
Phishing Analysis
Detailed analysis of captured phishing page
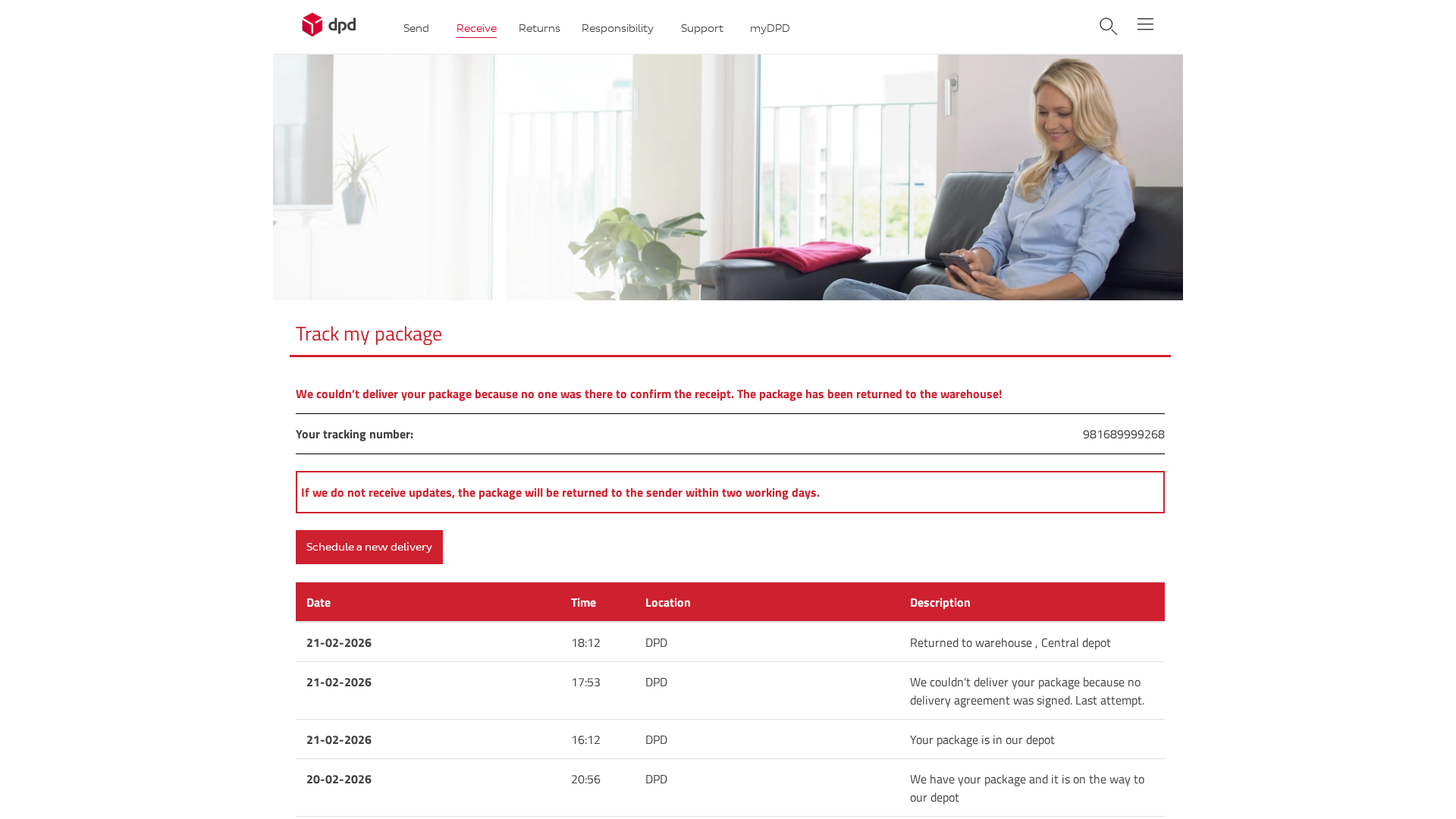
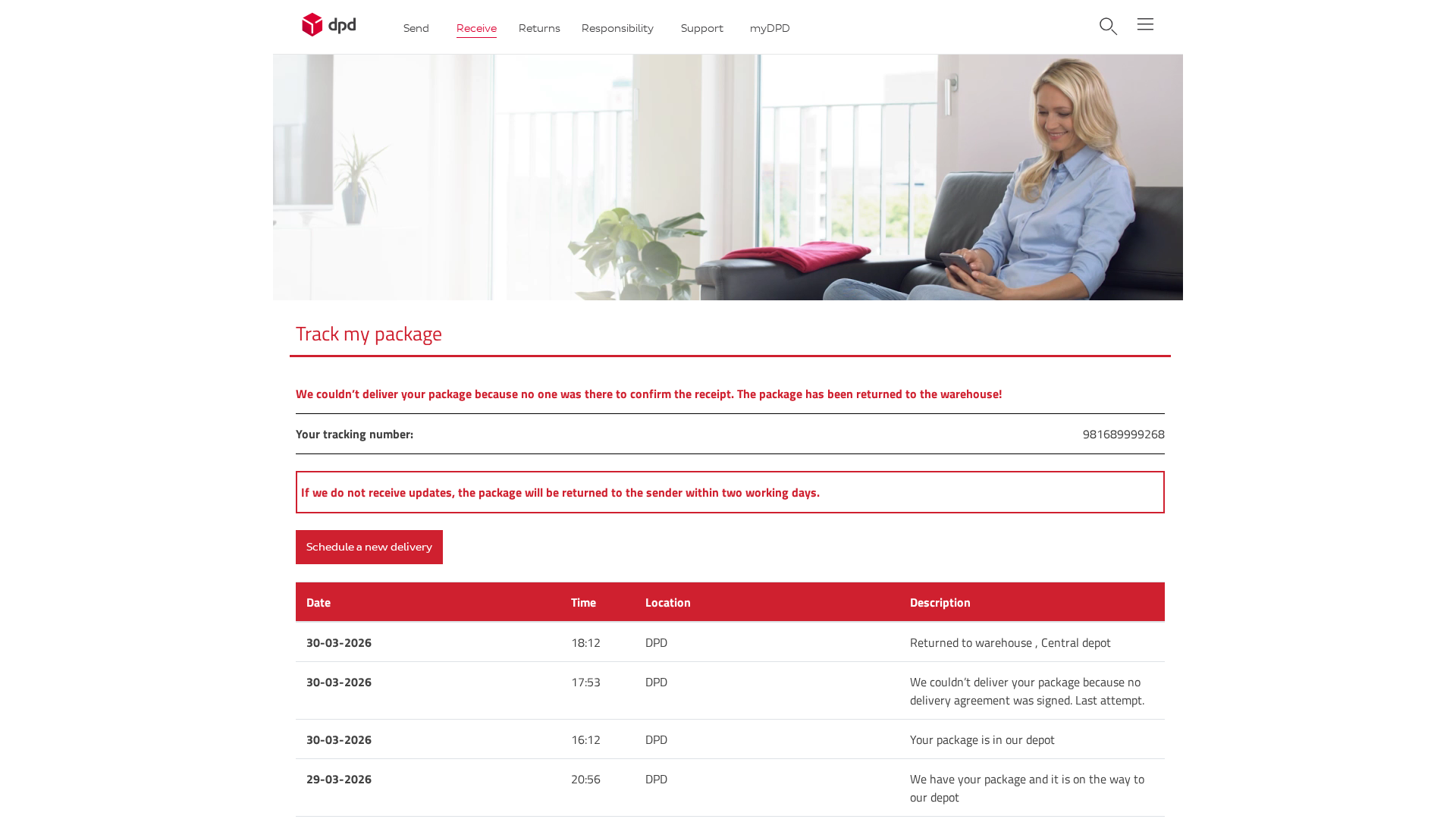
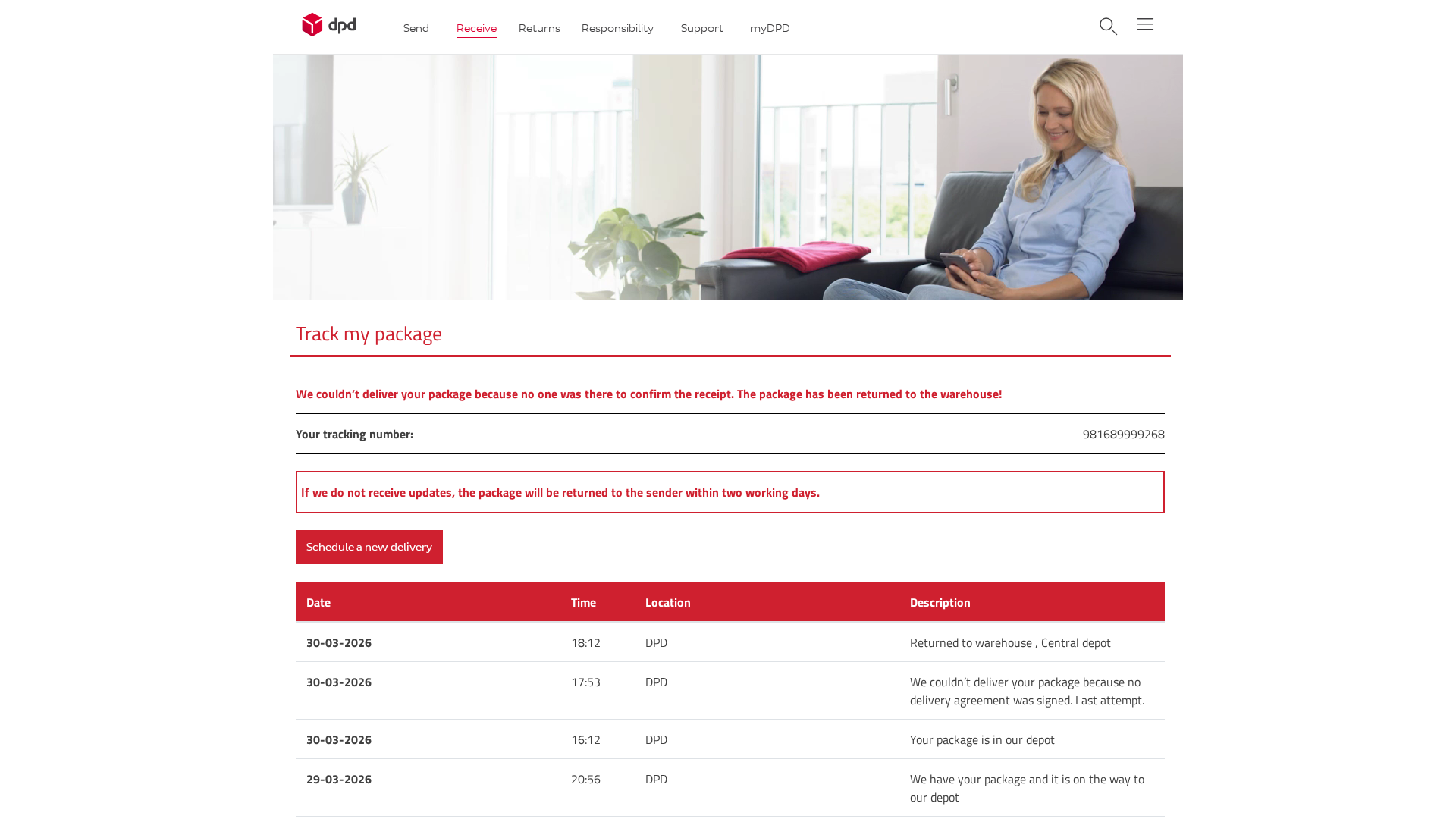
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T16EB2F17094B5B63F009F7391A7386709A3D39783CB520BE567F8936D4B8AE84DC23169 |
|
CONTENT
ssdeep
|
192:bixLoxwz77qKHv/ySchJrVUmZGkoRXTCReWyRMOsUFf9kITIJO:mx8xw7pvKpJrVUIGkk+TxFUHIJO |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e96b899c962666c3 |
|
VISUAL
aHash
|
f9e9e1f7ff81c3ff |
|
VISUAL
dHash
|
2b030327382b1342 |
|
VISUAL
wHash
|
a9a1e1c7c78181fb |
|
VISUAL
colorHash
|
07000000006 |
|
VISUAL
cropResistant
|
2b030327382b1342,696969c9692b3734,337367e7cdcd8d1d,0000db6464649b24 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: DPD customers
• Method: Impersonation and data harvesting
• Exfil: date.php
• Indicators: Suspicious Domain, obfuscated javascript, attempts to harvest tracking information.
• Risk: High
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- base64_strings
🎯 Kit Endpoints
- ./app/wp-content/themes/DPD_Login/css/styles.min5b21.css?ver=6.0.2
📡 API Calls Detected
- GET
- POST
- https://whos.amung.us/stats/
📤 Form Action Targets
- date.php
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 17 obfuscation techniques
🏢 Brand Impersonation Analysis
Fraudulent Claims
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker impersonates DPD to trick users into entering tracking information, which can then be used to potentially access the account of steal more data.
Secondary Method: Data Exfiltration
The data entered into the form is likely sent to a remote server (date.php) controlled by the attacker.
🌐 Infrastructure Indicators of Compromise
Domain Information
🤖 AI-Extracted Threat Intelligence
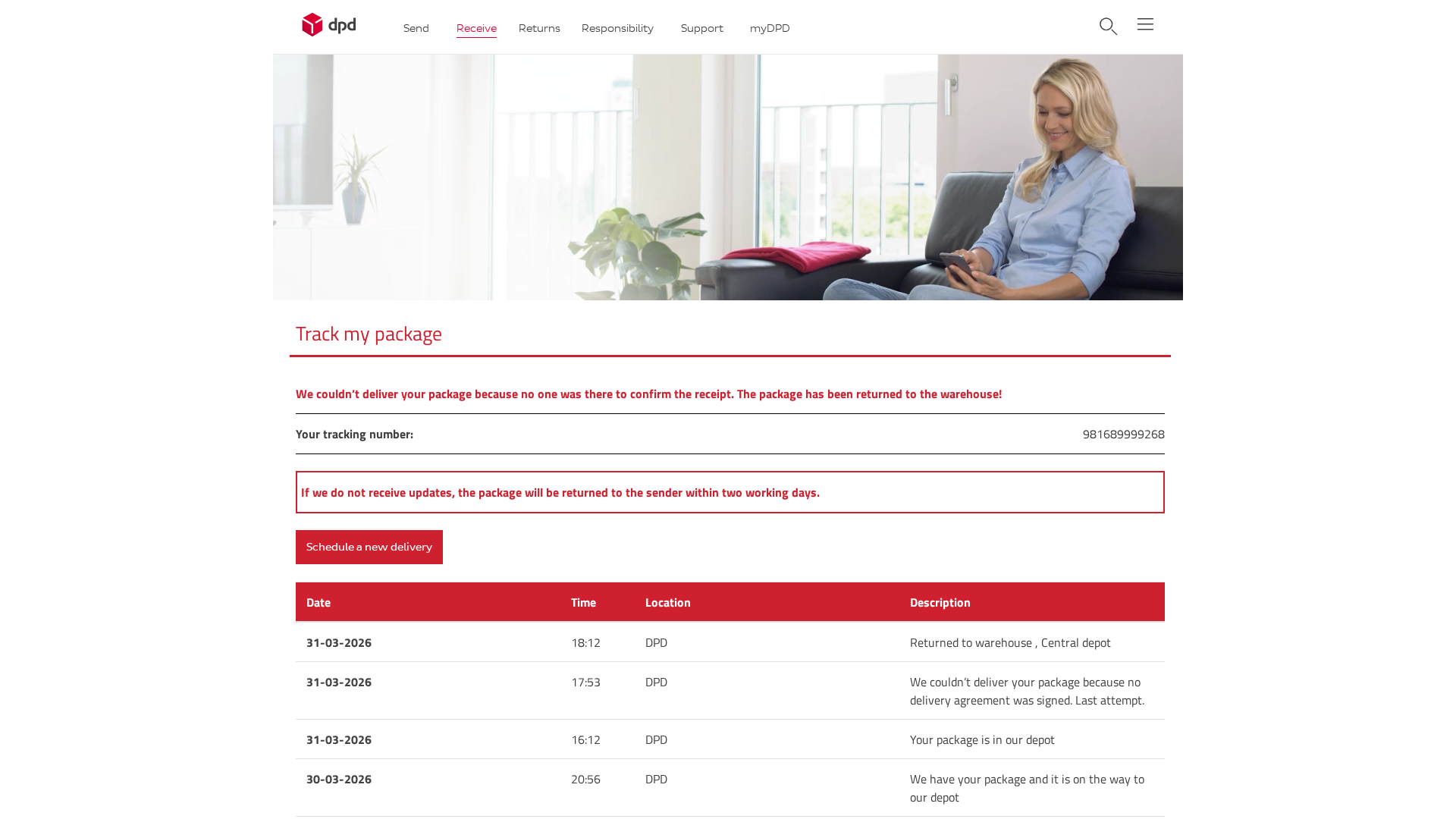
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
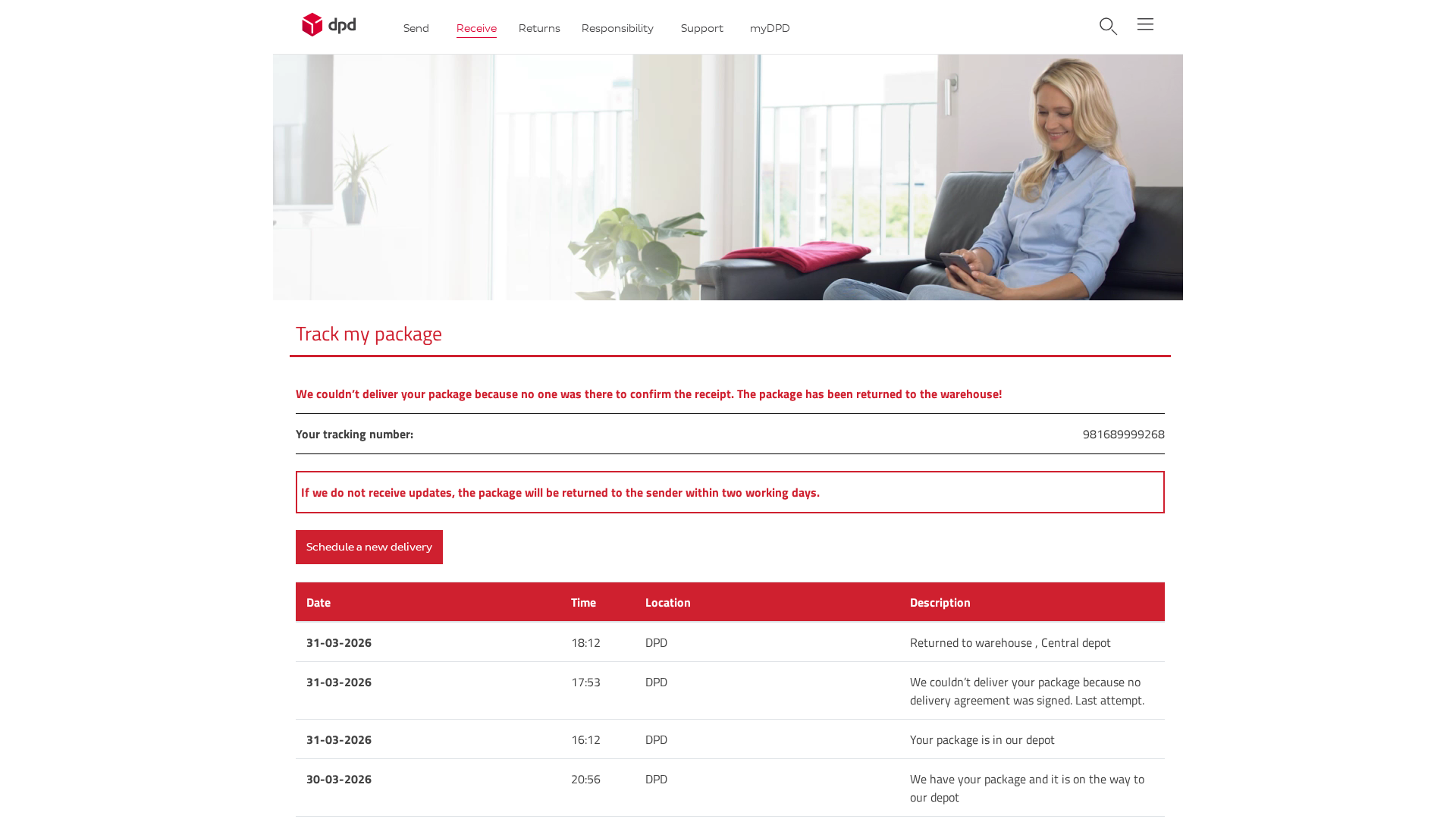
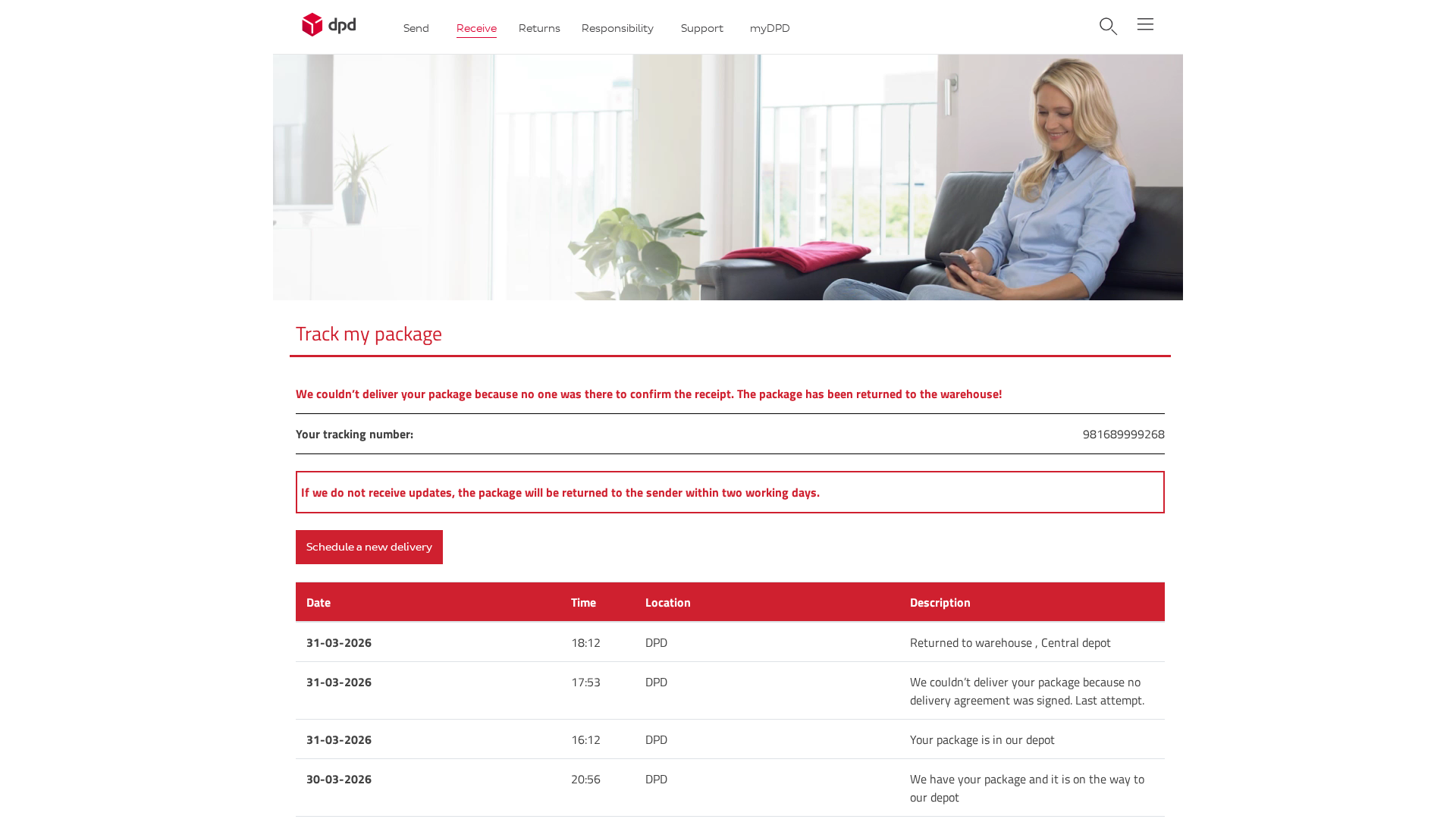
Scan History for 87-106-70-155.cprapid.com
Found 3 other scans for this domain
