
Phishing Analysis
Detailed analysis of captured phishing page
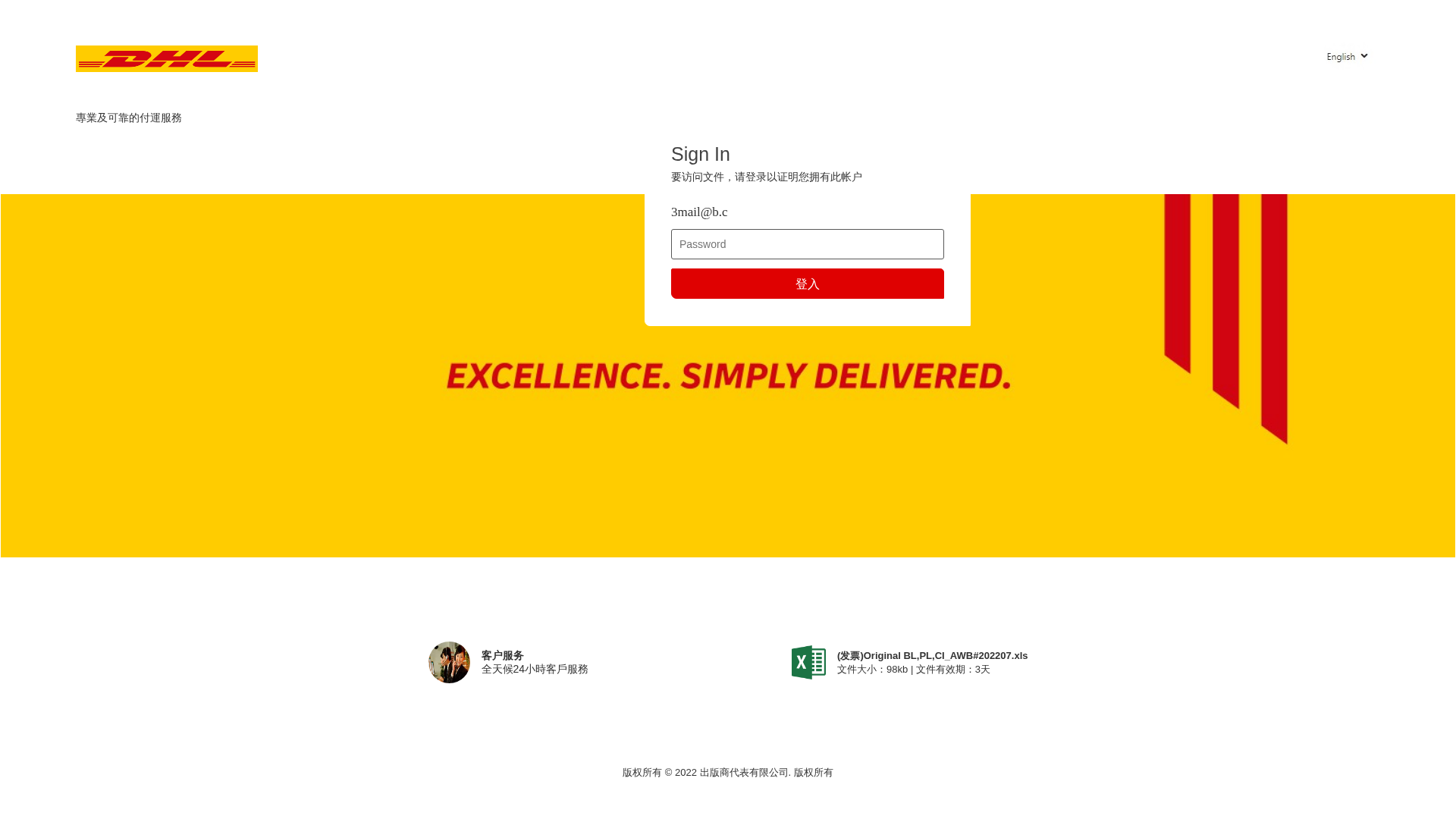
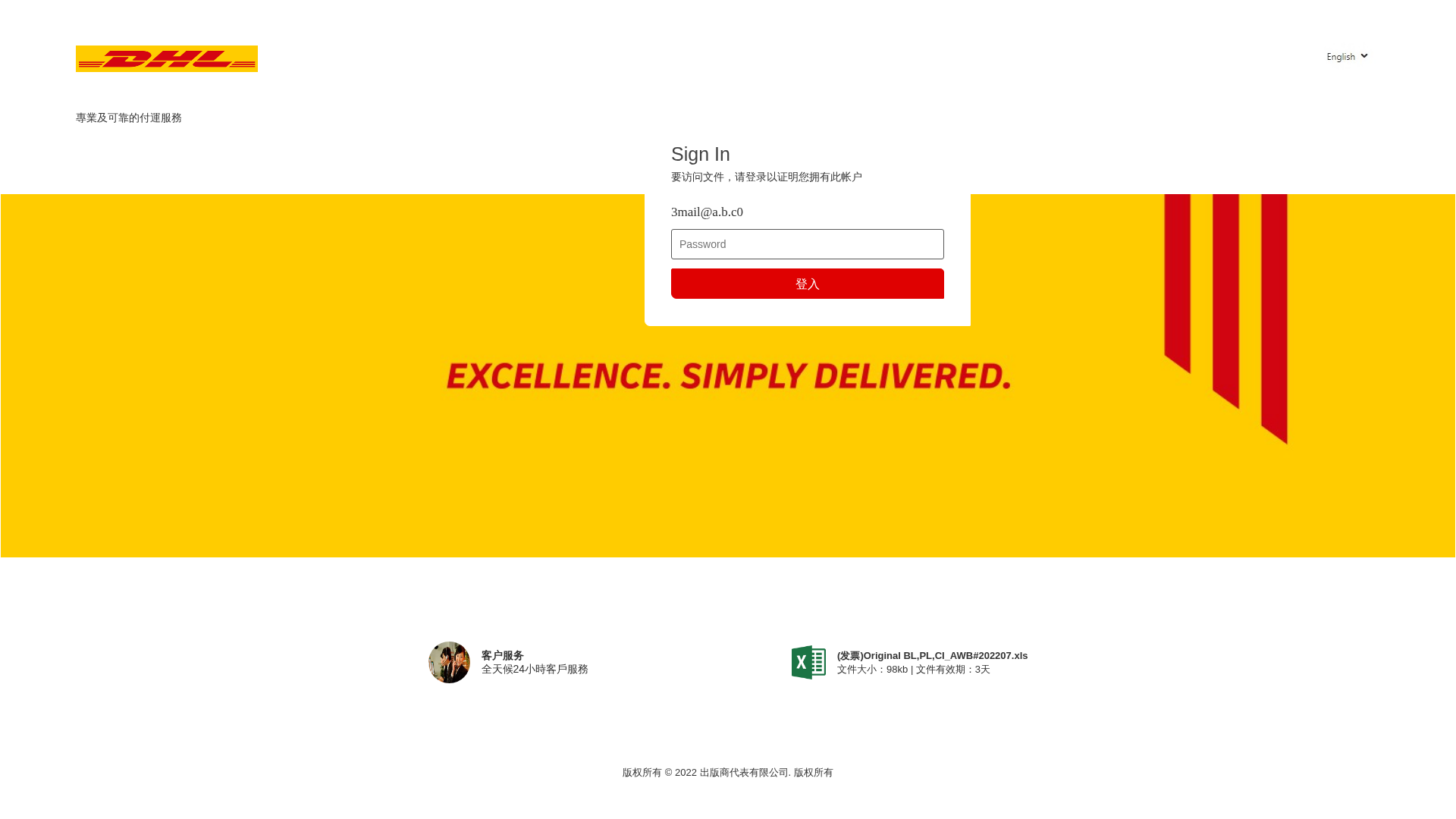
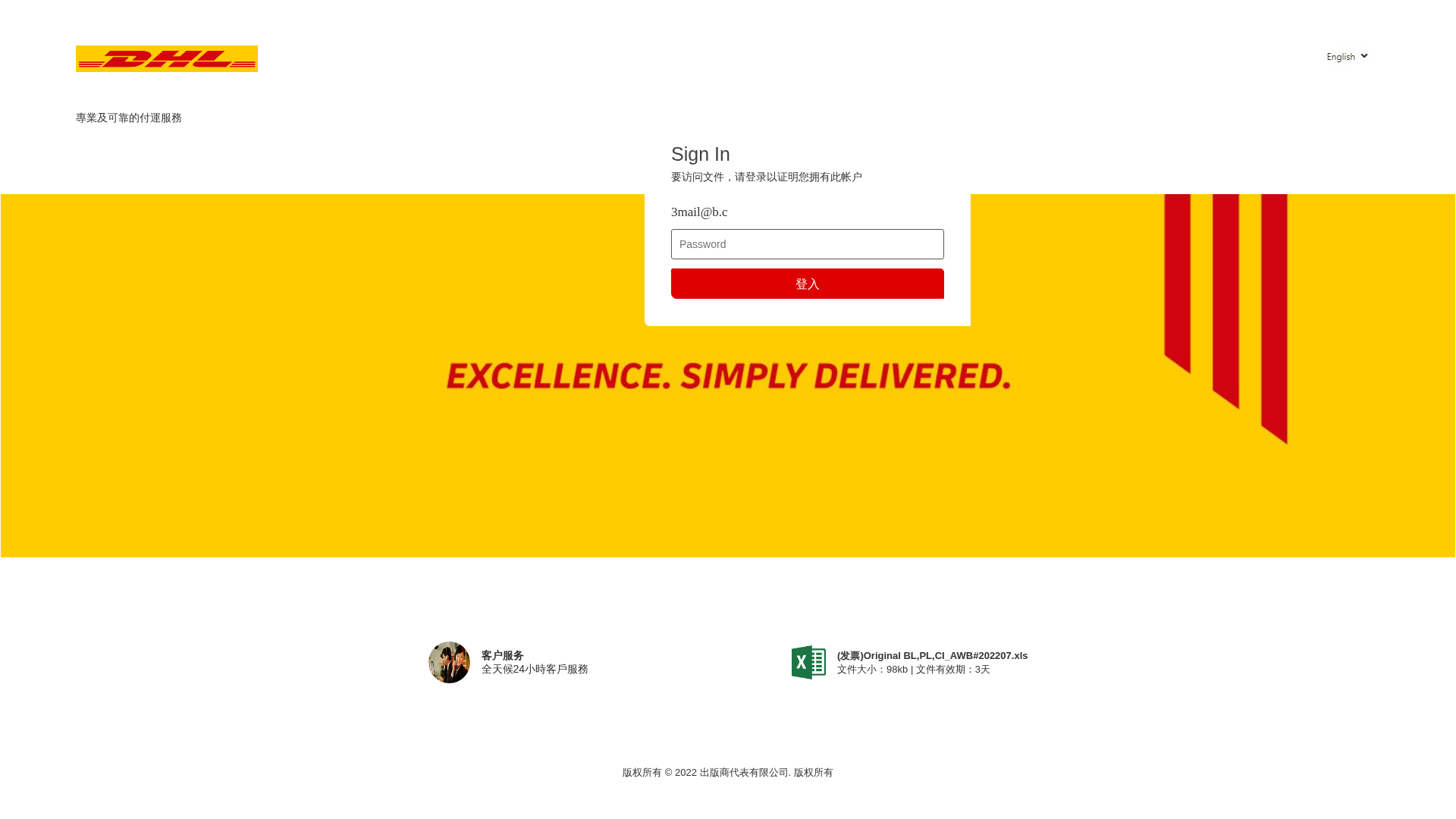
Visual Capture
Detection Info
https://akpp-volkswagen.ru/css/GlobalSources/[email protected]
Detected Brand
DHL
Country
International
Confidence
95%
HTTP Status
200
Report ID
113d39ce-24d…
Analyzed
2026-03-17 04:32
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T16951DBA0B3C46A5E94D0458BE1007FD5A3D0D0AA837139045E5BAF5FECCD0F5A9672EE |
|
CONTENT
ssdeep
|
48:fHfaRBRRZGMB+Rv441RrVCVv7kKG6bvtXV26/+SlRdaxrbEnCMj1a:SjzBmwIukKGOvxVldHI18j1a |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
da4ba5a5276e4a58 |
|
VISUAL
aHash
|
ffff000000ffffff |
|
VISUAL
dHash
|
c4d939851422340c |
|
VISUAL
wHash
|
ffff00000000ffff |
|
VISUAL
colorHash
|
06000038000 |
|
VISUAL
cropResistant
|
c4d939851422340c |
Code Analysis
Risk Score
50/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🔬 Threat Analysis Report
• Threat: Phishing
• Target: DHL customers
• Method: Impersonation and credential harvesting
• Exfil: ./log1234567.php
• Indicators: Mismatched domain, login form, DHL branding
• Risk: HIGH
🔐 Credential Harvesting Forms
🎯 Kit Endpoints
- ./log1234567.php
📤 Form Action Targets
- ./log1234567.php
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Domain unrelated to brand
The domain akpp-volkswagen.ru is not the official DHL domain.
Form on the page
The page has a login form, which is a common phishing technique.
Impersonation
The site uses DHL branding to impersonate the legitimate website.
🔬 Comprehensive Threat Analysis
Threat Type
Credential Harvesting Kit
Target
DHL users (International)
Attack Method
Brand impersonation + credential harvesting forms
Exfiltration Channel
HTTP POST to backend
Risk Assessment
MEDIUM - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
🏢 Brand Impersonation Analysis
Impersonated Brand
DHL
Official Website
null
Fake Service
Login
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker attempts to steal user credentials by presenting a fake login page that mimics the appearance of DHL. Users are tricked into entering their username and password, which the attacker then collects.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
akpp-volkswagen.ru
Registered
2012-05-25
Registrar
Namecheap
Status
active
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
DHL
https://www.maison-orbey.de/g/o/[email protected]
Mar 17, 2026
DHL
https://www.maison-orbey.de/g/o/[email protected]
Mar 01, 2026
DHL
https://cocorost-556.jp/mail/GlobalSources/?email=3mail@slur...
Feb 09, 2026
DHL
https://cocorost-556.jp/jo/GlobalSources/[email protected]
Feb 06, 2026
DHL
http://akpp-volkswagen.ru/css/GlobalSources/[email protected]
Jan 30, 2026
Scan History for akpp-volkswagen.ru
Found 3 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.