
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
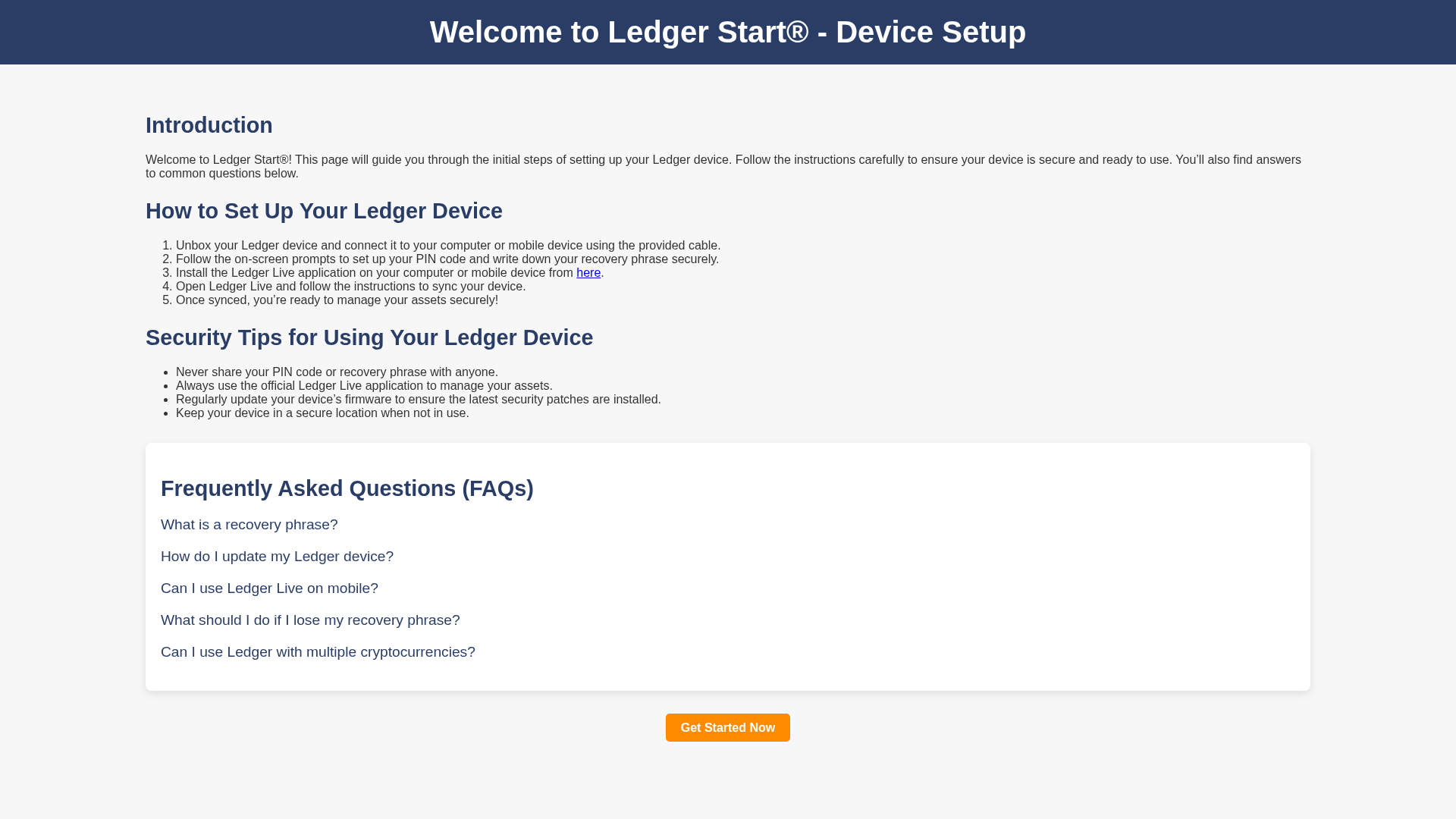
Detection Info
https://lexger-com-start.pages.dev/
Detected Brand
Ledger
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
378c88c9-304…
Analyzed
2026-04-08 19:28
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1DB612357A481F22201CB13E6BAA6938BF3118049D92723926DF5832D3FE1F86CE175D9 |
|
CONTENT
ssdeep
|
48:TjCCtnZ2w7YWpgAU8Z7ME9ojnfH+hQ9QWEIK6Zd47URcm:TjCCtnZ2wRqALME93WtbH |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9f1f43474a1e1d52 |
|
VISUAL
aHash
|
00ff9f9fffffffff |
|
VISUAL
dHash
|
697738343060688d |
|
VISUAL
wHash
|
00010f0f1f3f9fe7 |
|
VISUAL
colorHash
|
07007000000 |
|
VISUAL
cropResistant
|
4179383078602849,082c506969611648 |
Code Analysis
Threat Level
ALTO
⚠️ Phishing Confirmed
📊 Risk Score Breakdown
Total Risk Score
40/100
🔬 Comprehensive Threat Analysis
Threat Type
Ledger Phishing Landing Page
Target
Ledger users
Attack Method
Phishing webpage
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
LOW - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
🏢 Brand Impersonation Analysis
Impersonated Brand
Ledger
Official Website
N/A
Fake Service
Credential harvesting service
⚔️ Attack Methodology
Primary Method: SEO Poisoning Landing Page
Fake Ledger page designed to appear in search results and trick users into visiting. May redirect to credential harvesting pages, malware downloads, or serve as a trust-building step before requesting sensitive information.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
lexger-com-start.pages.dev
Registered
Unknown
Registrar
Unknown
Status
Hosting platform (subdomain)
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.