
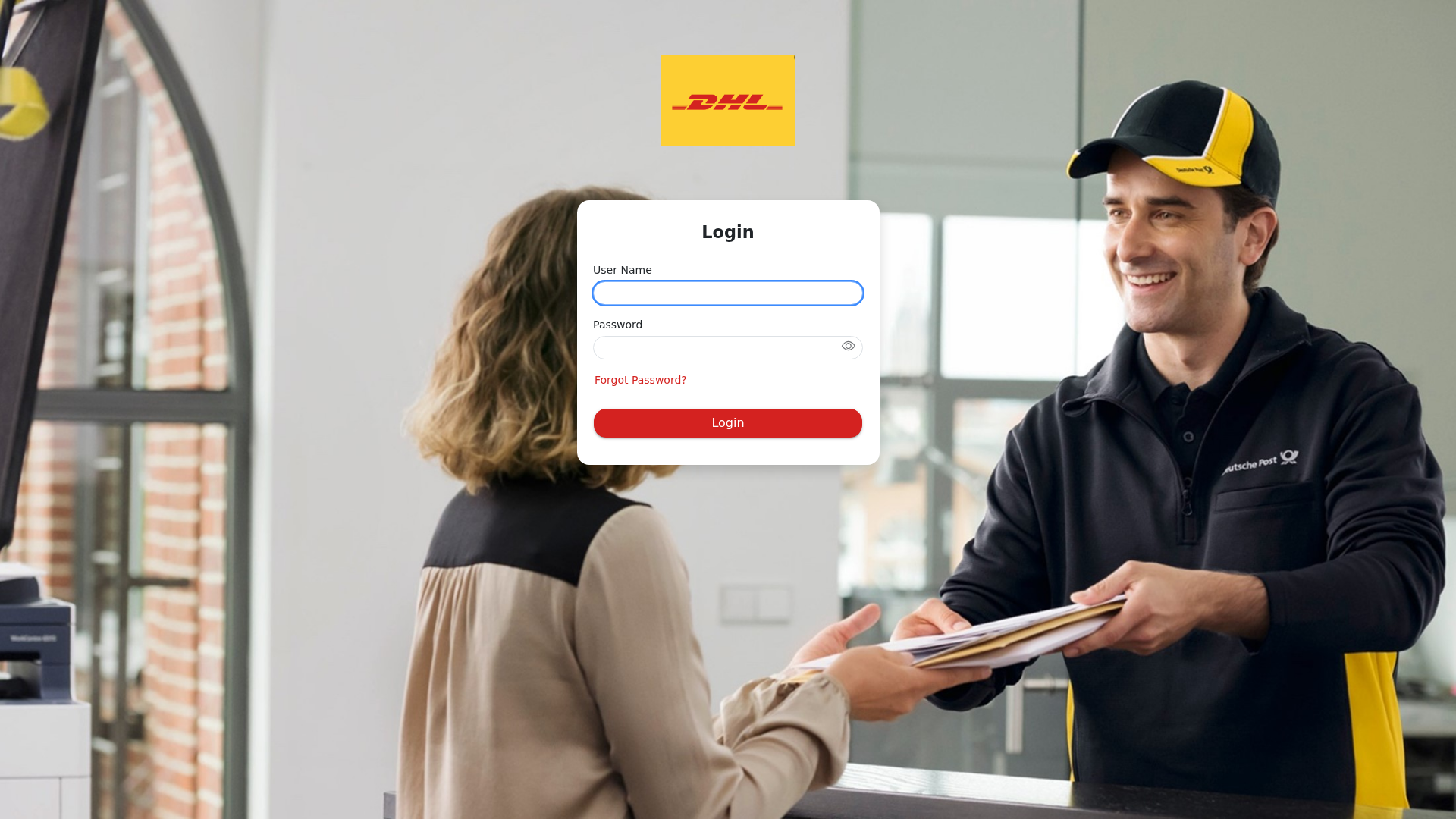
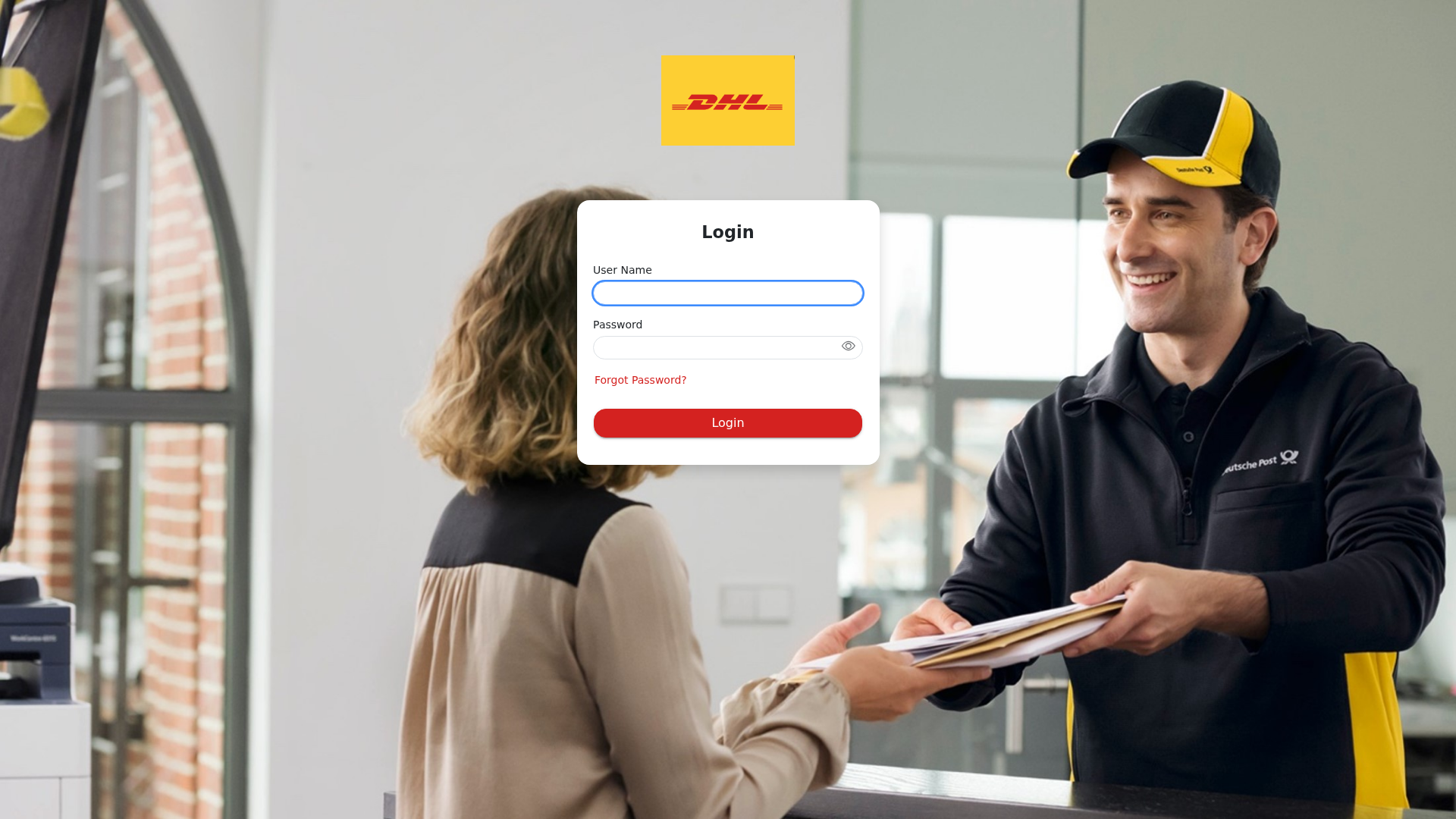
Phishing Analysis
Detailed analysis of captured phishing page
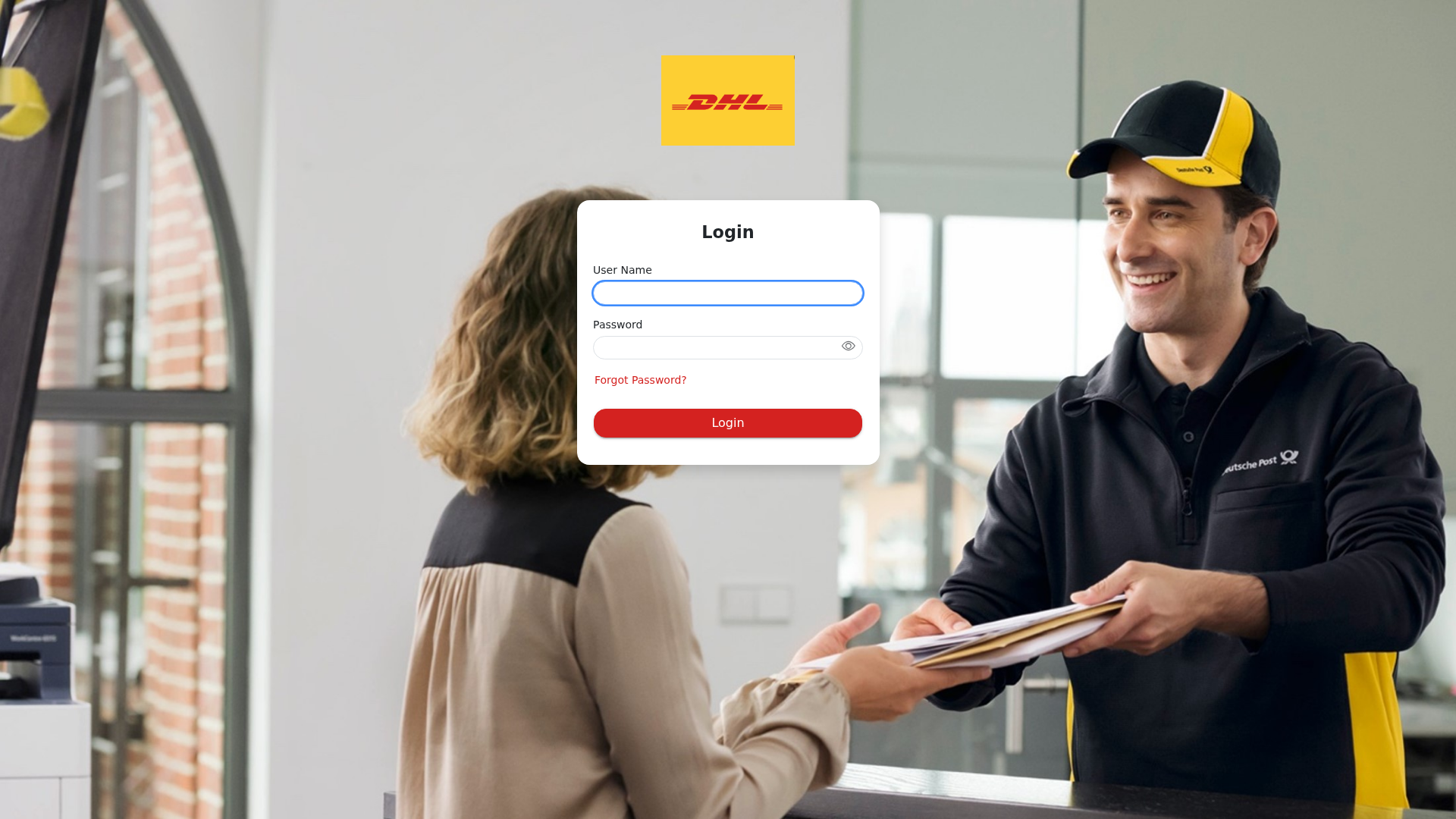
Visual Capture
Detection Info
https://dhlsiprod.eu23.smartcommunications.cloud/produce/account/login?returnurl=/produce/
Detected Brand
DHL
Country
International
Confidence
100%
HTTP Status
200
Report ID
15734748-f0d…
Analyzed
2026-01-01 12:57
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1D341A5A0E0384C67419296F4B7D4971A64C8E20BC7511D0092FC9BF893FFD52EC78968 |
|
CONTENT
ssdeep
|
24:nl8CiQ4tKonEnobcoEDcomCh7BK6jHWAPnpV2c1HcVK3r+hHc7VD8q04Dr+k1OWR:nb4UFnKc3cJC1PnSKbTJgyii2H5O |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
d884a64d7e94b569 |
|
VISUAL
aHash
|
7f7d7d5c484868e0 |
|
VISUAL
dHash
|
c1d1919199909199 |
|
VISUAL
wHash
|
7f7d7d5c484848e0 |
|
VISUAL
colorHash
|
0ee00010000 |
|
VISUAL
cropResistant
|
c1d1919199909199,36396cc8c8989a6c,d3e1c1c5013379dd,27222381899923e3,1a1a1b1f0f8f8703,c3c38f4fe7b57575 |
Code Analysis
Risk Score
73/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🔬 Threat Analysis Report
• Threat: Credential harvesting phishing attack
• Target: DHL customers
• Method: Fake login form to steal usernames and passwords
• Exfil: Data is likely sent to a malicious server or bot controlled by the attacker.
• Indicators: Domain mismatch, DHL logo, Login form, Obfuscated JavaScript
• Risk: HIGH - Immediate risk of credential theft and potential account compromise
🔒 Obfuscation Detected
- fromCharCode
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
DHL
https://dhlsiprod.eu23.smartcommunications.cloud/
Apr 08, 2026
DHL
https://dhlsiprod.eu23.smartcommunications.cloud/produce/wiz...
Feb 04, 2026
DHL
https://dhlsiprod.eu23.smartcommunications.cloud/produce/Acc...
Feb 04, 2026
DHL
https://dhlsiprod.eu23.smartcommunications.cloud/produce/wiz...
Jan 15, 2026
DHL
https://dhlsiprod.eu23.smartcommunications.cloud/produce/hom...
Jan 04, 2026
Scan History for dhlsiprod.eu23.smartcommunications.cloud
Found 9 other scans for this domain
-
https://dhlsiprod.eu23.smartcommunications.cloud/
https://dhlsiprod.eu23.smartcommunications.cloud/p...
https://dhlsiprod.eu23.smartcommunications.cloud/p...
https://dhlsiprod.eu23.smartcommunications.cloud/p...
https://dhlsiprod.eu23.smartcommunications.cloud/p...
https://dhlsiprod.eu23.smartcommunications.cloud/p...
https://dhlsiprod.eu23.smartcommunications.cloud/p...
https://dhlsiprod.eu23.smartcommunications.cloud/p...
https://dhlsiprod.eu23.smartcommunications.cloud/p...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.