
Phishing Analysis
Detailed analysis of captured phishing page
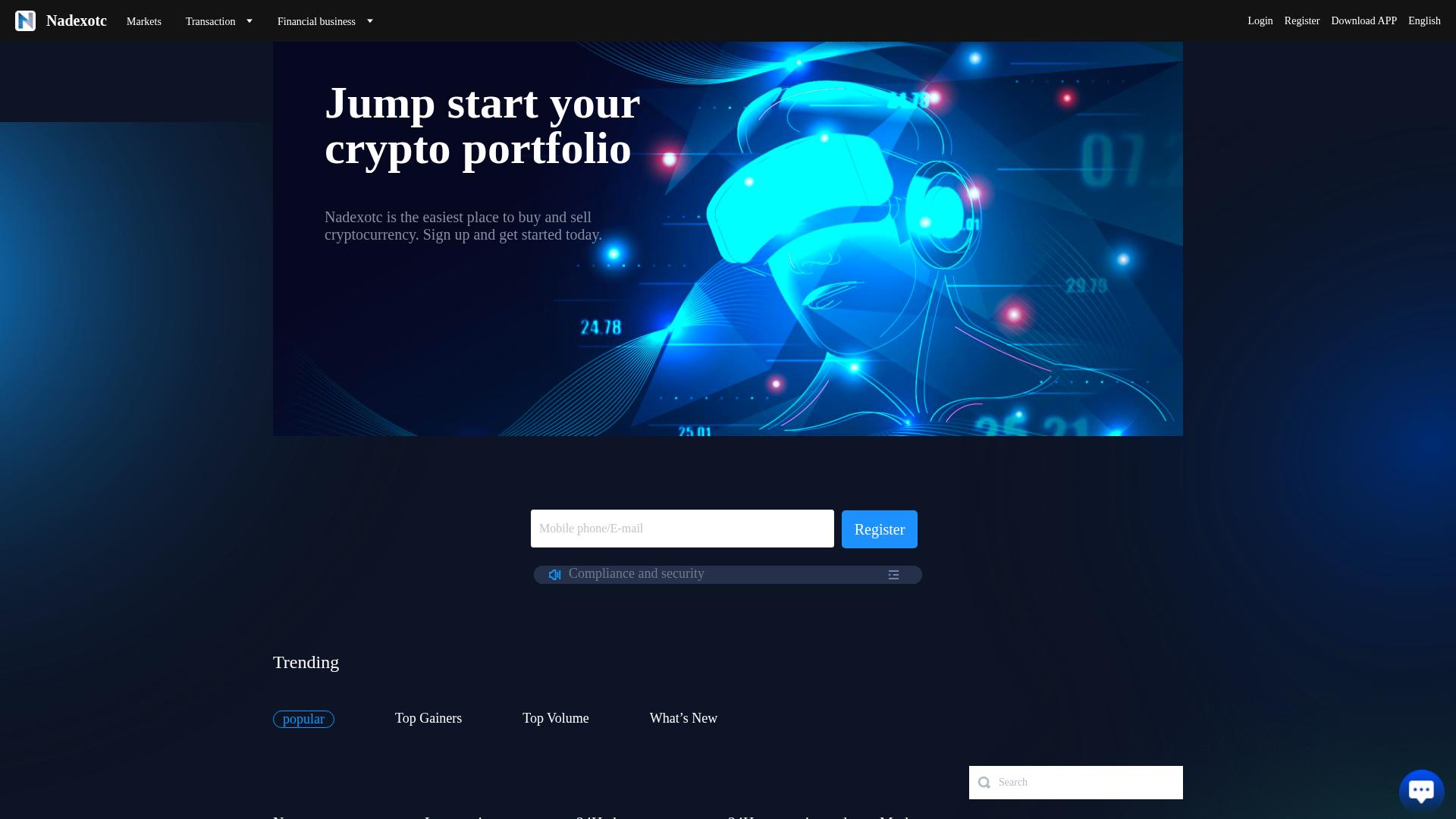
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1B9B2AB30E09010EB11B7DCD2FB707F5AA6D7F30E8939D0114B6D8A9D5FE6EE1A612486 |
|
CONTENT
ssdeep
|
192:aGSPdhwaVvaL9e5TeYoB5IpOK8VlT3hlWVl4nn2sJCrabVCCxUJuzUyc0NhM0vJC:vZ3qIqNms0OdqdYQ1KJY3hKMBQXKY |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9bdb266c26609c79 |
|
VISUAL
aHash
|
083c9c9c18180006 |
|
VISUAL
dHash
|
585838383133cbec |
|
VISUAL
wHash
|
8cbe9e9f9f380007 |
|
VISUAL
colorHash
|
380000001c0 |
|
VISUAL
cropResistant
|
e0d0b1469ee8c462,828292b2b2820082,280080e060c00002,585838383133cbec |
Code Analysis
🔒 Obfuscation Detected
- atob
- eval
- unescape
- document.write
- unicode_escape
- base64_strings
📡 API Calls Detected
- /api/contractOrder!list.action
- api/c2cPaymentMethod!get.action
- api/kyc!get.action
- /api/hobi!getKline.action
- /api/exchangeapplyorder!openview.action
- /api/c2cPaymentMethodConfig!get.action
- /api/exchangeapplyorder!close.action
- /api/user!verifCodeLogin.action
- api/exchangeapplyorder!view.action
- api/c2cPaymentMethodConfig!get.action
- /api/c2cPaymentMethod!method_type.action
- /api/exchangeapplyorder!list.action
- /api/hobi!getRealtime.action
- /api/c2cPaymentMethod!get.action
- api/user!setSafeword.action
- /api/c2cPaymentMethod!list.action
- api/googleauth!get.action
- api/c2cPaymentMethod!update.action
- /api/contractApplyOrder!list.action
- api/withdraw!apply.action
- api/wallet!list.action
- /api/item!list.action
- /api/cms!get.action
- api/user!get_safeword_apply.action
- api/channelBlockchain!getBlockchainName.action
- post
- /api/c2cPaymentMethod!getAdPayments.action
- /api/c2cOrder!order_pass.action
- api/user!updatepsw.action
- /api/c2cAdvert!list.action
- /api/c2cOrder!open.action
- api/withdraw!fee.action
- /api/user!resetpswByGoogle.action
- api/googleauth!bind.action
- api/exchangeapplyorder!list.action
- api/wallet!records.action
- /api/c2cOrder!open_quick_apply.action
- /api/assets!getAll.action
- api/kycHighLevel!apply.action
- api/cms!list.action
- /api/contractApplyOrder!closeview.action
- /api/c2cOrder!pay_finish.action
- /api/c2cOrder!order_open.action
- api/rechargeBlockchain!list.action
- api/kyc!apply.action
- api/minerOrder!list.action
- api/exchangeapplyorder!buy_and_sell.action
- api/item!list.action
- /api/exchangerateuserconfig!userSetRate.action
- api/localuser!save_phone.action
- /api/wallet!getAll.action
- api/c2cPaymentMethodConfig!list.action
- api/miner!list.action
- api/user!resetpsw.action
- /api/otcOnlinechat!send.action
- api/contractOrder!list.action
- /api/c2cAdvert!get.action
- api/moneylog!list.action
- api/kycHighLevel!get.action
- api/financeOrder!get.action
- /api/itemUserOptional!delete.action
- api/localuser!register_username.action
- api/assets!getAll.action
- /api/user!login.action
- api/exchangeapplyorder!buy_and_sell_fee.action
- /api/user!googleLogin.action
- api/minerOrder!get.action
- /api/contractApplyOrder!open.action
- api/syspara!getSyspara.action
- /api/contractApplyOrder!openview.action
- /api/futuresOrder!open.action
- /api/contractOrder!closeAll.action
- api/localuser!getShare.action
- /api/c2cOrder!list.action
- api/localuser!registerNoVerifcode.action
- /api/contractOrder!close.action
- api/finance!list.action
- api/localuser!save_email.action
- api/wallet!getAll.action
- /api/syspara!getSyspara.action
- /api/c2cOrder!get.action
- /api/contractApplyOrder!cancelAll.action
- /api/exchangeapplyorder!cancel.action
- /api/c2cOrder!get_best_price_advert.action
- /api/localuser!register.action
- /api/c2cUser!get.action
- api/newOnlinechat!list.action
- api/rechargeBlockchain!recharge.action
- api/user!logout.action
- /api/contractApplyOrder!close.action
- api/withdraw!withdraw_open.action
- /api/c2cAppeal!apply.action
- api/user!getUserNameVerifTarget.action
- /api/otcOnlinechat!list.action
- api/minerOrder!closOrder.action
- /api/exchangeapplyorder!buy_and_sell_fee.action
- api/news!list.action
- api/promote!getPromoteData.action
- /api/exchangeapplyorder!closeview.action
- /api/exchangerate!list.action
- api/c2cPaymentMethod!delete.action
- api/localuser!getImageCode.action
- api/financeOrder!closOrder.action
- /api/localuser!get.action
- /api/contractApplyOrder!cancel.action
- /api/itemUserOptional!list.action
- api/financeOrder!list.action
- api/minerOrder!listSum.action
- api/promote!getPromote.action
- api/withdraw!limit.action
- /api/user!setSafewordReg.action
- /api/exchangeapplyorder!open.action
- /api/idcode!execute.action
- api/user!getVerifTarget.action
- api/withdraw!list.action
- api/financeOrder!listSum.action
- api/c2cPaymentMethod!list.action
- /api/rechargeBlockchain!recharge_open.action
- /api/exchangerateuserconfig!get.action
- api/futuresOrder!list.action
- api/localuser!get.action
- /api/c2cUser!getUserCenter.action
- /api/futuresOrder!openview.action
- /api/futuresOrder!get.action
- api/hobi!getRealtime.action
- /api/itemUserOptional!add.action
- api/c2cPaymentMethod!add.action
- /api/futuresOrder!list.action
- api/newOnlinechat!send.action
- /api/c2cAdvert!symbol.action
- api/user!set_safeword_apply.action
- /api/c2cOrder!order_cancel.action
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 27 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 27 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
