Phishing Analysis
Detailed analysis of captured phishing page
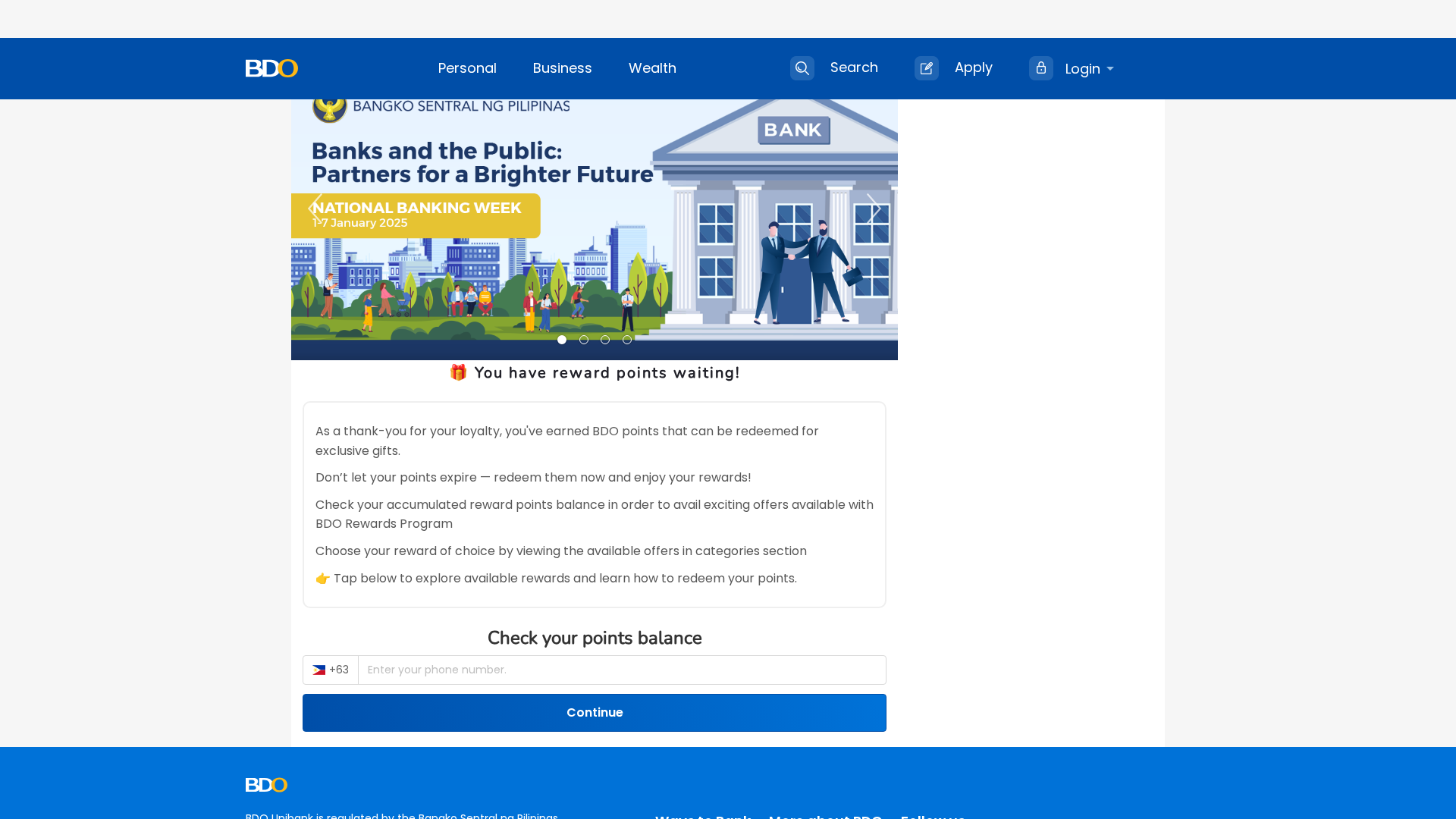
Visual Capture

Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T18FB27379A480223F325352C99A30FF05A3D3A78DCA065995E3FA435D7FD6D88DC0AB25 |
|
CONTENT
ssdeep
|
384:XesL9sRsSs9sDs8scLNmOq5ePnGS3b+K+KWKYnNPP:Xes6RZZPnGFXVVX |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b63647c949b84ce6 |
|
VISUAL
aHash
|
00c7c7c7ffffff00 |
|
VISUAL
dHash
|
a82c2c3ce8d81c2c |
|
VISUAL
wHash
|
00878787ffff8700 |
|
VISUAL
colorHash
|
06000000180 |
|
VISUAL
cropResistant
|
0000000000000000,2c2c3c1ce83cd82c,804498a8ac1a502c,394d2d2dad2c31c8,fffffff3f3f7ffff,00000090904024c8 |
Code Analysis
🔒 Obfuscation Detected
- fromCharCode
- unescape
- base64_strings
🎯 Kit Endpoints
- https://www.bdo.com.ph/business/business-solutions/cash-management/business-login
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 5 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 5 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)