Phishing Analysis
Detailed analysis of captured phishing page
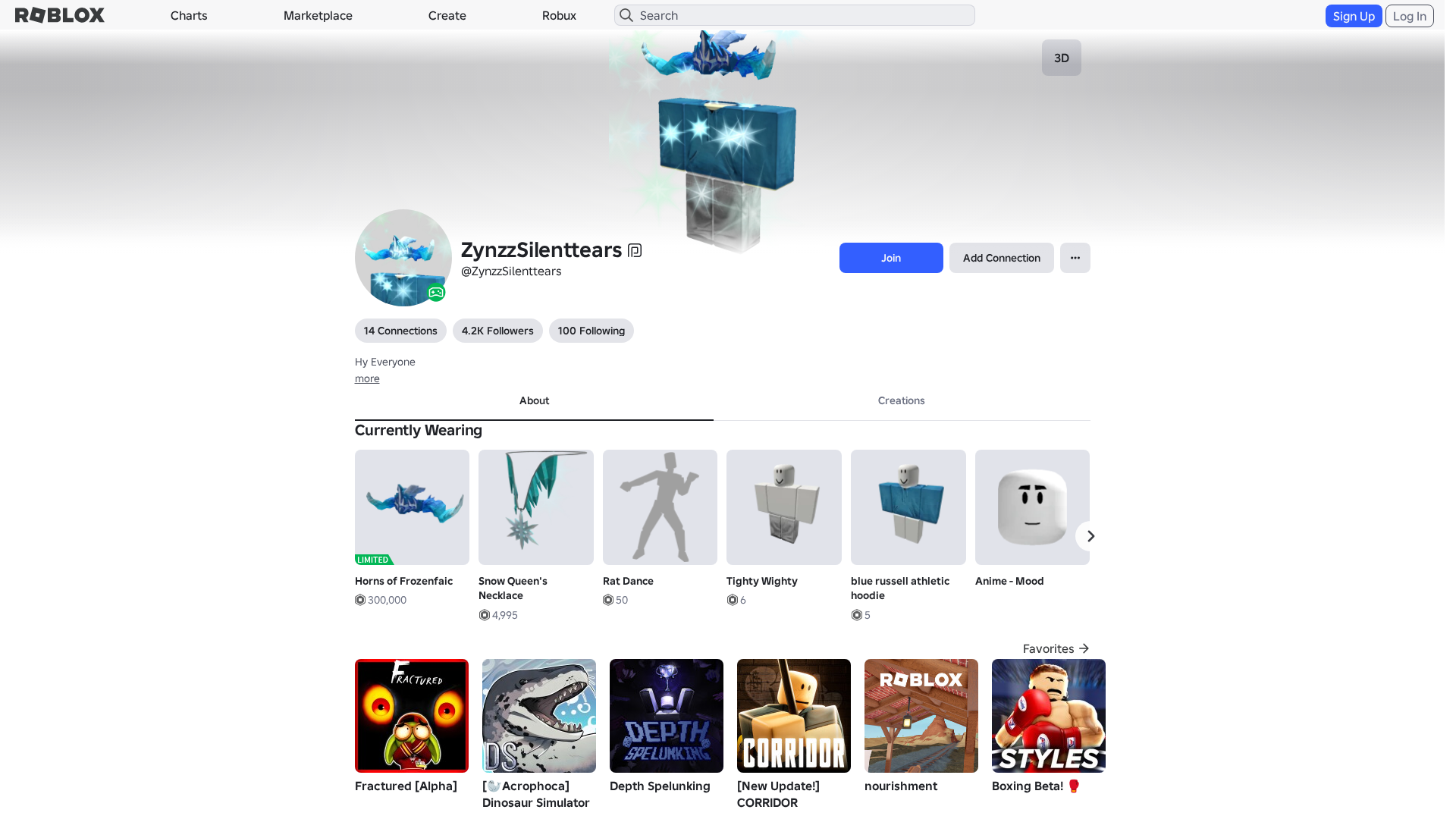
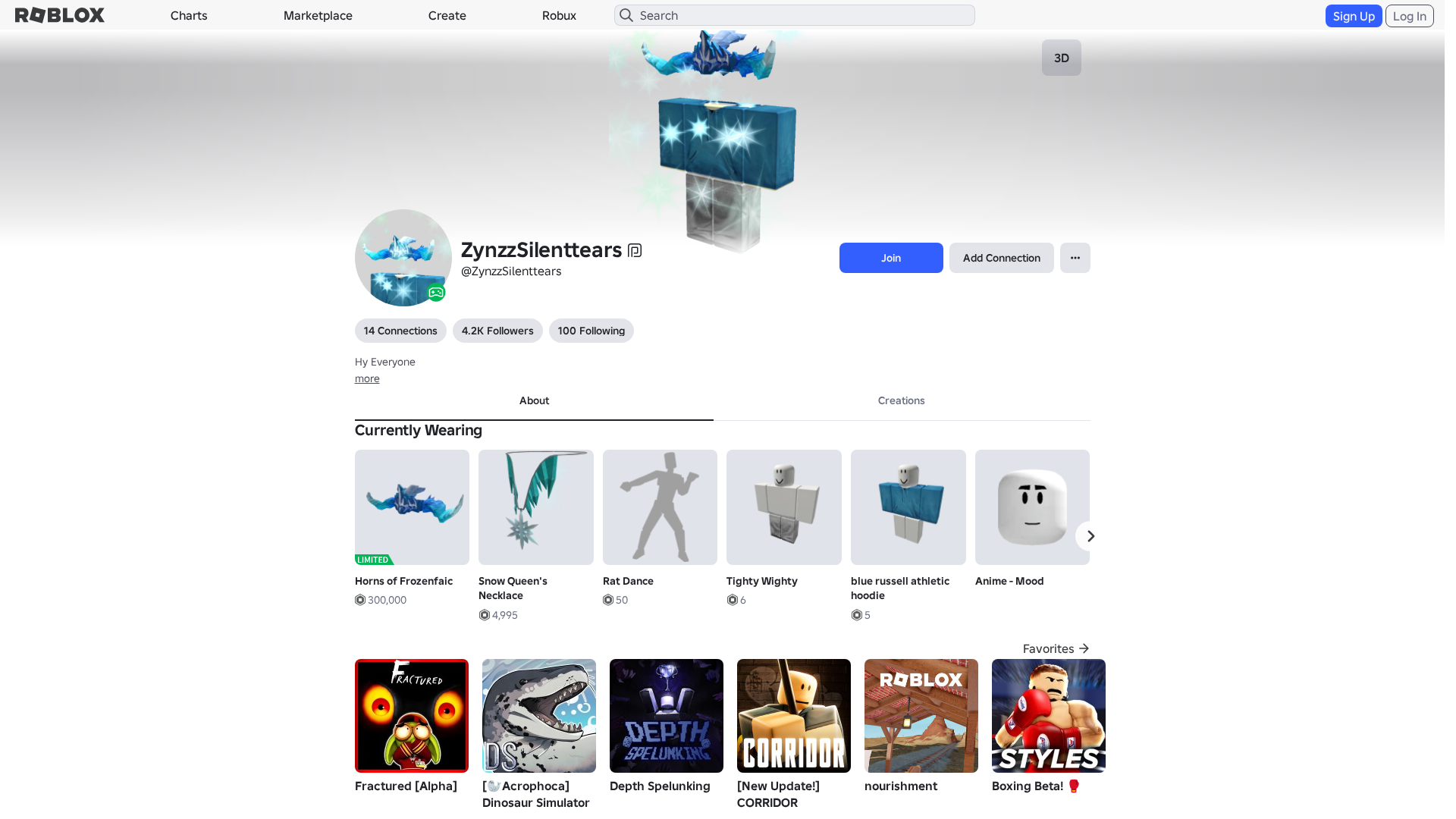
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T18953647292602837617F79D9F0656719D2D3D70FCA8346E1A2FC939A0FDACA1F853809 |
|
CONTENT
ssdeep
|
1536:jsDXWnGr/hseRoBsgL/gYEgzKgnPgeEgXbgXxg9LgsVgecgaYgM2gIGKhxHKesLD:QDXWehOflrlxg6tnM+QpxqeEKf9AF |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b4c663c79998cc3c |
|
VISUAL
aHash
|
0024dfffc3ffc3c3 |
|
VISUAL
dHash
|
c8ccb63016160f0e |
|
VISUAL
wHash
|
0000d7ffc3d7c3c3 |
|
VISUAL
colorHash
|
07201008080 |
|
VISUAL
cropResistant
|
c8ccb63016160f0e,ad4d593979670701,7171717151455151,65e98686f2694d59 |
Code Analysis
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/271015154/CW-Ultimate-Emerald-Entropy
- https://api.injuries.lu/catalog/527365852/Dominus-Praefectus
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/187998056/Snow-Queens-Necklace
- https://api.injuries.lu/catalog/1744068357/Horns-of-Frozenfaic
- https://api.injuries.lu/catalog/77655751151661/blue-russell-athletic-hoodie
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F172167473172%2Fprofile
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F172167473172%2Fprofile
- https://api.injuries.lu/catalog/136016585686255/Duo-Emote-Gangnam-B
- https://api.injuries.lu/catalog/1180419690/Disgraced-Baroness-of-the-Federation
- /login?returnUrl=
- https://api.injuries.lu/catalog/11573370910/Anime-Mood
- https://api.injuries.lu/catalog/15093053680/Headless-Head
- https://api.injuries.lu/catalog/15248005226/Tighty-Wighty
- https://api.injuries.lu/catalog/135470997/Dr-Ishmael
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/183468963/Ghosdeeri
- https://api.injuries.lu/catalog/98603994713783/Rat-Dance
📡 API Calls Detected
- https://kyxn.dev/api/shorten/TKvzwH
- https://kyxn.dev/api/shorten
- https://help.roblox.com/hc/articles/30428367965460
- GET
- https://ro.blox.com/Ebh5?
- https://apis.
- get
- POST
- /api/shorten
- https://kyxn.dev${e.endpoint}
- /api/pageview
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 212 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 212 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for rblx.foo
Found 10 other scans for this domain
-
https://rblx.foo/s/cyFAoF
https://rblx.foo/s/J3h4AL
https://rblx.foo/s/myroblox
https://rblx.foo/s/roblox-com-users-3324118
https://rblx.foo/s/www-roblox-coms
https://rblx.foo/s/users243671918813profile
https://rblx.foo/s/roblox-com-users-3110201
https://rblx.foo/s/robIox-profiIe
https://rblx.foo/s/LX0Gyi
https://rblx.foo/s/rxgKLr