
Phishing Analysis
Detailed analysis of captured phishing page
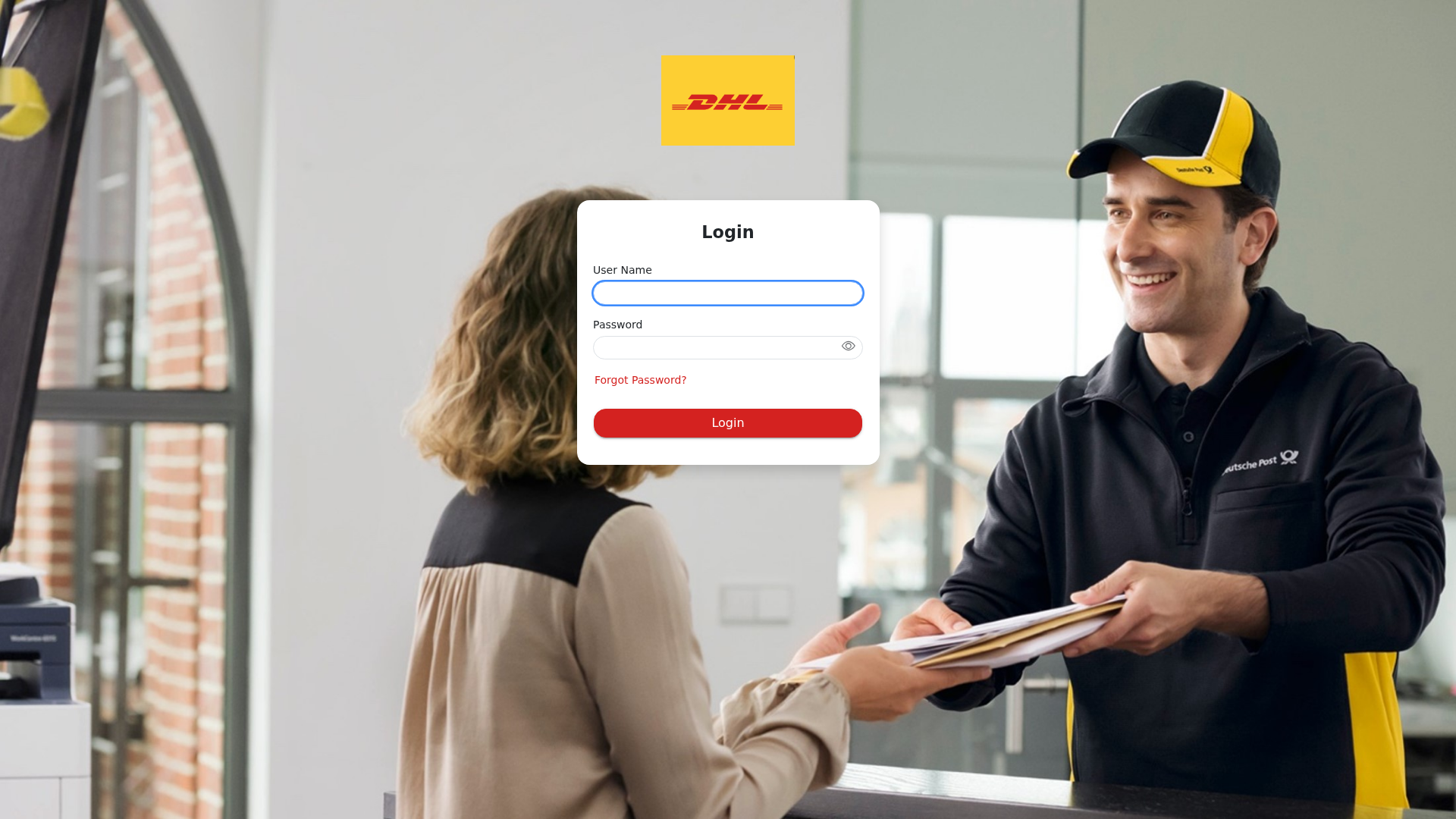
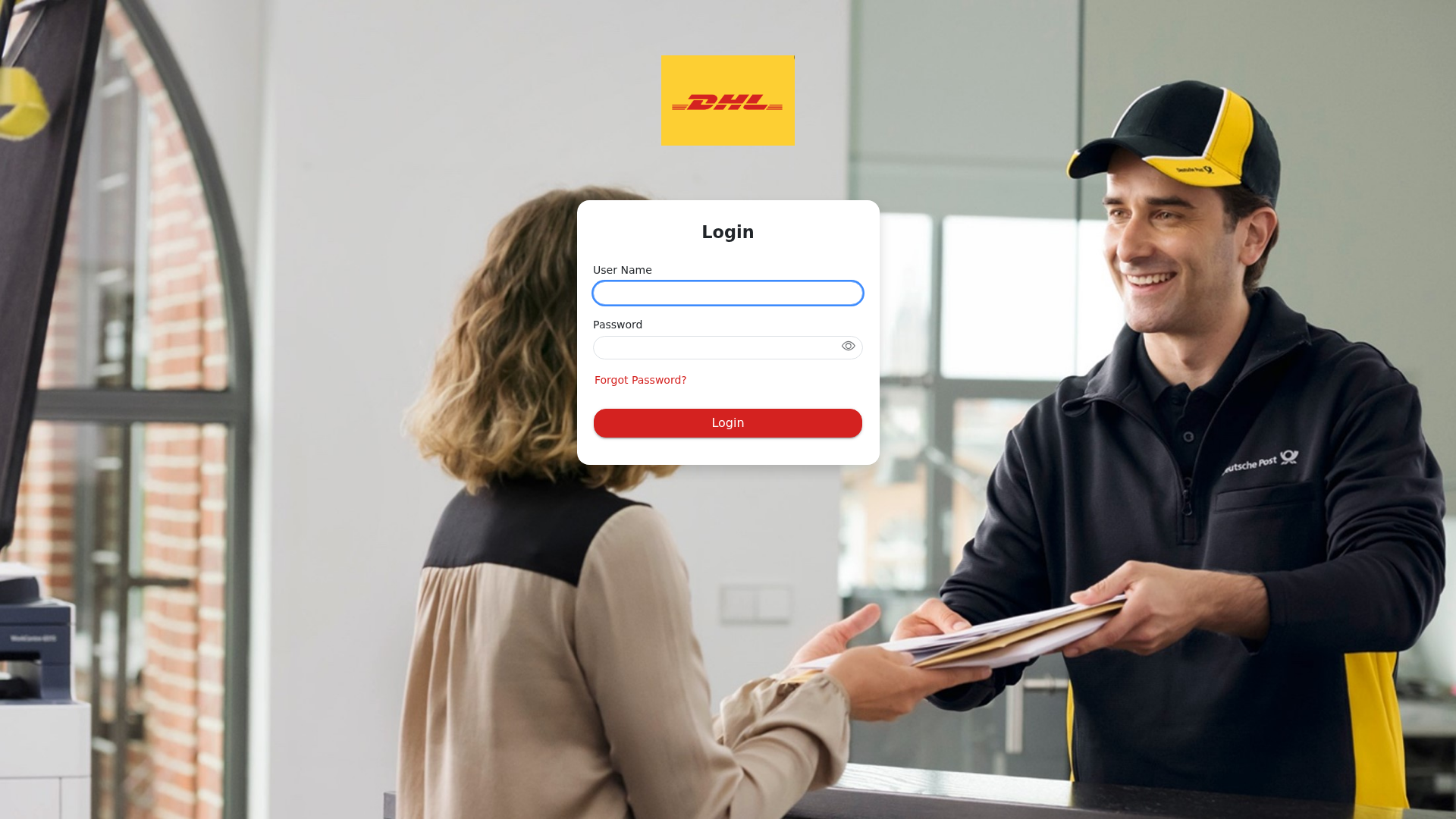
Visual Capture
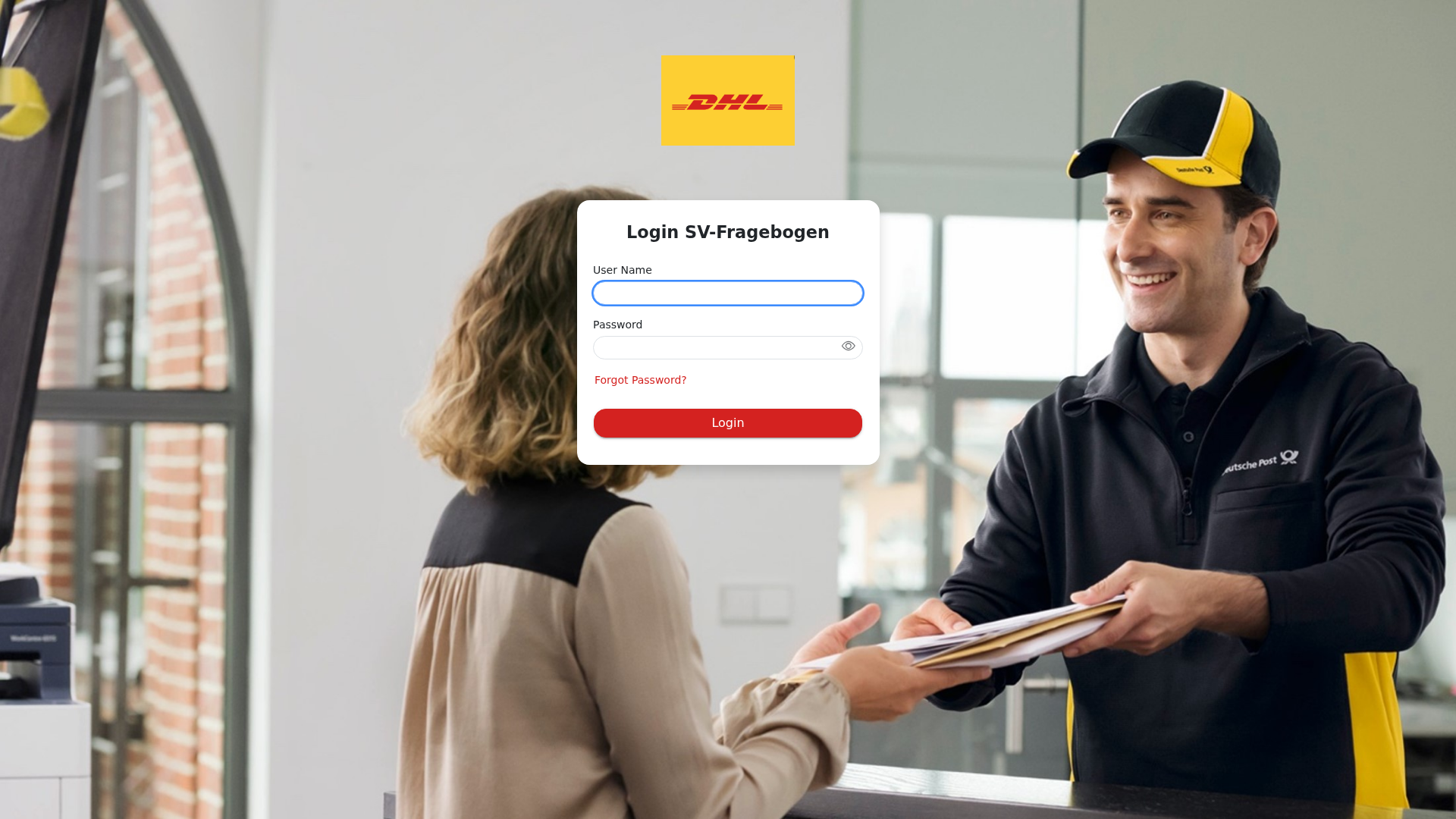
Detection Info
https://dhlsiprod.eu23.smartcommunications.cloud/produce/Account/Login?ReturnUrl=%2Fproduce%2Fwizard%2F83148dc0-31ac-41b5-9f40-219536aaee4b%2F
Detected Brand
DHL
Country
International
Confidence
100%
HTTP Status
200
Report ID
306a412e-d93…
Analyzed
2026-02-04 12:01
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1A641B3A0E0384D7341A386F4B7C4A71A75C5D21FC7961D0192FC9BEC97EFC42AD29958 |
|
CONTENT
ssdeep
|
24:nl8CiQ4tKonEyobcoEDcowgh7BK6jHWAPnpV8o9a5jKTMr+hHc7VD8q04Dr+k1OP:nb4UFyKc3cc1Pn0o9apKTYTJgyii2H5/ |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
d884a64d7e94b569 |
|
VISUAL
aHash
|
7f7d7d5c484868e0 |
|
VISUAL
dHash
|
c1d1919199909199 |
|
VISUAL
wHash
|
7f7d7d5c484848e0 |
|
VISUAL
colorHash
|
0ee00010000 |
|
VISUAL
cropResistant
|
c1d1919199909199,36396cc8c8989a6c,d3e1c1c5013379dd,27a22381899923e3,1b1a1b1f0f8f8703,c3c38f4fe7b57575 |
Code Analysis
Risk Score
68/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🔬 Threat Analysis Report
• Threat: Credential Phishing
• Target: DHL customers
• Method: Impersonation of DHL login page.
• Exfil: Credentials through form submission
• Indicators: Domain mismatch, login form, obfuscation.
• Risk: HIGH
🔒 Obfuscation Detected
- fromCharCode
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Domain Mismatch
The domain does not belong to DHL.
Impersonation of Brand
The website uses DHL's logo and design to impersonate their login page.
Forms requesting sensitive information
The page has a login form asking for credentials.
Obfuscation
Obfuscation detected in javascript.
🔬 Comprehensive Threat Analysis
Threat Type
Two-Factor Authentication Stealer
Target
DHL users (International)
Attack Method
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer
- 4 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
DHL
Official Website
https://www.dhl.com
Fake Service
DHL Login
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker is using a fake login form to steal DHL usernames and passwords. Users are tricked into entering their credentials on a website that looks like the real DHL site.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
dhlsiprod.eu23.smartcommunications.cloud
Registered
2016-09-02
Registrar
None
Status
None
🔬 JavaScript Deep Analysis
Total Code Size
15.1 KB
🔐 Obfuscation Detected
- : None
- : None
- : Light
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
DHL
https://dhlsiprod.eu23.smartcommunications.cloud/
Apr 08, 2026
DHL
https://dhlsiprod.eu23.smartcommunications.cloud/produce/wiz...
Feb 04, 2026
DHL
https://dhlsiprod.eu23.smartcommunications.cloud/produce/wiz...
Jan 15, 2026
DHL
https://dhlsiprod.eu23.smartcommunications.cloud/produce/hom...
Jan 04, 2026
DHL
https://dhlsiprod.eu23.smartcommunications.cloud/produce/Acc...
Jan 04, 2026
Scan History for dhlsiprod.eu23.smartcommunications.cloud
Found 9 other scans for this domain
-
https://dhlsiprod.eu23.smartcommunications.cloud/
https://dhlsiprod.eu23.smartcommunications.cloud/p...
https://dhlsiprod.eu23.smartcommunications.cloud/p...
https://dhlsiprod.eu23.smartcommunications.cloud/p...
https://dhlsiprod.eu23.smartcommunications.cloud/p...
https://dhlsiprod.eu23.smartcommunications.cloud/p...
https://dhlsiprod.eu23.smartcommunications.cloud/p...
https://dhlsiprod.eu23.smartcommunications.cloud/p...
https://dhlsiprod.eu23.smartcommunications.cloud/p...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.