
Phishing Analysis
Detailed analysis of captured phishing page
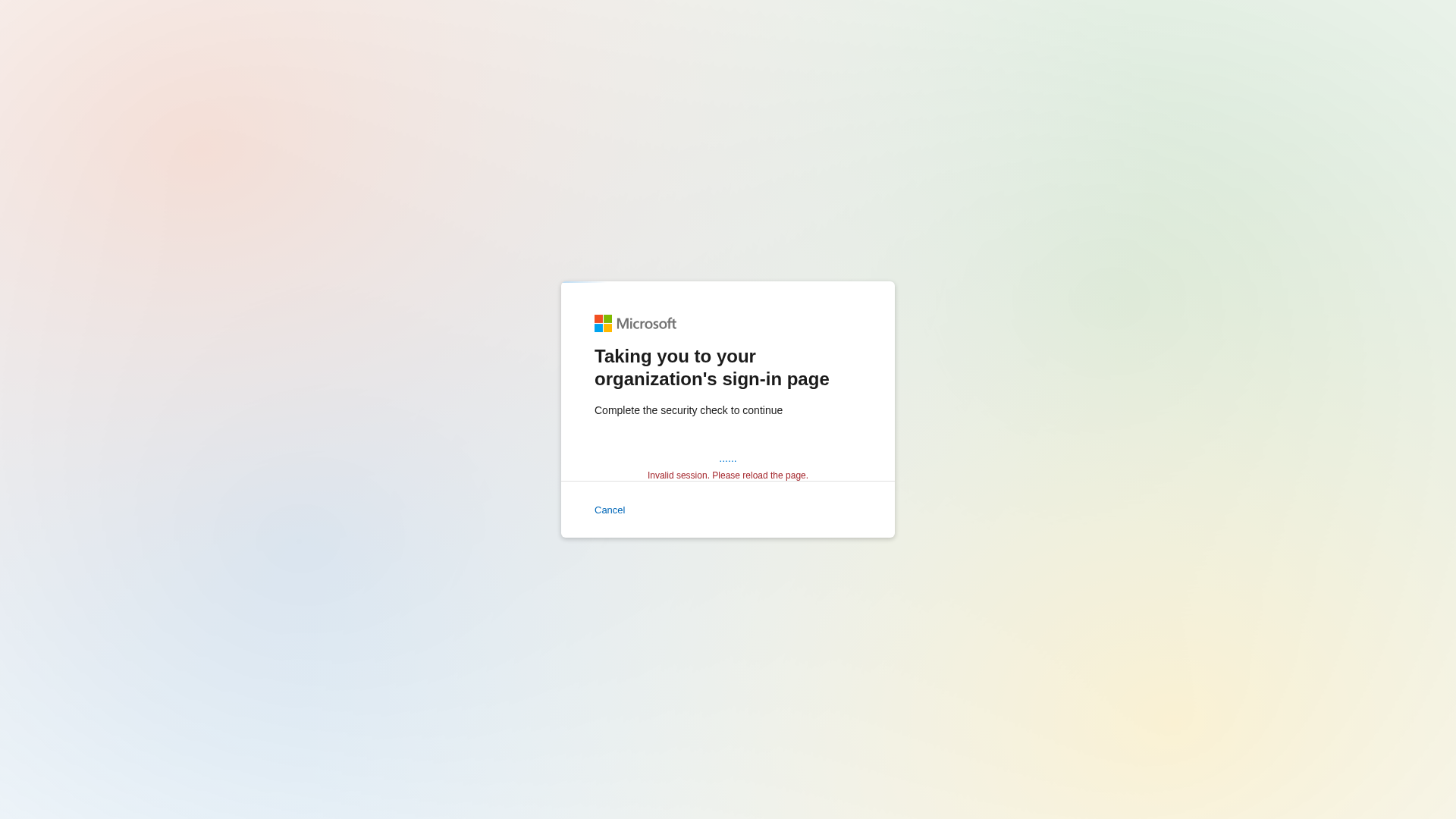
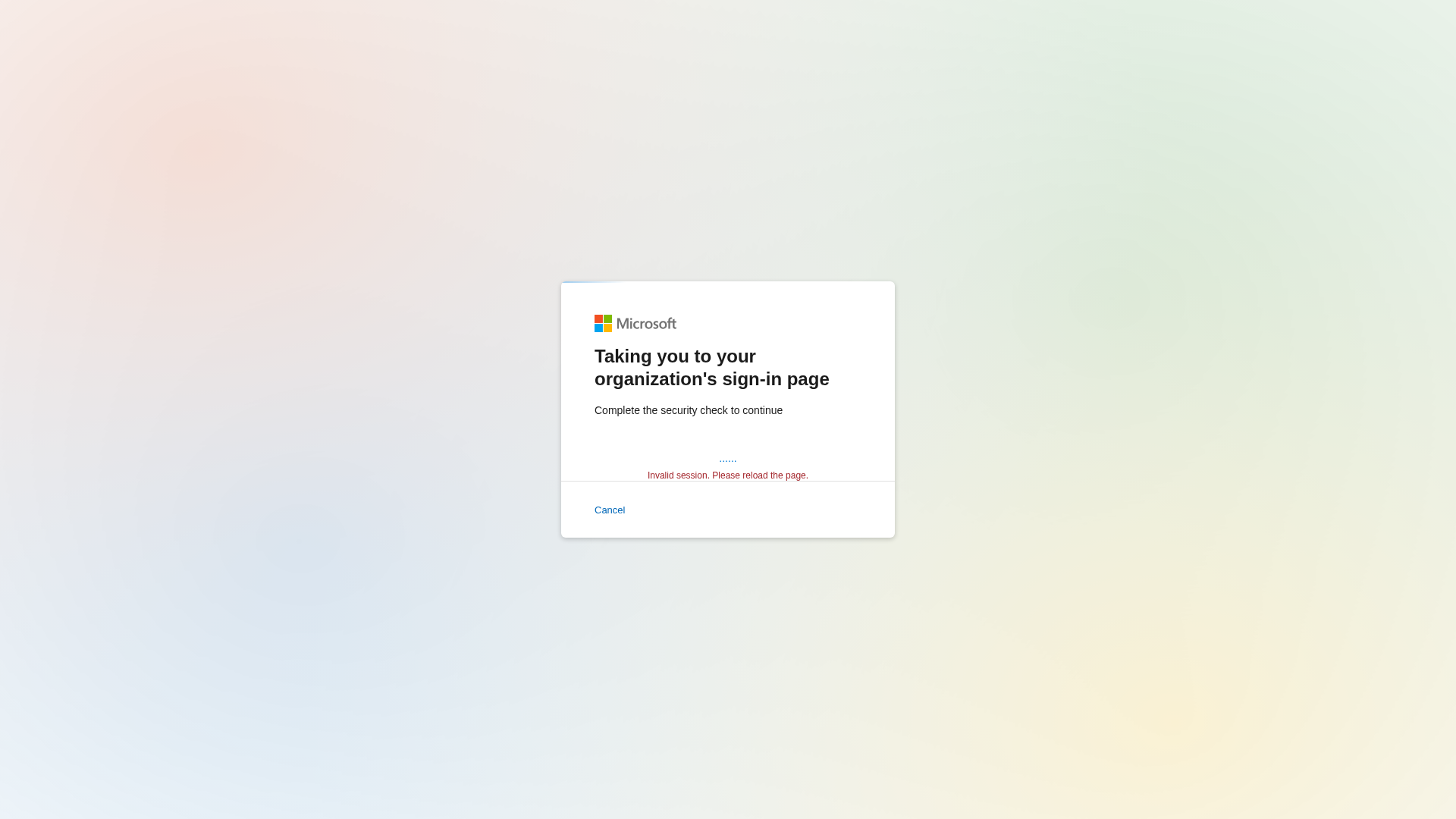
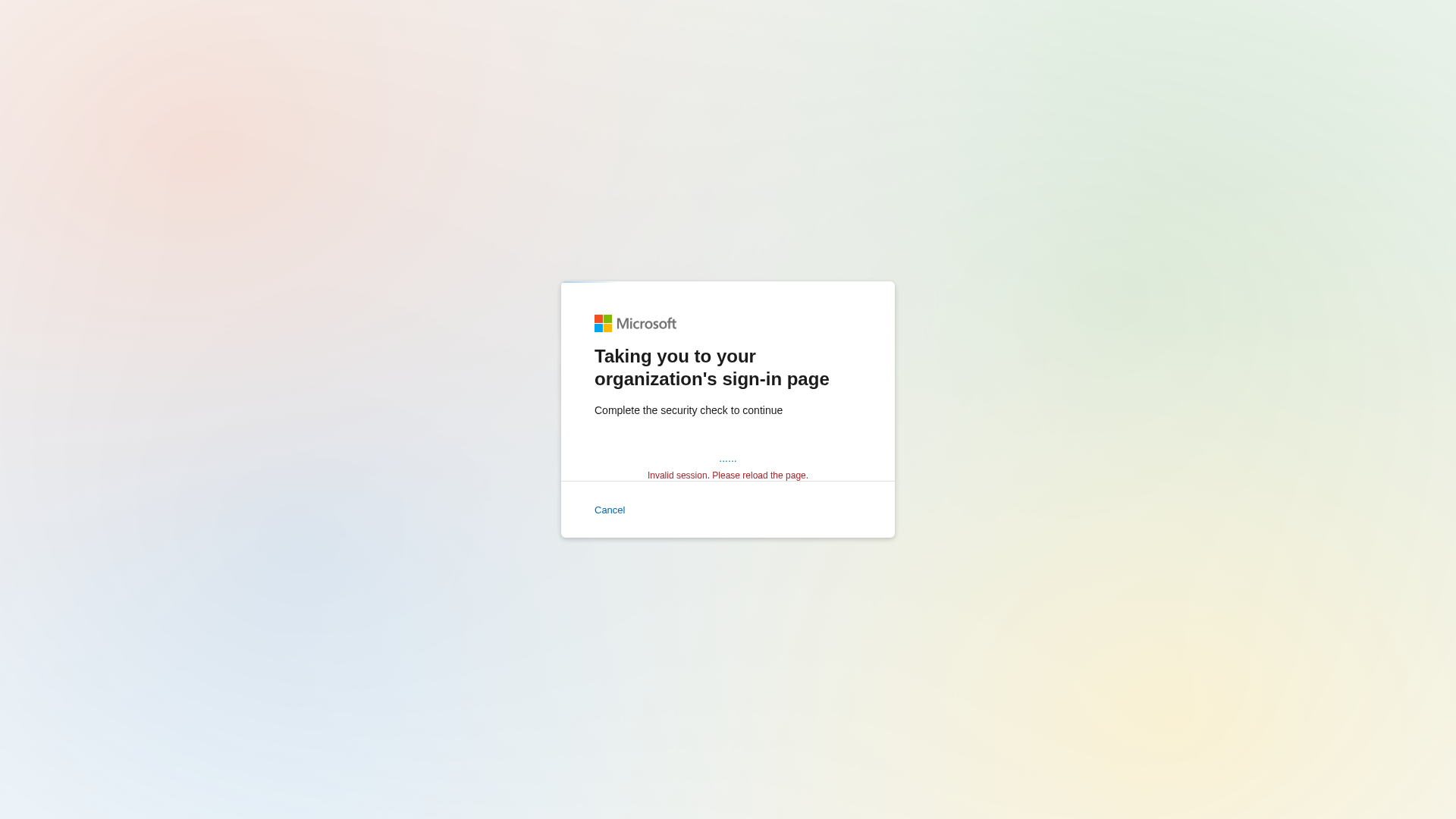
Visual Capture
Detection Info
https://pub-f8ae05628d044493abc7f11a802215fc.r2.dev/index.html?acfe0978063298d1ad8631df9bb563
Detected Brand
Microsoft
Country
International
Confidence
100%
HTTP Status
200
Report ID
20c6ab88-a45…
Analyzed
2026-01-01 03:21
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1CC218B78E048993747A3D5D9A6A1A35F3AA0878CD7130B055FF8039926DFEA8CD021D9 |
|
CONTENT
ssdeep
|
24:n/nTxVx/cIgDETsCVlWJnPKgNPALc756Fl+Nit8zZrAd:ntf/cIgwYCvANPW8CMiN |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9b4be68cd933c88c |
|
VISUAL
aHash
|
180018081d1f1fbf |
|
VISUAL
dHash
|
7161717b33717d79 |
|
VISUAL
wHash
|
391818081f1f1fff |
|
VISUAL
colorHash
|
07000088041 |
|
VISUAL
cropResistant
|
7161717b33717d79 |
Code Analysis
Risk Score
81/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🔬 Threat Analysis Report
• Threat: Microsoft login page phishing.
• Target: Microsoft users, especially those in organizations using Microsoft services.
• Method: Displays a fake sign-in page that is designed to look like a genuine Microsoft login page to steal credentials.
• Exfil: Likely attempts to exfiltrate data to a server controlled by the attacker. Due to obfuscation, specific exfil details are hard to determine.
• Indicators: The URL uses a free hosting service (r2.dev), there is JavaScript obfuscation (atob, base64_strings) and the domain does not match the official Microsoft domain.
• Risk: HIGH - The phishing site aims to steal user credentials leading to account compromise.
🔒 Obfuscation Detected
- atob
- base64_strings
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Microsoft
http://pub-60feb3b0da144b72b0f8c76714a15abf.r2.dev/index.htm...
Apr 05, 2026
Microsoft
https://pub-f8ae05628d044493abc7f11a802215fc.r2.dev/index.ht...
Feb 17, 2026
Microsoft
https://pub-60feb3b0da144b72b0f8c76714a15abf.r2.dev/index.ht...
Feb 17, 2026
Microsoft
https://pub-5c4cef75b08546e281f71e80755c72f1.r2.dev/index.ht...
Feb 17, 2026
Microsoft
https://pub-60feb3b0da144b72b0f8c76714a15abf.r2.dev/index.ht...
Jan 20, 2026
Scan History for pub-f8ae05628d044493abc7f11a802215fc.r2.dev
Found 2 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.