Phishing Analysis
Detailed analysis of captured phishing page
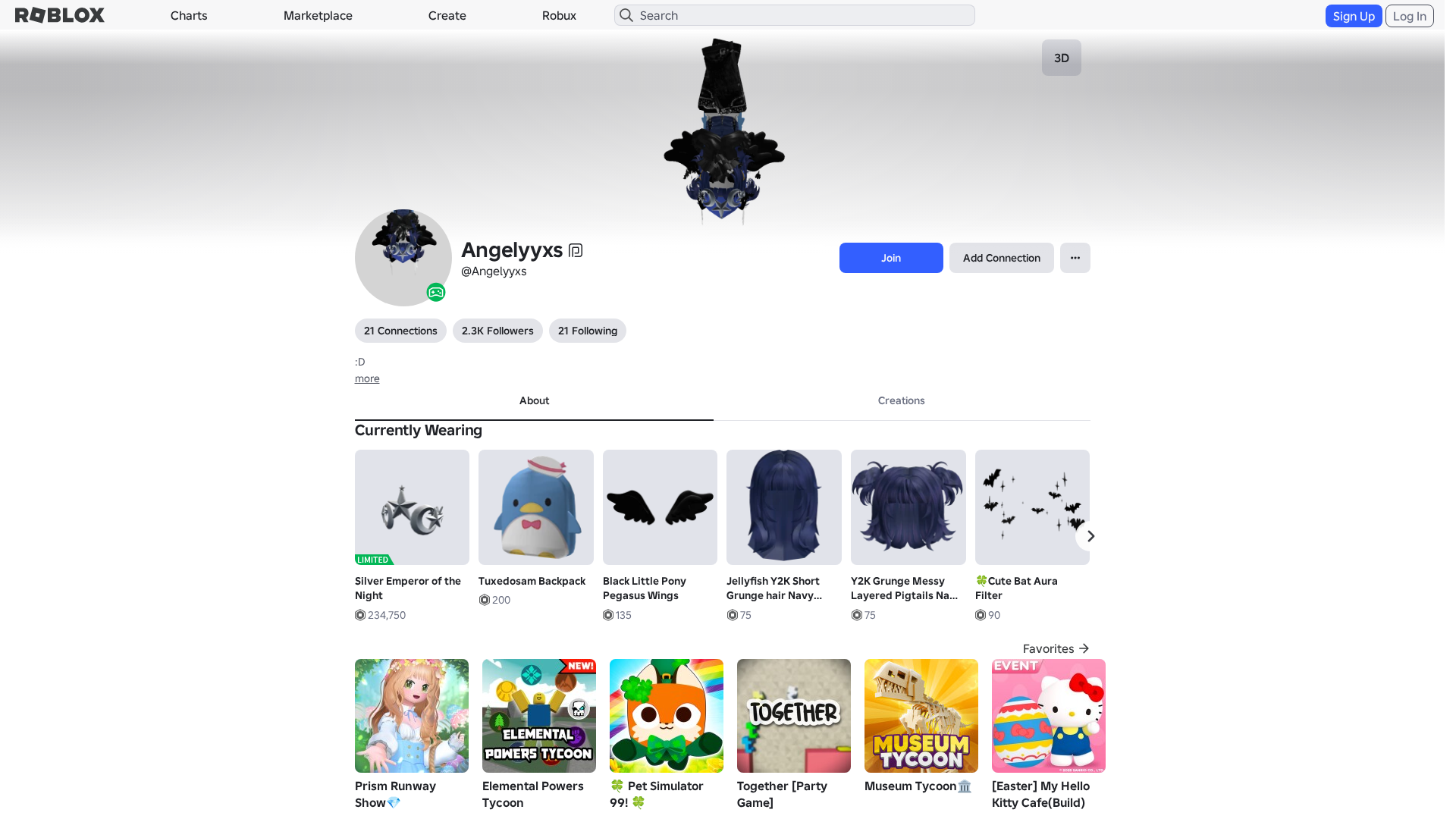
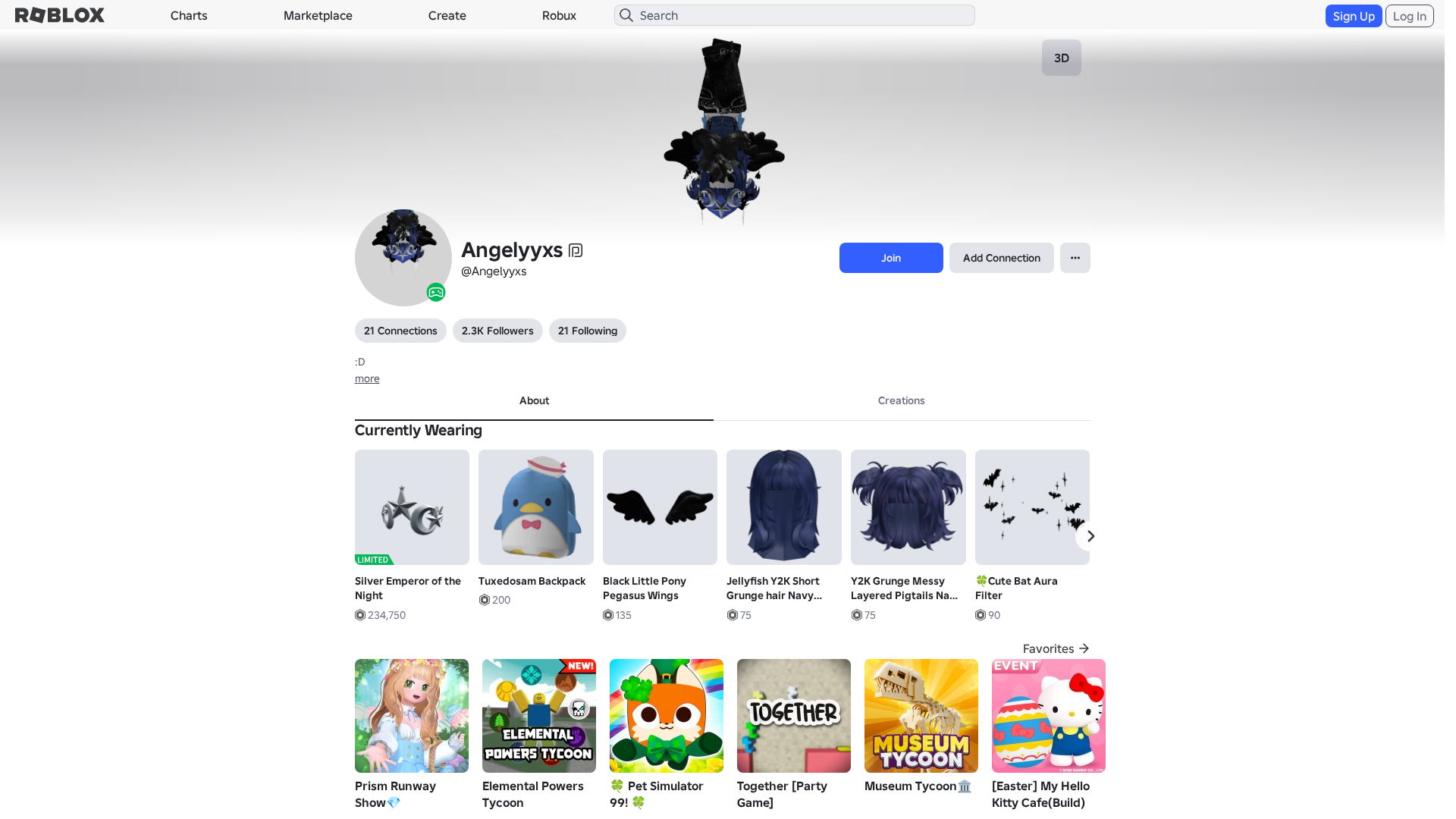
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T183A321729214283761BB79D6B164672EA6D7C70FCA8347E1A2FCD39A0FD6C91E81340D |
|
CONTENT
ssdeep
|
3072:TpXWisZhmwVlSV5PXpFss5a54NcvxaVGLLzRTEHy9902:lXFsZhmwVlSV5PXpFss5a54NcvxaVGLF |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b4165366d999ec2c |
|
VISUAL
aHash
|
0000dfffc3c3c3c3 |
|
VISUAL
dHash
|
e8e8363006061f17 |
|
VISUAL
wHash
|
2000dfffc3c3c3c3 |
|
VISUAL
colorHash
|
07002008000 |
|
VISUAL
cropResistant
|
e8e8363006061f17,8c8d9e8e0f3b1707 |
Code Analysis
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/10875654340/Ruffle-Puffy-Long-Arm-Sleeves-Black
- /login?returnUrl=
- https://api.injuries.lu/catalog/878899787/Silver-Emperor-of-the-Night
- https://api.injuries.lu/catalog/9255011/Silverthorn-Antlers
- https://api.injuries.lu/catalog/619511648/Stylish-Idle
- https://api.injuries.lu/catalog/9434711088/Tuxedosam-Backpack
- https://api.injuries.lu/catalog/1365767/Valkyrie-Helm
- https://api.injuries.lu/catalog/12355106932/Jellyfish-Y2K-Short-Grunge-hair-Navy-Blue
- https://api.injuries.lu/catalog/113919169704818/Vampire-Pose-ORIGINAL
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F248629734179%2Fprofile
- https://api.injuries.lu/catalog/18355868904/Black-Pony-Ears
- https://api.injuries.lu/catalog/86499698/Woman-Right-Arm
- https://api.injuries.lu/catalog/136276875045281/Popular-Run
- https://api.injuries.lu/catalog/7131016975/vampire
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F248629734179%2Fprofile
- https://api.injuries.lu/catalog/619511974/Stylish-Jump
- https://api.injuries.lu/catalog/133304526526319/Popular-Walk
- https://api.injuries.lu/catalog/14455386011/Cute-Bat-Aura-Filter
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/111380056196179/Cute-Chibi-Doll-Head-Dynamic-Head
- https://api.injuries.lu/catalog/12799268782/Y2K-Grunge-Messy-Layered-Pigtails-Navy-Blue
- https://api.injuries.lu/catalog/867827055/8-Bit-Dark-Horns-of-Pwnage
- https://api.injuries.lu/catalog/7241328263/Spiked-Cross-Collar-3-0
- https://api.injuries.lu/catalog/16571270907/Black-Little-Pony-Pegasus-Wings
- https://api.injuries.lu/catalog/86499666/Woman-Torso
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/14618207727/Default-Mood
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/553970961/Green-Queen-of-the-Night
- https://api.injuries.lu/catalog/619509955/Stylish-Climb
- https://api.injuries.lu/catalog/86499716/Woman-Left-Arm
- https://api.injuries.lu/catalog/7892385740/Vampire-COrset-Blue-Y2K-emo-GIRL
- https://api.injuries.lu/catalog/26380828/Sinister-Top-Hat
- https://api.injuries.lu/catalog/619512450/Stylish-Swim
- https://api.injuries.lu/catalog/619511417/Stylish-Fall
📡 API Calls Detected
- https://ro.blox.com/Ebh5?
- GET
- https://apis.
- https://kyxn.dev/api/shorten
- https://kyxn.dev/api/shorten/TKvzwH
- /api/pageview
- get
- https://kyxn.dev${e.endpoint}
- /api/shorten
- POST
- https://help.roblox.com/hc/articles/30428367965460
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 214 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 214 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for www.roblx.me
Found 2 other scans for this domain