Phishing Analysis
Detailed analysis of captured phishing page
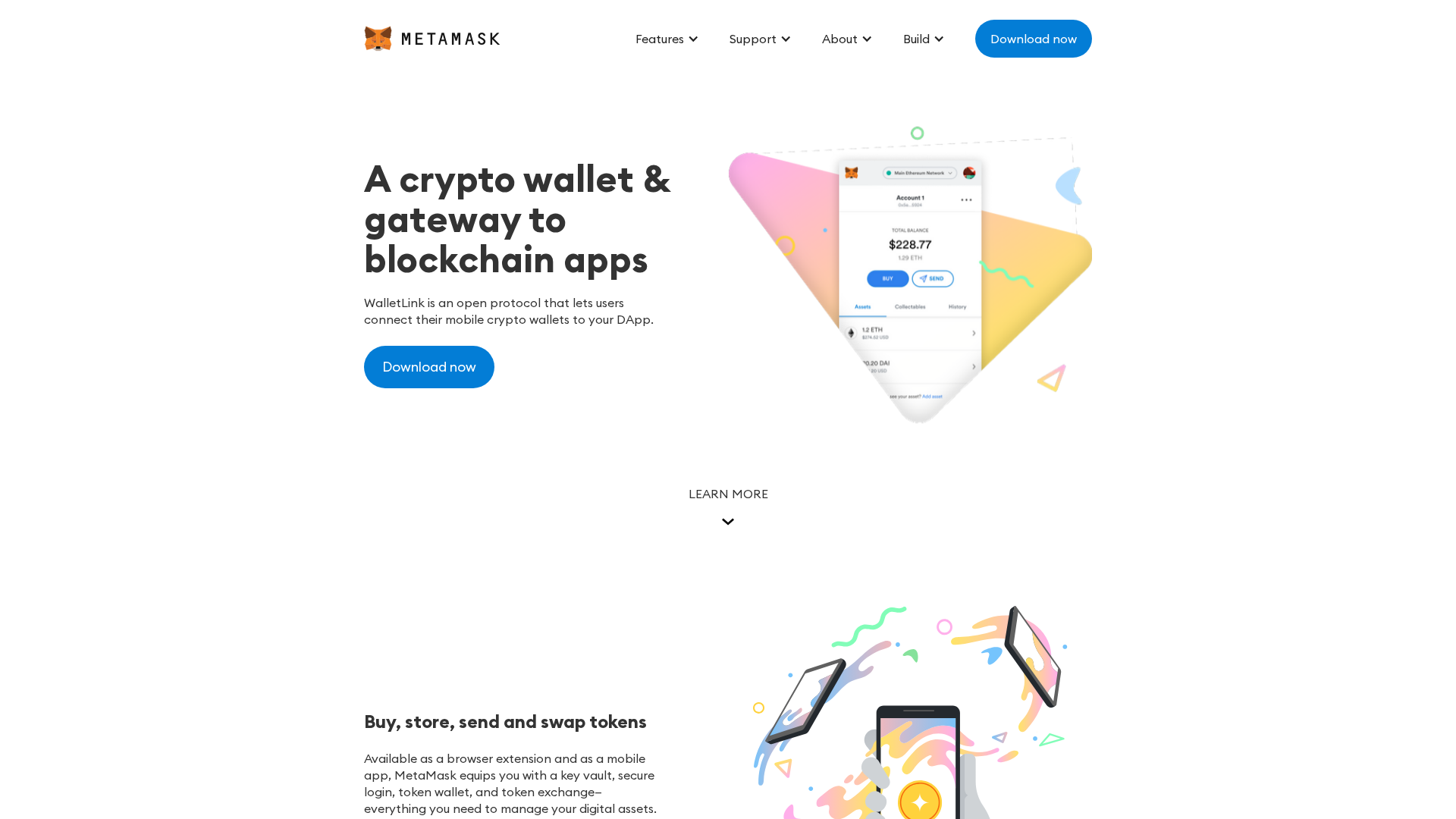
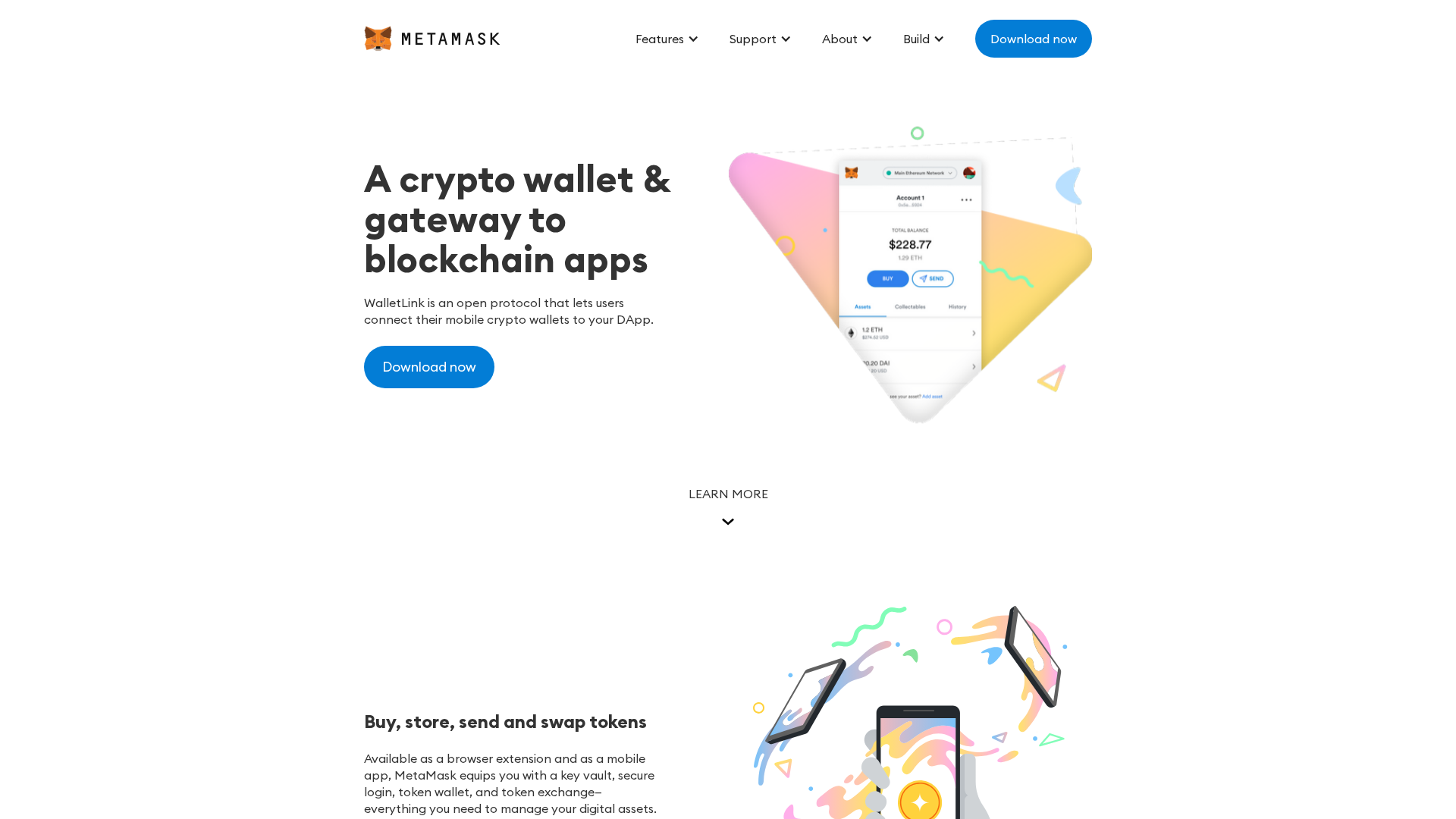
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T156520FB364802137078709D5B2717B6EB683C30DCE479856A3F8839A7FD2EA5EC05678 |
|
CONTENT
ssdeep
|
384:2lWn6mcFkK9Od5fXx2+ttHopNsX/oHHYkgBj:N6mcF19Od5fXx2++swHu |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
bc3965c3cc4d2965 |
|
VISUAL
aHash
|
f9c7c39bfffff3c3 |
|
VISUAL
dHash
|
221c363628020616 |
|
VISUAL
wHash
|
c3c38383e3e3c3c3 |
|
VISUAL
colorHash
|
07c00000080 |
|
VISUAL
cropResistant
|
221c363628020616 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: MetaMask users
• Method: Impersonation via free hosting.
• Exfil: Unknown, likely credential theft.
• Indicators: Free hosting, brand logo, obfuscation
• Risk: High
🔒 Obfuscation Detected
- fromCharCode
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
- 2 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The site likely attempts to steal the user's private key, seed phrase, or other sensitive information, using a convincing fake login page.
Secondary Method: Malware Injection
Possibly injects a malicious Javascript that redirects you to a malicious site or injects code to collect information
🌐 Infrastructure Indicators of Compromise
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for meta-mask-template.webflow.io
Found 1 other scan for this domain