
Phishing Analysis
Detailed analysis of captured phishing page
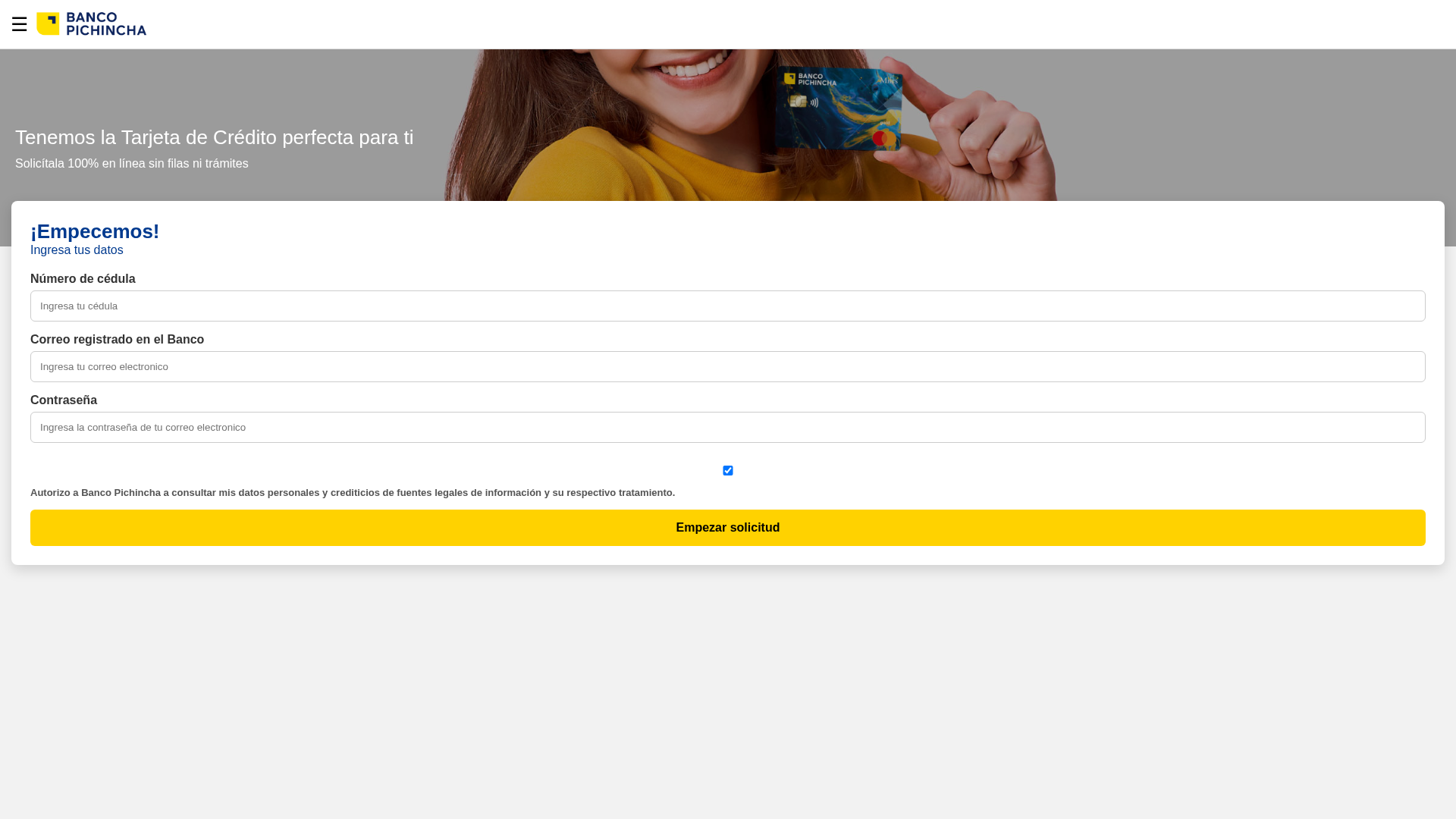
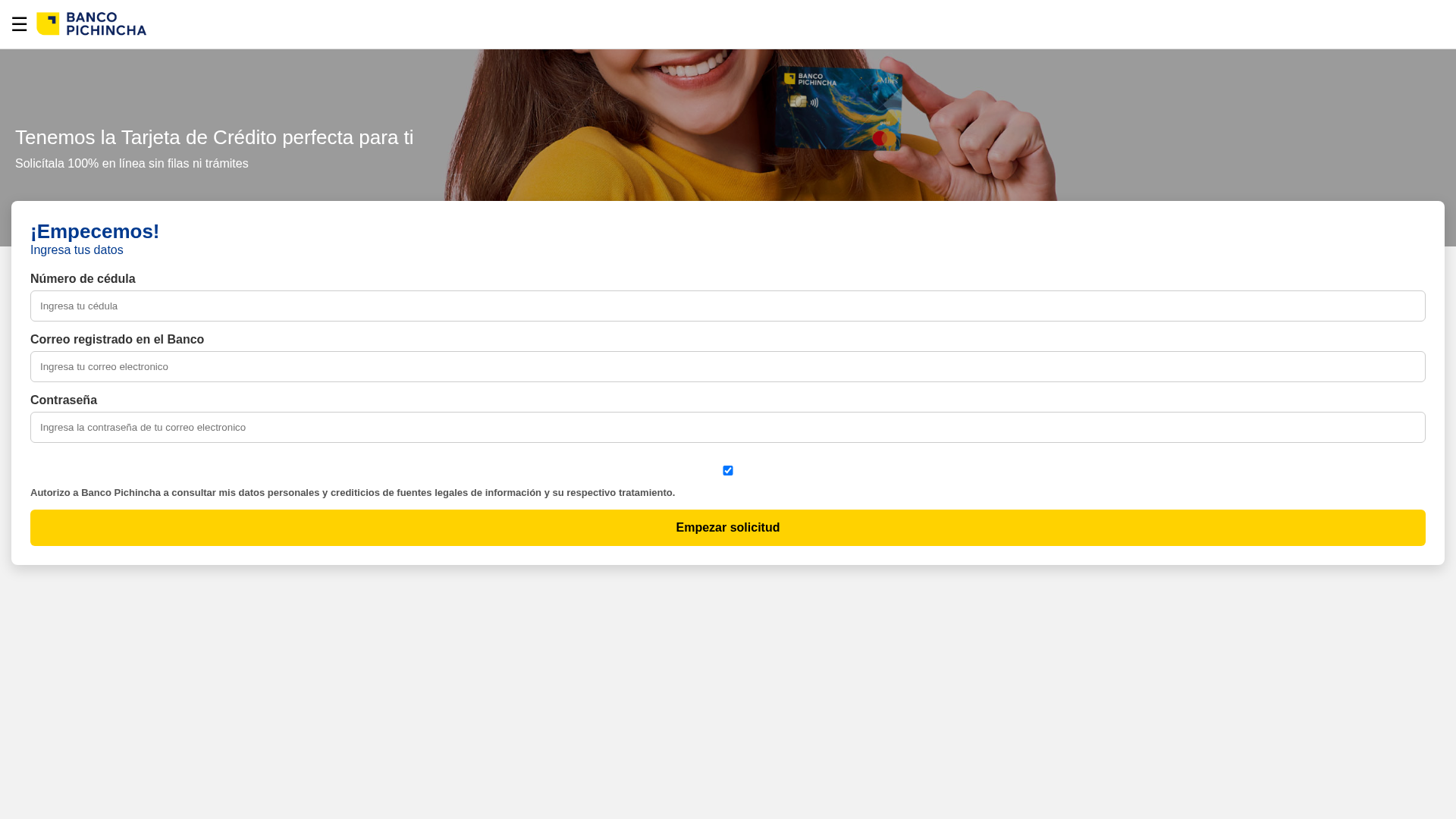
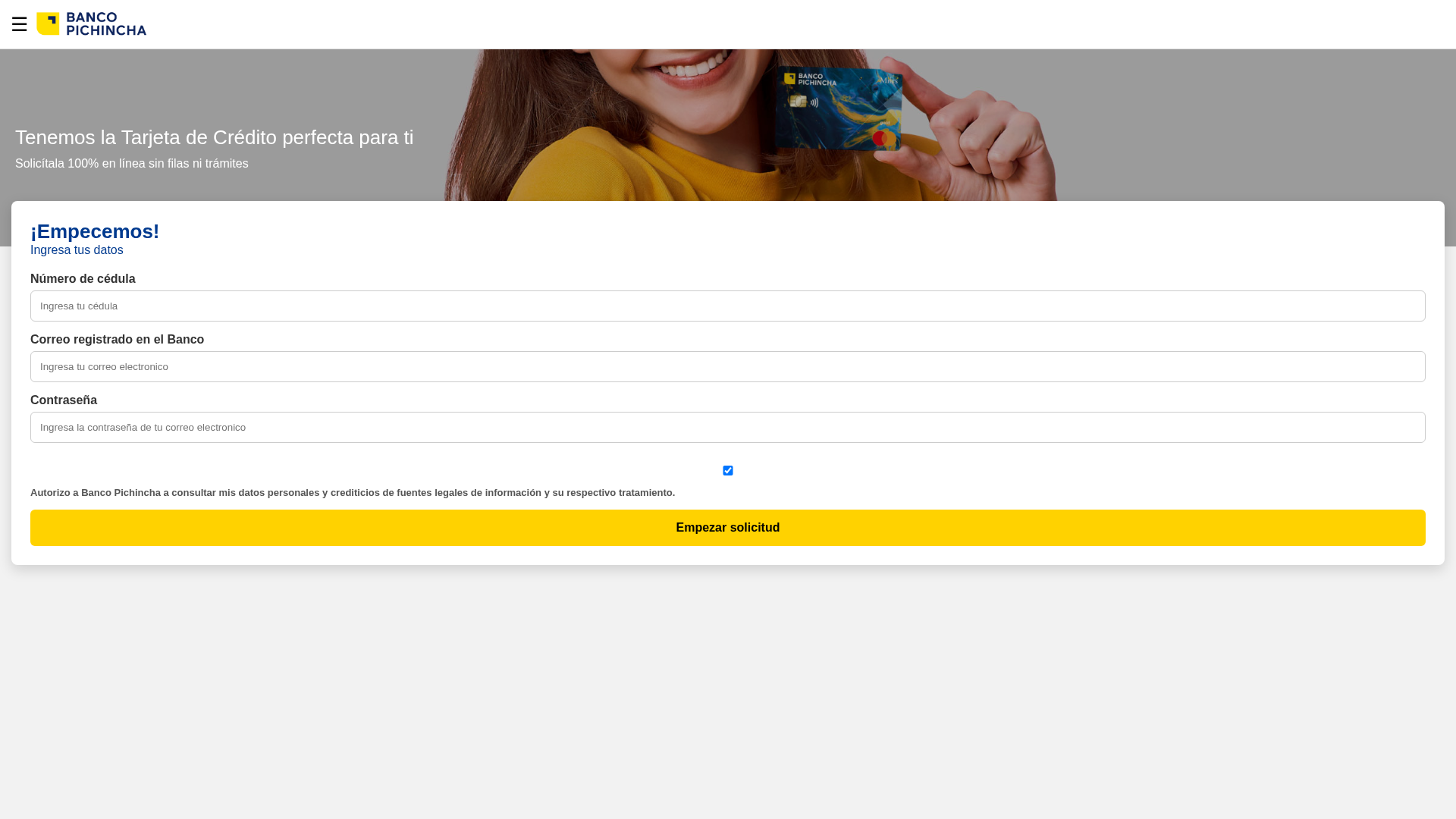
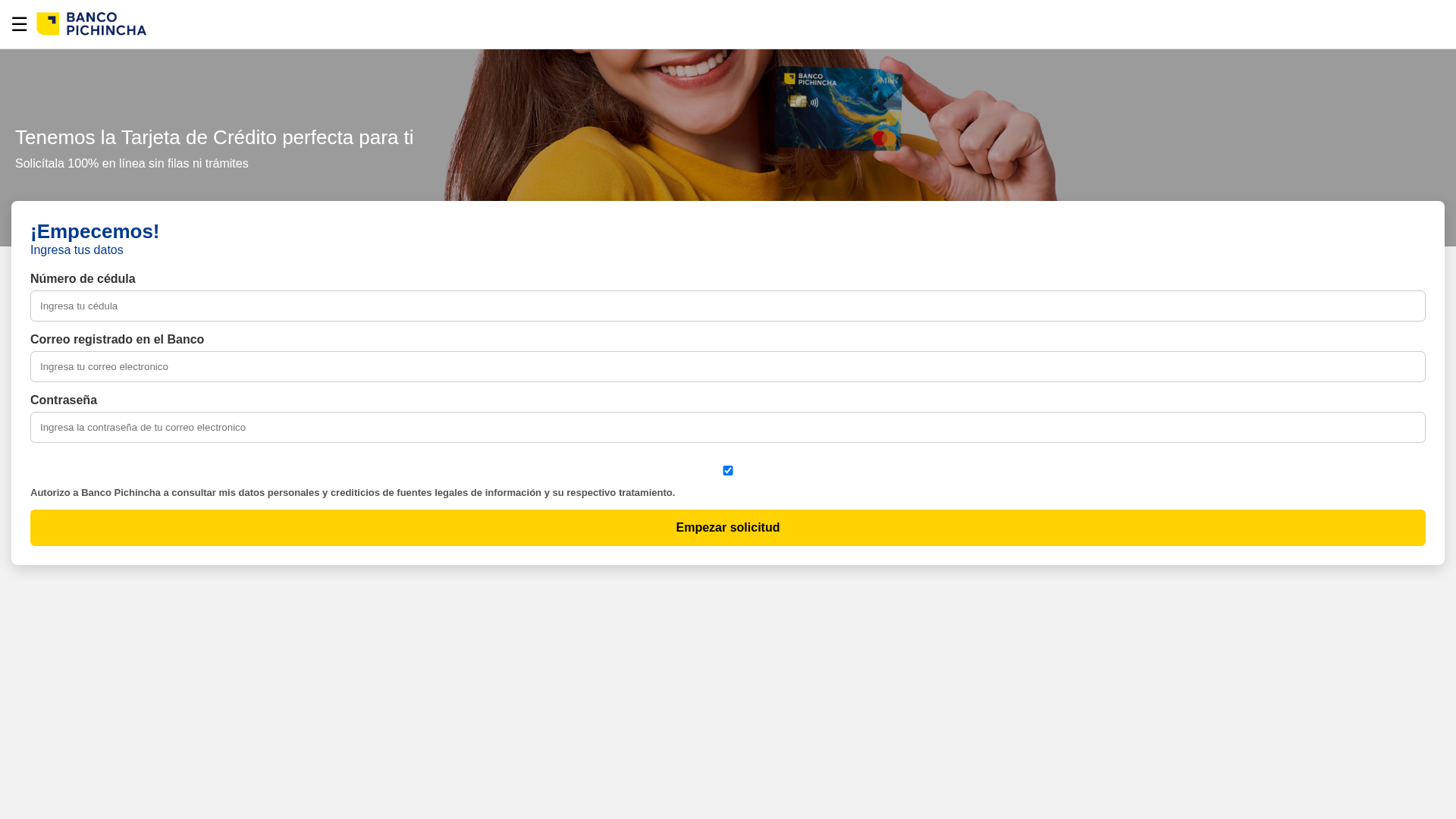
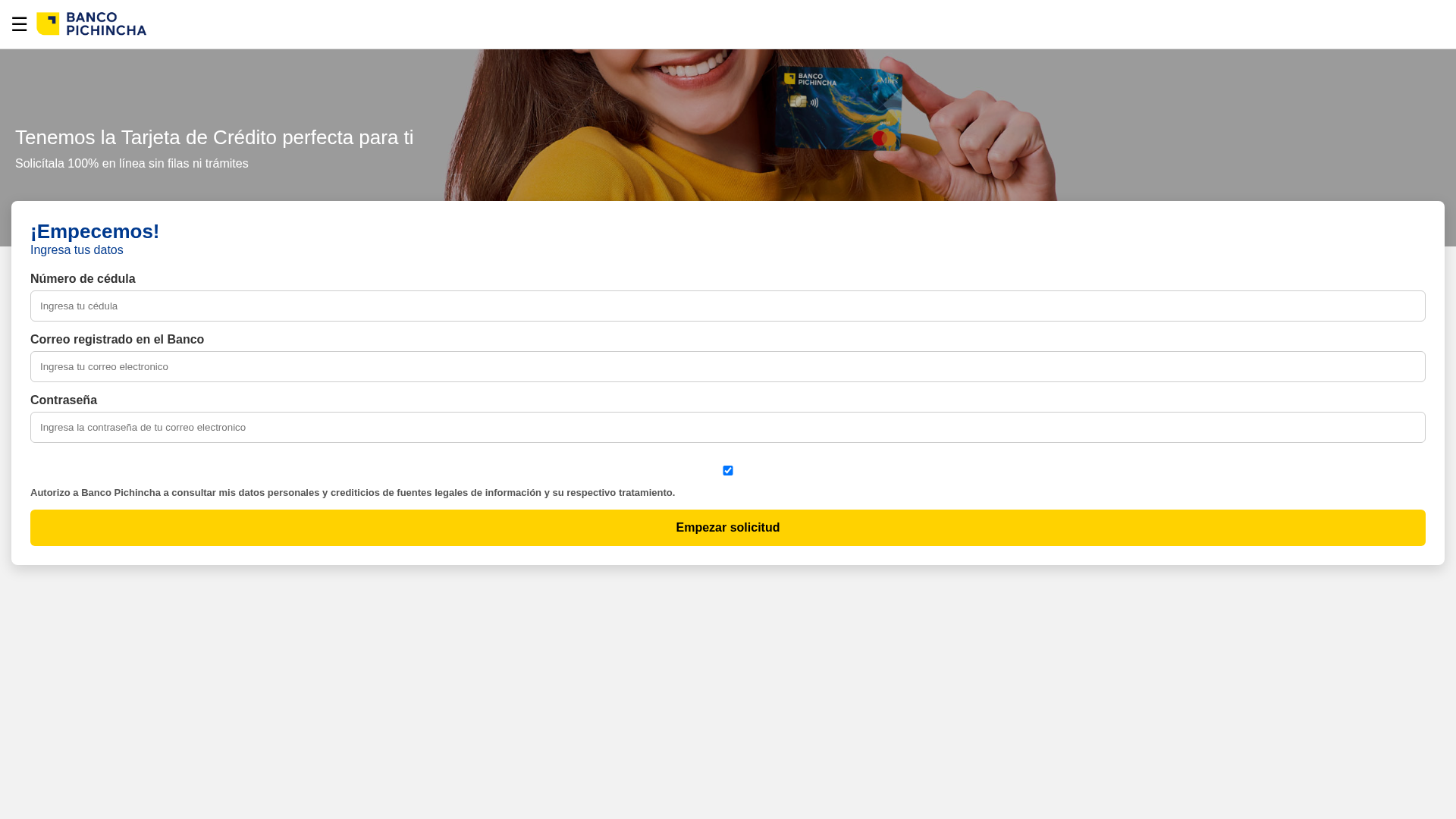
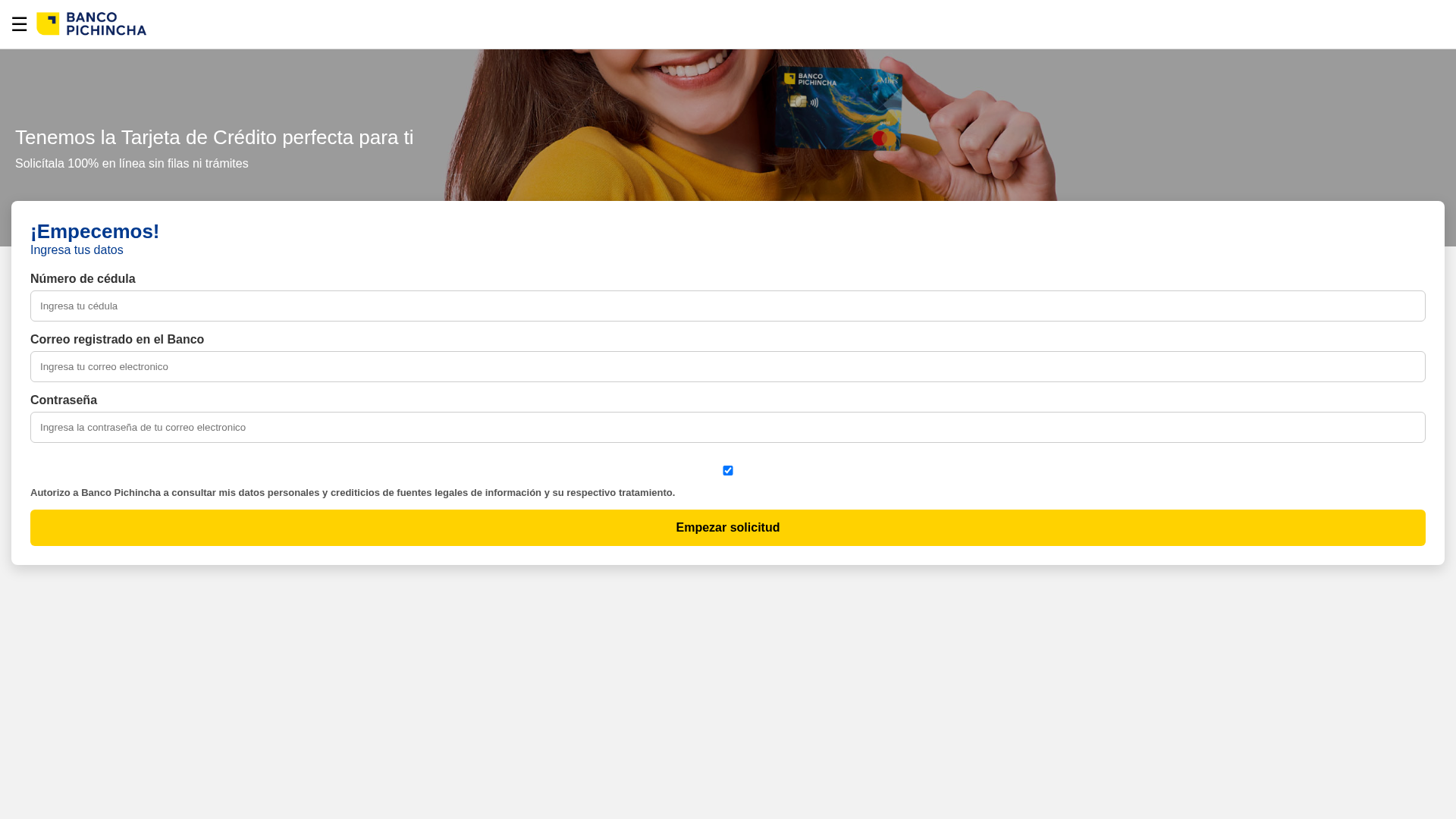
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1A5218362508089B7D453A0AC87A6EEAA5083D644CA435A11D7EC625E3AD6C04CFD2EE8 |
|
CONTENT
ssdeep
|
24:hWC0lfYGF+ITbEUfYAhY5sBhnXREo9Hs3wJlrIoS:YJpzm52Rio9Hsosz |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
a03076739b8b8b8f |
|
VISUAL
aHash
|
0000ffffffffffff |
|
VISUAL
dHash
|
9d8ea6c0d80d8000 |
|
VISUAL
wHash
|
00007f7fff00cccc |
|
VISUAL
colorHash
|
07200038000 |
|
VISUAL
cropResistant
|
9d8ea6c0d80d8000,6667672766c6c687 |
Code Analysis
📡 API Calls Detected
- https://api.ipify.org?format=json
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- 1 Discord webhook(s)
- Kit types: Credential Harvester
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: Client-Side Form Interception
JavaScript intercepts form submissions before they reach the fake backend. This allows real-time credential harvesting and validation without server round-trips.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for franciscolara201822-maker.github.io
Found 3 other scans for this domain
