Phishing Analysis
Detailed analysis of captured phishing page
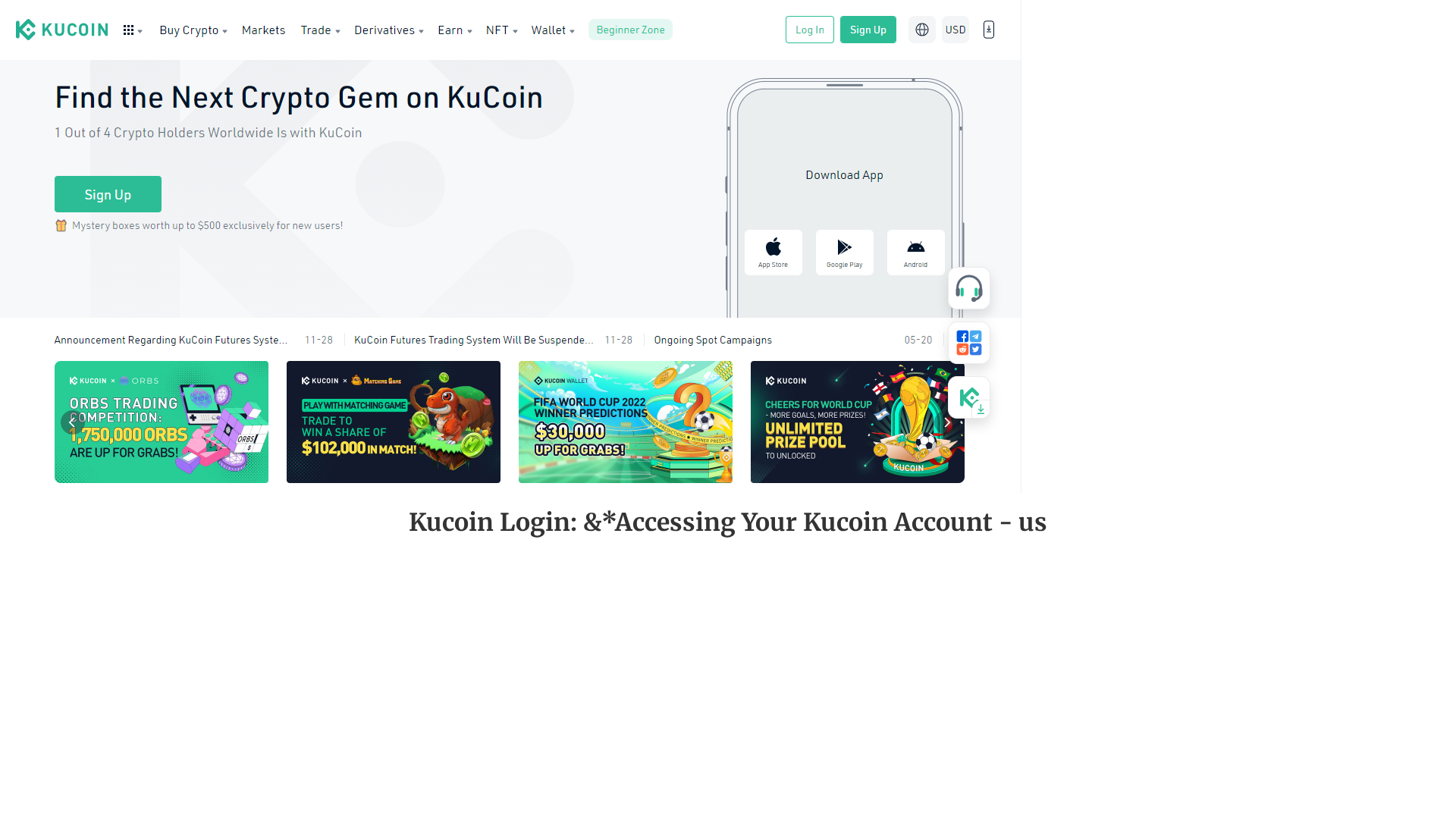
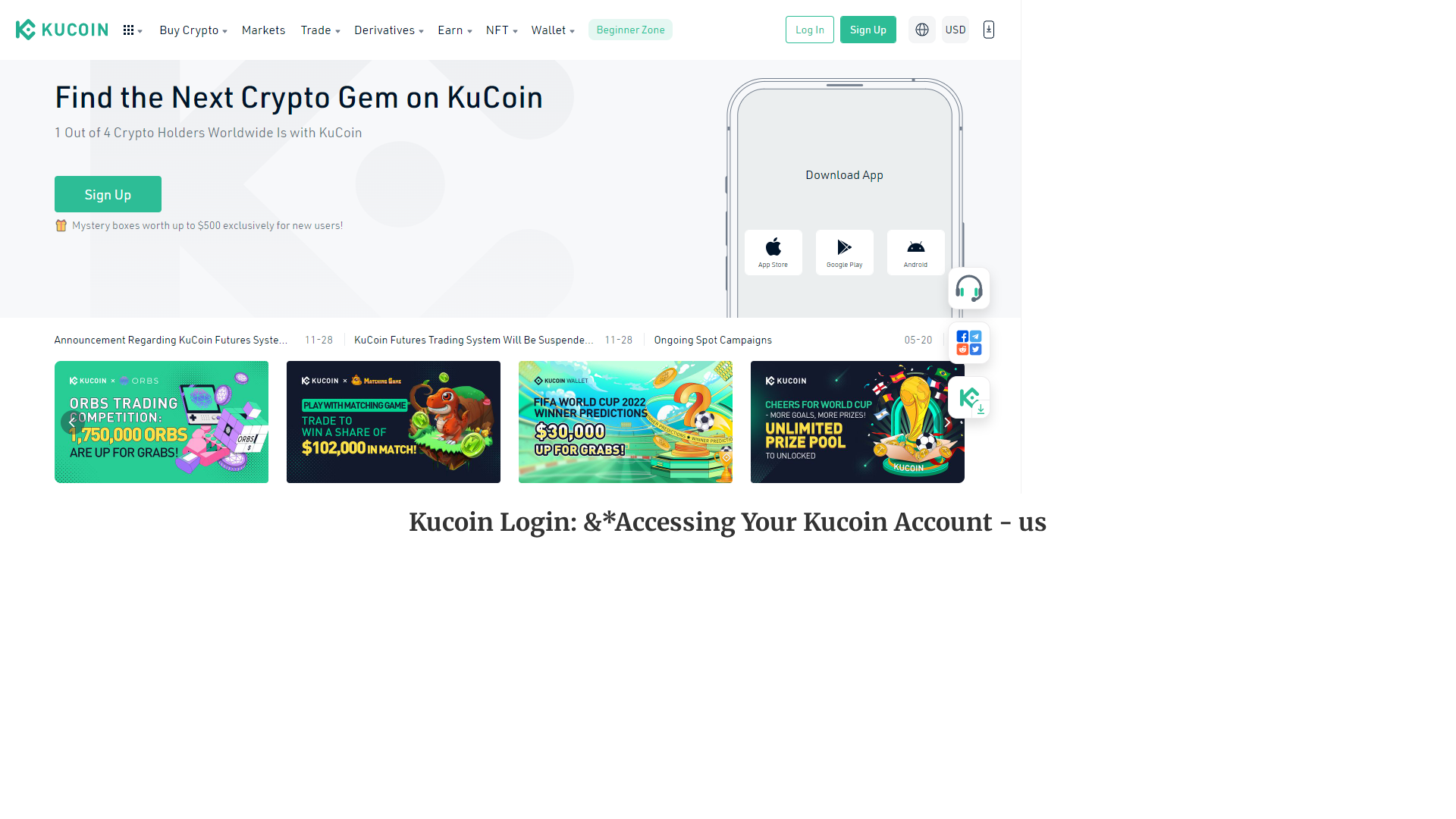
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1E14152BBA46C692F0355CAE87C52B0CCD64628AFD7D0B9C3A8F0114D97AD6CB8B6144D |
|
CONTENT
ssdeep
|
48:SjA9+755pIsL7c+ZYPJrKcMJ4o+u/1JnlA2VJ/tJFJL1Jny+I:Y/5JYPYTSo/tVlVxtnjVi |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
bc06c33c3cdbc136 |
|
VISUAL
aHash
|
bf37ff0303ffffff |
|
VISUAL
dHash
|
76e6c626261a2004 |
|
VISUAL
wHash
|
1703030303c3ffff |
|
VISUAL
colorHash
|
07008000600 |
|
VISUAL
cropResistant
|
76e6c626261a2004,85a4a68c8cced62c,a58f2fac8c8c9c6c |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: KuCoin users
• Method: Impersonation via free hosting.
• Exfil: Unknown, likely credentials or account takeover.
• Indicators: Free hosting, Kucoin branding.
• Risk: HIGH
🔒 Obfuscation Detected
- fromCharCode
- unicode_escape
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
- 12 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The phishing site is designed to trick users into entering their KuCoin login credentials on a fake login page, which are then harvested by the attackers.
Secondary Method: Social Engineering
The site uses legitimate branding to lure users. The site may also have additional links which redirect users to malicious scripts.
🌐 Infrastructure Indicators of Compromise
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for kucainluginc.webflow.io
Found 2 other scans for this domain