
Phishing Analysis
Detailed analysis of captured phishing page
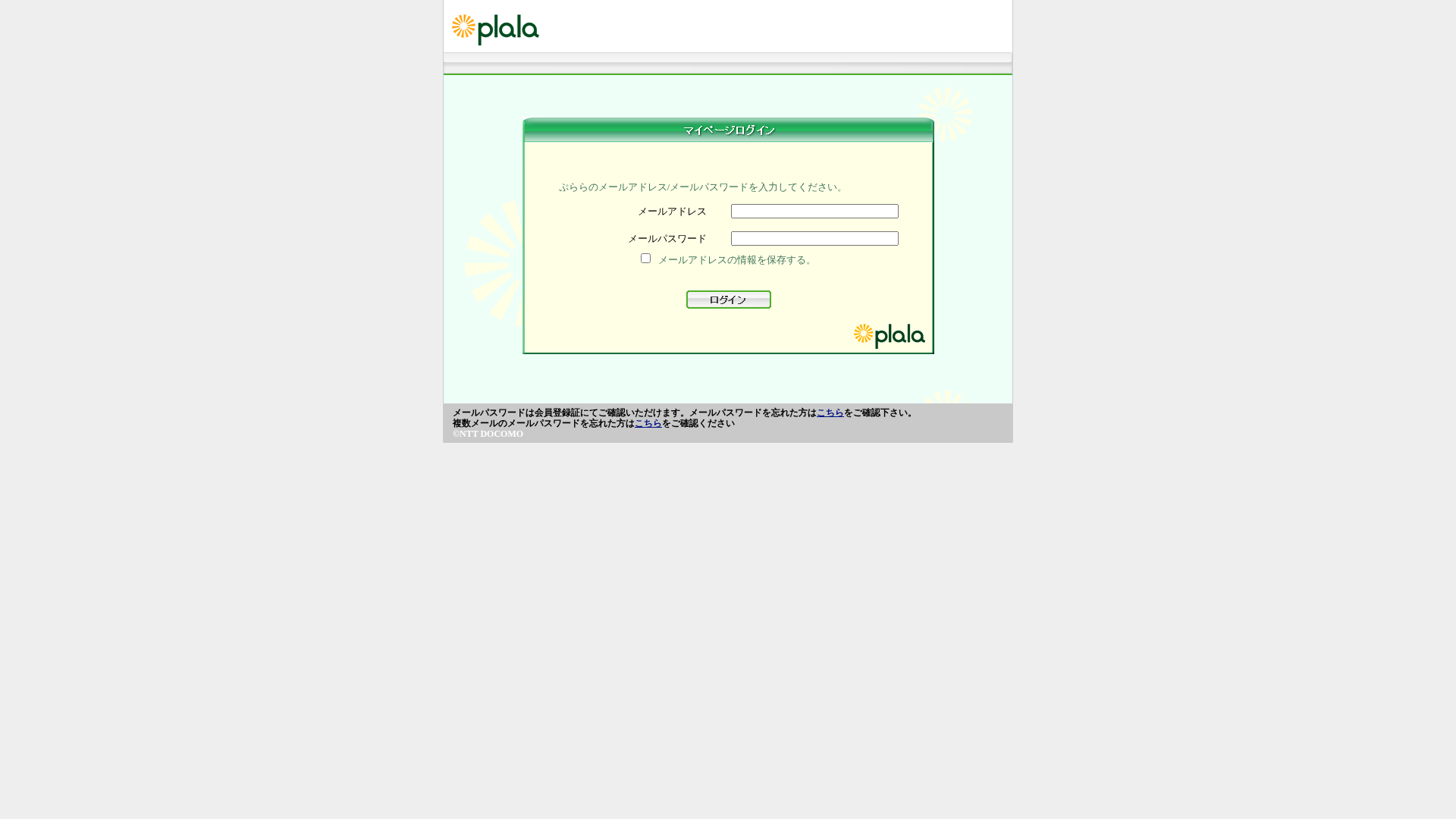
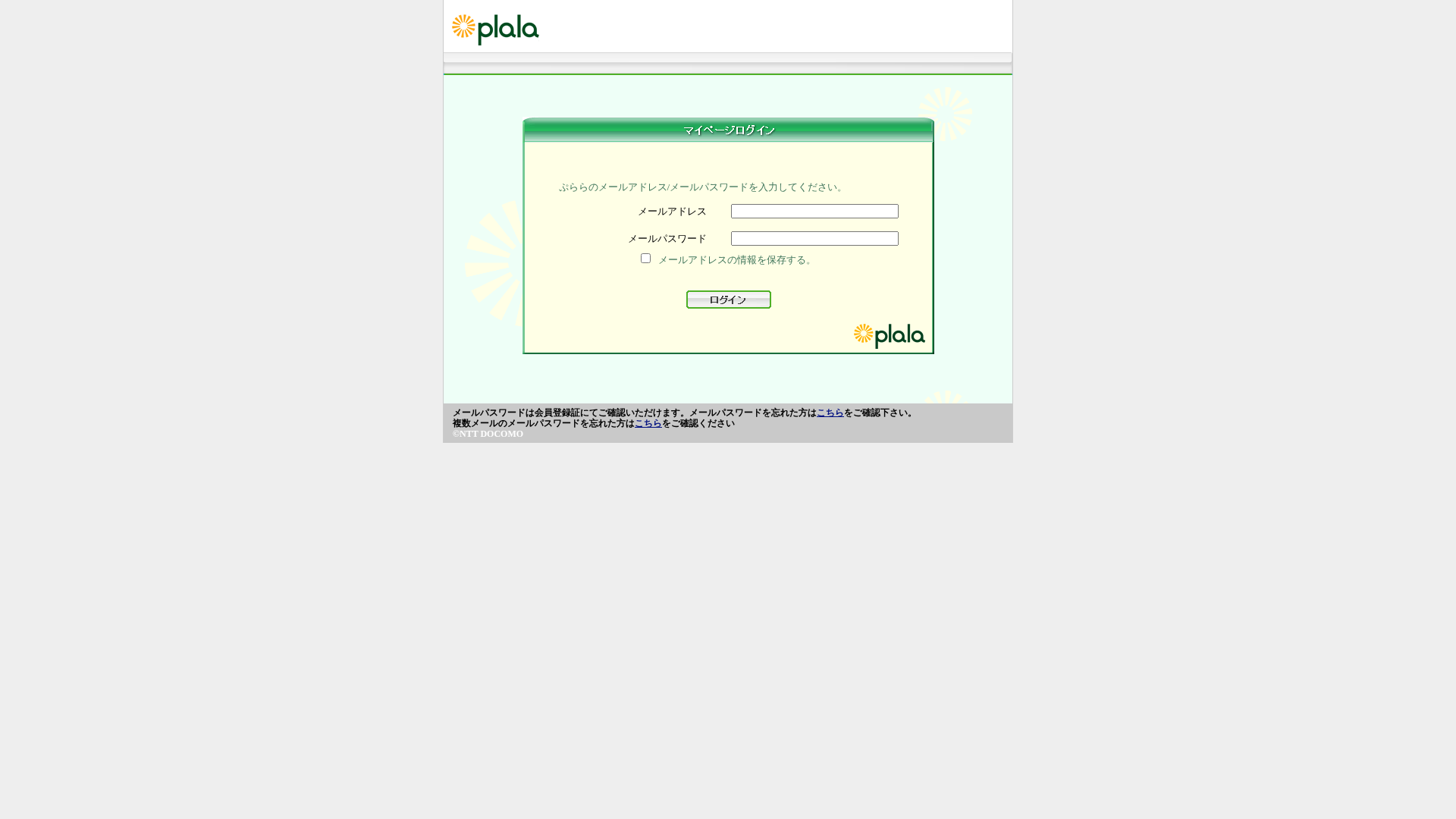
Visual Capture
Detection Info
https://marutitraders99.com/plalaa.or/jpn/webmai1/index.php
Detected Brand
Plala
Country
Japan
Confidence
100%
HTTP Status
200
Report ID
214912be-c6d…
Analyzed
2025-12-24 19:05
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T16C91001813853B4F99A552A3D3752E9493E2541EC7324C48A85EE72F1C8814EEC7F9FC |
|
CONTENT
ssdeep
|
96:A3ydpoIL/N+lglAtyHL5ZiNr2t5CLJWfsT3yDSxyHJHAPboRbDY7YoDSZHlfd5D:j2kcRMgc0QD |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b29e9a3131dccc99 |
|
VISUAL
aHash
|
dfe7bdc3c3ffefff |
|
VISUAL
dHash
|
394c68049e600800 |
|
VISUAL
wHash
|
1c243c3cc0d0fcfc |
Code Analysis
Risk Score
65/100
Threat Level
CRITICAL
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 Banking
🔬 Threat Analysis Report
• Threat: Credential harvesting phishing
• Target: Plala users
• Method: Fake login form stealing email and password
• Exfil: Likely to a malicious server (not visible but implied by the phishing nature)
• Indicators: Domain mismatch, brand impersonation
• Risk: HIGH - Credential theft
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Plala
http://salalatour.com/updateplala.or.jp/jpn/webmai1/index.ph...
Apr 01, 2026
Plala
http://salalatour.com/plala.or.jp/jpn/webmai1/index.php
Apr 01, 2026
Plala
http://marutitraders99.com/plalaa/jpn/webmai1/index.php
Mar 31, 2026
Plala
http://marutitraders99.com/plalaa/jpn/webmai1/index.php
Mar 30, 2026
Plala
http://nisha-interiors.com/plala.orr/jpn/webmai1/index.php
Mar 27, 2026
Scan History for marutitraders99.com
Found 5 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.