
Phishing Analysis
Detailed analysis of captured phishing page
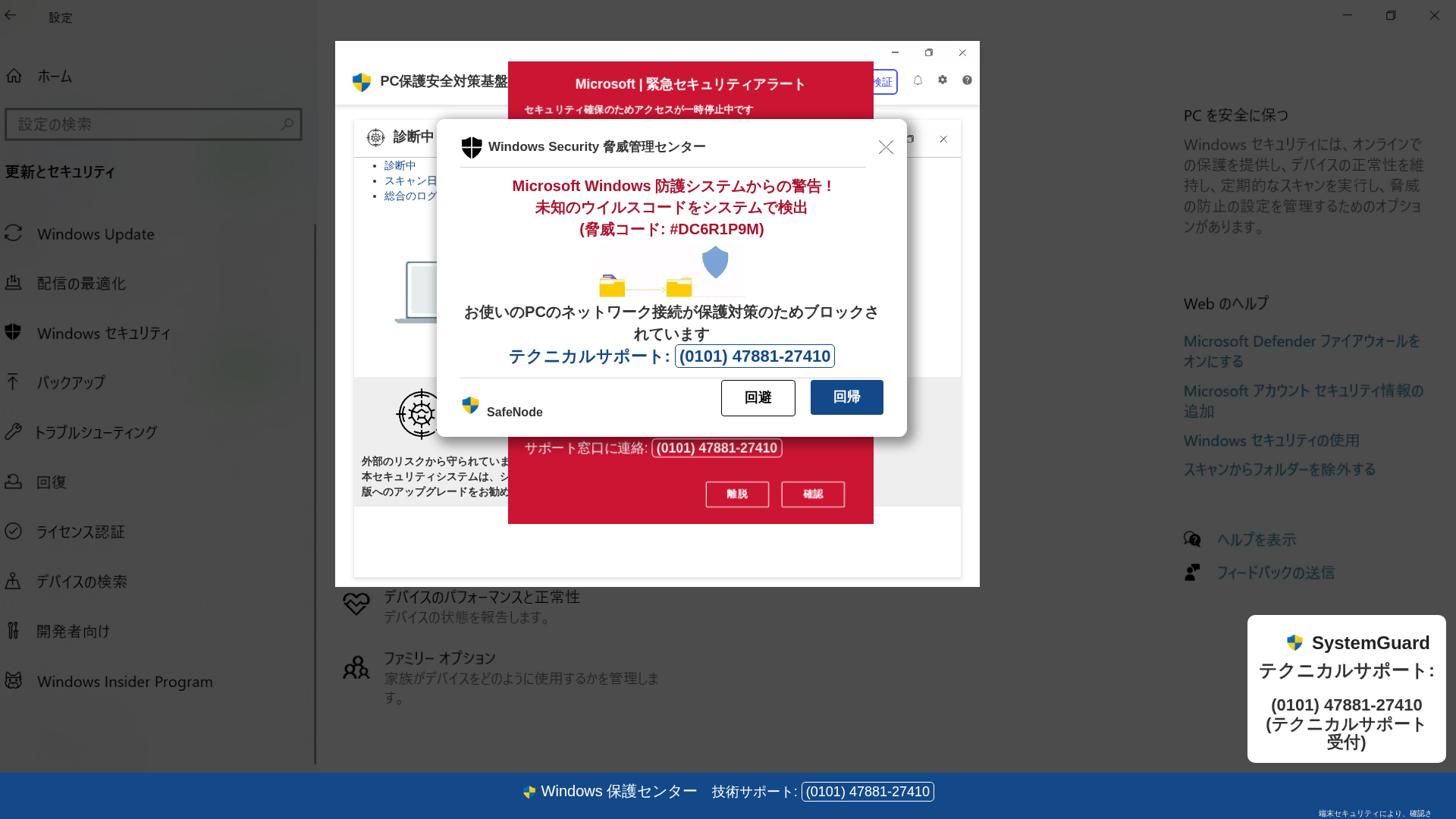
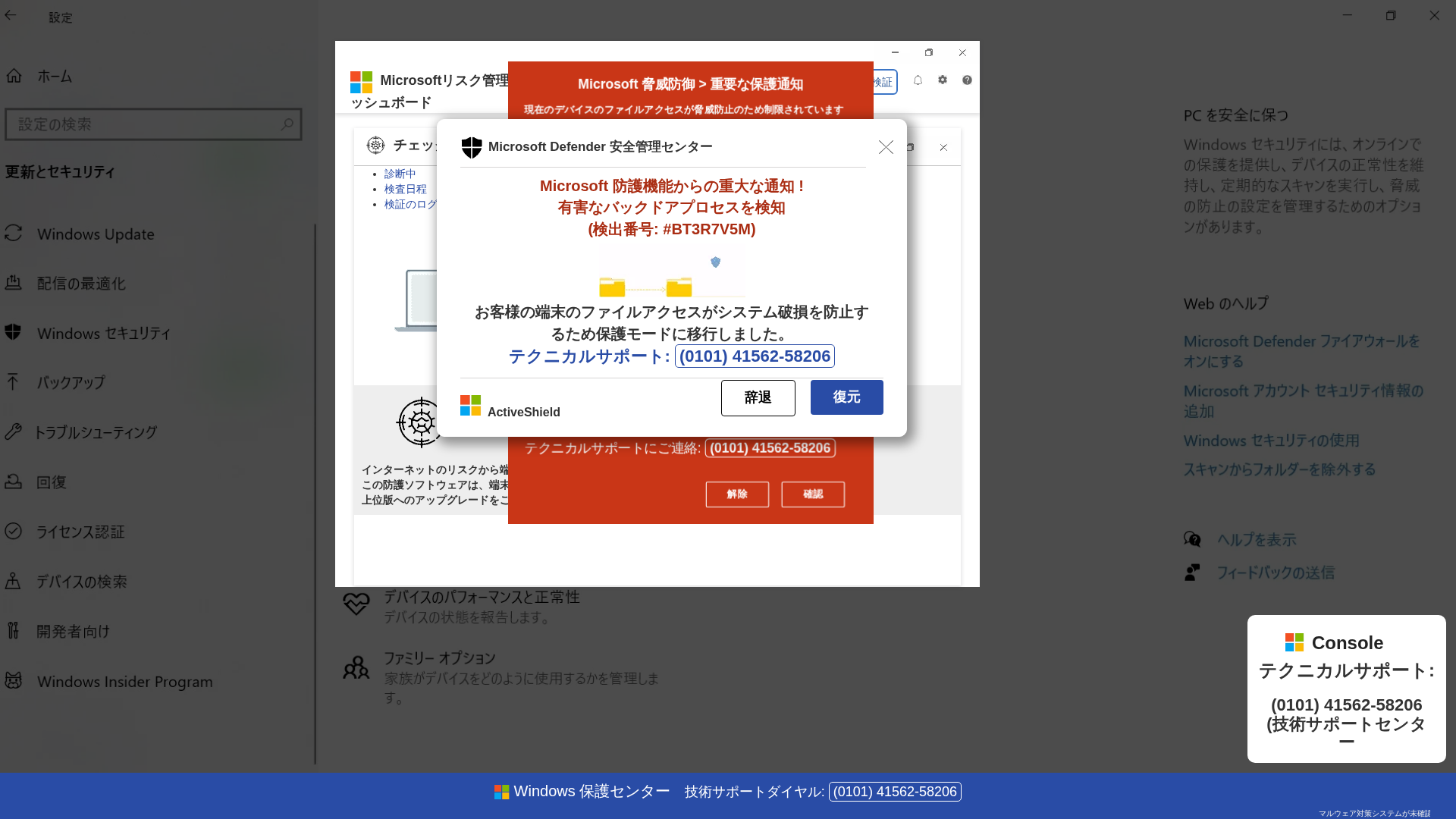
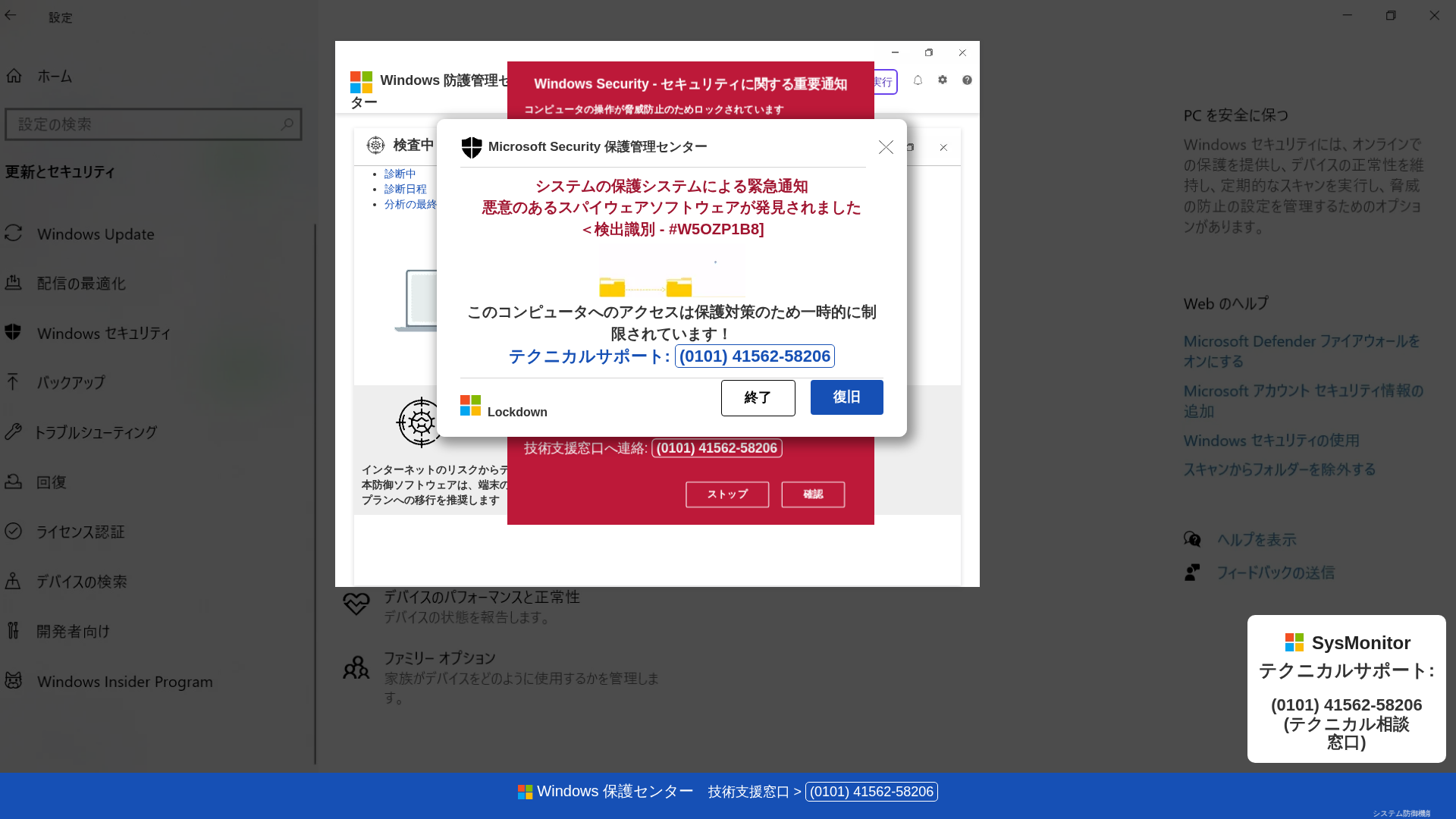
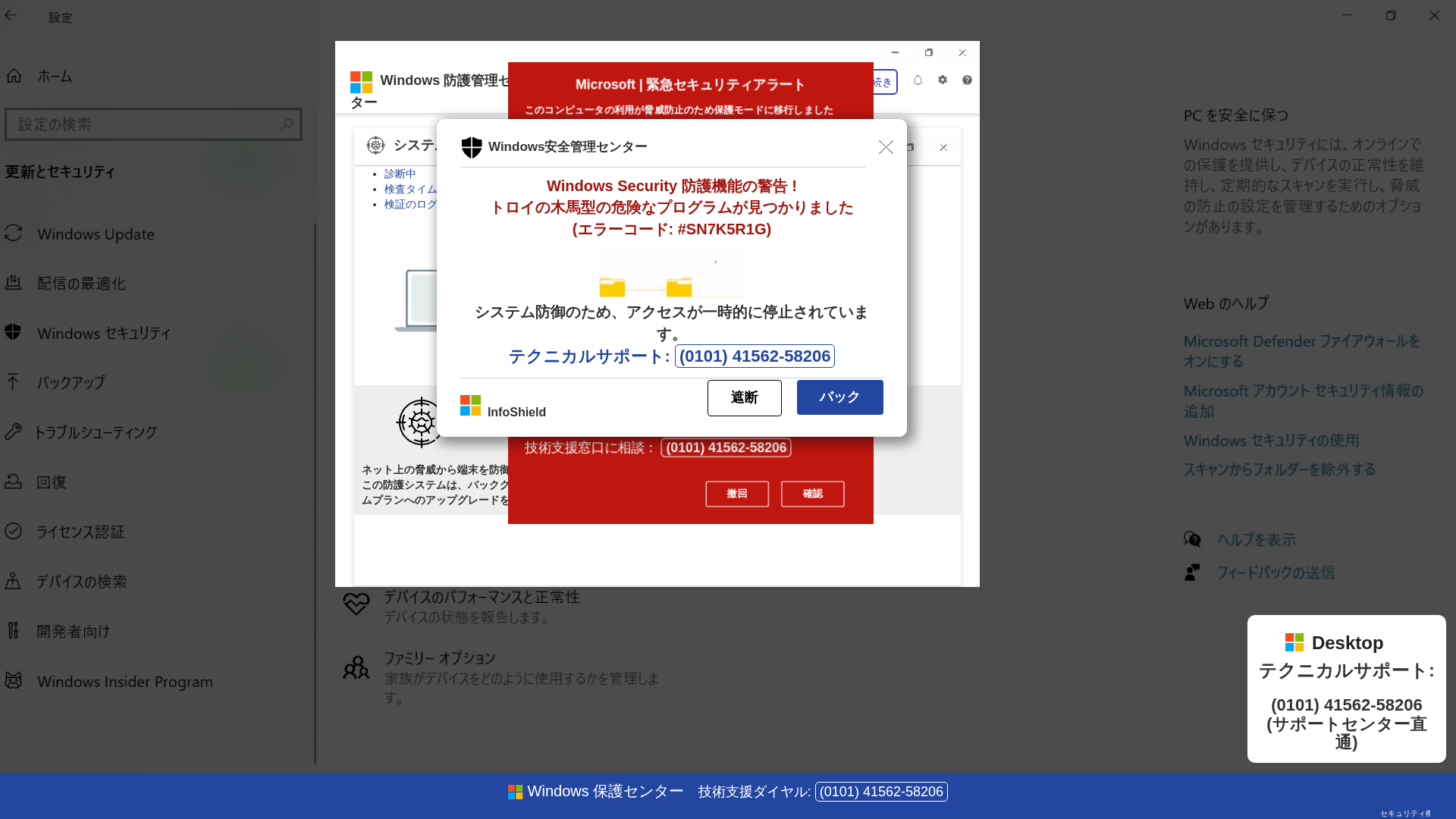
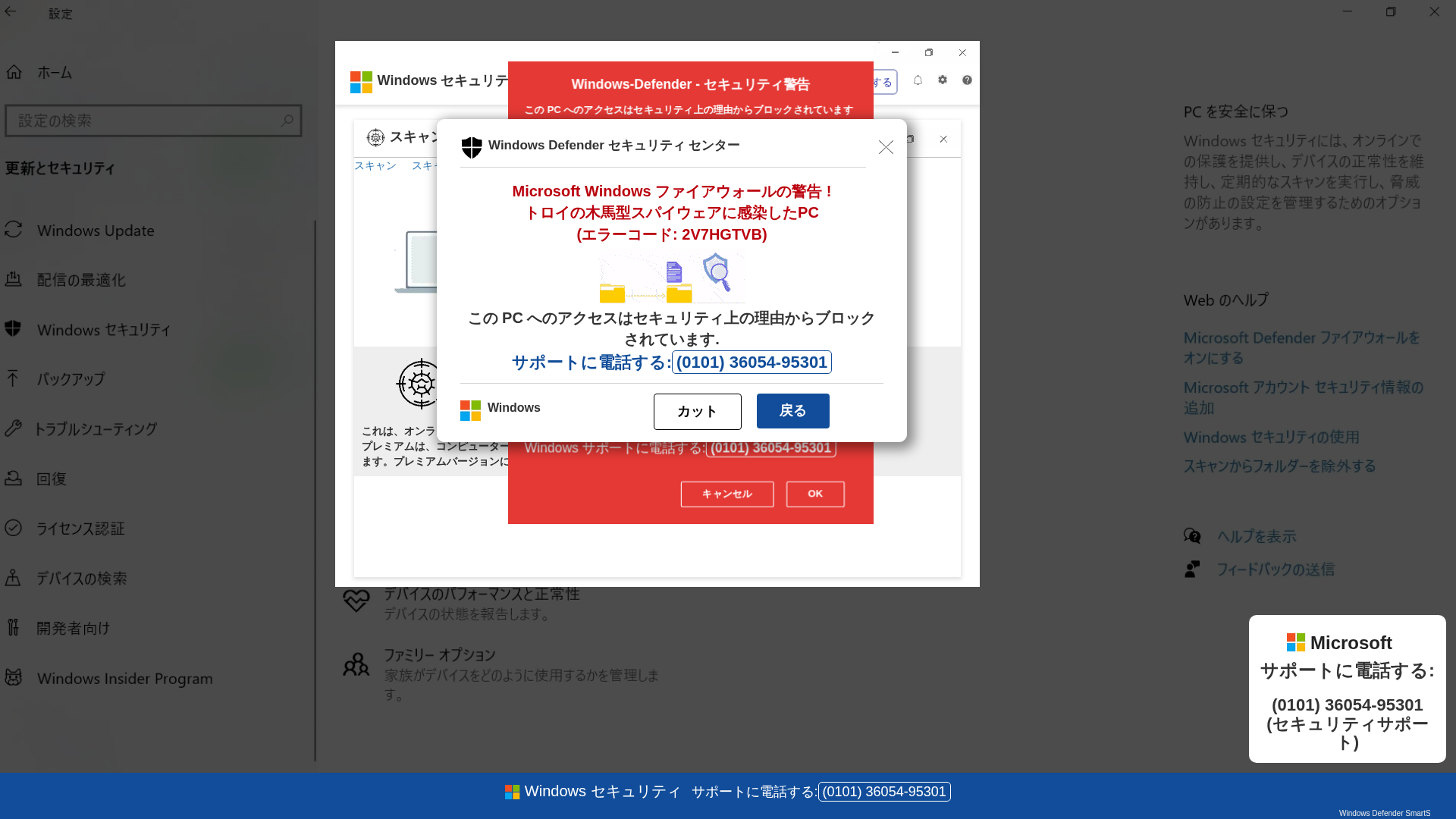
Visual Capture

Detection Info
https://mucigominu.z21.web.core.windows.net/
Detected Brand
Microsoft
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
1d803f44-fb1…
Analyzed
2026-04-06 23:39
Final URL (after redirects)
https://mucigominu.z21.web.core.windows.net/lanqxi0s4tzh.html
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T10663AE35E2406D324113D2C8EEE66F6A2362DB85DA520E59129CC37B7EEFD24FC2119D |
|
CONTENT
ssdeep
|
1536:UfdpBaHGPLbyx/FqaS2mhgIgWdrjcb/iZKIS5qO/kc3U0llW48:UVfaHGXyFFnmh7bdXqEJS5+c3Uklv8 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cbd33c33762c5522 |
|
VISUAL
aHash
|
283c3c3c3c3c0101 |
|
VISUAL
dHash
|
c9c9e9e1c9c9b3eb |
|
VISUAL
wHash
|
3c7c7c7c7c7c0301 |
|
VISUAL
colorHash
|
07000000183 |
|
VISUAL
cropResistant
|
9393c6ccc3139b92,b2ac8ed6aa2a969e,c9c9e9e1c9c9b3eb,48167575944ee0c0,b9b137181a1a180a |
Code Analysis
Risk Score
92/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- document.write
- unicode_escape
- base64_strings
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer
Credential Harvesting
Credential harvesting detected with 2 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 30 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Two-Factor Authentication Stealer
Target
Microsoft users
Attack Method
credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer
- 30 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Microsoft
Official Website
https://www.microsoft.com
Fake Service
Credential harvesting service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 30 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
mucigominu.z21.web.core.windows.net
Registered
1995-08-10 04:00:00+00:00
Registrar
MarkMonitor, Inc.
Status
Active (older domain)
Hosting Information
Provider
MarkMonitor, Inc.
ASN
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Microsoft
https://cumegagud.z20.web.core.windows.net/
Apr 06, 2026
Microsoft
https://rayutucon.z5.web.core.windows.net/
Mar 14, 2026
Microsoft Windows
https://sapafugesu.z38.web.core.windows.net/
Mar 14, 2026
Microsoft
https://lulelucov.z36.web.core.windows.net/
Mar 09, 2026
Microsoft
https://reuaziwh.z33.web.core.windows.net/
Jan 04, 2026

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.