
Phishing Analysis
Detailed analysis of captured phishing page
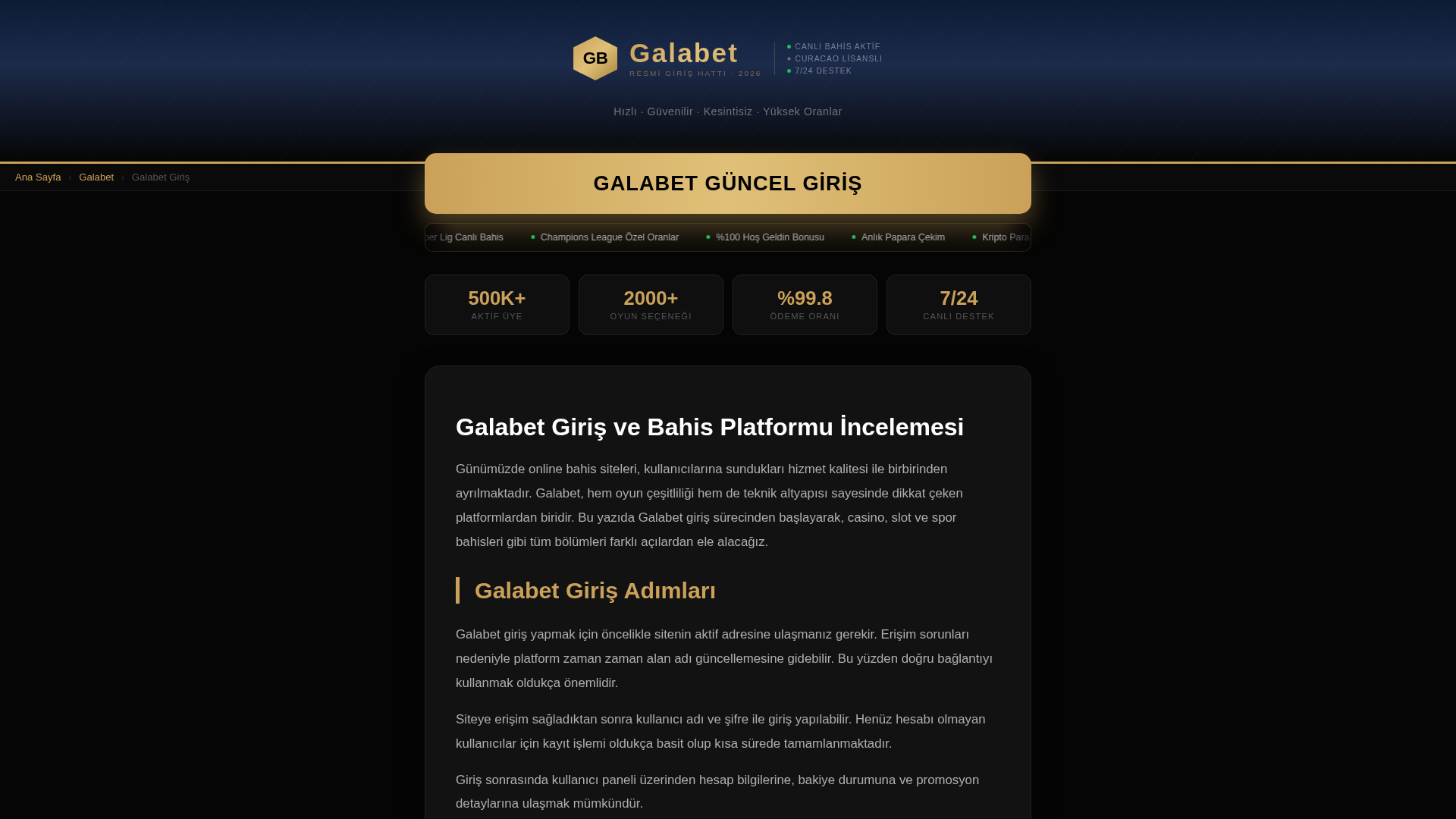
Visual Capture
Detection Info
http://tr.galabet.icu/
Detected Brand
Galabet
Country
Turkey
Confidence
95%
HTTP Status
200
Report ID
30ea0677-364…
Analyzed
2026-04-05 02:33
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T16B52F946A3A7542F037383C6D6C74F35AFF6025AE8126B098ADFC70E17CCD16E192505 |
|
CONTENT
ssdeep
|
192:DlVgz4tL1TSv0aUnS6M8+x9g9/HOFBUeru:DQz4tL11aUnm79g9/HcUn |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
ce9ae4e46534649b |
|
VISUAL
aHash
|
ff3c3c0038181818 |
|
VISUAL
dHash
|
a669696061616161 |
|
VISUAL
wHash
|
fffc3c003c383c38 |
|
VISUAL
colorHash
|
30403000040 |
|
VISUAL
cropResistant
|
f0f0d29696f0f0f0,a669696061616161 |
Code Analysis
Risk Score
53/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 OTP Stealer
🔬 Threat Analysis Report
• Threat: Phishing/Credential Harvesting
• Target: Galabet Users
• Method: Domain squatting and brand impersonation
• Exfil: Unknown
• Indicators: New domain, obfuscated code
• Risk: High
🔒 Obfuscation Detected
- unescape
📡 API Calls Detected
- POST
📊 Risk Score Breakdown
Total Risk Score
85/100
Contributing Factors
Recent Domain
Domain registered 3 days ago.
Suspicious TLD
.icu TLD is frequently used in malicious activity.
Obfuscation
Detected obfuscated JS patterns.
🔬 Comprehensive Threat Analysis
Threat Type
Two-Factor Authentication Stealer
Target
Galabet users (Turkey)
Attack Method
Brand impersonation + obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
MEDIUM - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: OTP Stealer
- 2 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Galabet
Official Website
Unknown
Fake Service
Gambling/Betting
Fraudulent Claims
⚔️ Attack Methodology
Primary Method: Brand Impersonation / Credential Redirection
The site acts as a gateway to redirect users to the latest 'live' domain of a gambling platform, often used to capture traffic or spoof login portals.
Secondary Method: Traffic Monetization
Uses affiliate/referral links to generate revenue while impersonating the target brand.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
tr.galabet.icu
Registered
2026-04-01
Registrar
Unknown
Status
Active
🤖 AI-Extracted Threat Intelligence

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.