
Phishing Analysis
Detailed analysis of captured phishing page
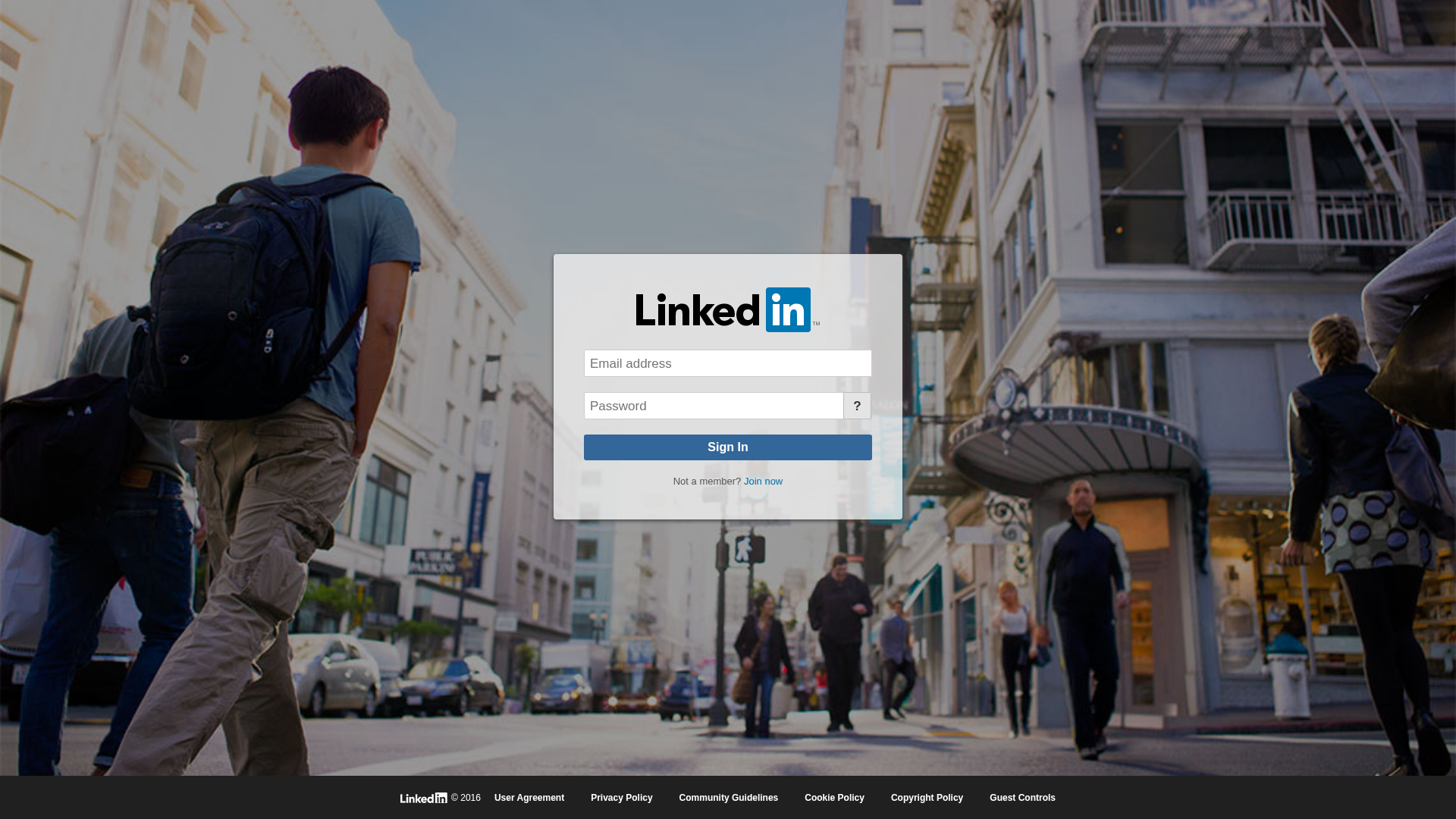
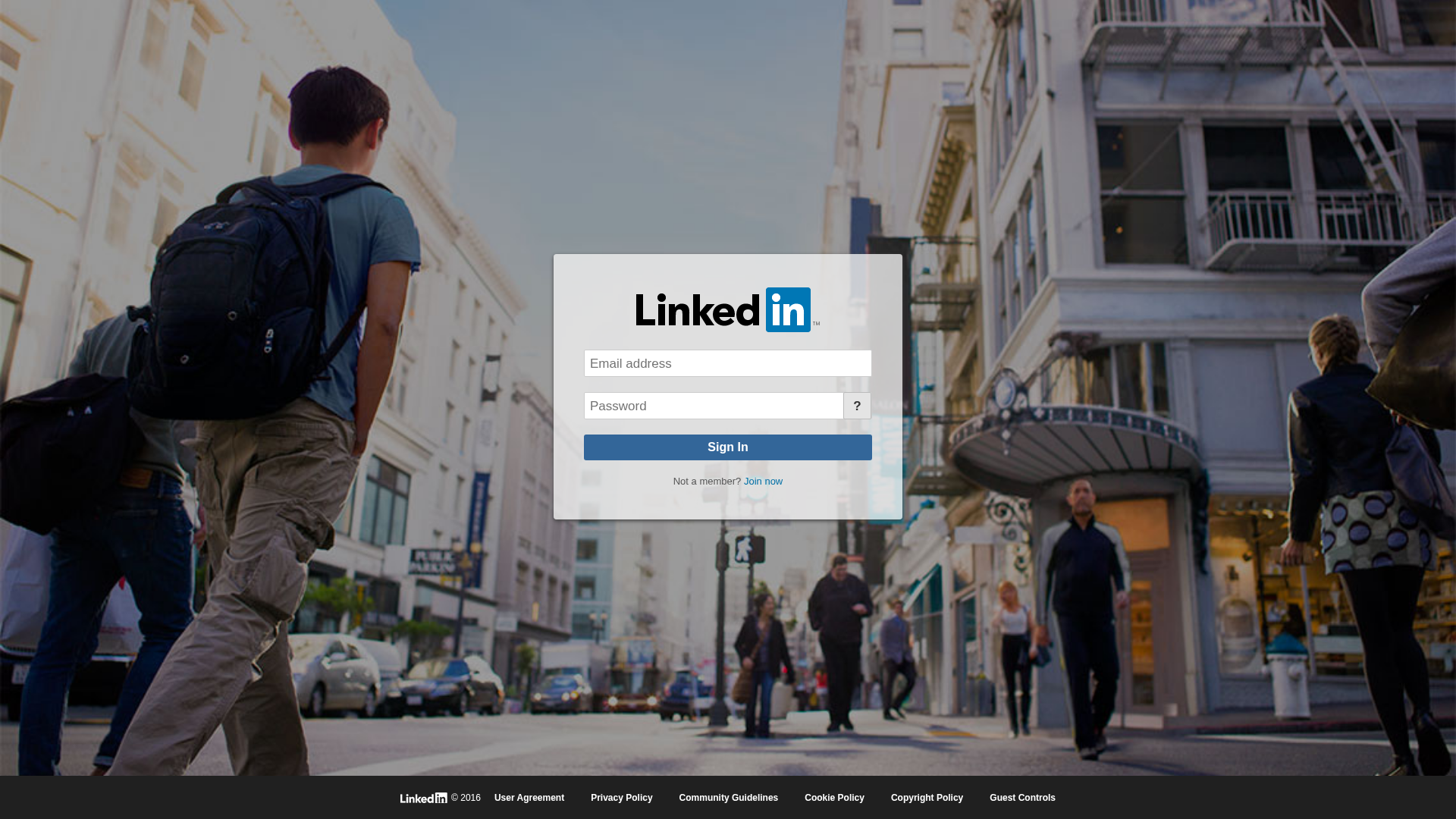
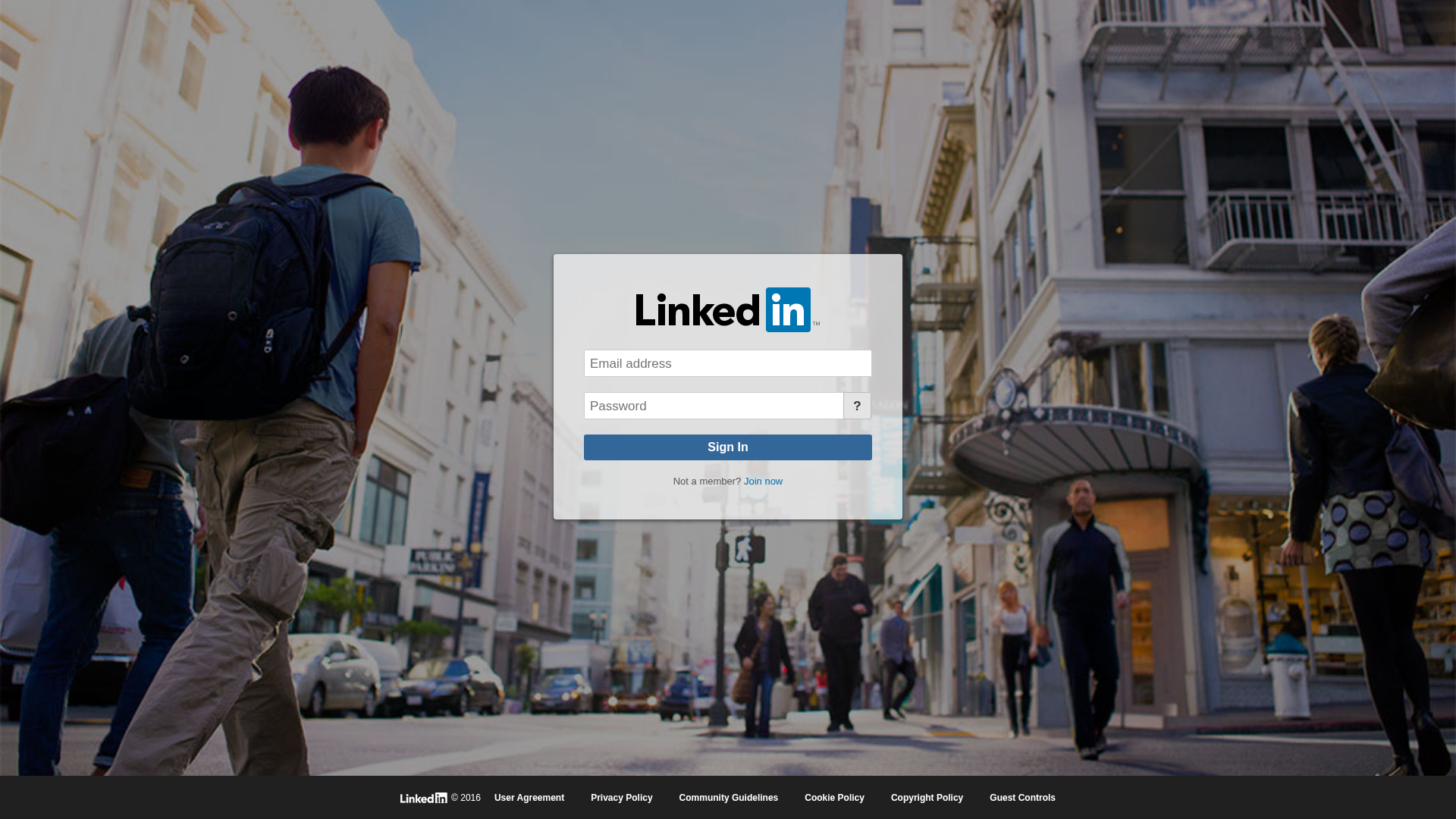
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T16141AB690047AC264153D7F5A2E1332EA1D3822BCA236EC823F79F9D9FF5E85DD49084 |
|
CONTENT
ssdeep
|
48:TRfJcfbNcfAFvCMxeN2TO8PnMu+8G9r9MBMx7dMshMXM7Mh:T/8XRC/MO8PMJ8MrOCx7u58Qh |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cffe72c081a53f40 |
|
VISUAL
aHash
|
fcfcbc3c38381020 |
|
VISUAL
dHash
|
28216070f2f0e2e8 |
|
VISUAL
wHash
|
fcfcbc3c383c1038 |
|
VISUAL
colorHash
|
0f602008000 |
|
VISUAL
cropResistant
|
1d96343a3efefc7d,d8ecfcf0e8c89222,28216070f2f0e2e8 |
Code Analysis
🔒 Obfuscation Detected
- atob
- fromCharCode
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Personal Info
- 5 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 5 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for notifyhubss.net
Found 10 other scans for this domain
-
https://notifyhubss.net/y6fdcd23ac12514b3bl8adf9c9...
http://notifyhubss.net/41a43b03au34a94c25la184a3dc...
https://notifyhubss.net/474fdb4d3uf92e4f67l9de64d6...
http://notifyhubss.net/4d98cfdadudd0c4222l8ec2903a...
https://notifyhubss.net/d7f328b62704a34024p9afecca...
https://notifyhubss.net/dbb8e431f785e24a80p8e67224...
https://notifyhubss.net/edc08ed07w15ff4b5ce9227fb2...
http://notifyhubss.net/42443f283u743741c0l8f0e556e...
https://notifyhubss.net/y8b5c8750c68c64cdbl94e2b27...
https://notifyhubss.net/dd74bfd507ed674866pb8b8126...
