cm1w474XMNww7kc5ymy2Z3ihwj629BzSQQtjkPjmjWyEOFQc63I8U/FnFK74yJmdxomQx8Fgpk2CM0kl/Qb42WN11zTUJloZy5xzHI9gFXt3TOnilN8fanDgCjenJ7FJLXAmg6N9fZXHCQVb0jLKPNO6b+fH4sMX7o5JnDO4XR+e/QyjzXgquSGbpaePAKOMea0DJG3nfv8ABJ60bT+mRx9VwPFzt2dKGSz/AIjv9l9036ZJ/wAvqOLnb1THc7QckUnqv3+GP1Y2j9Mjx6zgO3igQVVTn3iE8rRcP5ZJmDFwF4flv0MfO7LDByndHbHb13gZcc+3ksrjn3Tcr2geLdumb661vGLtyzoyyOB3I3LeKhUyDbxzN801TJozVrxUZLowlbiwotcKOGBG9hmZgxe5BjBRrRQDI4NNJJMG/vxk7x4PM7xLjgfVOXZoaNnH9yLJGFrhnB3m6wUYOE/kCEMQw5Tz5HTSmjR+qMr/AMhzD0ELPacYuR3qoPY4OacxGSkraO5HjOEXXdkj9Zu2DWgknMAhJbfFt9TlKEUTAxg5Bk2SZ1OYcpV5+DRwW83oTxbqs5WHMg1zthk5nfvlFqjYGuvUdTaxSXBsr23nO5cchc9wa0ZyUWWPxj/XOYK/K8vd7ePHY2OdTPQbWm0igMhMTzdunkyTx87MNoyMec4BBo5ME55zNFVelf8ADyDeKRxuefYK8YtB9oV4t2OT1mqsJbMPZgVu4ZG9I20TxyPB/XJRSR+q4jLFXM3dfLJOfs021GtLuhYQEDndgq2mWv2WLY4YwxvsU7ftnbY8RtHSNpuomO6WrGyWfqwtDg1AtDh+S0OL5IObZYQRmNzLMRmdR2WaTmbTIWSMa9pzghaHDqrQ4vktEh1VhZIOrCws0I6GBYADaWj8e2HEbS2uOG+RP5SzLLJzyXfkO/fJ3Z6vO2HEb0b3NdzgrSpdZaVLrLSpdZaVLrLSpdZaTLrLSpdZaXNrLS5tdaXNrLTJtZXpXue7nJykQTyRg56FY2ubWWlTay0qbWWlS6y0qbXWlTay0mXWWky6y0mXWWlS6yobTLrbxX05P4QHG5SlD0rgP1lwZNZTytElWRucN17EQDcY3hOWLpSfxL+brIzWZxkaOE050+Oa9QNrgothLqOrWuSV0xeC11BRGCMuLaA4qaVjpLzGFwxU2zF4uUpdTYor1CyuOUy1lvbHez+xPjnrdbHXA+0Lgyay4Mmsj4M9zX8l7EFMsk4I3V1wX83WX83WXiZpGO9uKMMw3Q/VRvrKHPYDwvYjFNepcrgojCX7utbxyTCe9RgFKFMbBeo5ld0Ux52WpaDwkY87Diw+zI58tdhZzcpUs8QffbSlXe0L273avh7VG2KeSMbHma6nKtMn1yi11rmc0ihBeVEQOEST81KyOd0TGOLQGqvhcv5lQzuFHObj0q1sGYXgPmrN+eSf8fYvgarT7p30Vq+HtUfuu05Xe57FP7vtVm2GaWOodW46nMtMtPWFMfa71+uBdnIW59bHpuovheWOvDELTJtZTRWiQyBoBBKs0nKQ4fT91Z/ct+iPulZ+l2S1dDe1Qj7vtTCcwYFQULxuoym2Zgo8mmPIo4QaNFG9JKtHw/5DfLV8Pagy0zXHEVG5JWlDUd+ydFBMHPqMLpUH5/VWj3rvqi8WSW6BWpbRQdB+qtvxf5KzdByT+87F8DVaPdO+itXw9qi912nL/S7FP7vtTPCHOF+tKCq8pJqFbJZ5ty4YObnCjikdecH8LnWxzsvs5lozfmU7YmMibncU3YvJx4A86svuWfRO92VZ+k5LX0M7VAfu+1V+67EbFI7dMxZXmUtpYzxkucqyWWPycU7L3tdVWj4f8hvlq+HtTJIGtcAynCovJs1wi4tjw+2o2g4sJaVJNZ7sjXuvUrQhbDbWULMGuvA1CJ3McbcTzKd2bZQSPmo3wUL2eaTSq0X+9v7pzZqX3urQciddNaNAKn90forT8PamSQMDgGU4VF5Aa4QNoju3s26BX9LsUw+67QrP4O0OuXq40z0Xk264WxPcHPLrxoo7pzOA/RPINN0EyZkjqsNc6+7mYnwScJporL7pv0VCaXmEBM2Ei+w1oeVaP/e391K+egdJTcg1pRRNBxbHj81/R7EyeM7phqE5tmZK2YjOQKNVmP3zPqp/h/yG+S3oTJfpmdRaG/XWhO6zuRb4G7Ef+TuV+LEHhNOYrd2R4PscsLLJX8QVbS5rK4PjOKLrHI6401Y7MVS0wXj6zCtHl/RUssFz7T8VfeSSTUlSQizyAvYW1qFKTFsl+nnUWhnrO5aG7rO5RgQmO59qqEXgrq3Ltb6dNseyXmXaXqLQz1nctCPW9ypDZ2xnnLqqO0uF8tdeOOdOs4s1y9y365HQyRukZWraHMmSxxPjeBR1eVRQmzyExsDc6D2mjgagjkQFos993rNNFosmsFSz2e6edxqnSyuLnOzlbD4I7gXeHljmpW48Opz0Uln8FuX6Y7JXl6N4xWHpOm8vlmc66110Bq4EmuvJv1yuBJrrO7rFwZNdcGTWXAfrq7Q194uBJrrgP115N+uty0nokW6Y4fGvJv1yvJu1lix2usx6xeTfrlcB+uuDJrrzusWDH668k7XKp41vQ5SQE1uHPxmX3vYMtmskTyzwh9HOHN/8UIrU7xlPOe7H5Jgh8ndFzoyTSxmj6AA9JotmM48LMWyXtkxrStFG+Q3nCra5Tbf+OZjFIm2r/jtmEceWb8vqoGyteZ3AB3D4SaxmDWigyTiz12S7yZ0yO1scy05nbI5wqU2OMUY0UGW0dPZxR1Ofazt+0MsUtm8tA680c6dZ3fwp7XHO6qgjeKObGAflkmjjaXONMB0hBxsn+42CvCPDu/umxysLHXjgctts9ric1kkxorHDZInObHNU0yyxxNLnGmA6VFD/AKPI640NrXP+iY97NjcRUt5sj5I4jK4ZmVzoRD+Dlj68M5woonmrmsAOW0n7wjiZJTh7KrBYL25HFjQ5ruECtCHW9y0MdZ3LQh1nctCHW9y0IdZ3LQ29Z3LQ29Z3LQx1nctDHWdy0MdZ3LQ29Z3LRG6/ctEbr9y0RvWdy0RvWdy0NvWdy0NnWLQ29Z3LQ29Z3LQ26/ctDHWdy0IdZ3LQx1ncsLKzWT5X8J7qnJTJXe6bRzeVN+WSg9ADfMdsfYseMY8UBTelYZA7nT8mGXN6MdjwcyGSu05lm3vHj7m86CrlwGShRBVRvNMtTkz8cCHTkrXaY7SpO29voIezbUchjeWIVWquSu1x9FXXBFZlWixoFuVU+i6L2bTErFwCo019F51nXJlwWOXN6Ozfqs36rN/0v//EACgQAAMAAQMCBgMBAQEAAAAAAAABESEQMUFRYSBxgZGh8LHB0eHxMP/aAAgBAQABPyF7qmrONJ4EvCkVLoQ40Qngmk0W5XRB6sSFtoYY9WNeOEEMQkLwR2CF56ID8EINTXBBiZExlZEzQ0NDIQQ9Bsj1esH4EIhDkWiD6C0UiEGkg49fM3EFwQSJrizsithkjpjCODLNOj38cINaoTRkEtCaMwuglFkbfgLIhWoUIoS0MJaIL6BqbCeBOhYZXQet6oek8Sk0aEtBqDJWKNDlwU30ajfoJ3wR4F2DngqZILIrM2w2W60W3sT3Uw0H02EyIMhyIZBvVIaJkWs0cqbixpsrYiw9vCF6+mld/QXSbfX9p/w3Ebq5/wCEWA4b0MiV3nL/AN1GQ+mqb90fREu629SPAuQpodBRZ5Iwkb6OV4InBh6p60uiYGhiEIITIyWNKNiIIMaIieUG/kuRKaOVN9HQhjSyMRDA0mo1UZc7jw/PYMOR7l/CyaSCZkbHJihsY4yD8C3LomIwaGjBRjZaWRowG9YJCCk223FBNzf4l9cCVgolskbIoEqas7+guOH/APAMz27+QZR71a/YxTadt+zESLhF83kZKLuft/TqgybrzXGiawRCpomQs7/c7rTpRog1BKsWIQexKbLo9HnRnIxTcJVtoODAJQTIqSulrRCCFxmkVVNvX6wYCXoIy2+BCIW9vq+RpkaxW2N+pc5E9LQnu+n3YdzFtx5O/YYpsxclTvuPVdiMEmTJOrGmA6xNFDBQfiS02DDaPcWcCjOjIcCsTRCCiYV5h94i7EeYxsJkTz/hQMPRC0IgOIhU08oXDLO7OvmLcREWiPZj2J2R369DLDHSYGizFhKdkLmnPgbwIg+whIFQsqPGTQTBlaV51kI+x07CtpI792Jmj8YLTfPL77D29xvI9GsnBSlNxOD9VYRgpS/kFpg3fcjj1GhZcacmgUMQTMOB+BPVMQzyHSh7GVsLYpuGXgqGxKgr84U3ft+RoU5txMtjw1A9E2GyclENkQbF4Dxjdl7fbj8FNxHVG+l/q6RCiCgo8CYymZFjOP8AwvgitE2ZKtEJZWTcNUZTkspeOHv1nj4SIPbZ+JH8UY2YjDwGtFrTcNantHPwQwyRrOV8r9mMGac6MMsSJlCDfN2k8C67NDWQlDvEkmQ3UMwQxc5EyQDds23V/ooIcj7/AKJiaHljGSeFRC5Npeg/nPfUemNc/rP3pZk5FqFgYhTJm4Qxa4tdg0RPkSiHgVi6XI9dg3keRoQmTDyv5GvlaVD6Ra7kul0miCQgmUILy7k4FTv0NuEybhKFoxZjycjEPRDBCENkaUYleWhVFyI2e9GcPo4Xcl0kepgJunRCXUo9tPIB90b/AALqhiJjUr2Dn38lEXMM6f2v4LBaENYGM3/LR76LXDzFcyJoiDi8qFcXQttpzFqdczCCwN5MUL1/iC+IWoS/hvvl+KZ20LgmiaIWvAstJqVWd8ll/CFJFoJVPI0dtl+/YyFybxlBpR9BiHpgOdsNi0Wi0on5A+EuBlE40JX6hlRyENgjqMYjX1FuvvQ2DVOqI3Z8egxQ9xh7DGIcDELOlQd61Pc/f8GTOTL8/wBBfXokYjGmBgwxiGhLIkiyUwhC1otRoQnCNxOF5mTzNhKO8Qe2TY3EFx17aHJB7j1D1M6eTHgXaFsybgww8tLEJaHIVE4vkwv6KWSBwhEjAG3LdLkPXMcIpu2KEwIsGKGMW+jcLLuia5EEho6Ntw9EySETG+hMvZ5GjZi8Wyj7RjpLh9BjBIM9PP37j/zxDK1bcIcJZMVHMSecJfR9iBNPMfqxI+VmW6LuYzeFv0BqhcnIzdMXqPGIzLF5LbRiGJDNPQZAjfr3EI2CZY5EET50YmWMuoymBzDWdqxvP/AmQNYwxGNtU+waFSmzO47rgflMDwQ6BMjS7RCtlZPfS/N0NmVKDY3U238KL7263hf6WrIkMFE6IQzvsNsHt4ESmJw0N2i8JaEeS1E0M0LAfI9yZG0kkInOclv4RQZz4b7CCi4gSKJ3n3/JHSLnQ3geC7iXtBUzNsYiQjbgh7S5GZ+csV0Z7tjXhkaNZMJ1aKN7ODkaEzrHWvYbBwXRC0Sj30IsTroN2i1i7U4hjI0LYyHw5ES5DEbSUuJZctmug2TEdbH5llfKFFuJUZmGhXmxG3kSG+GX8kP7LVwj9BIyeijHKHnkRTWB6mlj2+B2OlkwMS0g9WNLkR7hj1QtjETOlIh6xzIFS57T+Rm7Ts3zWzLnQVvgf9G+2cthd0a+ormRWNbJgz7UglkRMbZlw39tc0JBErK39GPmCETeW6+uBGYZTPgq2O2P6jolY1V92HyTu54F7sSkt7vN8kyxPzjaIhB9qYMnkleExBYfgoVh3FNJkKQV949JgScmXdPpMe6X36G5HMKhsNiZqhKmc6PxiL6rPzTMbsQ4dtPV/wCGDmxAyY2BEaTn459NnsVnla/QiiDokN7CYHucPahtUKI8sXvpMPRaIokbukzRsHMxCGO02PIoue4xMWw9jkjGLwKVKpNeT/0yZE8i+r+IMcHBwQ2C0ULcao9obhStxG/UayPQoofB0MUFxjQ9ExaUNW0IyQkJEO0wJm2WExZ/vj/p5Z+2Jf8AWVf7Yp/eP/Rj2Ej1k37Ak4+af1Aeba0ymrOR7Yakk2bo/WJv9pn/AHRM/vGlfuC23vRX/fP9ZH/pyf8AWWHpqSyszcRDR8CQaMyo94IUeraMx8jcTDy0ImBoTGLcfAnWI28DcLLByTI8b6CV3INObFMT9Cmk2LfA5FxnWuSDGmND2EzZBaSmiOoaaJY1LQoRt0Ru/wDglpzpJbByTMTqazqzslyxFVzZ4fobML1f8iRo1DFdV1GJJLuZolmU5N2gshRQVM4JVSHvyZykxN0r0O6sSb3+DcWUz12v+GzQuUjJxuXQW47C4Mw/b03xBfKesGoLP90nGodj7+QyuP32H3orFRMhcieE6opeFaTd10GWIrLczUOMK3DaCdTLbHC3b/huTJyZrRlMo8y8ihnnXn+loSSuJvDsokqu8LKv2KWJC11kkNdLggtNmn5hMB1G2EtaVNEiYCa6Gbg7dXS/CQ04TPNnKxSRzXdXsxNSkq2jD/Au2RHRHF+T9dDPyYpfZyfbdQ79Ik9hoCwZ8gdz2fgLZblGvQTf2/cfCzNJOC38jqt1EuHRkSG/rHo7dQ9es7UQmWWPyw/IynzH2nvL8oxbPoijMw7+a/cMxJSfoPsw83/GZsYo9bfkKrPJb50922OSUYDjI34C3MdBMhKeSh4noijGPt9iRfPVotj4/OfSdRnvQZw7Xf0PonIf3A2H1wLDH9p+Bsz7NmXd/MPgEt8loC8FrLqeP27Be/IX2S/lGbI16qlujyez8yoaX5qbpJSlpl3973GXvsP8tiitrbWKe7+ENW/SRor7VH3/AERBSKzvn5CbF3o52l5W/T6C8il/l5lt7k7X8aRbxBmyCQ8MyCZESrQuD5h21m1GtfURUrmSV4C6Ed6Zq+GhEDdgsvdZKD+yYHHwW/IOkTlsYHNFfqhmkVbAfRsy4GnQosuyQQSMKcPQbBPYriX6mVfXzG/7fyJ+K7W8TyYuDynvFX28zvRqsbG/kUeVlU8XCVii9h1Uv+e4YKZbL7kwGom8fZlfh+wv8EGT1To/Ua/fwJlNc8vDnwxMU5GRI9/UfRExW5WAVv7ljGI6VoPgM8XnTsQw/VQ5do1tNt2+J8MDR64QkPItx5YIzB6EzRtwJe3cUf0f4J/8QRZVFWgbJowC4vUE2vwhbJ9DQhsY1dv/AKQ+awW0C06voL6Mh/f+h4utb1L02GSlgeWy9qggm1B/GOzBL27jQv0h0PaCv1N5yX0HJYnQNp0Nh9ndGndn0OiU4EM7zXSfLCGsKWPL1DzNE7wR9IKRDNGFKudyuMA6ccbepRWwSxxQYz5oGFtlLqXpBkky/L70Q6A1ZyJZmLPPSdNL3O73aZLDANexIj2joUZKzAcDFHrggowle5aF5QgxlHBgMGhTIRvRfBQsB5YHgJGdwkxA0hAopbkGC1AxrIlzBNHGjDsRHuP301JUtkbGPcwQzqc9Mw3IYSYiYk2ghBc5EtC/+okq5cv1OoPUI4bv6DhiE/KYhkvpH/vB+0Wqf9Idy9Q4/sllR8OjhOyG1fRx/wBGIKqurYf+9E9VBN392jmvDdhQWB5zaVBmRN67PvRAR4xyuGbyZJ08g1el8aGyj0xZ0jeSGK8DKBctdxEzM5gyd/REdfwsZJT64HJEiNu/u4CpNlEOrDGh5hSJxCvkfT8TOi+nUepZY27jwM5RltfFxzX+fQSu3fhx1tfn1Qnl6Pt+gSEzFvaXbG4uqAm2JFM4VhzLmegppFhTtNOL1ghghTbEcaEPy/4GaPAgMx6IQnpbRdOSzgkNhRmgf0iDVucBE2EwqOu2d7r/AAfML1IyO0eTHwiFX41s+FP2QcBejSFMMtqq3HDJlq275F9glHXtEe5SjXJFWG1jKIayQlczWy0bMYliK3gXUNssFuHsU7Lt9Ci4z1EMNw5GnfJEK3vl3SKNafYgsFEoqzcMdsG6Ykyb0m16JoQ63gsxBZY10kj7w3/0VbjRil0jsyDDOrm2eN2J9geicyaL0R6rCdgExaIF0Tmj+gf9eE3+0Y78wf8AbD/rAtnB5v4Zv2hb+gdQJKR1gzPs2d8V3+hudY85um7JqNFMtjsWDbJjZlH0ZRMWwvcNyJl2HwFeQShecPIpzYvIyIbj1GtkfoLcVNpkU33G+40Iom6MMUVvks0NlsY6J2xzuxotmV1L1Hk6hxvK9IVgKB6PWPwJjmFOEFs5Hh8xviMzDhDwU8sUc2ERKURU4MpixhtOwTIhHAqWDDczILIaKPYRQTEI0luyj30GMXQ/USkZhIxmm+MY2PGTIGUXOUXw6sqJb4IYiBbEN3tFzEk6uTuQkfBitewtwtJ6hVhNrA7uHNILRQZycjVkh4nRzdvSCKSDcepQ5WhKY3LMup6MXgTGg3CuBOjxlfuBzleXGJWZEEIUeRM1Jb7mWMsx8uBlKHidQfIbDCdlbDTwjDkYKtKPEj1vS26PRsDlJBdiwPeKx+BsiZwZDHotVvpTJaKOUPBSqdRGxkUuBuVpJydyglchcCrgS9h2HNSGDocwdAqYqxxKIzgkaEIx3Y3gRsRPgQxa87EUYbNyGNdBbsfoZIgfSNy+NDedTwWROCrcUTve6EgiVAmsMU1g6R6miz5i4FSJU6Am8JC08yc7Say8iOIdqHWrYy9h6e/kK9zJXpYRkY8s8yESD0hhIY9UcDfjV14B6KKYZpqj9uENSvgyCZpG3c4exg/LgvfU+w7qHllC0tVErzVDHeMIhuNo8MGupgXljZUhqUkw9d0miY3ihBMpRFujTTd4qdYZUcnkGGUhLCkkky6wnxDZqQpDEUWTuzIR3JIOfkjFrHzGIkXYedyDG803YjYXqMJ4YscnGMwN4J4UTA/BPTHJkqYnpclO0qW7E0HBTQdcyG7mDKjbT7D2DMkztRsZzo2LUpuq2Qx0y+wvUJUUDrwWyjW9K1yU3H/4QhsJlGhrVMotPOwuoNFsxUwxq86ZbgTwH4T6myvvLvOgks15wpMJpbsT6hDYofbbR7aMxM4mbS58DF/8ENeBBCE1RSl8FF3CboR4GcX3M+WD7mgNWNhUPpGEsaLZFvDNGc/+K0ZCaoTRhkJpzpQu5l7/ABoXcPSXcIJht1GC7NL7xsvhg8DZRv8A8v/aAAwDAQACAAMAAAAQKaWGmW8Gu3ay6GGqCYHEwJe6i+jOik60jgYr+qI0ucRq59Ki26Q+CrrIXPgRGXNg9l1Cutwi+GmO/UvP2mG0KlMaogd6dpsC/cO2KKJBzYjlaJuwVP7FcSNifjSuUKgGBBPdjgYJDvhhvUZNOVTqauWoT5h3iGQUs3woB+kwtwxwM2UCwMrCmWeB2/5crkmUJN3pMSGQS9GBgKozoAjsqZlgErNWAVMJlekvHQ1cL28gefHVz4pWS6ZA9p2JdoqaM16WDQmTxFdvdiBbfdZSAxqSNioQAmvyuwgIo2bRp+SdWbT300yc4ayIOToEPOxjphwJhuQGNDMU1/8A0FNoyCgC4EuSkvcBfHQlzM3Szqro993/AAC/pk8LElNBw7wxW5cmIgbUByX78Dx3u1+MqA3sa7GlXJIbVoja+ZcGQue9TvtE59jeWRnPo3ZvmidznDu+TzVXqXpIy33VA9w5/oat/UEuApe+XLvB5iBqEqKYF+REJ1G2tVa5f6UjnCr9LRpA6x6a1T4oNzDL6odtIrfTTL/NskqgrUQ0pNAp7LbZuUlHLLTjS/76rNHFNB7Jp5aYrhtAtqG6aByx2UV9jJqpKYr6p4/ZYI+rgu5UJ2ANr6T5rbLb/8QAHREBAQEAAwEBAQEAAAAAAAAAAQARECExIEEwUf/aAAgBAwEBPxD+JM+86s4D6z4yyyC2fjLIu0zOH6yOC2LeO3wEYLCwWsv2Flk9S8hBnC5YjvjNs+WfJEzJJIIIZx/hbxsfh56mTh5OBttWnI4X5xnyEMlumzJ+hM4JZeIn2z7eOCWeThT/AInZGzgGRPz5HD5wzPJwQ2WRH5Z+yx5wOTgNhnw7n7HJddju3JBLy2E8ZmWdQQlg3uDW/ZF65PktiTPbCYSQpITSfILvhWh1byyz6JywurJu5vDydEajpKs+ASchwWEh1/B43kvXBM8kQQXkTYl43ju74Nu2V5L84IiPdoR3acPtvDCPIdi3eTtutkgBLLwWXuV2PbO+E7s6v2yCyNiHgOoO49YH7LRl+MjS1u7bdtbu2221teNtY2VtshHyOR2csiXIb8h3jHC95ZLZJwxeG3gNg5dgTjq6ez0z2RmymQFpdeWk5u2JRhJFvGHC8FlLTZff/Iz0tTb13OchJnLaWBPwLw8jKGS67Y2dWExMpZExBsmQ5NssXnD87DHiX8ktRtBl4kgbBrLnVvWs6l4zhl+x4WKe+Hgt+m/fgMdIIt+dl/jsMNsNhEB+y/CW23hZf5b8bbbbHI22X+P/xAAeEQEBAQEBAQEBAQEBAAAAAAABABEQITEgQVEwcf/aAAgBAgEBPxD9b1u7+/q3i/rfxttstkd222bxEIR+tltmCbOJONcAy2tpgQ/WS8W2Dri04JlyJwx9t5vWx+hdhhmW2e2cy/qdexDbHXgss2T7BnHnnP6c2O5e8WkF6Maj8/E/x0G2XvD5bH6L3jBHV4IX9jMkW8PXnxZ3b70feDwcZ43mGzX9tgvrm1vF5uW3nD/ePRLPdGGGT42bCjeJZenyLtvsvAJf5Lhehavnr+WyYd+W/wCwXqHJl3G/vTP8nF68+ubbP5Y+we2/7f8AqLzLTfL+nH7fWwT6gzfnqw9W2bYgRzmWdH8Z1vnjwdZllvJ4JCwsOeXl5IWBAh42exxZk5ApuzotZtrbS/trl8T+T6yfWz6kiH2VwlmiK5efsthCZbdnAj1gZ5eS+7GGQ7B8eD+ZL77eHk+5BL4JcgJfwlXyOghwny2w8sCzYOQBY+WbFh4YZDIzIDBsMJJXt8giy0nx6X2V2NWfI1cky1t79th5vAabazdsiBf2LOKWtuJjfsatMCMmMyAZ148PveRhmcgP5NIPtl8tWyDu8M8geP8AZ342jL4jdvvFId6XpGo/ALIO5AuwYZayL6R/iFC2y4ZxAYbBZBLYtkR+WfDJz2C9Fobfccf4lwhvtmuEZYOacILP+BwB4cfdL6CD5Yzv1NBnDuQz/gWSWbwzWbv+QPrCDoIP+2WWcJjsyDufr//EACYQAQACAgICAgIDAQEBAAAAAAEAESExQVFhcYGRobEQwdHw4fH/2gAIAQEAAT8QJ0cdwiXKXADcKqKncIYJaqJR5lSpguBDETuJeJY0XcadLjg2YnM6hWhFMphKxEuVPCVEVKguHRRcx2ait1BTcTqMNxNyx5QILLWJqaTcrGZtCblZjdxYTipVuoPU7MFfU2guZNQEq9GIhcRdS4DLKEXLcLgddQ/AjAog3HUTqaQ3jiVcovv+CGAIyQM+IZbI8TEDUQxMtw0a3FPM2gHiaeCAqZl3pNpuBH1qVcazGkDKlQIcwXxHpuaRPyg5iIZlrnBFRTUFuOZf/cBsC9QBtCYUV3Li3+IUSr0bgVnCILxBrUwklvxLI2tj6gW6m0bIRV04xFZbHfcRRiUFi4uiWXBg1RK8o1YZZbt/gu8cQlsrMxcSnywV5j8JfmVTmJUs0WzYlXqa1CKjJLAeI18Qyy6alnCHavWYxeotnicipV7llqYsKCKtu4rmolRMuOo1iUS1aheZ6B/hDPcZSrg6v7QV1nqNiCiUlrHLO7URwFpVpqPP+RK3U2hY6/gWTSBK4vmIGIm+47piXEppmFqWuZDRLGY5bjggjE2ZgFblXzBxdQhA6hoYQnwiJdfMcYPc7b6hWWvqKMqnxLMXuEs6S/BfU2wQqwfcVaiWyoKpDxLhiFrnDUJIsPxLgFYnESziUtXcrNxODLMYMQVqGUqK0wXhioEu29TZ5Jj1KeIvJjdQMONRFzxHkQsdQhzCWMBLtMA3GxiUOortYVE3EF22wYWrrG41UJmxdm3wMXsbEP3wOut3d+BPwgKePiw5pfAvsmnrMwfH6kfR26a8ZB90RC24nd7/AAKMZ5oTPhEC7tnveZQWZNSqUFdRWKYq4VsgzhmWm2LGZx1NfMRcQFxubai0ambhCZgDzEKaI0IWCWX1A2gUoQ5zOKo6MLFxOTEbYFwAG4uZYKjNdS1FQSxHGYVDDKcO1R8dy84PPEqP/BXeGj6PawvloO4OA2xBJgqYhZJQgwMC4+AhSIIwcU14y/c9lPlmRI1nWaHleH4vcd1klOtXHBeYQGZxbJVPMeSZdRPuhU3uICClGXuFecwVjcxjxGckSCZMXlgGILTzKedwOpbmVYralOC4UQb9RgCsxBTnmIsGE4MRyTiC4TNwC1VqiKptNz0vd+nd5AkCKgUB0EaWjUSaPMbiuHto8zX9Gp9uQPjPtjzbXFMfSE1Ubst/MBBGbX/EKHI1w9h+0oNdOce/2Hwhc7rPleEyvcLrMdvK5FsR3GA0b1Dpz+U8mlorUy8ytqHSGbSJqhCO+ol3AwJRo9IrdR53MRiwytTYgvCLHcRzKgxkmIc0tibq7j0IOKEJUG9zE6lBlJuoFteWVdwywMReZa1Gr45fExqlxE2vl/y9AHb3CnBaAA2rClFVlnou/b4OYvTrFLartjVWysu2V+5Y1UuneIIEYe1r7hiooalOR7PDiB6+AxWb6dvp45C8Szk+JatQKrnV35OPWgZ4tnM3C9LqOoVQf3JYYy51BXEbhFgTdi3FxAlWeY71KG4+4WifEdVXlj9GBLBDipSOEKuZS1SpiagFqNe4DxDC0gKwTNq74gCiQuAzf0e2umWaFcxoLQAZXiK9cvSDkPH871UZ62xG7jal4msTef4Kv1Gd3hgc2UhDIiaYPvEV1Xivhiz59BaxMsirBwiSi5k7QLzfl09I8zF+TuXKjUK7VEV7ipDPmFhCjBrbLDwuNqZnU5qLmdnMrniP6lEZXqKFe0E6P1KVRtnMMsv5uVqxbxELxTzLQzVxVaMyxe0y3KTE6y0z7SOV8Bb8RQ5N26b8i2vlmaoIqqDh4R08nV8kUBkuW5a7zERvUTSJW2JcZZcwzqDTxEVjmHMghvw9jpORYpxRcx4f067EeZpFzbBOHKgsGnpZ7SIhGubimL8wvliWFu+iEUg1FS5j2bIDdm2VKlVK+0AEurdxLYY1OJYU35l6OJigsLgAvcozLrGBMruXnaPhgLY2ZiyYqIFbQo2BAqtrG8qHqTJHD+DCcu8QIwFToDca6laxjA6xn2rzEdmotY/wrt3xBPMsd4qZMRXxG7uY1GrbJhYyAQx4Mh5bstqIvs5gcT3YzOPQHxGhvBLcnM4BxcJAWMoqfWIoWu4lgCiO06gNRXuciBmVkjqbXFpqFWRXxAs+Qw0ziACGO4BwHiCvu+D+GFrY1MiGm4K8szTMS0bYGlImxD858ws04lc531X7GT4juc3HdkCgNy3JMmCGZURzMGBFA6hh3KZRybQb7UPlJ6WOkOEsgLyQq9AByY+p/OBb6QYW5aqBeHxC1BquYyLXqVVnDtlF75mCm44MDEqJKy9zuVgbmuobGn4lYBfzKoWsE3g+I2sKusZl3RXUDmycSIcyzolfjGEWADzDMoo8CP1NIwDV47tf3HBa5uYL3cdInEStSmpkuBQYEqiLWmZGIWtx3KUO0WiFbU+/7iOag5hYvC/5x7NJmKNIGoRbWKlblDdVKxXeoqxiyY8keP5BaeYALLYGGGqmdemBoATMccYrcddZSJNq3CEZAypeCGflGKoFdVLnUUY4sisOv602AMIGLjpMW7ClpKRzOacm4McKl3iV9xwa3/BIDjUSo3zGSHDGDH9ClfiFfCAYsu+pAGdssq4BxxHAaqJuh4uW3KEfKYPjFlm3x/AxLNBNyplRqosy3UqpwxKzSNku8G57gBB2zEFT5jA8lr9xSpbmPg2QJZgFYlIRwzGaaB7gulh2IR/MUCuopxhl6f8AsIWzcLWDUT3LdQgd3BzK6uBDMFsMzc0sTmz5iAi6zXc3pO+/6iEVL0annH+GXOfcdrn1FiRg4pmoYvUNjeYq4MmU2wS87ubwGYGlZgQmiGpviCG5SXBKuQn+Rj5hj5QpXzKGxdPmZCuSjEAbRZ4ixBVdQjMFMmoOjsqO0YpjpLeG6/8AR/MPYlBcKWVLB5QDyxbDF4alHkxRGxZNPMccxlxNY3Foq4BDhxFcNRrIkW0Pmv8AhGVIAooiu/EMnk5oUj7fyS79TgYnKoqjxAOHEsRwVFoaizCW4mBdyhf9ilku5rav2Yec2sGmDRHmXj1HiIWrlhutPiMc4MKqRYkexdDAxcdYwViA2KXmNXBiXzHFxPJMciBpAmu8Beap9KUa3BSNVWeoqAKiMXN+ys9U8xkEW7hAVtgg7JY+5QQl1HjENgdzFUUALj1KC44OL2Kvyl6U+JpUcwsq1DZrs8Lb5lWomIIYu4xoOYdtMcwNQLuGjVKRfcE3nFA85kiqrqVaKA+oLY9Y1CGrg7iLjaFbY1pMWD6iS3kfCxaytP8A2EsuoujbzDwcnUIIp4mBq5Li0qKDjFqpz8hT5h0zW5L4ThHCcIwOBDzRVm6Zf/AgxdZ6EhhE7iJRKiXZMEJtD2lzS1UG27liEGvCWQCHrQUMdZ5aPviCZBiACgiGIWd0bKMXVDQ9pGavMxqMknW4ghRfPqFD+WVUO8VGKdmJ9oC5hCqLFZQxfGPEydWQJmBWSWkxVU9Iw+IohpG5XWs7i5Xay/KHC2mK/Mct3eohIWREbyVEsvPzEykHDzMedTNwZ4YbNZLwvN+q+nPcCFBLQ2J3CVkiu00OCNC44HoPY8yFGSBS9SnMLUuMKDcu0jNiN5IHkofEVwzJI9eVx+hmD6z0PNTl/RRolWPuAHJgPQLlRbgpnAWh/vKrGQrmW2PtMvLhCOSwL0Xq4Dat8EBt1P1ExEDUWZmzBrcNVk6isIOZiRI2XNphBLDECqERQkszZbAB1YRczuYkoMZiWAzAGs+Ii+UXA6vXEVTabThh29NdcD3+Z+ILbl8F5GUqVALAh4r7OH8RYdoLp2yvlsO52QM4mVEHbuUqBKcS83gy3gDKxjAFX7mj9vqGRCqg8r29rlgIxFoaHaQ4/s0SpC5bkftUW81xqZQ89wRvF/iZKxWoN9Qi2GYSlaPccV7VFVOHlAWCjK5hazHkkqnxFGHmZOE7xYLFWKzK4mEyX3HKNFSlVYSiPYNNa7imswEl5gUtusQKsQKLIK4YvEAFYazBF4td7bW15K+YVWsYvUwD4ul6iwI2bxmD9VKu/DBvTDF4F8xYAVibGsEuxhqDthGA+GjAuwEENosVMwYJ0c3auAhd+UjyYF9aPenAPHM+A0HgxMhXKzMRUcoybubgICdLFbh91DSxqtRqx8wUhbVTBiW6RV3kItZiKFfpCqVWMESr3uFJU3qPuBWoYMS5RMkygzGUKWvxGS9sQ9k35n5J51mjB5jF1PxCtWBVhmZBILjqWk4csSL4gi4z3HYit8QqjkKLBLnKsGM61Htkl8USf9+CVAOWonCswOyAa9sCBX5gEmuOAqNJXpUV/UU3kvB8eB3uNzPz3AmriAO2NotjN9NwLimGIqwkLsMDugwhRTrPcIqkEMqQYlQPMCyXlOb1BZSvXctEYitbMERElUzKG6dQYXqXYQa9xquM53/SUlmHuY6dTtGPwD/uJSBmq3v8pvzG+MITPNA/CfERV+wQ+aqXAMmwYfg+kosl6izJLLSHNwqxG1vI/qVK9ceYKtgidjBAonPK/wBIHeb8QVrMVLML6sZwDMw/f8RdLHBMrFjF5jZQMeIvB36hyWYu4ZZ9BO7EEI7yF+BlN1chfRVb9E4DNjPklq8qsAuBQHFt/uWrHKxNVxG7BWHMY8IWXyxYGL4JutXxErfEUccRq4JRATnhRl41EuDOJVIYjZeaE4i7k1G8+QrN4i2w1EafZL/Zht/dkCRhgeW52B+iIscnRJrVbvOETlUYbEawjzAKZ9xzqGhY8mtX1lVYuH5dRnDKvmYCmyEkKgjbyOI6rk3QP1FGvlLBafMn7i3LeV/cBEg2NN9RSkNCCKNmrl9xgdtR1ey/QSx5nGZi5vDsozFIMoX6idrvEa1XLlY1ZWosuZbDZTAMGQIS1VVLUPEek9SxAjLMVqNEQtk4kWCWY2zs1iteEPsl3UowmO4CjVEpk1BcO5kyKQrgshwYiVxFs3iClbhES8mawv5SzUywSq5uGwgHw/sECxhi1QG4HPfqUTMDr1DW8wrCRXyuIi8TGrESjhuHioQ2II/r+IMG9QIwKLIKDEqACCkhlGPctXSFO6mDfcpu6hXlzBTZByRUHcC7XMtRUTzK+SVuMXuLslZRndMoZttKniyN6zZz/rEsSGDFd3j/AHlRQPNZ/wAzJIPH/wB5eobWE/3h+HPv/MZQAeP95SVb/wA8xsxzRDdCeCi90AtVdW8fxA7MuHsPQVdd1WZ/QffuFXV/33Ohf99xa3/n8xABnPL+YniHt/uOSuf98w9n/b7iXjev9ZXPp/8AaPb5CoT7iSzcb4hUQXuCFjBucCCKmy4C2MSpgpVeosou54JXISr/AIY8kvN8QAU/EJvMpEyojnJCGBbgDULWXHJC9iU4S4ywTgqIWTcak0RUug4ZiXdkx2nMTKX8pmoagaz4jBRBOId0mOdkhjKiaPxC5xBjdyx2mnzFLjMAXUResyrlBXA5KlrUqckF3IC3Bo5gSSCazXmCGxGTxLtzG7QHiDqaVBhzKWnO54hbruvvSCBBvz/yYMF6f+Rup1aAiytWQERsKtrAs6srfVjigWi3mjCGUF8DDxfF6ebDU5KErmN9WprAcjwx3ewOiqVQdxywyhZHYps3Y5h1A4DhtyBzcM7vDCsCcMR7gVG227HpFD8UgQOQMQB2mRZeIGbfRw8XC4Juiu4i/FQQP+n4igU7/wCcROkE/gBaEvvjphumyRhsvPJC9yYg2B8xeHoYNgl8mH6YYlRLTNJyP/2ovFmABrA6W6mfN9agbR7ZXCTQpoqg7ZTRSLM8l+wt4bhjnXAYMRo4CNDhiKsFr5Sv66SluHyYe6vF1KjUF7y9ZjDU6EX2dw49hVljZXSizwDdzIW1gO76ipZdNw4IRjM3Oo8zFHtpiPKxvyenKK0OWg+oqZxdf7Rv3DRFKFyJZC5Ba5rj5oegmm8RDmBlWr+YpwLBW8NgwdFMDYUDgtIcXCRnAMAQPqOxfDUjbGCKxz/WlCnL/mFbcK1JmTX7JQM05WSJkxMtesQCCCPL5QHcqPB/5R+xpDY1uxdW/ctnn5aOFwqK+Zei7Kebii4r0oA92U+RlVP2sCtlxRbL5zNcUB1CuQ7L6YGHyuGhC6cFEOrNRRZ2QvxLgQi01+6FvR7HAOgDb+IG9FqVYsB6aHjTxEQrCxhq7CjZvFQyY70hho/ovREsDgRZVQAjrWpd1BlkpHOoCLPSX3MRHkQYFYgG7kp8TnJRpWS7cMjOr601Qj49KhZwTXmWoQUfhiEgyxr+vEBBd4dPKC+Gz3O4F8sOx2/6yFQMwwcXqkyxau9xxV5FLHyfsl0UVCZwJo+EbFyEBWdBldzQKDzK1/dKcB7/AMI2cE44ThwPAjxFBXZMd8t583HboWoLNNiQoBl6kSMjDSjlWjyxqDtcoJjkGgvgmnM/FGpm6k2xE2o3Cs/4udj5L6b+4aqqSCsNtxfkvN0o6ejGQ0Cpqt+FsvbOMWhvBuuNTyvRM0vi5FU4ZoNbivYWgB5jKMzCQxActQQWDJAopDeWj+uMOgzS1pGKSF2T5/1igJ1WUFsYAMDlXu9ql5e0aNpcEtaR+ISpqh/HZN4FuyubjrPSgVWgeVfKzsaLeT8wX9MPhtgYPgFicpj87CPqU7aP0mgSYXCtWZixh+rpFT4EiKWjG/eGmeb8yW4ipFvSOBmWxhCeh4QWAt3VuOzO1UNwldhPoEFoBVMeSF7xNB720/hWXYRV1wCILQM0ZuCqLccUwfF17GZ+VDCe8f6QgE2C5EsfDCRVY020UntWeyWi/TweHwKT3L29Es16I1tDzSfEwoXOIAHRgVeN6ihZbF+bCsbRZa6i68wCrtTzAfLS+q7hFukRUZhlxTa8JY+GU37aIKANUzWN0y6IArau+BtWxQqdqDuO/cpyQ0xNXuC1ym1S21viNdUsvcCzPD7g3YpB++rv9Zhqm4SQFO4GFxNEWVDWFLOg1daTNJ2wAGGHwq0jx4ksfIP6mXL/ACjYhRkHdfqCxXxgJsHDi+a8w9o1RfviHyPxOY5MRyko+kTL2vqLcdalNqvbCHRrAdnN1mFXhhmefK7/AEmFWnFEFtxSyEEjjBqlagX0IGzma/WDYEMYdu4MarmBGG84yHL6s131D35iq/dzF1gFc3aHLd3FKdNcA8PXcPACpQC2KNp4ND7vuK/ORrr9h+CdRWpYlytnINdY8wxeHKC2I8Iwcwhv/NaL9J6lDN0G7QPPPBB9vxEBnfyn9eDiLxNBB5q+8d8XFaSrjLDxCHJTV1V0xxCgvb5iOG+ZlgsWepGwUyzoEdVhlEKKEC+5tZ6iCYzyStWxzFlZ+Jkx7iYdXFqlRCo1mZA5YwB3AShqHNGBHDiWrI/UdgxuoWdfEVDmAULicwb7lDIwDZSANRA5anYQfXH6jxX8ytYxB3Y+iF3ZcBmmF1t0weRI4bRhtF27xKCmai8qYL0RUtiO7DcTkxdQ1aZZPfELYyx7mTOHqBtGkj2lMoKOq4gQFrAyxEnVSKFsSWFcSrQvmATGLgmKzUPPUAzREVEoNFDBXOZYyDp/ohRK+n/2iDYBmTa2fVP7IQMhYib/ABGqafLX6jfm7/nmIv8AG/gXFwoP+uYmV86LRXp/9ZcROhZeacQG4Oqe3xbmD1/1eYFoZuCvYZ+4TL/weYHSE4oT7lkBeplGjzb/ACOvCKZQi0WIokDo8h/2iI4UW7eiIn1VargaOLEallE+glBV4OIieZbZ+v4VtPQx07zEBKpW4y4t7Yi39yijCJCncMgpdk9AqCxKgVGwpNiYvYQKTBDCo4gbIgWwr9f/AFlbsX7lL1zBmt/UBSO6UL3hpYKAhYnSsZ+AjeO6LBYralVlbgcE3PgCaAeEEnmMmZSqrq2+mXMSfQ9gwl5aqftAqg3EPkfKFQB80fM5zlW1LMJHaAneHjFCYq4U0bmaGmxJuNfUEKKwW6xM3X0UFBa247hoLOD5NsgrTNttQ7uE5GoQXos9whynVEoyquOWGIpXUWruit7Dijaal+4Nu+IjLEwGxYWC5gdxbYhxj+Dj3EhFVsR/Mq0abiLKy5lyKymrgiWVMgFHdkeyFasgrItJjQ5j8i6fq0lDVW1IEgEbtwBbIXF2xe6TmUp1pAQWzAa7RHC+7MJ8Nxh0nvNBKPQsDhtIygvHfgripU6xsDg1AUQyLgaAs1ODvkKYuhHadK5V5gU1OhzGy436CNHoZuD/AG6Rherq9subiKIZTRaepcC37mRkcRswNPHiGFaagOS1Q821BJKNsQDTyRQY35i0c+ZuzH3n+Is98S45IBYTPERWzUpiVXZCaXxAfcYLxmBVBLJkxCcSt5iMdCcB/hDuziYNF9x7cLv+QtmVmsvACoMq1V3rxMuFDPxGllP5gqGJqB4k2gzWBseTeo9Mo3bzCrjr5siKsfeSuy+FK5gXy2Qyy8WgqBQ3nF2v+cVl39lpVUAcWllqgfd0JbKpLSz6kqoE5uAVsauYHh8rJXsnQhHsyC5KR1SRXsnhkco/YgMKflL1Mj2prBnsaPkBf2QpC3Ci8qOC2W0ViLj7rMEuZVtr9oiqo6QDAeJmLjY3MNDHceYZT3RbEZVA8eYejnREuBAGOWX/AEohpyLLFTLZqk/2pTEF+9QgSpWTnuDFQT7Sw98LBXL3G5Q0bsgc7agi85lAWh3zHWuEWxW7mJVuI35bhLJLQUl7UAcMEbVChLmJU5LSYhuoqnriaU1xDOH/ACbwJQXgTbK/E5UcQA2wGvMQS8xXl3DSORGhQaqCxa06m5mLRuYBiBjlgZhq5RiGE4bIUSPZzAeuCzMYGoXFUN4FLzBBN3HqCk+YNNAa8g/7GWzwuMqFNPeoIMLZpxBRzmA3IfEC0K9xr7QpokVgy26uYKVTKBu3qFNmgjLBcPK4UUZqiNszs+pSs/TMohRBNBqLWeTuK1q7gLy9TAvCoaEgfaI0S+pa15lSS1xWmCaRqNbSPG7lG2WLMuH8VUcRxpiKxl5IXFySvsgQ1UvxoRvu2ZhIympxjNVAsqK9eBqDYoiX5IRLjtB5IBoXYpRScxdGG41KGuJU3UJzTiJWK1BgQtJMlfqGncKHUKF8TRNQAvLxAvSYNL8QtgYiENGIpGWJbv5nuPc0uyCBtPzAGlDxBVyqYzyMscYM9TK10qx1MCwV1K0MKpC0H3AYuD+CpHUHqcUCjyRdipovBMhYQe4RRSB1k1UR9B0uxYtN6wZ34iIl8hnEo5rNTEFvBuJG+RWeJTirPYw5djjwxLXslAJr1GyMwV4swgoDiXsriNV3GLC48MS5RkeIDyAzmIvIHDuDxhu4YUVY9I07RLncyDKkClywKYK6jA7YXfeOYcKjm3cWuEbOJcMpN1GqPxmW3H+F3dweP4tV3LFA1ChfEpV3csZg3agRM4YwrFf3DggR085g3bXiooV38xmVlXKe3XMZbYsPJEixNdiURA7tN6DZcErtLy9jDAhRxxLsA34iItFhqp9RQdvRBNh5ahNgXuCBQ8ylUDxWWWKpVbSIjRrQQw9HEYoJmA4IgVUqnMLueJQUL0iFGWKpqNszRP8ASUWRQq2Zdx1EWJTmGokuMvzGMPqIYoY/MVVw/iIEc4gGOi8wojowHJAXAOOZjUKzmIsld4hdV+QlaKgpworXVw6NlsOvuL46slvCTmzMwQXVkKMA0MsILFxFA6MTKbdQZU2mMRgUlupuN7ich7xhQxgcEW9rr8xYMzBUVmW5m7mO0XqAHDTCK+48tVUaDMFZjzMdWtTm42/wQMiUalrDU3qc5JpuLcNhBqA6Yicyxu5dSwbjpjjdEJbrMKs+UVDxCLa2UMZ9b6jVQHbqG0IoONW4sAA4TfnuM35HR8XLY44DUxLreTUaZWauFJQtyzSK8y8MAZ4DuFReY3BqCvFS4AnmImqOYuKMHcQdM/KWOVQ4HxDBLAffiU4fcrXh+Yqu6IlKxUZBwRUTaszGpax1CCW/1GVLZfUMvuPBh2lBiXia1K2NygHhhVxdsMof6gOzfMKv6RhxzGQiGMJy9RSyt8f+yiAs7vMIQCt4GVaMtC/qJWXC1UOdFhuIhoZdjMkpHTUAES9VbqC1ZLQaCXlFm07l6xdb2ihYwhNHuZK+Iti5jB9QPLRDK9p0teZ2FllBLLLiAtl52L1UtwGIwa3KgrgTmLxLjFO5Rsb5OoPv+GtQWJg5IE4H1DBSoBmJrGjcMljXOYZ5GIMKx1UEEdaTmUirWkXiHFRT7lKFGrdR+wHGAISAftKIgOMBcpVC9EDdy/ZqVRrH6COMqvcCJbO6ikvKJcqTCfuGzhUwQpi5VbmEqswh3TB73UpA/mL7iDG0tKfSdCJTmMWFy6lyoY3UwcwFDFG5k45lmSJ1DzBxuL1EpkuZEbdS1YfkqPWPviCeJ1FsSvLHPBKGaMwECvZC7E6XDGT3VP3CklHw/wCQwUU91FEAu9nxFZVu1bWYAQ8sOV704mmzpiilOA4geGVwDLDGGI+9RBtY6gSZLYsQcynKLjdxbn6jVRFPMti/wXAlSmaTojqqzNXBpjDlYFZCJW9eo25mnJBiO6mtGoG8tQK3qDZy/M3tSDndwY1dREwL8kJsPqoIpX3Ao2B5f7FAKHy/uCms9pc2nwjALRvyQgxmI9/U6UE0r8S9z+oZSRVd3Hc/MrzNy0rOoYxUYDAJXMruLHJU87j+oLMx/gPcNRU4YrZnxEopzFjVfxojANagG1if8Mvsv7gptr4lNYfUBdEtdkoIW92+4TVEfkUG/wDyLnA+oq2gPmMl0p3BeL+JQKSvUU4xGg3FziCwTKYqXLcGDqWiPKwv+MkIb/iuv5//2Q==
📡 API Calls Detected
- ht
- POST
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: OTP Stealer, Card Stealer, Banking, Personal Info
Code Obfuscation
JavaScript code obfuscated using 193030 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Equilibrium Games users
Attack Method
obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: OTP Stealer, Card Stealer, Banking, Personal Info
- 193030 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Equilibrium Games
Official Website
N/A
Fake Service
Banking/payment service
⚔️ Attack Methodology
Primary Method: Two-Factor Authentication Bypass
Victim is prompted for 2FA code after entering credentials. The code is intercepted and used by attacker to access victim's account in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 193030 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
equilibriumgames.info
Registered
Unknown
Registrar
None
Status
Age unknown
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.