
Phishing Analysis
Detailed analysis of captured phishing page
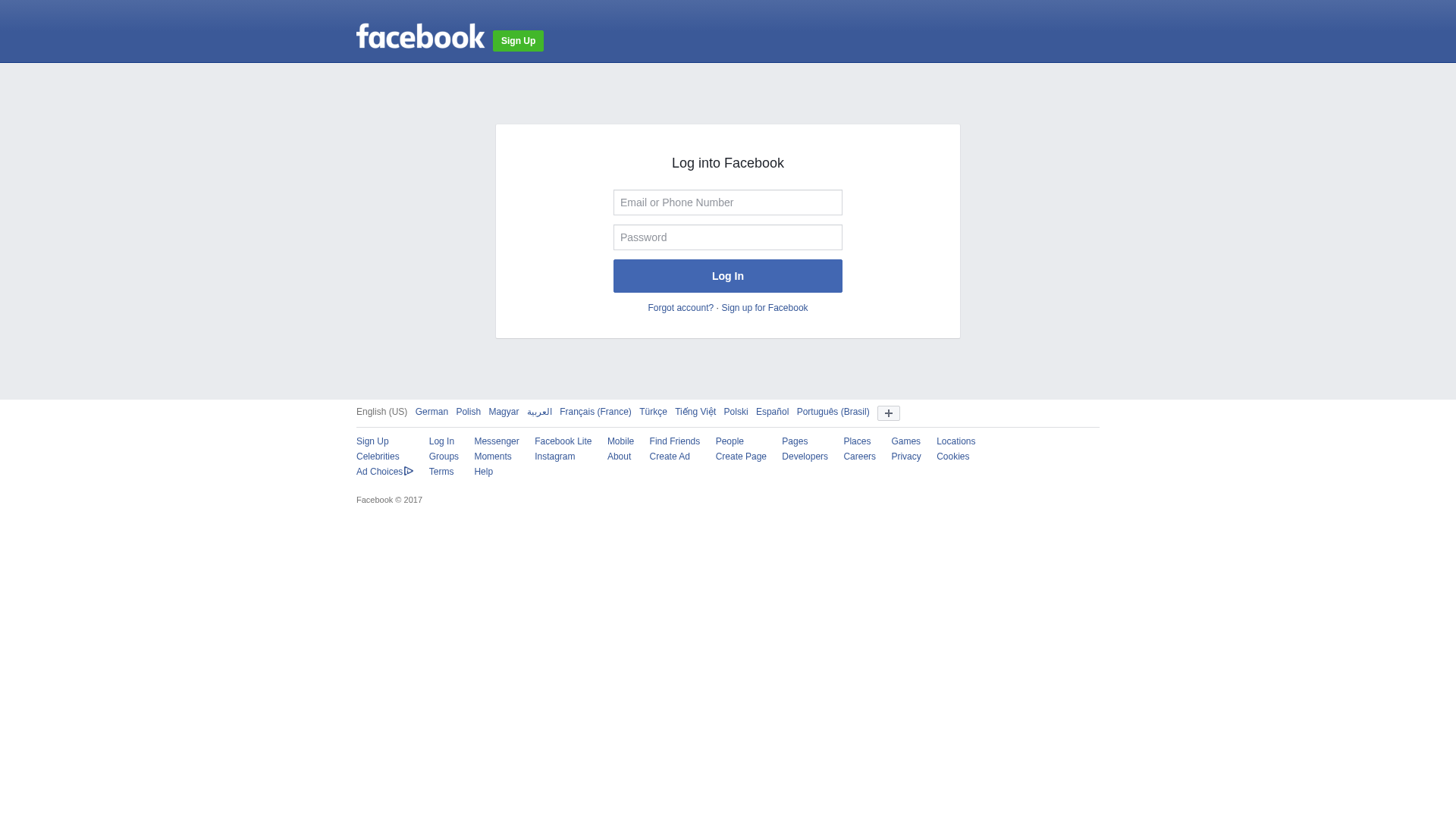
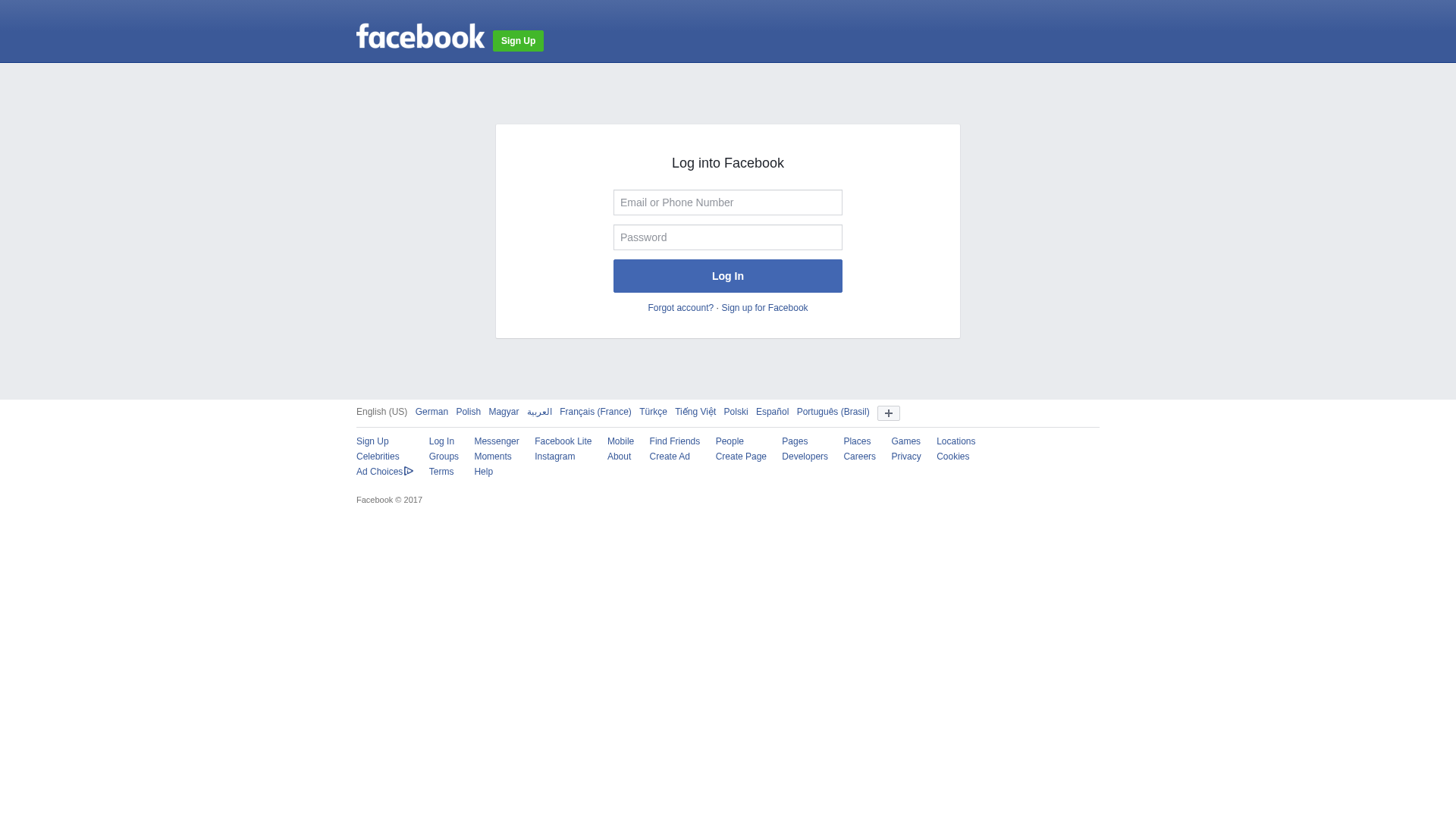
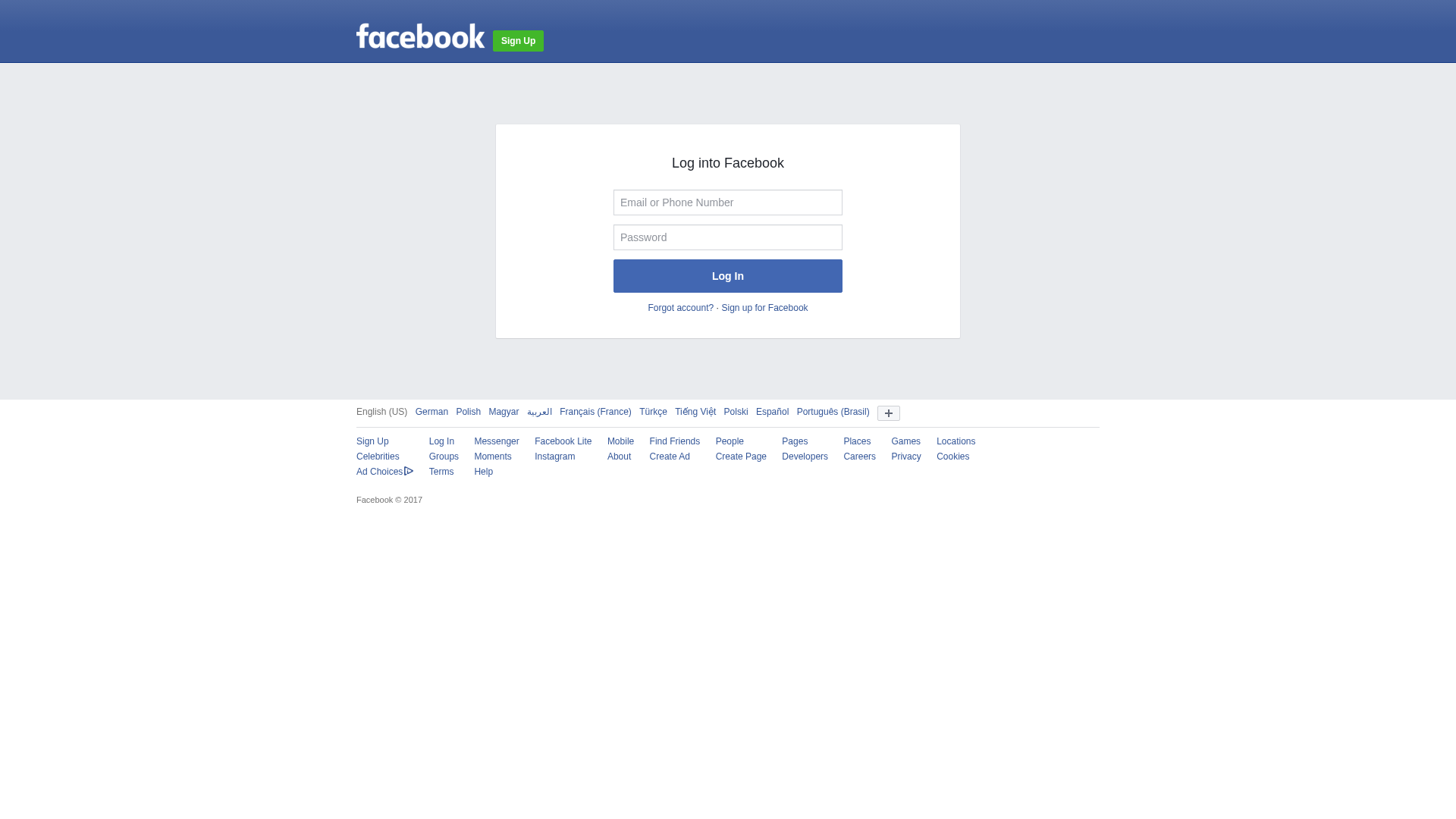
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1F4C13AB728C03207126F8A945996FB5ED19B069B8AF10F2351D9340DF5A3FF2D98F44A |
|
CONTENT
ssdeep
|
96:TTZCKGvKGRKGoS2MK9KGU9KGtKGBlKGPKGEKG19KG2KGDKGoKGbFb1SLm1KG2KGm:/Zznlqv63tHc5KjqU1SJKHjcOPYkIKrl |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
c343494d65636767 |
|
VISUAL
aHash
|
00ff24e7ffffffff |
|
VISUAL
dHash
|
4c20692916000000 |
|
VISUAL
wHash
|
00180000cfffffff |
|
VISUAL
colorHash
|
07007000000 |
|
VISUAL
cropResistant
|
306868342c000000,121150c948484830 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Facebook Users
• Method: Domain spoofing and potentially malicious code.
• Exfil: Unknown (password likely)
• Indicators: Domain mismatch, obfuscation.
• Risk: High
🔒 Obfuscation Detected
- fromCharCode
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Personal Info
- 4 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The site uses a visually identical login form to trick users into entering their Facebook credentials. These credentials are then captured by the attacker.
Secondary Method: JavaScript Obfuscation
The site utilizes obfuscated Javascript code to hide the malicious actions like credential harvesting, redirection, etc.
🌐 Infrastructure Indicators of Compromise
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for fnxx.info
Found 10 other scans for this domain
-
http://fnxx.info/c7134438766b12414dpbdd7ebaad251a9...
https://fnxx.info/z4861f563ya621420asab3f568ev2ae7...
http://fnxx.info/c6b2154a16ca154fc4p95eaa81ddc6645...
https://fnxx.info/efc869fda6f8284c6ev9658ffee54fd9...
https://fnxx.info/a3cfa19bddb6af44d2qb0772ader45e7...
https://fnxx.info/zdc6808b9yc3ab4513sa8c92037v1c90...
https://fnxx.info/c7134438766b12414dpbdd7ebaad251a...
http://fnxx.info/a79613f9aj6d9a4614292687a1f799dd0...
http://fnxx.info/c57940b0f6b7e3400cpa50e326ad5b098...
http://fnxx.info/c6b2154a16ca154fc4p95eaa81ddc6645...
