
Phishing Analysis
Detailed analysis of captured phishing page
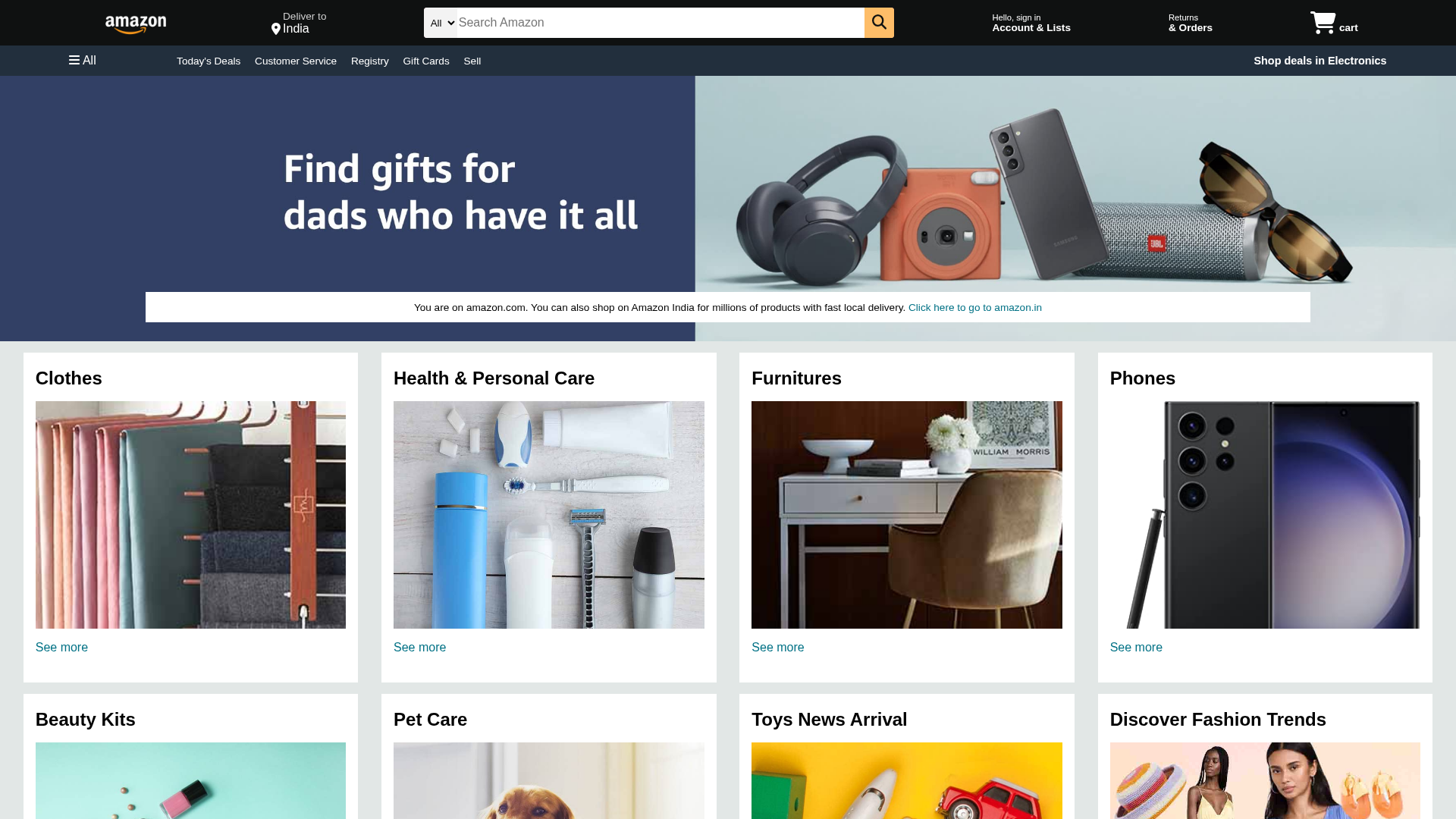
Visual Capture
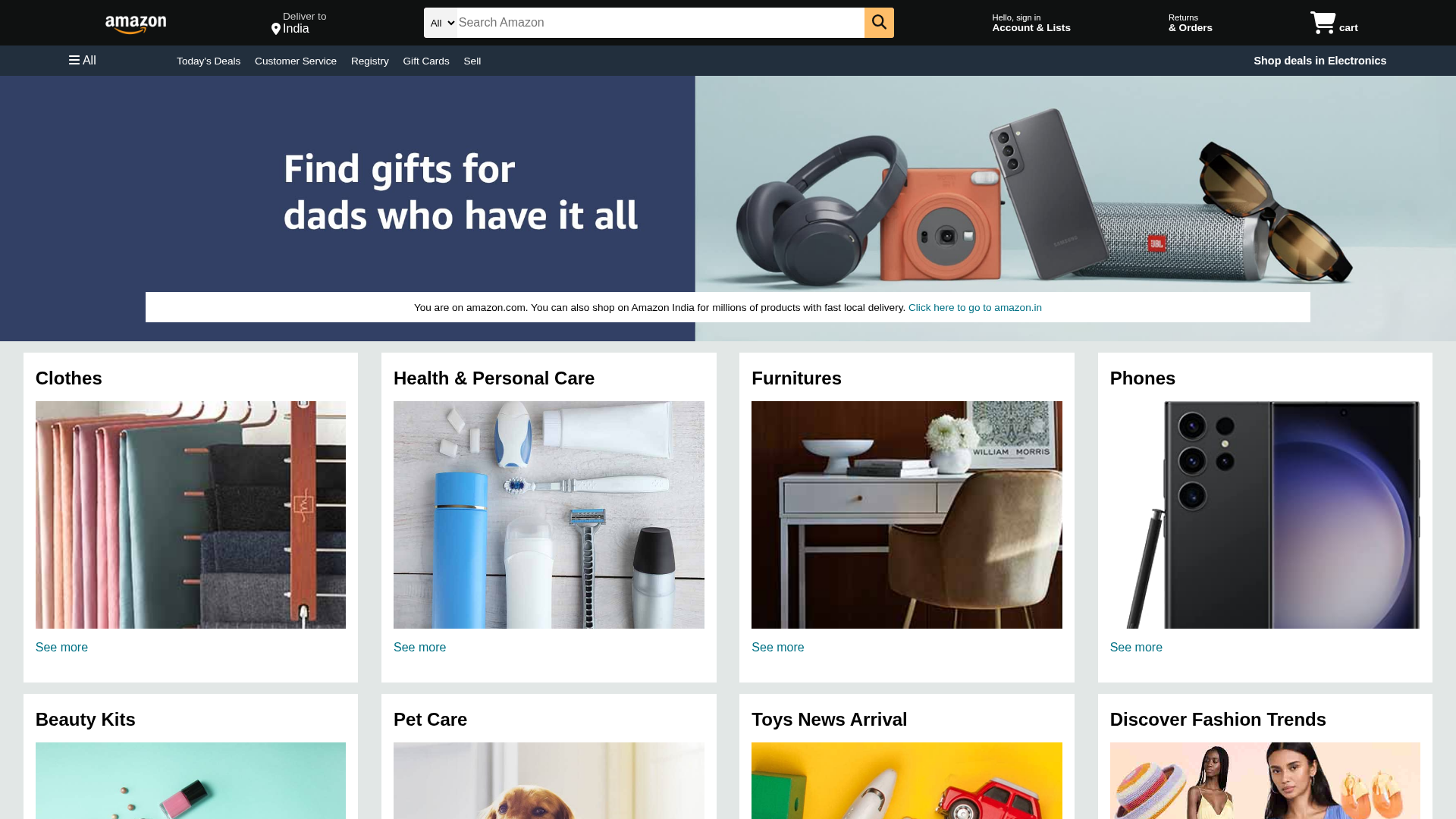
Detection Info
https://www.amazon-clone-amber-five.vercel.app/
Detected Brand
Amazon
Country
International
Confidence
95%
HTTP Status
200
Report ID
3842d551-f5f…
Analyzed
2026-03-02 14:48
Final URL (after redirects)
https://amazon-clone-amber-five.vercel.app/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1DD91BB705482BE3301D7C3E2EF39A79FB2D486A5EA83570517F5C34C8ACAE5AED21950 |
|
CONTENT
ssdeep
|
96:naTJJoljDNnv/NUmyRmeNbbA3N0KF/Ddhrk11tB2K1:aFJo75b/Ddhrk7tAK1 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
8e19394edcc94e4e |
|
VISUAL
aHash
|
000301ffb430ffff |
|
VISUAL
dHash
|
72dbdd9464656565 |
|
VISUAL
wHash
|
000301ff30b0ffff |
|
VISUAL
colorHash
|
07207000000 |
|
VISUAL
cropResistant
|
8282e2eaeae28282,dbdf9be46565a565,62db1adbdbef9dde,d9e6766663697926,4c9736666d595932,adccd9b3b7b7beb6,616c6c5e1e7e7e7c,1d06028602029a9a |
Code Analysis
Risk Score
50/100
Threat Level
ALTO
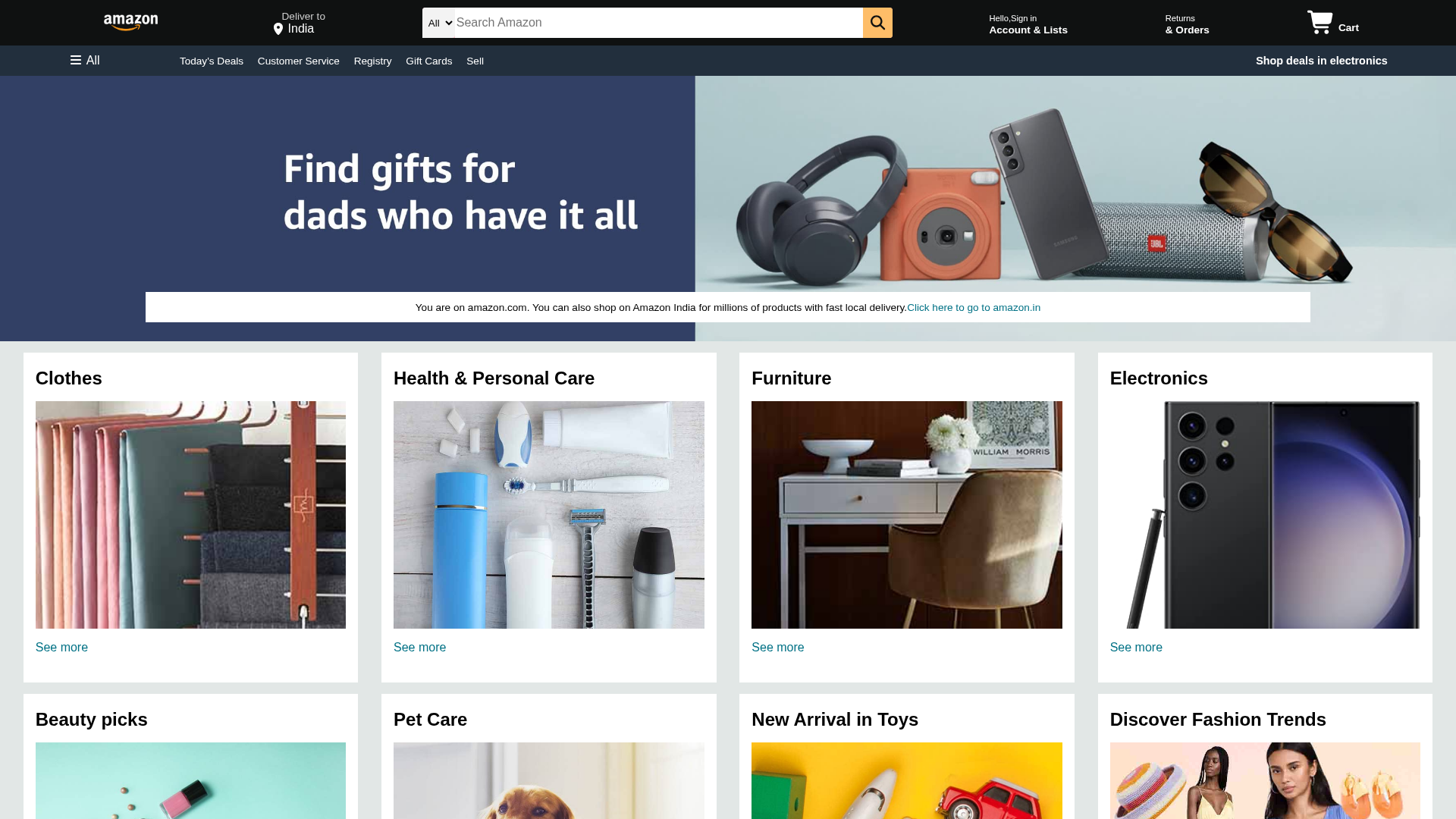
⚠️ Phishing Confirmed
🎣 Banking
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Amazon users
• Method: Impersonation through a look-alike website on free hosting
• Exfil: Unclear without further analysis, but likely data theft (credentials, payment info)
• Indicators: Amazon logo, free hosting, no forms visible in this screenshot
• Risk: High
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Free Hosting + Brand Logo
The combination of free hosting and the Amazon logo strongly indicates phishing.
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Amazon users (International)
Attack Method
Brand impersonation
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
MEDIUM - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Banking
🏢 Brand Impersonation Analysis
Impersonated Brand
Amazon
Official Website
https://www.amazon.com/
Fake Service
Amazon
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attackers will likely attempt to steal the user's Amazon login credentials by presenting a fake login form. Once the user enters their information, the attackers will have access to the victim's Amazon account.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
www.amazon-clone-amber-five.vercel.app
Registered
None
Registrar
None
Status
Unknown
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Amazon
https://rishh16.github.io/Amazon-clone
Apr 07, 2026
Amazon
https://anjaliy2906.github.io/amazonclone/
Apr 07, 2026
Amazon
https://shivakarthikeya-99.github.io/Amazon_Clone_Project/
Apr 06, 2026
Amazon
https://amazon-clone-amber-five.vercel.app/
Apr 06, 2026
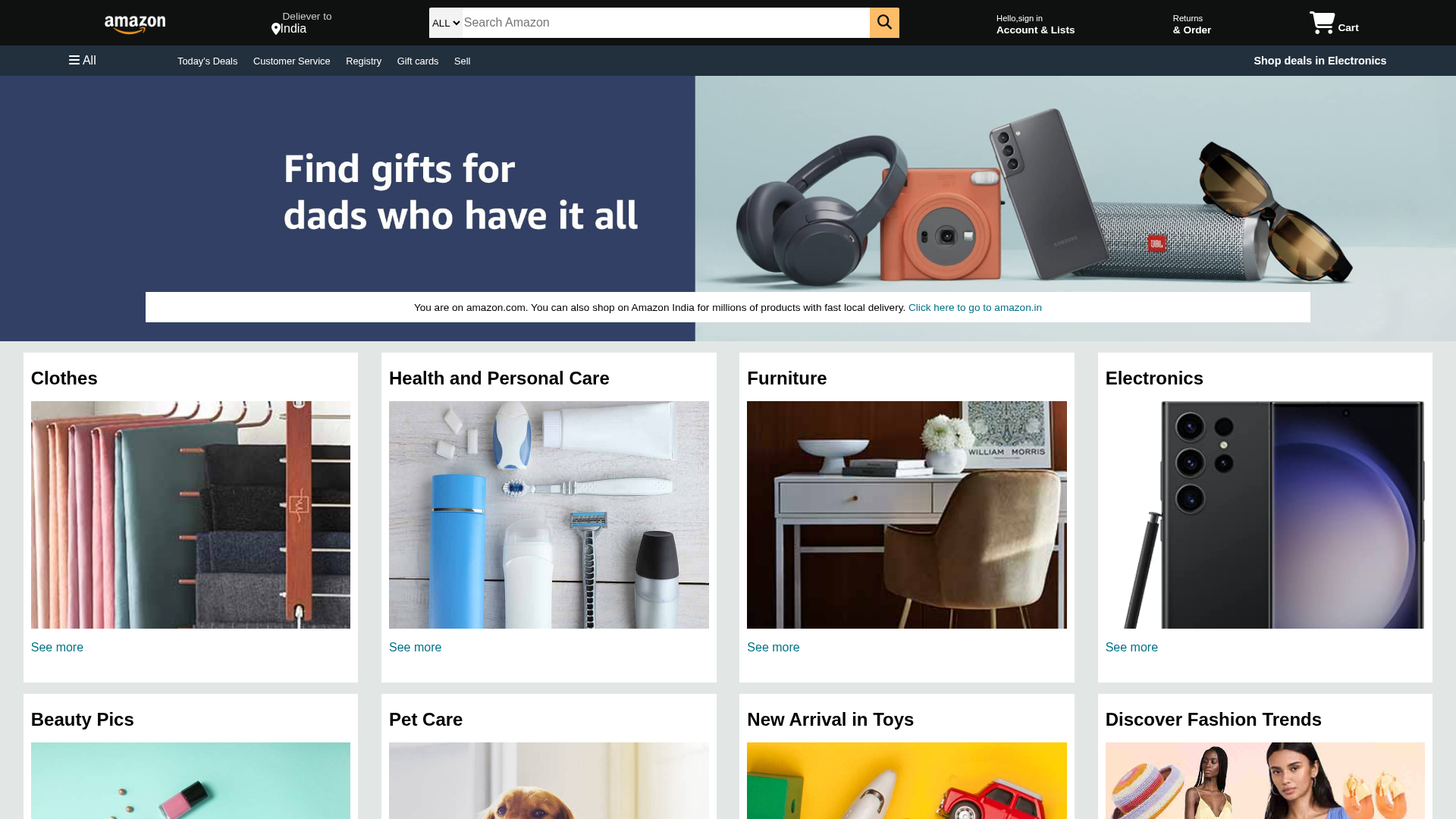
Amazon
http://www.amazon-clone-jade-ten.vercel.app/
Apr 06, 2026

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.