
Phishing Analysis
Detailed analysis of captured phishing page
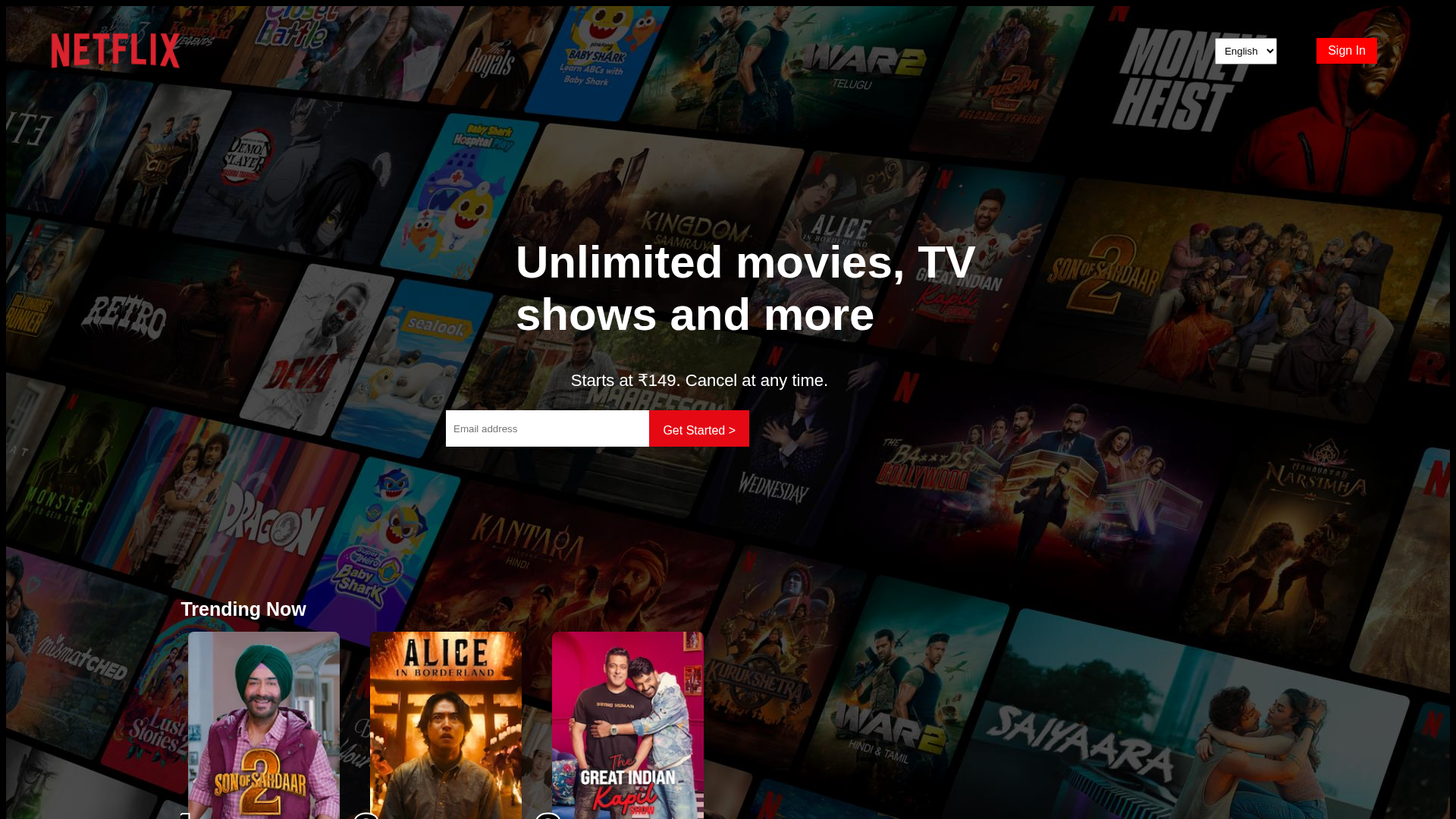
Visual Capture
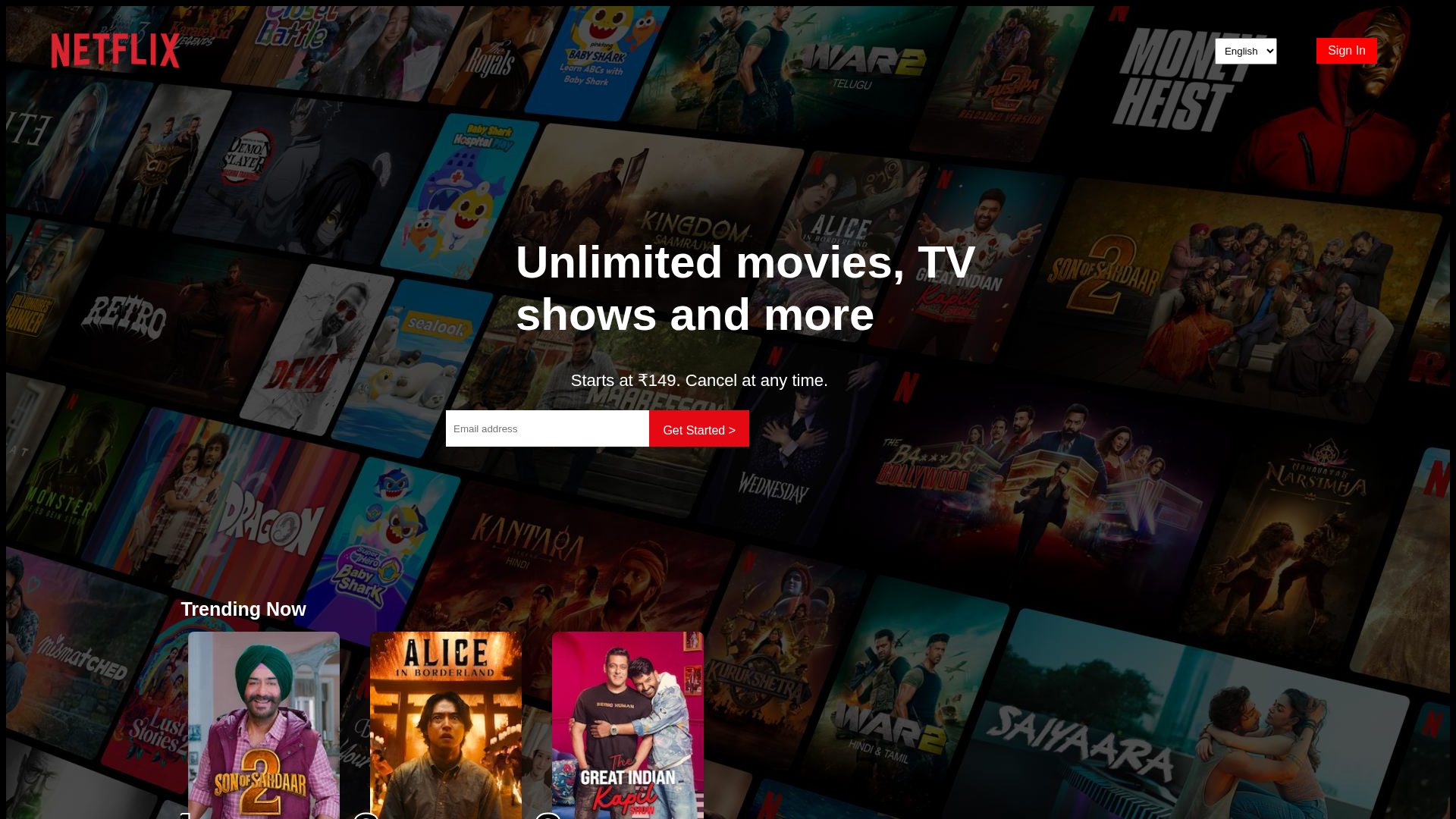
Detection Info
https://vadiyalasrinivasreddy01-a11y.github.io/netflix
Detected Brand
Netflix
Country
International
Confidence
95%
HTTP Status
200
Report ID
23f92486-473…
Analyzed
2026-03-02 13:22
Final URL (after redirects)
https://vadiyalasrinivasreddy01-a11y.github.io/netflix/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1A2B112BB5055EE63049382E193785F4F7A81878ADF431A009BE9D34D9F86E5CDE922C1 |
|
CONTENT
ssdeep
|
96:TP6N9AX2qEOj9zXgbGz10IKo5SpeFyHtJmD9H+K4L9Ul1Vlkk0O:D6obGGWIRYHDS9eKC9Un/V |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
c41ff532c4893997 |
|
VISUAL
aHash
|
021038307040f5f3 |
|
VISUAL
dHash
|
e2a673e3e49dc5a6 |
|
VISUAL
wHash
|
3a103f787040f7f3 |
|
VISUAL
colorHash
|
39400008040 |
|
VISUAL
cropResistant
|
e600027272020014,e2a673e3e49dc5a6 |
Code Analysis
Threat Level
ALTO
⚠️ Phishing Confirmed
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Netflix users
• Method: Impersonation through a look-alike page.
• Exfil: Email Address
• Indicators: Free hosting and Netflix branding
• Risk: High
🎯 Kit Endpoints
- https://occ-0-2663-2164.1.nflxso.net/dnm/api/v6/mAcAr9TxZIVbINe88xb3Teg5_OA/AAAABXuxnTub5falOGY9MXXmFvUqTEHS-jYkcWNjQr7OAdPRQ7mtHheMBLi4uJi9rhLCLcsfHlrNXWRbuNGcCWRkJUoWlT92oqoEoWE.webp?r=00a
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Free Hosting
The site is hosted on a free hosting platform (github.io), a common practice for phishing sites.
Brand Impersonation
The site is attempting to impersonate a well-known brand (Netflix) to gain trust and steal information
🔬 Comprehensive Threat Analysis
Threat Type
Netflix Credential Harvester
Target
Netflix users (International)
Attack Method
Brand impersonation + credential harvesting forms
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
LOW - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
🏢 Brand Impersonation Analysis
Impersonated Brand
Netflix
Official Website
https://www.netflix.com/
Fake Service
Netflix
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker aims to collect email addresses through a convincing look-alike landing page, aiming for further exploitation.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
vadiyalasrinivasreddy01-a11y.github.io
Registered
None
Registrar
None
Status
None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Netflix
https://vadiyalasrinivasreddy01-a11y.github.io/netflix/
Jan 19, 2026
Netflix
https://vadiyalasrinivasreddy01-a11y.github.io/netflixclone/
Jan 04, 2026
Netflix
https://vadiyalasrinivasreddy01-a11y.github.io/netflix/
Jan 01, 2026
Netflix
http://vadiyalasrinivasreddy01-a11y.github.io/netflix
Dec 24, 2025
Scan History for vadiyalasrinivasreddy01-a11y.github.io
Found 6 other scans for this domain
-
https://vadiyalasrinivasreddy01-a11y.github.io/net...
http://vadiyalasrinivasreddy01-a11y.github.io/netf...
https://vadiyalasrinivasreddy01-a11y.github.io/net...
https://vadiyalasrinivasreddy01-a11y.github.io/net...
https://vadiyalasrinivasreddy01-a11y.github.io/net...
http://vadiyalasrinivasreddy01-a11y.github.io/netf...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.