Phishing Analysis
Detailed analysis of captured phishing page
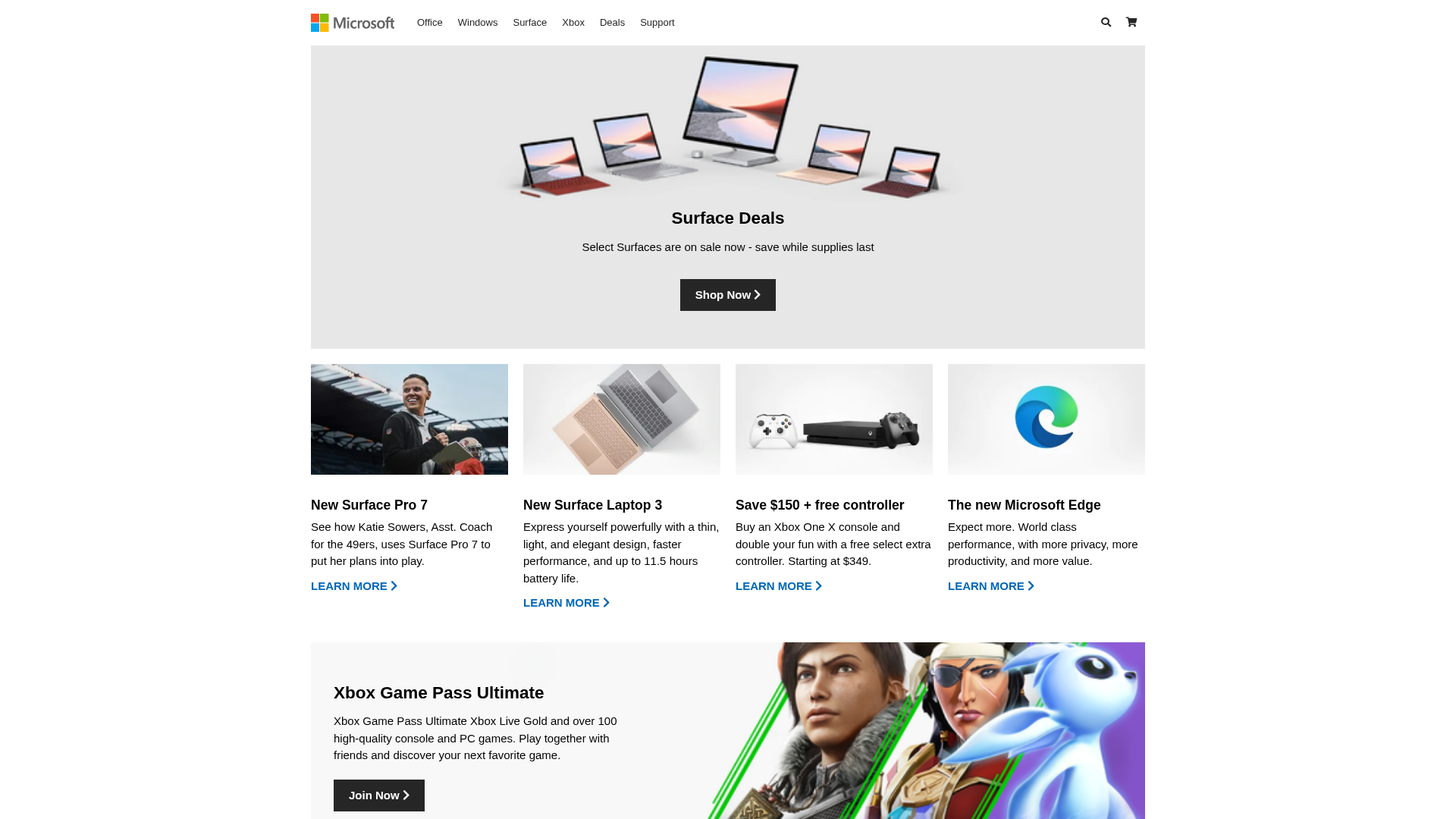
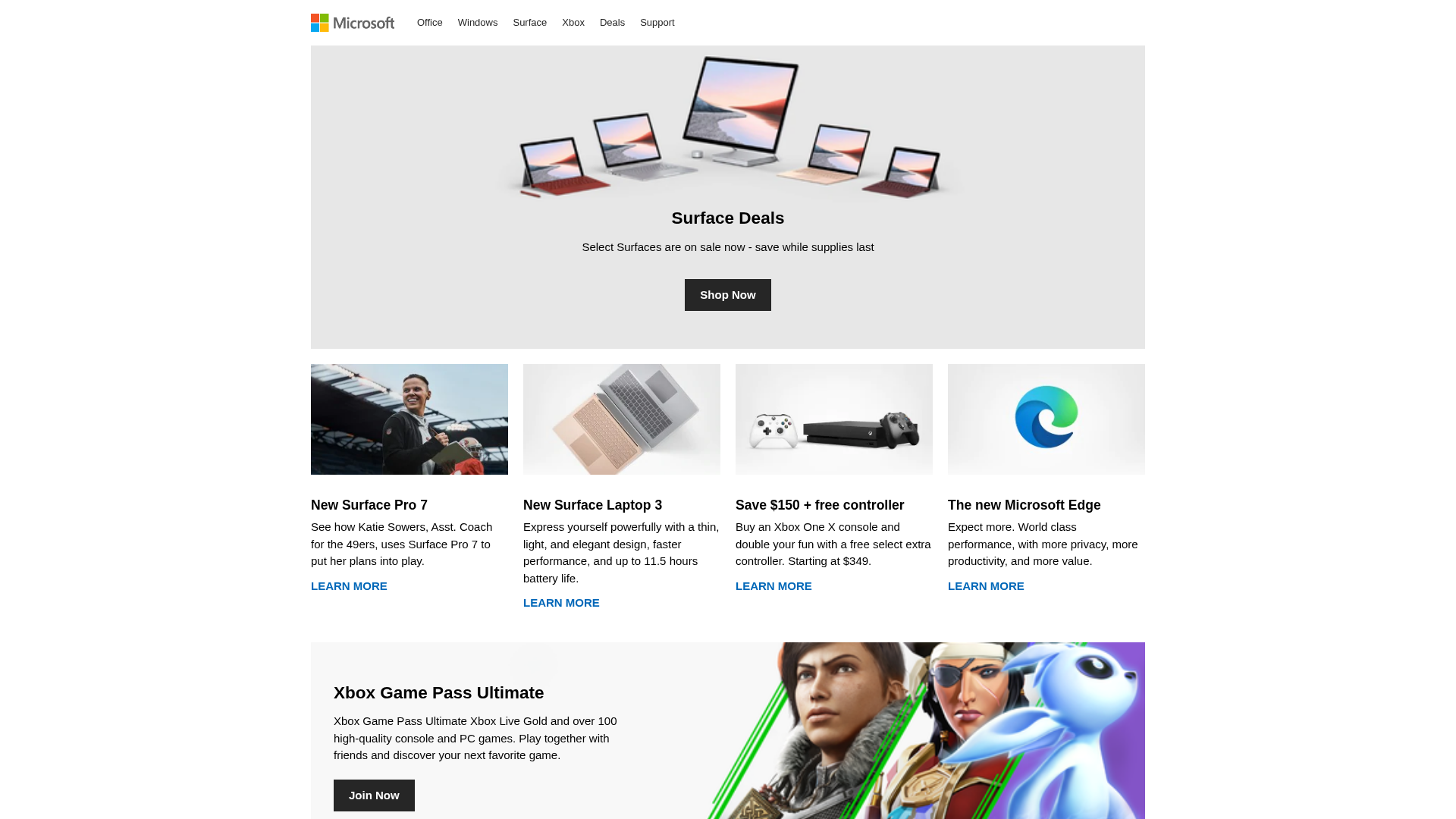
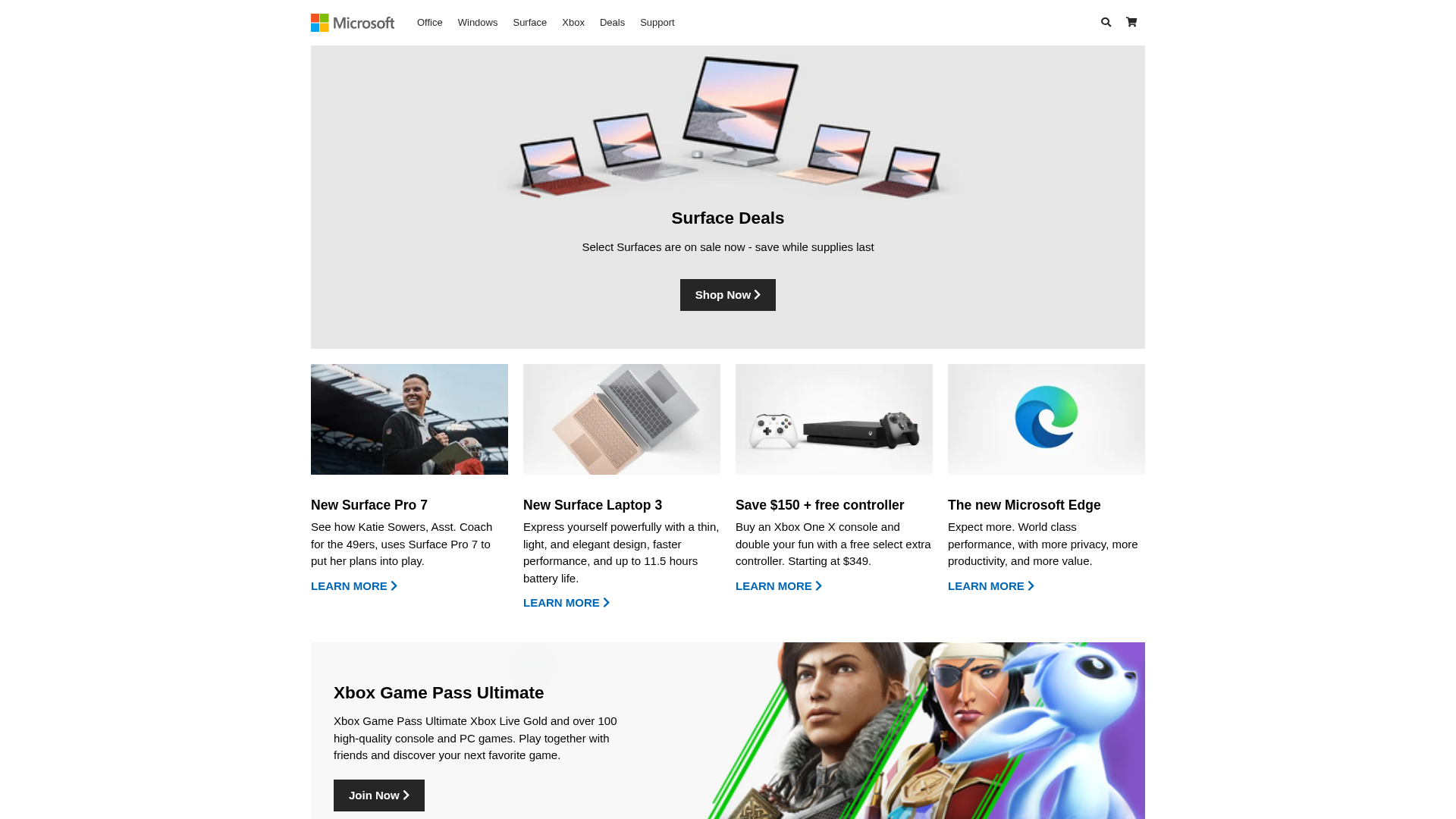
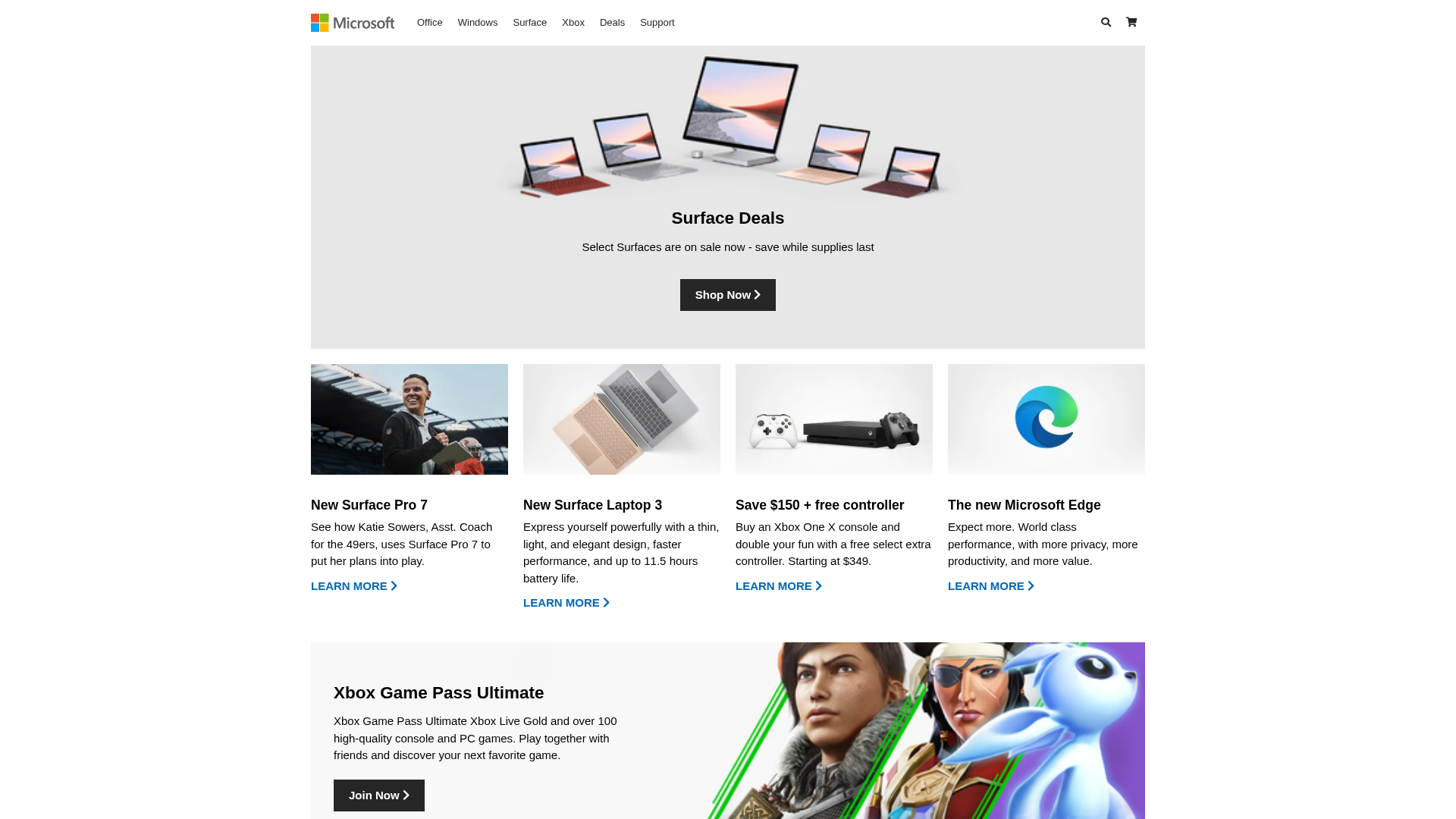
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T16BD1CE6230C8312B4B92739DBD15A75DE39B41A78B290F0225B55D0FAEA3A4ECC051AF |
|
CONTENT
ssdeep
|
96:TZx0FuzOYEtTOwCYPfF9ji3Pk+y8kq5IJHTTKt0Nz2kVs:l3uTyGfvIk+y+IJHnXzZq |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
ec93649b3cc3c32c |
|
VISUAL
aHash
|
e7c3e38383fff3d1 |
|
VISUAL
dHash
|
2f0f0f2b370a2727 |
|
VISUAL
wHash
|
c7c3c38383e3d1d1 |
|
VISUAL
colorHash
|
07401200000 |
|
VISUAL
cropResistant
|
2f0f0f2b370a2727,cced7c7e38de3f1e,2734050c9c2d2a5c |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Microsoft users
• Method: Impersonation through a look-alike website on free hosting
• Exfil: Unclear, likely credentials or malware if links were present
• Indicators: Free hosting, Microsoft logo, impersonation
• Risk: HIGH
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attackers are likely trying to steal user credentials by creating a website that looks like the real Microsoft site. They may redirect users to a login form to steal their Microsoft account information.
Secondary Method: Malware Distribution
Although not confirmed, links in the page could lead to the download of malware disguised as something legitimate
🌐 Infrastructure Indicators of Compromise
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)