
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
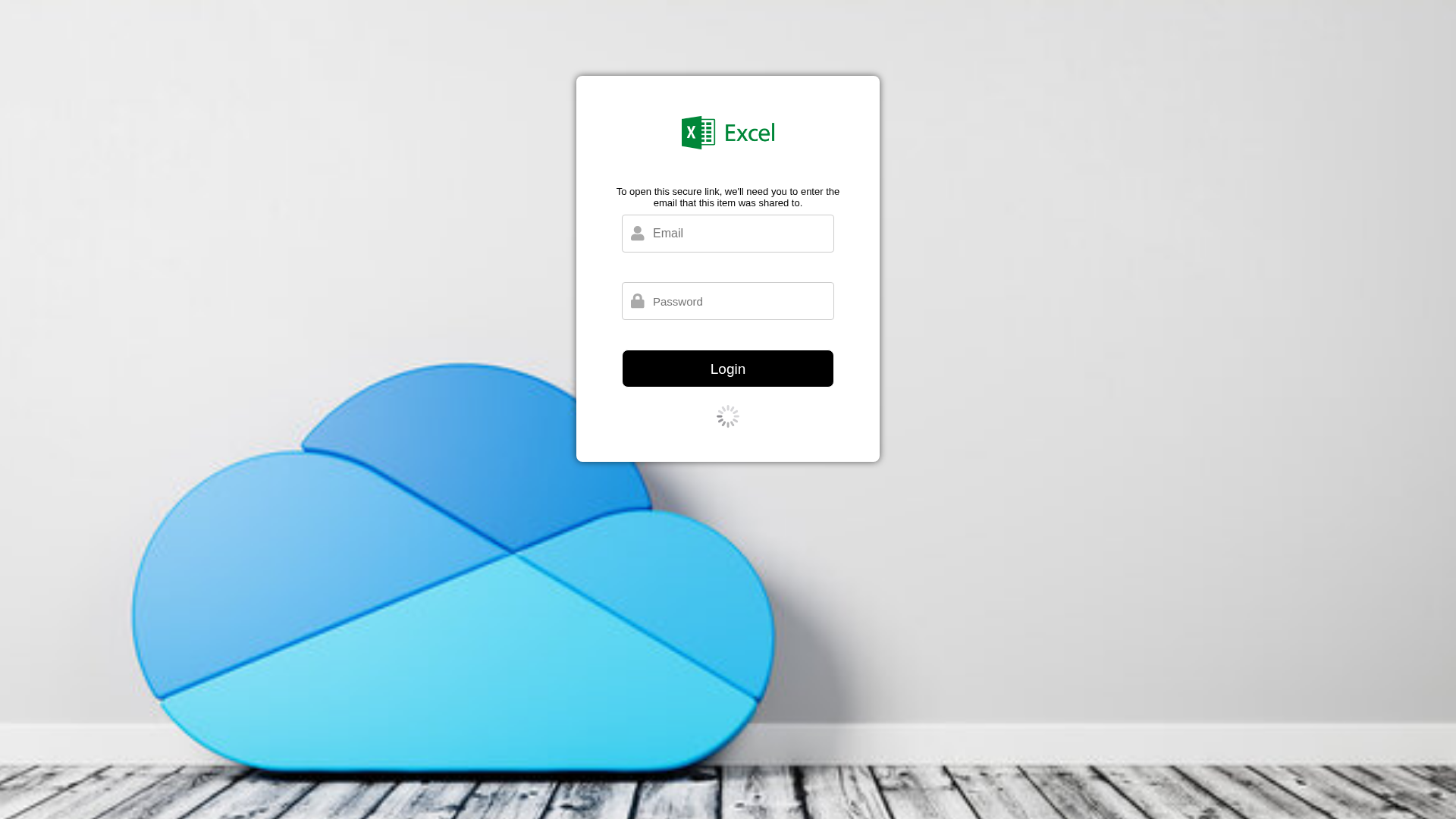
Detection Info
http://anydo-user-uploads.s3.amazonaws.com/jtdikCCOxGpKjdtvgNlJnA_8adb9e705a014c3089eb01c13a60618b_Onedrive-Excel.html
Detected Brand
Microsoft Excel
Country
International
Confidence
100%
HTTP Status
200
Report ID
1cd9e32b-13c…
Analyzed
2025-12-31 05:27
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T16C31681251055D976083F2A4F1E5EF6F30D982A283160E3857B0939B3DCEDFE8A656C9 |
|
CONTENT
ssdeep
|
24:n/CiDDfT1FdVyWGvr1Mm8KH5QzrZLBvQLDzrZL8NNEenNabRx0R7Ew596RUK:np/yzv+N5BvCD584IWRx02496Rv |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
bbc8473938e65998 |
|
VISUAL
aHash
|
ffffffc78e868680 |
|
VISUAL
dHash
|
003070ac38184c1c |
|
VISUAL
wHash
|
fefefec68e840400 |
|
VISUAL
colorHash
|
06007000080 |
|
VISUAL
cropResistant
|
003070ac38184c1c,4501253131710155 |
Code Analysis
Risk Score
95/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
Telegram Exfiltration
🔬 Threat Analysis Report
• Threat: Credential harvesting phishing kit
• Target: Users of Microsoft Excel
• Method: Fake login form requesting email and password
• Exfil: Unknown data exfiltration point
• Indicators: Domain mismatch (s3.amazonaws.com), impersonation of Microsoft Excel, presence of login form
• Risk: HIGH - Immediate risk of credential theft
📡 API Calls Detected
- https://api.ipify.org?format=json
🔑 Telegram Bot Tokens (1)
- 7091810784:AAFk...6Ehndfyo
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for anydo-user-uploads.s3.amazonaws.com
Found 5 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.