
Phishing Analysis
Detailed analysis of captured phishing page
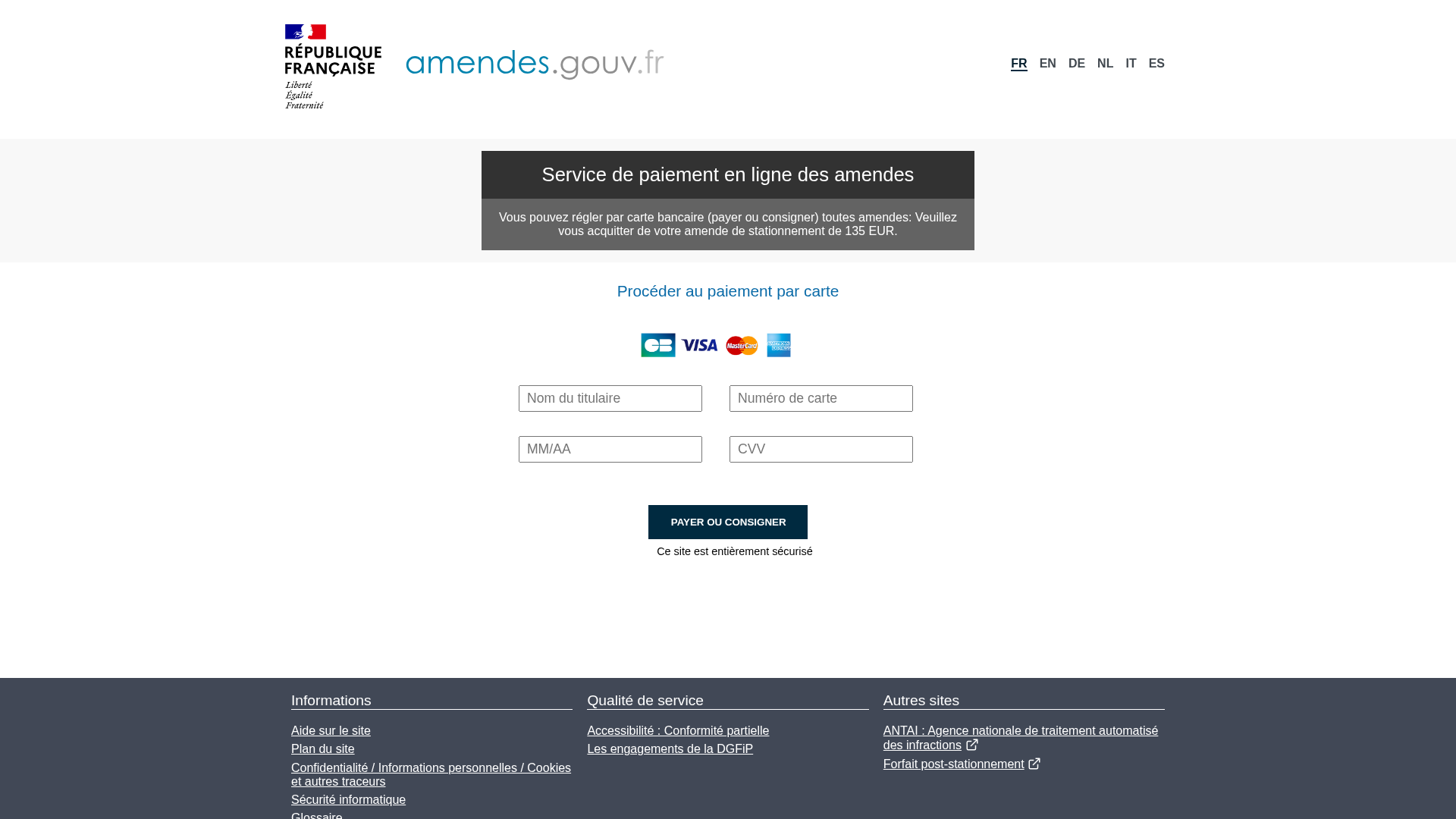
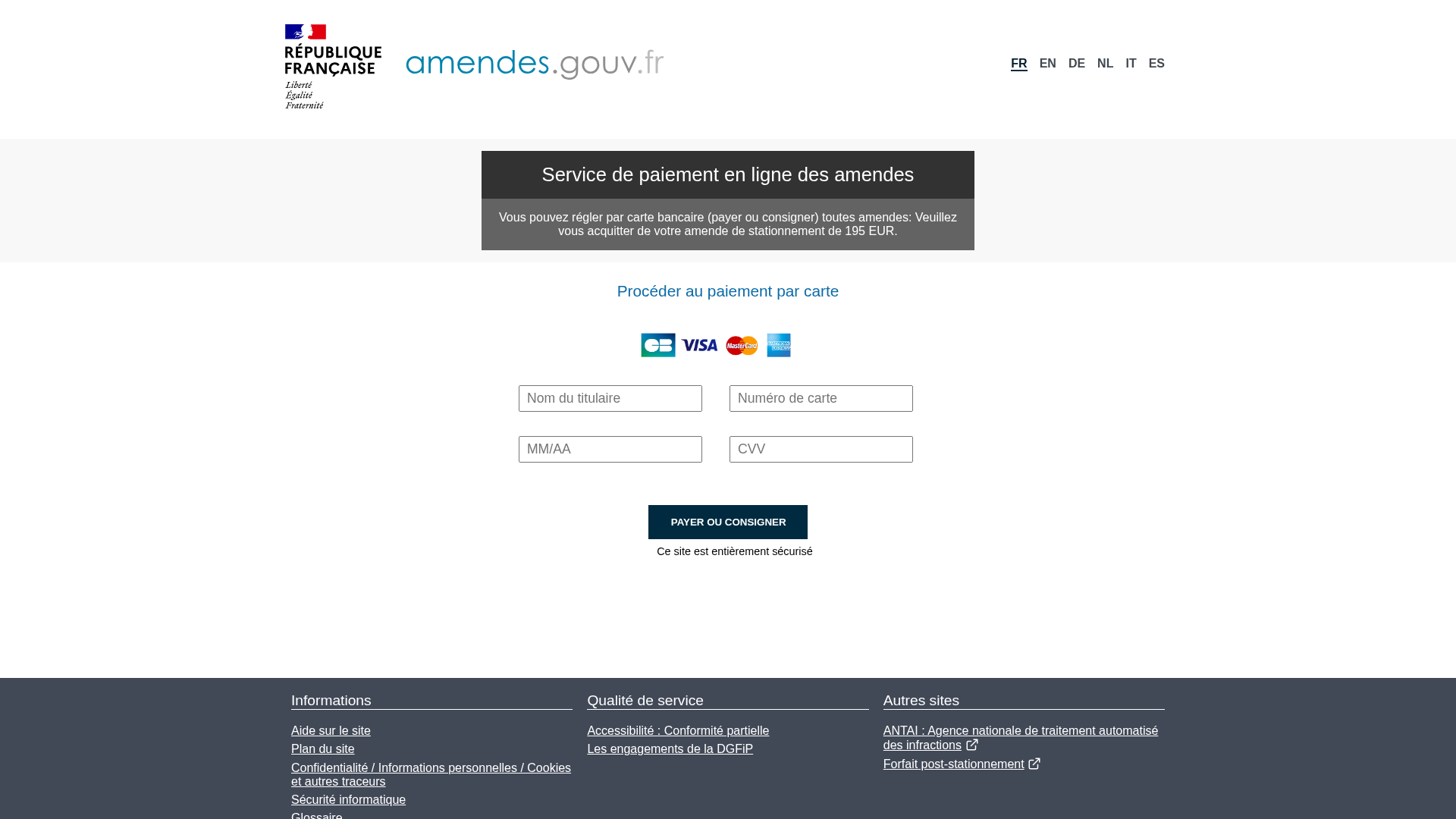
Visual Capture

Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T18AE164726158383B027792CDBE52FF29C4A7C12FCA4E2C0196EC9B5D1ED5EA0E94425B |
|
CONTENT
ssdeep
|
96:IZfYIkzIoN5W4QkQC7JXntEGvEhW8jxYrZizaYO+0ETia5K2nDRA1Uebmw0g9If:MAI8IAbZl8e9f+0ETLzeawRY |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b2b51c9e1b9cc334 |
|
VISUAL
aHash
|
ffc3e7ffffff0000 |
|
VISUAL
dHash
|
238e8e000c08b0c8 |
|
VISUAL
wHash
|
9f83c3e7efe70000 |
|
VISUAL
colorHash
|
07000000180 |
|
VISUAL
cropResistant
|
230e8e0c140c0c10,13eae81380aed8d0,a0e0f4b4c9c9d2d0 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: French citizens (Amendes)
• Method: Impersonation and form-based data theft
• Exfil: infoz/infos.php (form action suggests data exfiltration)
• Indicators: Mismatched domain, obfuscated Javascript, requests for PII.
• Risk: HIGH
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- fromCharCode
- unescape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://services-publics.grupozasacr.com/infospage.php
📤 Form Action Targets
- infoz/infos.php
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 64 obfuscation techniques
🏢 Brand Impersonation Analysis
Fraudulent Claims
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attackers are using a form to collect user's credentials (name, DOB, email) to potentially use them to log into different services, or for identity theft.
Secondary Method: Potential Malware Injection
The site uses obfuscated javascript. This is often used to either inject a malicious script or to attempt credential theft.
🌐 Infrastructure Indicators of Compromise
🦠 Malicious Files
Functions: sendData, submitForm
📊 Attack Flow Diagram
User fills <input name=username> → sendData() → fetch('https://services-publics.grupozasacr.com/infospage.php') → credentials sent
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : None
- : None
- : Moderate
- : Moderate
- : Heavy
- : Heavy
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
User fills <input name=username> → sendData() → fetch('https://services-publics.grupozasacr.com/infospage.php') → credentials sent
🎯 Malicious Files Identified
main-es2017.8d2eb497bdf1e092bf40.jsMalicious Functions
sendDatasubmitForm
Similar Websites
Pages with identical visual appearance (based on perceptual hash)


Scan History for services-publics.grupozasacr.com
Found 5 other scans for this domain
