Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
No screenshot available
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1D323D872A1245833617FA3D9F519B70191D3E70ECA825BE2A1F8E37609CAC71FD1341A |
|
CONTENT
ssdeep
|
1536:GxNXB1pyLxAiDTpDjM2zXMTSW5B39NTxJ8m8:+NXBbm12N2 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b03030cfcfcd654d |
|
VISUAL
aHash
|
c7c7c3cfffffffff |
|
VISUAL
dHash
|
8e0f8e1e12183018 |
|
VISUAL
wHash
|
008383c3c3cfdfc7 |
|
VISUAL
colorHash
|
07001080041 |
|
VISUAL
cropResistant
|
8e0f8e1e12183018,6b17aaead49496ea,62f0f0cccce8f035 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Impersonation
• Target: Roblox users
• Method: Malicious domain mimicking Roblox content.
• Exfil: Unknown
• Indicators: Suspicious TLD, impersonates brand.
• Risk: Moderate
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://www.roblox.com.ml/info/blog?locale=en_us
- /catalog
- https://www.roblox.com.ml/catalog?CatalogContext=1&Keyword=
- https://www.roblox.com.ml/api/exfiltrate
- /login?returnUrl=9738936600469449
📡 API Calls Detected
- https://apis.
- GET
- https://ro.blox.com/Ebh5?pid=experiencestart_mobileweb&is_retargeting=false&af_dp=
- POST
- get
- https://en.help.roblox.com/hc/articles/7997207259156
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 252 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Impersonation
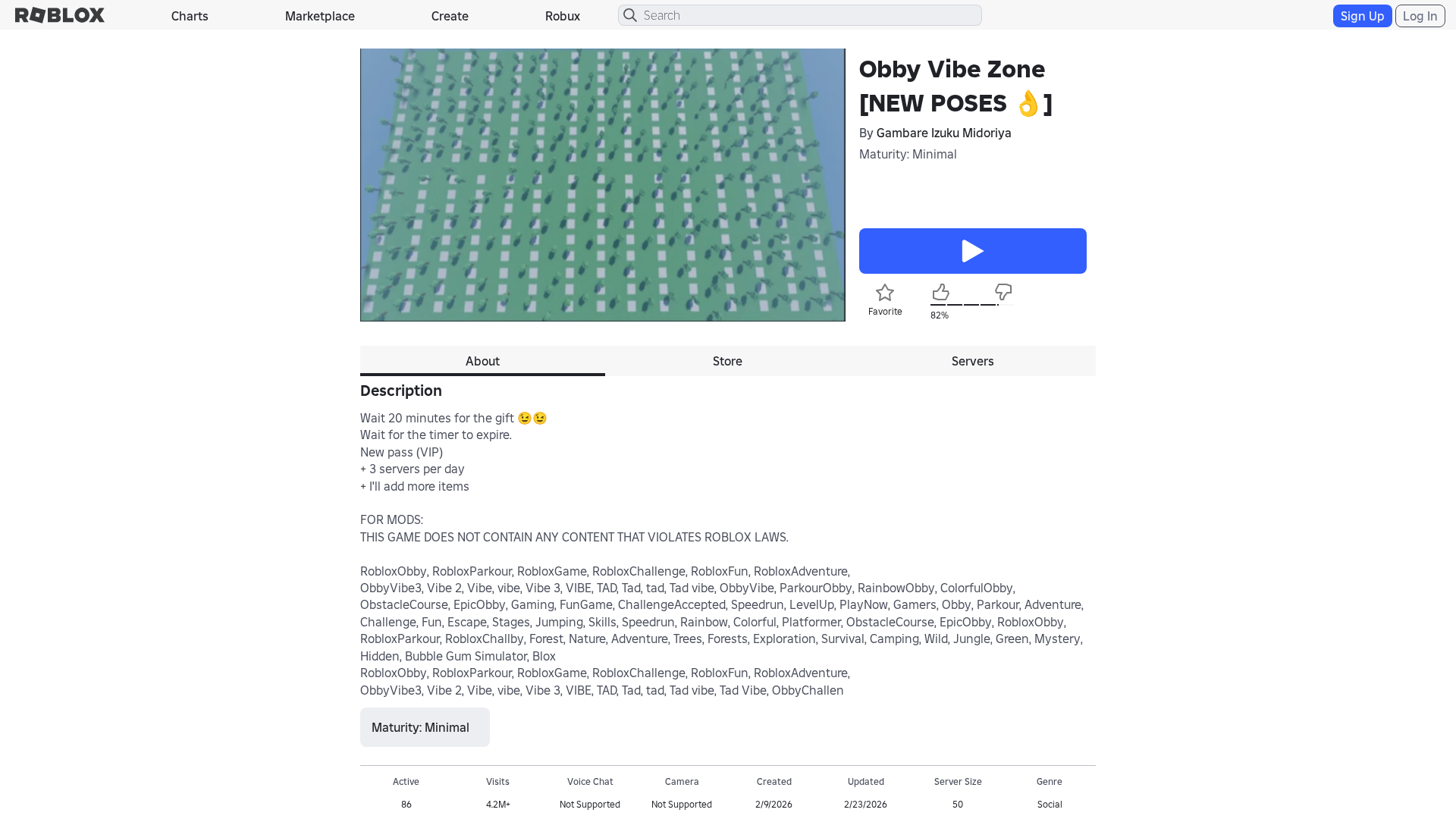
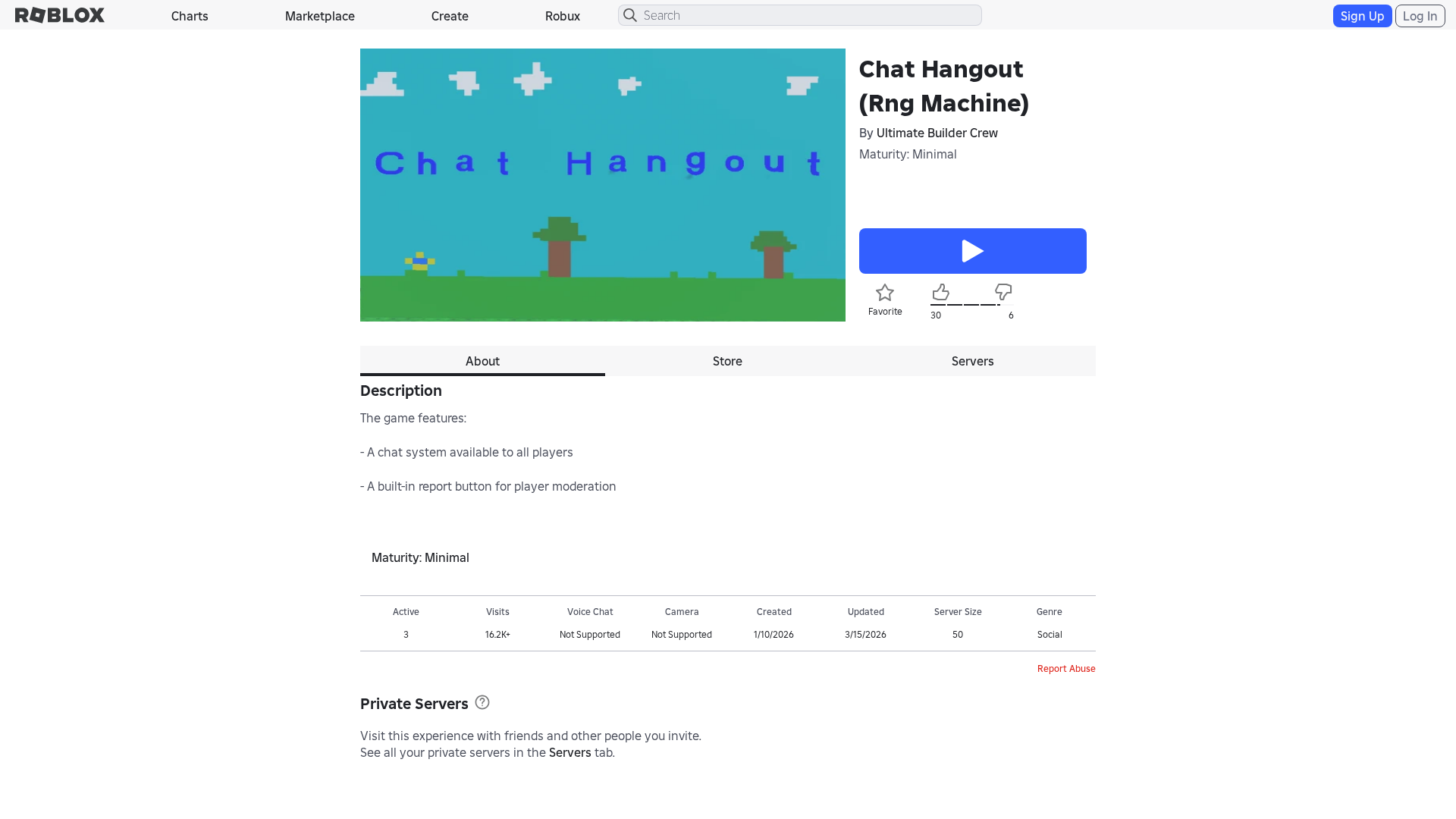
The attacker is trying to impersonate a legitimate Roblox game page to either trick users to enter credentials to take over Roblox user accounts or potentially host malware on the site.
Secondary Method: JavaScript Obfuscation
The JavaScript code on the page is obfuscated using methods such as 'atob', 'eval' and 'fromCharCode', to hide the malicious intentions.
🌐 Infrastructure Indicators of Compromise
🦠 Malicious Files
Functions: trackReturns, fetch
📊 Attack Flow Diagram
User fills <input name='username'> → trackReturns() → fetch('https://www.roblox.com.ml/api/exfiltrate') → credentials sent to endpoint
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Light
- : None
- : Light
- : Heavy
- : None
- : None
- : Light
- : None
- : None
- : Light
- : Light
- : Light
- : None
- : Light
- : None
- : Heavy
- : None
- : Heavy
- : Heavy
- : Light
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
User fills <input name='username'> → trackReturns() → fetch('https://www.roblox.com.ml/api/exfiltrate') → credentials sent to endpoint
🎯 Malicious Files Identified
bundleVerifier.jsMalicious Functions
trackReturnsfetch
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for www.roblox.com.ml
Found 10 other scans for this domain
-
https://www.roblox.com.ml/games/123573053194279/EV...
https://www.roblox.com.ml/users/4359662752/profile
https://www.roblox.com.ml/games/102438880728881/Te...
https://www.roblox.com.ml/games/920587237/Adopt-Me...
https://www.roblox.com.ml/games/83789872591767/Swo...
https://www.roblox.com.ml/communities/7111087128/R...
http://www.roblox.com.ml/communities/8359925132/FA...
https://www.roblox.com.ml/users/8640321039/profile
https://www.roblox.com.ml/users/5222656123/profile
https://www.roblox.com.ml/users/23215749/profile