
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
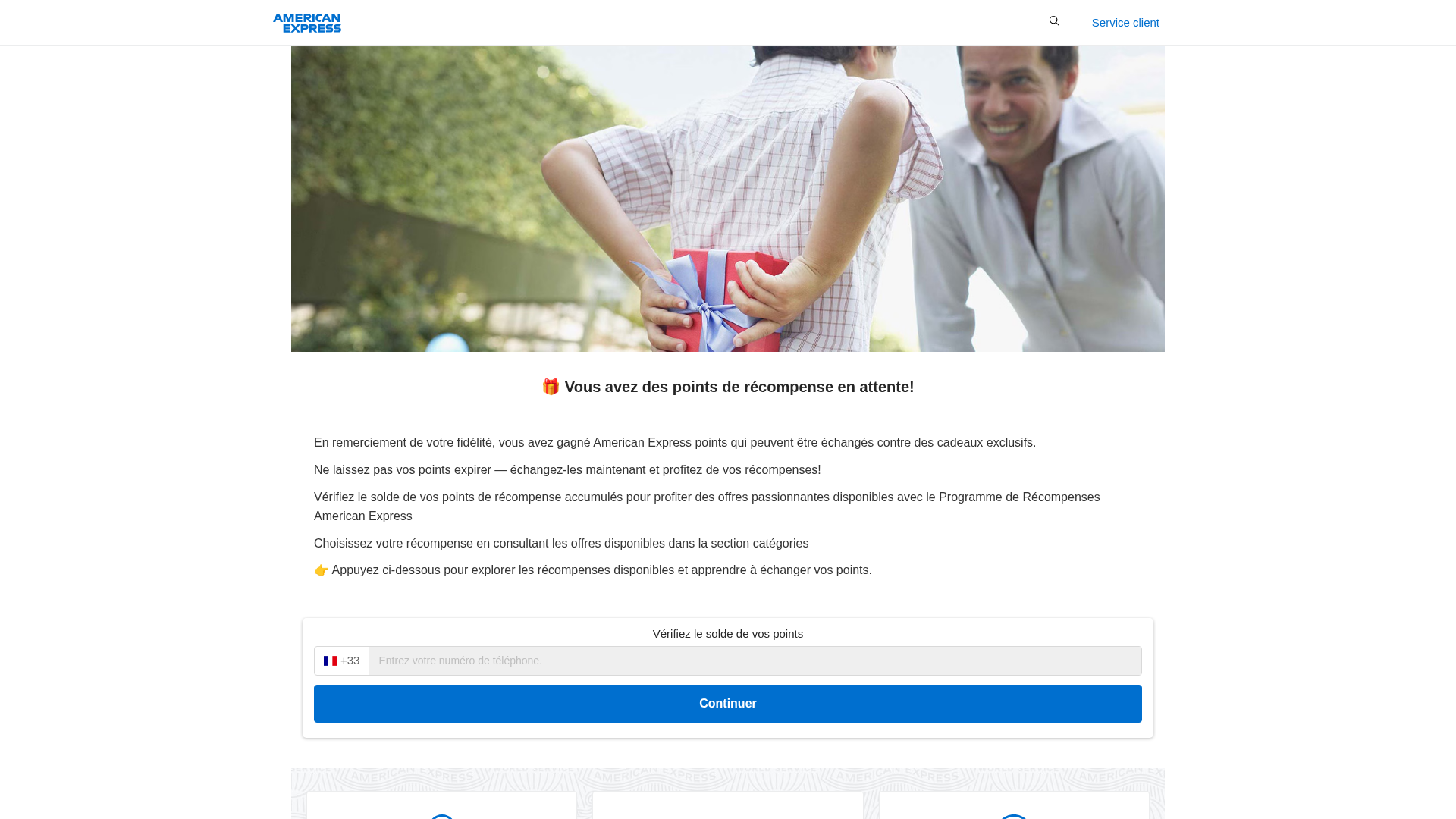
Detection Info
http://americanexpress-prime101.ink/fr
Detected Brand
American Express
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
1412cc35-c48…
Analyzed
2026-04-07 09:55
Final URL (after redirects)
http://americanexpress-prime101.ink/fr#/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1D48331E897B5B12F53BA71CFFA021D56E4C680BE811F1C63FB5C941E2EC3A5A96D1408 |
|
CONTENT
ssdeep
|
768:DQ9m4IGKKbNZSJhNewtBJOicqNXXXrJBv9SkrMs9ckVMWCQyYUwSF:09m4IGDbHgrVt22bIkrFeSSF |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
bc3c2dc3c3729269 |
|
VISUAL
aHash
|
938381c7ffffc3c3 |
|
VISUAL
dHash
|
32333b2b16280717 |
|
VISUAL
wHash
|
93818181cfff81db |
|
VISUAL
colorHash
|
072c0000080 |
|
VISUAL
cropResistant
|
32333b2b16280717,fbffffbffff75e4d,19dddf0b23948d4d,0000243232100810 |
Code Analysis
Risk Score
92/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- base64_strings
🎯 Kit Endpoints
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAEAAAABACAYAAACqaXHeAAAABGdBTUEAALGPC/xhBQAAACBjSFJNAAB6JgAAgIQAAPoAAACA6AAAdTAAAOpgAAA6mAAAF3CculE8AAAACXBIWXMAAAsTAAALEwEAmpwYAAAC1GlUWHRYTUw6Y29tLmFkb2JlLnhtcAAAAAAAPHg6eG1wbWV0YSB4bWxuczp4PSJhZG9iZTpuczptZXRhLyIgeDp4bXB0az0iWE1QIENvcmUgNS40LjAiPgogICA8cmRmOlJERiB4bWxuczpyZGY9Imh0dHA6Ly93d3cudzMub3JnLzE5OTkvMDIvMjItcmRmLXN5bnRheC1ucyMiPgogICAgICA8cmRmOkRlc2NyaXB0aW9uIHJkZjphYm91dD0iIgogICAgICAgICAgICB4bWxuczp4bXA9Imh0dHA6Ly9ucy5hZG9iZS5jb20veGFwLzEuMC8iCiAgICAgICAgICAgIHhtbG5zOnRpZmY9Imh0dHA6Ly9ucy5hZG9iZS5jb20vdGlmZi8xLjAvIgogICAgICAgICAgICB4bWxuczpwaG90b3Nob3A9Imh0dHA6Ly9ucy5hZG9iZS5jb20vcGhvdG9zaG9wLzEuMC8iPgogICAgICAgICA8eG1wOkNyZWF0ZURhdGU+MjAxOC0xMS0wNlQxMTo0MDozNTwveG1wOkNyZWF0ZURhdGU+CiAgICAgICAgIDx4bXA6Q3JlYXRvclRvb2w+QWRvYmUgSW1hZ2VSZWFkeTwveG1wOkNyZWF0b3JUb29sPgogICAgICAgICA8eG1wOk1vZGlmeURhdGU+MjAxOC0xMS0wNlQxMTo0MDozNTwveG1wOk1vZGlmeURhdGU+CiAgICAgICAgIDx0aWZmOk9yaWVudGF0aW9uPjE8L3RpZmY6T3JpZW50YXRpb24+CiAgICAgICAgIDxwaG90b3Nob3A6RGF0ZUNyZWF0ZWQ+MjAxOC0xMS0wNlQxMTo0MDozNTwvcGhvdG9zaG9wOkRhdGVDcmVhdGVkPgogICAgICA8L3JkZjpEZXNjcmlwdGlvbj4KICAgPC9yZGY6UkRGPgo8L3g6eG1wbWV0YT4KB3nDggAAHPJJREFUeAHVWwmUnEWdr/rO7p6eZGbMwMouLpdh30xCjglCcHfpMYCGAIoy0X3IIWLi84AVebtCiNNDgMRdeRzuouStuPJUNC0oQgI+EtJxOSRkcsEEQTCyKCsMJHN293fW/n71dSeTYS5AF7eSr7+rvqr6/+p/V40Uk5R8Xhk9PUIWCjKqVT19+Z73WkLNUUq0SqWOwfPDpVDTcc5IIVN45kopHBWrlKGULZWwDKEMQ8SGGQtpCBxKCBMN4D0OPIiVwHcK7xXqx3jOI5SxCFDfQ11PKukZsargfQnX/UYcv2JEai+ue+I42rV60989Vxvjuo515p5Ch8qj5dqzsc5yrIe1Z7ncZqtYbA95f+aFz8yUdnS+kOIcfHSC7WQNQ5p4g/bjSGC8OOPAWfKaZ9wbOGOgVULVCKITwmsAHDwLDQhBAeG4lvhG6vMh13hrKhO/GE0UCS8YimWongaI98ow+sHVj7f/iuPOg4Z8lQbejy5jApDP59m3wDk+88KdMy0pu5SUH3fTDTIOKyIOyiQwRCWFf/jFW0wcr/mDwWOW9eyOnGlcVwHAJwnBo0DQXFB7pzkB4KEOIK0CpHgPDuCBazwH1kn/0nJlStjSFcN+P0e2zg9U59Xd7b9CVdklumRe5Fn7kPIGADrAOoXCUs3uHzl/xz+BlDWOWy9Drx+dqgAtG+jcOEgwycag+AIEJgCAlavsfeCsAakRN5LwkdfJexJo4iBxvK4Sr7vhM80dYDC+w5hwhuAlUxHjChAJO2NNF6VwkJx51eVPLFpDqinO+fyhInEIACOJP29p9z1uuulcv7KvSriwSDQ65DRDUiGjvMdYDbIjHuoDr6EfcJ3IuCaE93heA0MToLmhRhxAqBLG9mvva8Qn+gHdahFDQyBR4Zpih/4xWZp8A4MBU1Io9CghutLO2o1iMNj/081PvH5eQSyNRtJIUA4AAPYwqiwil567dXM61XQqiPcBu41KZHFUVhE/sKVjmqaNgYQiCEpgh7gfgx4EgWVTqArOFcyajyMEEBEIiPE8NsnO5Efgp4HR1xhyrKgYE4A4sxxYrAzUQdOxiRmGEpUOyIKCFSm8T6NKPQidnjIywoQuCsCcOGqKGt2iFtWpkH7WaXQHgr5fbHzPvg+Qu0fQehAAjoXInb/klz9NpRo+7Hv7Pbx1NeHQzpjtyDFTFlGPokoP6j+I6o+aQfxcaFRebegbGpr++B6vCiLG96cpHPy0hS2uVRHZrJNtjlU0E6SeAlIXu0ZqFhWzF3shGQ4jwCtCKytZuyHVH/Tdd+nWM86p0soBYjJQapryojMevSbtNq3y/X0e3rlUZKhAXpOulZZ+OLQlUmrVtx/6wCZ+N35RMp/vwqedukpPT0H3M7p+x+gHI+4LuG5t7QAdKPkutNSZSLp+MPbPd9vubZfSWJmxMu2lCIoafAR+AgLoHiZ0Gjhhv7//q5968kOrajTLmkxc1P5Iq2PIpzHRYBzwHjkCvAo2NjSLieBL33x40c21rpe1bbOPqB9UPc29qrWwB/a2k+zG18mgaxX/+Gct8NTqLR0tsrm3WT43WC+Xdy+gudZ9f7/tp5dZpn1LDDpw1ECgugRJlgjDaM5F2xfvVlCKVm186TC4PmVlRRAOhmB7yj2BgPCZwo+Hl37zkcUFgtWKDmlX13YvgEVICmcL06R//w9+yAmgVIlib5eRK3ZG7ZDFzbD3vb29hmgR0dLCR279wYIf/96Rzo+hgDCXtCM0GjLIWq49qIZXYZwf5lj1lC1b+NBs17R3SxXSTsJex0BKhSkzY5WD/stu/uVZ3/ji4g3uNx44E6Lxzpf8QYX9hsHQA/zDjqx12fNnej+ef8/n01b638qqAsml10b7AvjA055S885/cslOzQHwWy/KmGl4UwPQ8rENyEIXCs8PBzaSeC0vD7T/WRG/4bhbXT/btBIivgQs4YCsR0MZdn6ssPR/AIJYN2+deV7ho//+k7a7z86a6Q+WAAKYmp54UG9kbREMXAD0dkJBEJr47DgahtwHpilCnEM4Oz7UqOpMIN7yBqTfiQfU3pj9eJ3oMOP6hocPcxtWZEx7bkZaLTOsaZ9xlbX9vjnr/nIpHbk92goIGfnXxrEnLHA1TJiyIQ9hXIZ9VWdRbKzLT/rZbEu6M2HClQWDC8MbpQwH1m1o+9ce/+hjmt2KeR0P/DGIJhGFjoLR3LtHi1+tzd7mFtVR6KAnN64SXdu21hLdIsjOXfylRrv+lD5/Xxkc7UAdyIG4UplhN/3F66pvNdq8kLpA9UDt7ZSPrZ//oyczRurESuwjaDEQP5XBMtbMvuG+WZbjWPMzpkPlF4H14e3FccpMmSqK79eDy51qiCJM4dsoBPHUnDC2oB0QGIsCvbexy8i6nO2RtRqPaYwBABwftSiMSpjiiMRrpwcYpMrRIJw09f51rXkHXOCva13niB7hIwpd70rjxABaHUYBOk4GdWbKHgwG51uW8mc7wkU7MH+EEhCJkCwTPsrOW2DmRg7izVzXiGknB1VB3HjSzYf7kXmcKcVfwcVgCE3jNQD19DvLsJ5vf/Lzf6jV3ZzLWwRtNBCYnciEdYPo0higgJmg5PkshI/c3HyqBq65uVmf4Wk+Fkn4dXEEd1nXFXTXgccsCxdHS8q9Rgb8KWMzjIdDy4ieZ9N7YON5frOFg68Rfl/bLe+BW/sJdH5OFIo5GcPKOrDAjB0oB6QihFvtx8HQ5gW3PgXH62fwgO9qL37hRfZba4s2n/dWrNanLWuJF0Cx6SdoGY5Og5nKvB70bWyHmaY1yBVyCQfF4fOBjDwLASN5AAQBhhBJCnWUBdQOk3FANGn6lMV3ItpXCdRr7IweGGaAl1MqNRlvLywN72676d0ZKTsh1RdPt+vcSJFIH8R6MRQTxAGA61aBO9SPLY2sK+2FAGfhgBq+9hfzbvpuEKt8e/GK35OgLYUtmqDc7uXf3DLntiUzrIYlZbTHGYIVA/H7nvVCuYJNVidOT16dF7zmZ+x9UOrvDujW0rEH4MhbHA5lGE2H/ScH4AhpT4StooGWJ5xhNpTMEa8mL2R5KjFq4Q3zbrwkK8SvG83MclvEbikYCPyoBL8kVJaKEOhEAD+yDRyYBAQ7VEGh8qJyNBQOBhiY3WTXXZo25a8fn/v1S9kmRUEBCI7k1F2fO6sv6L+8EpUe9uPKI/v9fTeo0F/woZ5L96kDfkIC78ZnXxqGGAzYoAb9wcrB2uOMoG2aXHXKXc8D8WPjyIsZ76YNy0Sws/vyxy+eg37YwpREgMRzgBzcz+ffuLbBqvsM/XGlIp+YommyFnU8WQ31qG9q8PKa73RQyLCWvMEPkA4znXozI/rCwTtO3nHlp/FGEARJUzdGIfFylPJktV/MvWM7gqV5FRVGJMgxXLMShy9QBNIaFShnKgYHaSYoEkYSYPw87e6kAJDtQYomfuP8f72n0a47tz/ALCIvgtGQqUggBqyEa5hmWtp4DBWIfzwzscXiQRR9KDhU43NwLE1cHA+qgbDZnnbJ1nlfn/G+HVd+mMRjXLAspxq9UNId0FNr295tLuteBjc+GYduED/VsVHBl8FiaJeczikgB8RpTHrUQPYHO0gLWtXR3yPvxZKvHryeoNCu07RtnLfm201W5twBv9/D6HUojc7QaxyBaMvCBJdCb++w9DYjzt+JMPMVg0kzJQ5H83ORZMxljdSxeC4qcUBioCchsJiw/UGf12zVn7Nt7prvLNj5lU914qEcmevrFvFysXyMUXYRY1qIChHV+Uq6QVCCQKHBgnxmmJwA8fCUYsqniOg6obT0tPDjCcvtbctsyGfw8PzVyxqszCWD4QDYNkYorWcR5EPQzLQ1GJWegurr9HZtvq9dFMd0rMi+22aHZ4NJuhrM9JxBiKVuJWnK3R8M+O+y6i7ePmf1E3LXVd+qWYeJBlhAxIjJQYl9AgBlj189LPCdhDHBLUAgO+gDriL+gRenULS8deeDzSfk/wpcdEspGCQnmYy7OPNEr86wjOFg6GsLd3V+pdYkB57DTbH6gNfdgy9LibbEU+Je3N67Y+6116cN52ov1iJLIICpsgbgsoOBb9k+77oH5heveXE8ma82feCEcVEktQhoKwBOZ9Bv2ZrwiByAAwl8cgDlcAqlCO+OTothmNc1mG5qKCpr7V1Ne6mMYRtD8fDnT9616jY2tw3csqB7baj9g3Ha39Z2u93WvTyUO7+6Yuecrv9Om/a3PFiOJJJDf0i1NVl1Tl84fC2auEgcmOGxG6wlXejiJ/JPPwC6h6YQXE9zVCUeAPAaB55phTZ2k8lTIk9C/mt2/hi4pp8sYWbwLXwL+iZhON10jHI4fMPJO1fdRqLIdiCenAVixi8LupejjhI9cGfn7uq83Yu866YZSNUgEYeDM2gPhkMYo/jknrmr3kuFyLGM32L1DWiCaCYcoIeQXMMfI+E4kGWlGPAe7DzhINlkd9vL2h5jqeeCJhNJUhVR9sGnUZSVlj0UDu84cff1K0i4nlFgPukgqxWg/FRLTz7gtyfs6lpZCkvbMtKExYIBh8cKG+43WimYdvVJfqI5cZLGsbjC7BZZ6AAIaEgYB2Yd6FJBaF0gtdxN2GRb9+1akVkyOjsSFWEYIZa+dCiN/DmcDRmsTAbXBbdfQz5he6Nf8pvutuU6X4Hk8ldpqcgBkGXmd0wfehrccBa/m0ikDraLMVEHoB2CoNsjIJpoEq45geIAHxk2cqKSB8txlraeeMWRtu21xsaQsEzPsBwvqocj4cvB5+bu/NoGtjG1wY3dW1VkROtTNzyATO8zKaZymLOE1+hHPkagZj0zN38Uv+aYxm4leZqIz0EQqKi1TqAOSPQACJeBsI1AuKav2bWmQEY33NnRQwUvXCucWe/GKcP2Isv2pW16cb0LEG1/I2eQ2n70t2/2noqT32DmNqUwXZw6epXIdERZw3agbmbyfSeV4QSF2pNE0/0CcGwPnIDDxozbJgn3hWP6wrU9gVmdoCm86m3VnWHG35NyAZwVKNv2heUgi4RvTbu8Y+IGpv62rf4IPRlwqXfSe9ODpkQhsHchdFA6R7K14qgES62HA88NrUAx64fqAMu2fBAPEChfPNuRcMQkAFRbd+xguoMMoiU0O6Jx/IemQqLiFVbJNWP95G2WYvV7zOAriPY5c5p5GddrYpRelp+0FzpBBnQT2Z4raNodwpXlcMbxwpIhMi0g3sKCPAiaSjGsAPqeNHtoktTDgdcATA3AqfRRqwMC4FqRAyIyLjgAK5JgZViECVm/9r1mfTg/EouQFCIqwQggWmR7CzNPzW2CTWwAYB8AIMn4H2ykdlXUF6bj9UOGYEYDTTweKhfRRUmEh7FCsbd3ioPTzY35k6s9ldFhNnizTCtQnT+GtHC6sBY+edHcAt6BQwRjTQlCCAYQtAiMBMCCCFhyYg4oVvuTZvASjCtkHnELCrkAEQ+sSMBQWuT48zYLXWQ2AaM/x0BfVGAsUGhGiMw1tPvveD+euOWQbOV7HSSC4IQTAAC+pLNuaB1gBdTcVGb6bIK19Ufj/ORyOe0p2tJ7zpcVDwCY+AbrTIHhG/AJ7GARP5XF4sT2dJz2Rz6umUKk6hYFCFEw+6AdS8eIFEuxF8RG+JyuX2idWN9gBTpRgCAdXEBOIBgAAERDEVqwBPqMez6bqGDlk66iPOKeDS8advhMnQs/wgpjAABvoBJNS4uW1zvOOB1tKJXLvWVTqKpm9MXZnzktbchZnvLpCSJhEsdpqH9ww56ZT930G44VSZAJAdAeoOYezn0CAs2igZlLZh7n2jWImZAD2GH3sjZNGL65P50ikgQAesQMwQnQ1k50LesJcAvB0tdv4kd/k8MUoZi26rLYJnQVWBltIZMBABDTr+f7qr8xIQCa3zXjs1pyaE7QbE/ibQIAS5AAMumA246AB8ymzPL3BqIyiUZWO1DSDq2yqASNWXly34WnXk1uER2tCIamDoKu29Fh89s/LDz/Kw1peQo4C752iAxTCMmN7T6sC4AHvscx5IoJULwet0D1axNIJ6gKRBUAOC8k3OSRcAFmk/pswqLFIJ+zmu949FkM7IcNGUyQFYV69s3QGozLcV1aXN9/8SkXyEKPjw06UqH+hI3iJUUGy9AG9uX5r+TOOz/litVDqoR0VWBiXJD8MGiy2Uz4w6OevvkZ1dGBWAMgT1JAPWiqzj5P1WtLEw7zhwUjmEGwMvKziAd0pDdJm3hdTDpW/orBKOxAaMl8ChphZ9grA62bzZh3Dlx68pEA7AY8S8Qhn0va72nWQxE0lzm8zRcjKE4dZO1bfPY/27FYUwl8jAkhGoYIvQ3+l04/t8SpeCW+EEIrv/HMta6R/MDu6TwA3WjqAvI4wk0NABZBkI+NpIm1UxNmzIgD7X+P+HzMS5kHQcvabLl2696hL5x4ZV2ddfNwOQzRMJesmHiLkXkV9XX29cPLTzoLq+8r5bef3ARCNZGHNFpM7vZ/dFG7CO1V00zz/X0VDyJlgWexMw2N4V84w3adXhVcecTO7zxPJSm56jRBKRQScOBIgTKWGhckniQBKJsWdApCYJgGqVfRrdjRdVthWqoN6PsxfuTa7kDl8wZm+Jahf5y3sC5rfbxcDj2InKvT3NBV5cgLMilzIXJHG4eXn/g0unkI9OyMQvNVKhIzMpuRr5krIvP0tGHOZhJ9oFIOMSPkFO6IpNx6zXbKfa08uO6IbXfdpFNhkxDP4XYImscC2FK5YEA8oQWgM4VwSsYVKK6wz7FVGo4hDCV8ZXRpxGGKH3eJPE+Tllq97M07PlH+8pymdNY8vVKKfHAaREIvW9kV7GYi+ABiFrTFLO2O0dhopY7hIF+DCFeUfT/SVt4ysUjFrhnFieBdjuO+XhradNijd3+cT7v4M6XSiV7zpDvFZBibxFlZSEEj9deHBGxYsuD+GlSAJgGAsIEj2HZnXvMLLycseYpCXsu9SN+464yK5/8oVS+x3kKOitAwEiwW9IoVmRVsZauEXlCO/BDLWlEJ93BowhK4pCywzQ3sgG9MTAwsC7JMaKMxbSIHWC7MePju0zgQclx+CoqPdenv6bNUaQoRLQF+yAEEpQQ/ICrT/UVqC5oWUwJbC02bUR2IjVglUResPmHR+qAGwr88/QnP874kLbBSFqsg3JdhxgEOKBosgVmxjTPWKkGsoQ+slIaoh9VbK4pION6LaVhMwH3cFwxf2fjgfUs5gKq4Tar1dd3q2PMUIwUupytMCdA/mhcqBjobsODAsEMMAJxIAKLprx19fKbaCE9TKgQB3GCQG1Krn7lZxcHxfhj8EIuN0p1m2C73NOI6AQLa0YxDEAhZx5ngWJHMuMKsy4BwM5ZDobdOyPD4xp89dGMy61Cs9CumXPTki8+1fi6DGZ/GEDgpDIVY1ABEIX7Vhn6E1sLeiRj/ENyYqhE6YwZqDEJ8YGYPfKk/m+gHAMR5VNDWYU33b3D5D95Vs7t8P74AmC+Bgmtx04ghYY20/FML8oD8VypRUI7Vr2RorsdE3Vl/1y+fwRuk02Fp8lgzeNOlS0/zcDRtBnigCTKPFqgC6RToV6+C9aLfIiZmaMjNQgzuo6xr2MMV81jU3itaOlBzCnZ21OAS60C9kMOsFbl1fQWP8jUnHO1F6ngjio/EnDdoxRypfuwbeAkh2LMNa58iaLpshlPEwOutEQ8vJYf+i9jy4sTHYtk9VcaiPPgP/gQ5QAPwW2wDjJ6W2O5MNuUync6SIvkGHBZiFBvFnrce01MkMAytILtfbjPb1naH8rrde9Euj3HLNvgWdLVBOHaWFMetN9mL+mooDaW/0IWXVpY+xUdPPp0i6IQey3BV9xA3C9hwBKEqgA9TLdgqKZhyXkUCJutosvcJEN26HeqHIrgiN+qjIu5z6It1F8C3QLg1qsabv72/+wjyPCgWZwZgf8w8Jx+KQFpDSKtDJ2yX1PaDc9/3bDplHOvHWD3BCgKlxEXGsVxRJ2Wu2LZVrYO/vbSgG3vzw3hnvmCEyJT8C61fPhE2dSumGKLPCNKIHeyC494A2JsWBB1IjVlyvZWBHtDJQXidTAzWOcLOWiv18Jvfuhi8M+STm5ICmq/Bpg/eaA0I3saGCOhgFW9o7cljBxmK4cjv6n0T0Aj4UwB48giKIxlajemzwu/9/SWyvRiqDYvhSv7/KL8+7osuY4S9LZd9qk465wxj4w0IJwqQAWkORVhVUupOUiNr7F2+7f0bUllrcRDGAfZ1wAFBBILoGyty2NQUL7aXbnoQKx2W6G1Wf67iwNC4+zeNBtNoe+d89oNSuQ9ybyiUD9jfZCIsqDfr7P6o8uDf7L5uMeMJzRtEAuubKyAjixXWObFFHJewFoyPbfhKpvFAuGHJp2X7+jtYV6k8zYshcsj7dyHY6MxDcfDN1P0FXftt/FCTiTyOHphpHU5rc0k2j3538iUXq0B+h0wfRHT/9DYUfCIsuOLwP5QW7YLoSYbNmSWbe99fdL3TlL4am7mwvGO4NI/0jgCeYWQR4Vbi+0MpVzmLClvHGruONbryUv+dRAHLZyPX1opT0CNbklaLOOVaqrmCWkd7qknPPMAeB+iXcx9bIOP0yrSoO2ewjHxxYMPyYyOaTqSbXpM9zX0tGFpz/FOrr6opST1vGk10xIbDnyx5yGxInxZjMw9BQKYESgIcgUUDmXUt7KDibratAAVbaeVjcKxeEJXh18SWQikxd7UR/+nOGK/R25HLIIs3Q8r0MWFknhIHzhIrck924pTo97BG79kIarHjKXQw4YY33ap394WVTSD+NI6MNJNeDYB+kMT0sbq9zY6OPOoxsym9QA0FAMF0wAXwHeE/mFg+omJIYz0MWIgAlrSMaE8K/GmZHICwldBqCY3jjwvh3CKMhR+GAIPrWXA1ufGEf8YBlQSLi+6RIOJKPK+hdfnnCvijR6F8xMg+3PIAgZOHTI4f28pXDvY4p7AUkI4rKqPKcnpcMRpTse04UUpUPEMMedgGEmBtO3SwAxiyHzgK1/40g8R73fbgK3979G//s6JzCdVo8gAAGoSqvVfb2mw1cPwG+a7saWqI3hN0ATQDQaAthcvIBJWWLQgHwlzNJaiG5g5pkVCDQB78kzcmxGpnEg1i9T3P/FsNntkd//iLZ2zuxt65g0cZ32P4Ic7hsBL8+82wgrDeB6sjZYizEUWw5UhoqcAJI9w3igaj1/M2vTT4+lntJJ45xMJBn2b0cEXNKhCQ6JGLrzfSqatFGvJf5vSgM67RkyO4OklqmavigbGh6F86WzoOrxGvAagRD4L4N38EQoPAM7JauMYexgQIAKD/Ag4gKAAADhAxsmPKQzcAABwgFTbygSOQ08GgsAEu9rHDKbRjgBABBLMuqjNK4Iqyb6w5dsetV+nBjSKez94AgK5ILS8TZeM/+dl5tmldJxznTFGPRJFHFiXfQicg66fDa1DL74iGPjHcIgaEQ8fguMCZHE/i+QeQehsSN2IcAIHEo22CUOUAgkDiyQ0AAn+NCDkCCAAAWzkJBngLm1GjMrI7Hv6SMcIfzyKXM1iRFImf+4Gx4rgn/kP71CPZXo+x+jMmAHyHoUqxOW/K9iTpqHZeMS82zYuQp1uCROVxoh5JI4hDwtYkjETiQxLE2eT5EA7gPY4Rsw+JTepRN5BongkCdAvvAbQWA4IgsWPIwIFd75gEdAQOkB6GD20fl5BDHIDSKRsvgP3XB4Fx519v/kFCOFeXinkuIXN0byjjAlCrSZHgdc350T7Ac9FsKMM2yPws2MmjMfFcDZ6Gg6m0DOamAUKh02oHOAAAabYn65NwnkEwQaD8awVJELQYEIQEAIKggahg9cVXfTDFyKCpclwSg0g5v4rzXhxPRyW5vdlwd9fkm7LOIH7pCHnH7RvK/wJLTdcMW+xMSQAAAABJRU5ErkJggg==
📡 API Calls Detected
- https://ipapi.co/json/
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Code Obfuscation
JavaScript code obfuscated using 40 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
American Express users
Attack Method
obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 40 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
American Express
Official Website
N/A
Fake Service
Banking/payment service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 40 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
americanexpress-prime101.ink
Registered
2026-04-05 09:16:19+00:00
Registrar
Dominet (HK) Limited
Status
Recently registered (2 days old)
Hosting Information
Provider
Dominet (HK) Limited
ASN
🤖 AI-Extracted Threat Intelligence

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.