
Phishing Analysis
Detailed analysis of captured phishing page
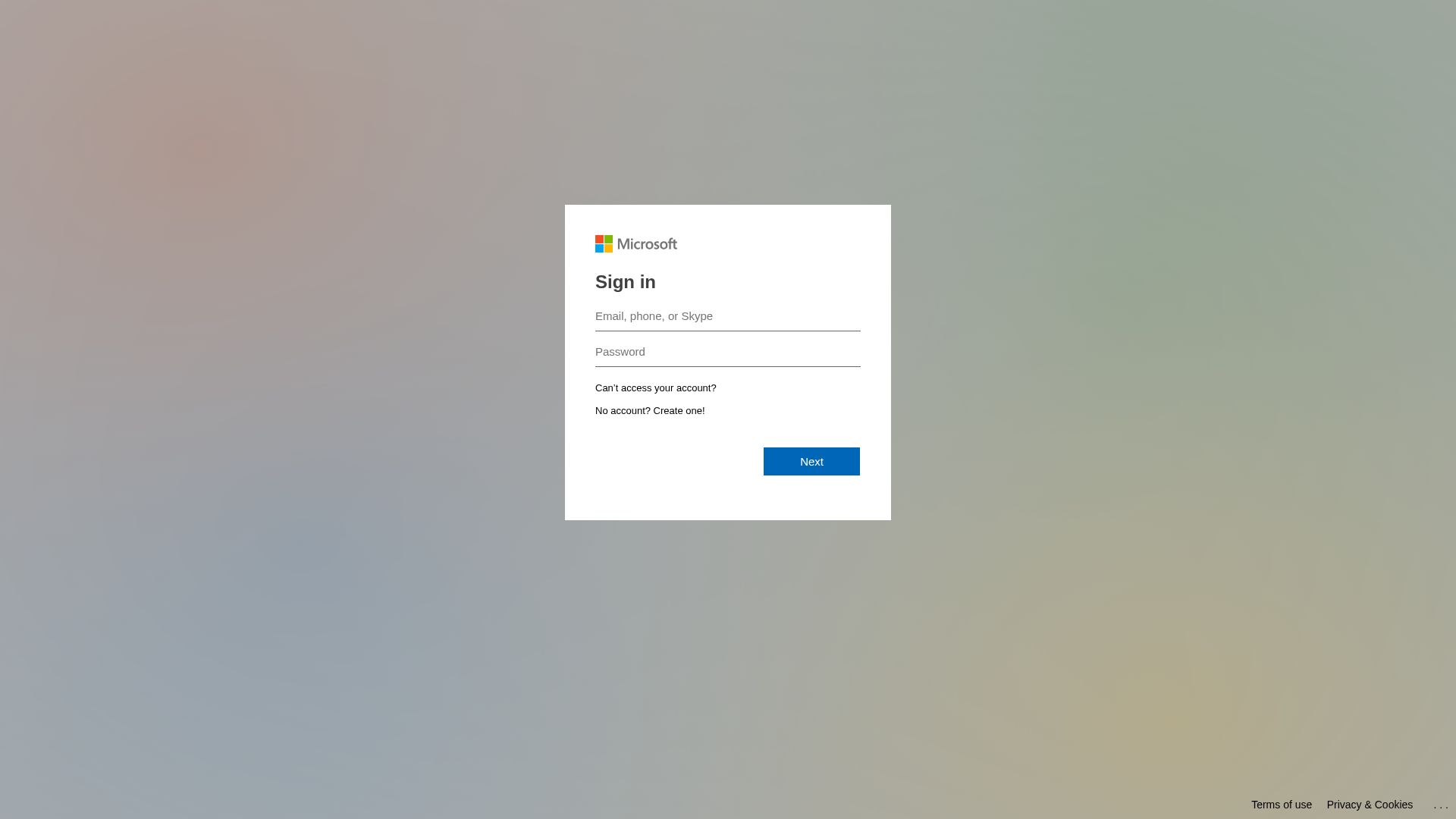
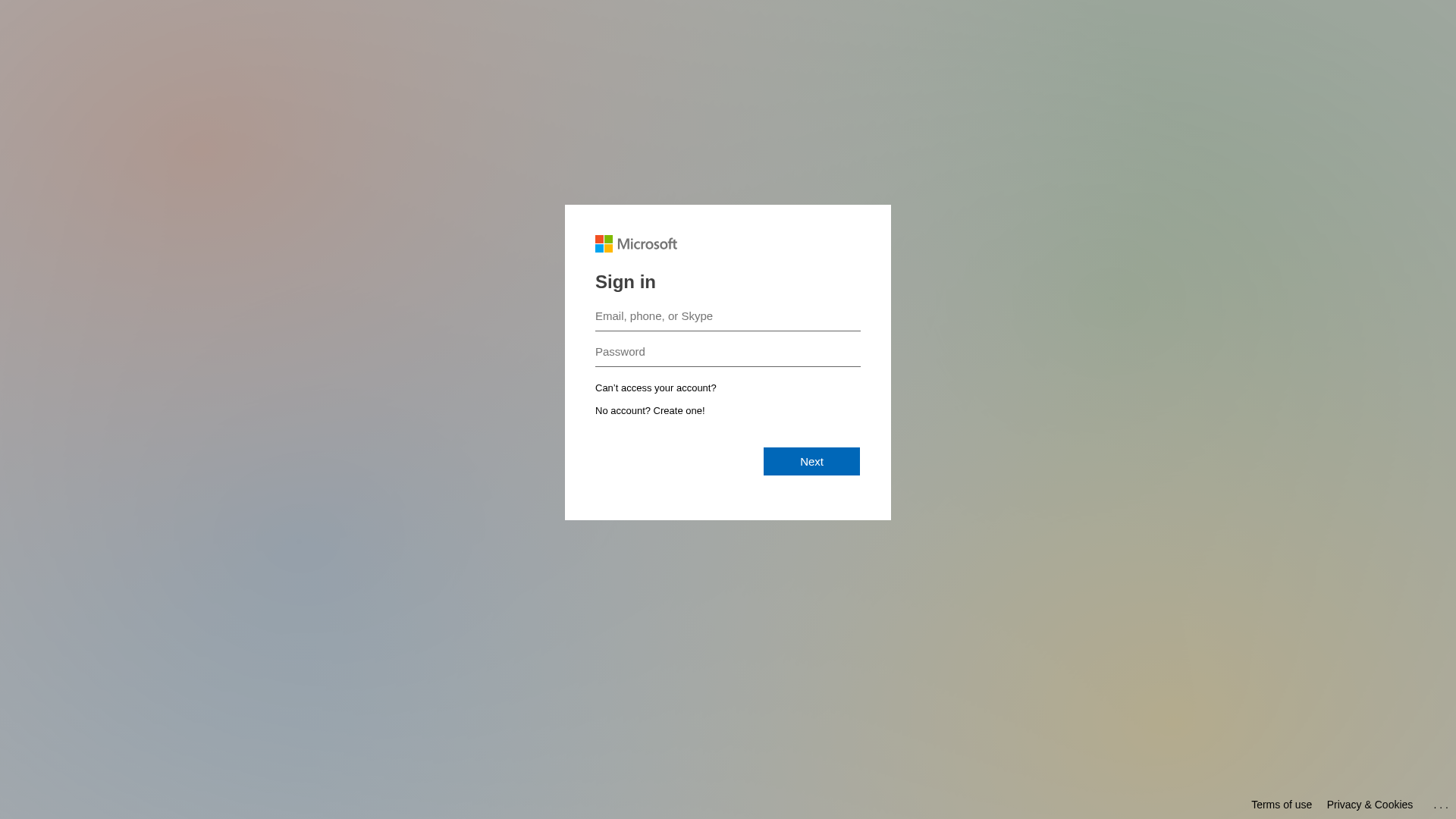
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T17E41971CD2110346E357EE90F9A2FB9666140BC0C6134A7C6AB9967AB1CE27553723CD |
|
CONTENT
ssdeep
|
48:T0i0Hls5hwhjO7c2ZgV0jxJF0jIPcU85D4c5hkj0:Tfjhh7xg6jxJqjJTt4g5 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9cc97326cc99d98c |
|
VISUAL
aHash
|
0000181818180000 |
|
VISUAL
dHash
|
6171333232327c78 |
|
VISUAL
wHash
|
1818181c1f1f1fff |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
6171333232327c78 |
Code Analysis
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for mgamt.com
Found 10 other scans for this domain
-
https://mgamt.com/landing/form/21bc5847-bbc2-4619-...
https://mgamt.com/landing/form/1b05be23-e63d-4450-...
https://mgamt.com/landing/form/33ea672b-2f23-4a2f-...
https://mgamt.com/landing/form/87a63a6a-17b4-4186-...
https://mgamt.com/landing/form/9a701f4d-e4dc-4658-...
https://mgamt.com/landing/form/6ba1432a-88ea-4e64-...
https://mgamt.com/landing/form/8a4d9b6d-1def-4aad-...
https://mgamt.com/landing/form/97d4a173-9d2e-44ac-...
https://mgamt.com/landing/form/9be989a0-3b32-448e-...
https://mgamt.com/landing/form/e4471f71-58a9-4bfe-...
