
Phishing Analysis
Detailed analysis of captured phishing page
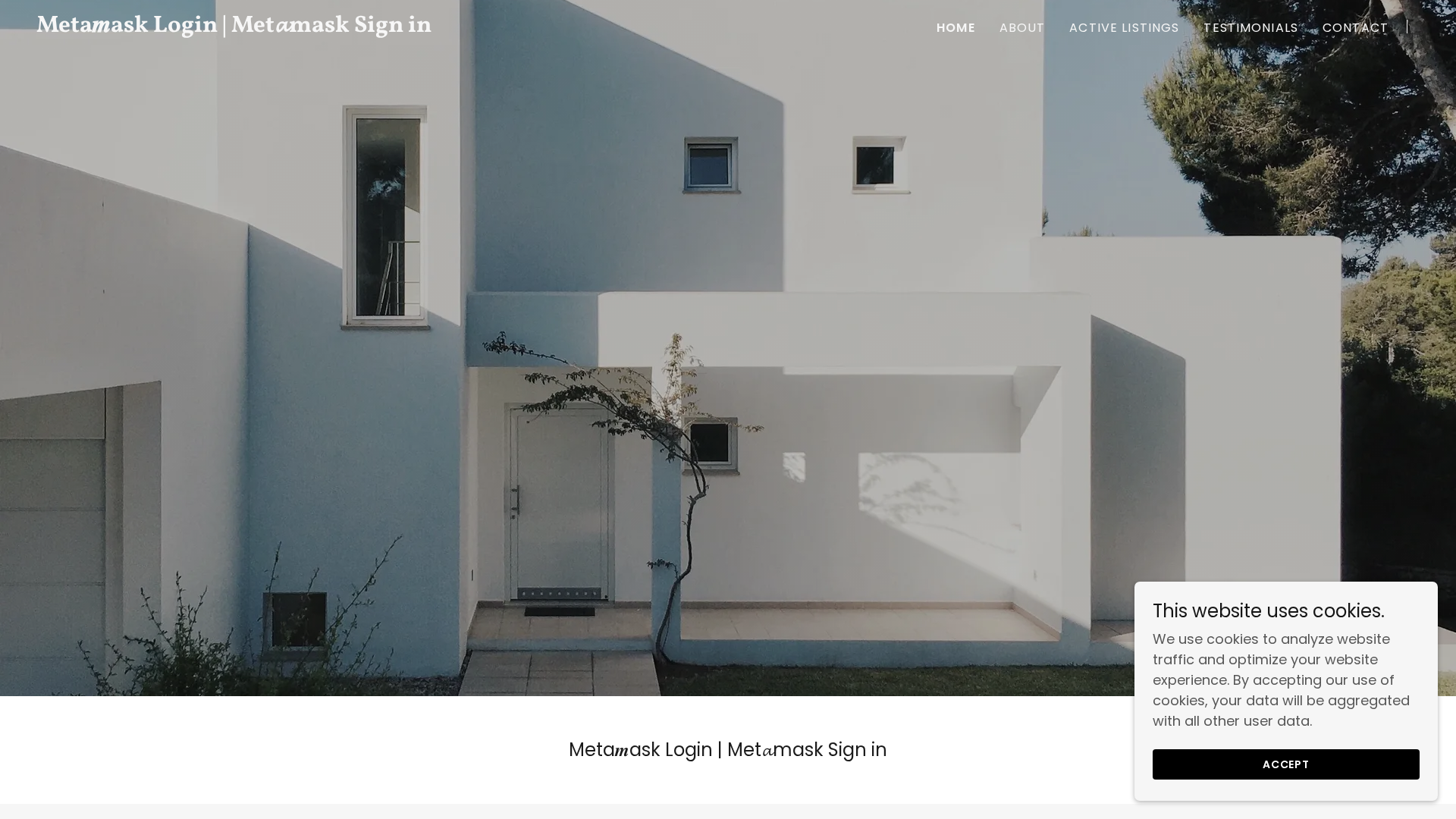
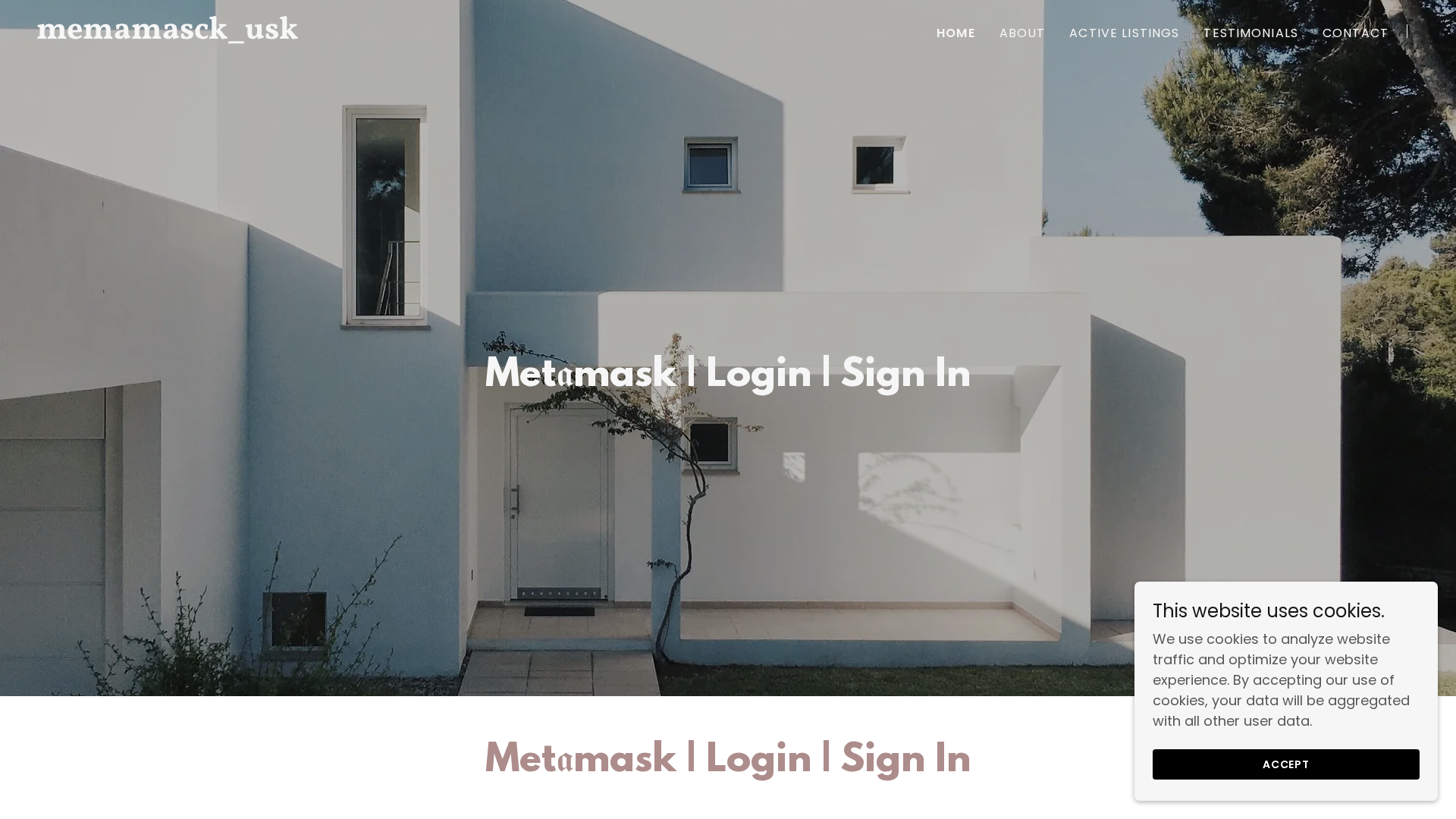
Visual Capture
Detection Info
http://metaimask-wall-llog.godaddysites.com
Detected Brand
MetaMask
Country
International
Confidence
100%
HTTP Status
200
Report ID
2d058d43-52b…
Analyzed
2025-12-24 23:47
Final URL (after redirects)
https://metaimask-wall-llog.godaddysites.com/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T19AD213027108A995C2F345D9A5002590A083FB4ECD7487709ABD1E3B27F7AB577E8B3E |
|
CONTENT
ssdeep
|
384:5Cg8xMdSyoq/UJhvWSFIsjmHhsHglzlJRHPrrpRSCQOelkbFm6G1HUtsrQg1zRZw:s23oq/UJhvWWIsCSAZ1PXvLnTx2065LM |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9550ea35d32dd427 |
|
VISUAL
aHash
|
cccc0e0e060603ff |
|
VISUAL
dHash
|
989cb83a983a6f0d |
|
VISUAL
wHash
|
eccc4e0e0e0e03ff |
Code Analysis
Risk Score
70/100
Threat Level
CRITICAL
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Phishing attempt targeting MetaMask users
• Target: MetaMask users
• Method: Impersonating MetaMask login page to potentially steal credentials or private keys if a form was present on the page and user interacted with it
• Exfil: Unknown, likely to a remote server controlled by the attacker
• Indicators: Free hosting, brand impersonation, domain name not matching the official website
• Risk: HIGH - Potential for credential theft or private key compromise
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Unknown
https://cdn.gosafemode.com/screenshots/73d717512755.png
Apr 03, 2026

MetaMask
https://www.memamasck_usk.godaddysites.com
Mar 16, 2026
Unknown
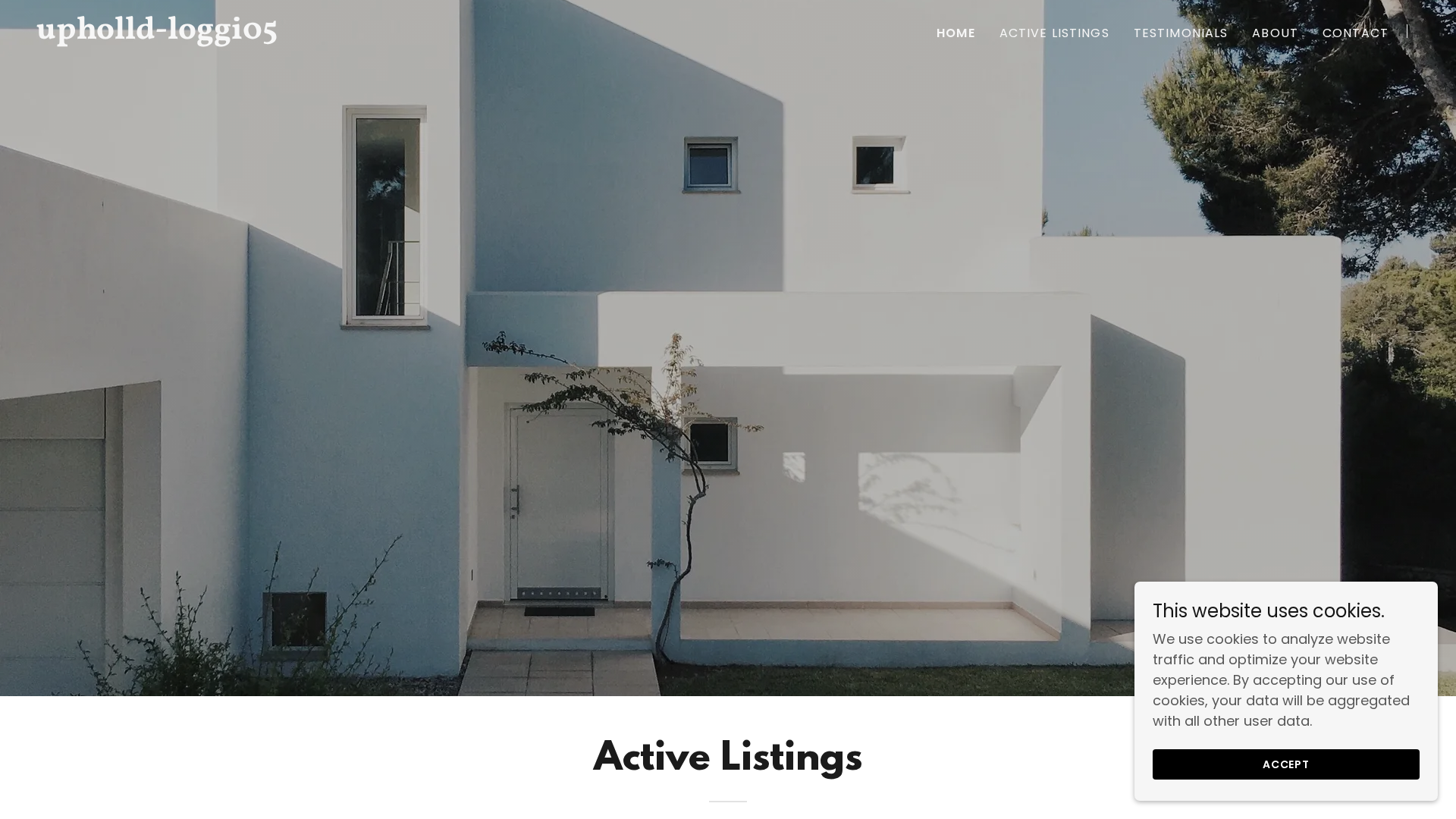
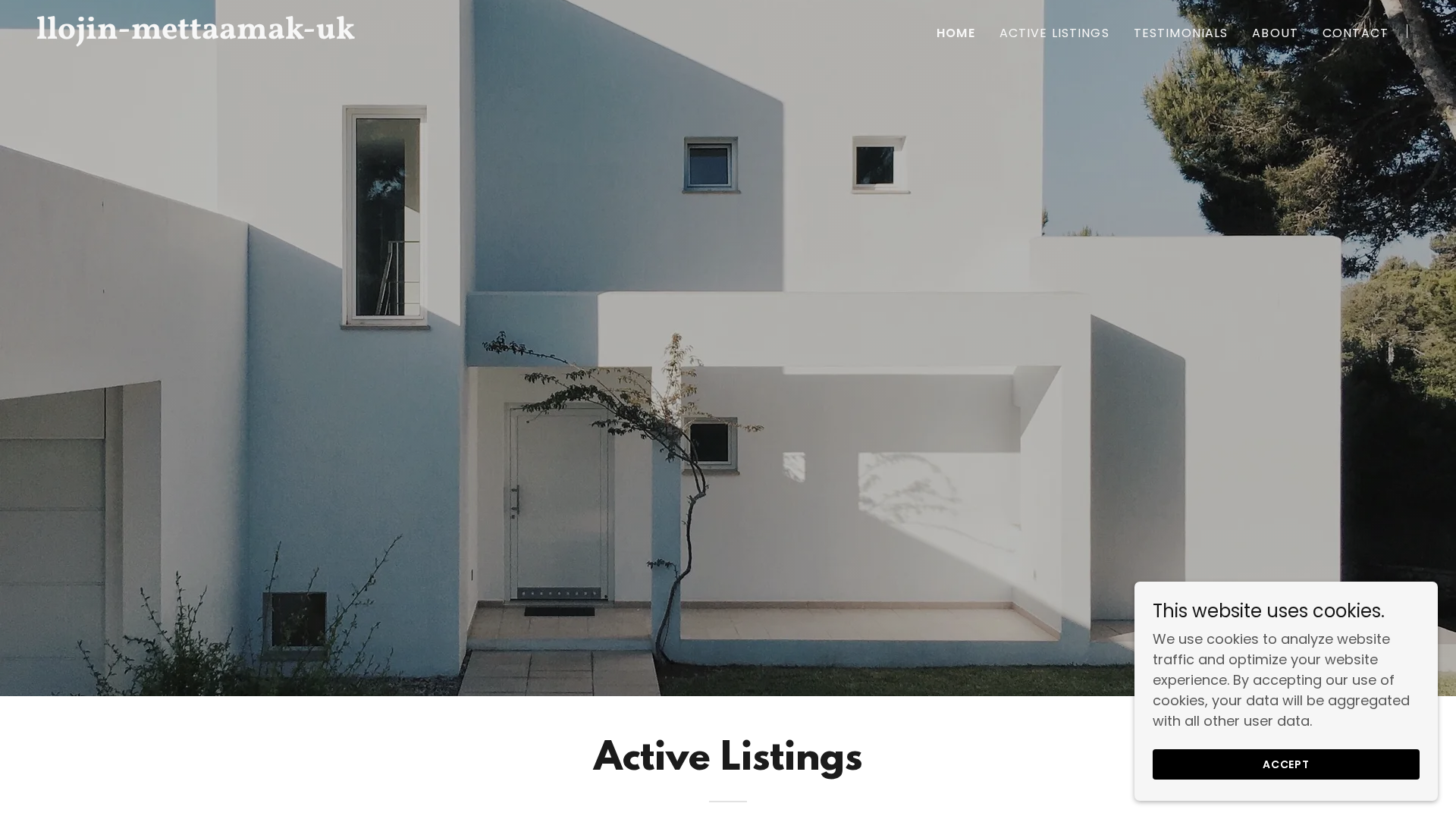
https://www.llojin-mettaamak-uk.godaddysites.com
Mar 15, 2026
MetaMask
https://metaimask-wall-llog.godaddysites.com
Feb 17, 2026
Metamask
https://memamasck_usk.godaddysites.com
Feb 17, 2026
Scan History for metaimask-wall-llog.godaddysites.com
Found 2 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.