Phishing Analysis
Detailed analysis of captured phishing page
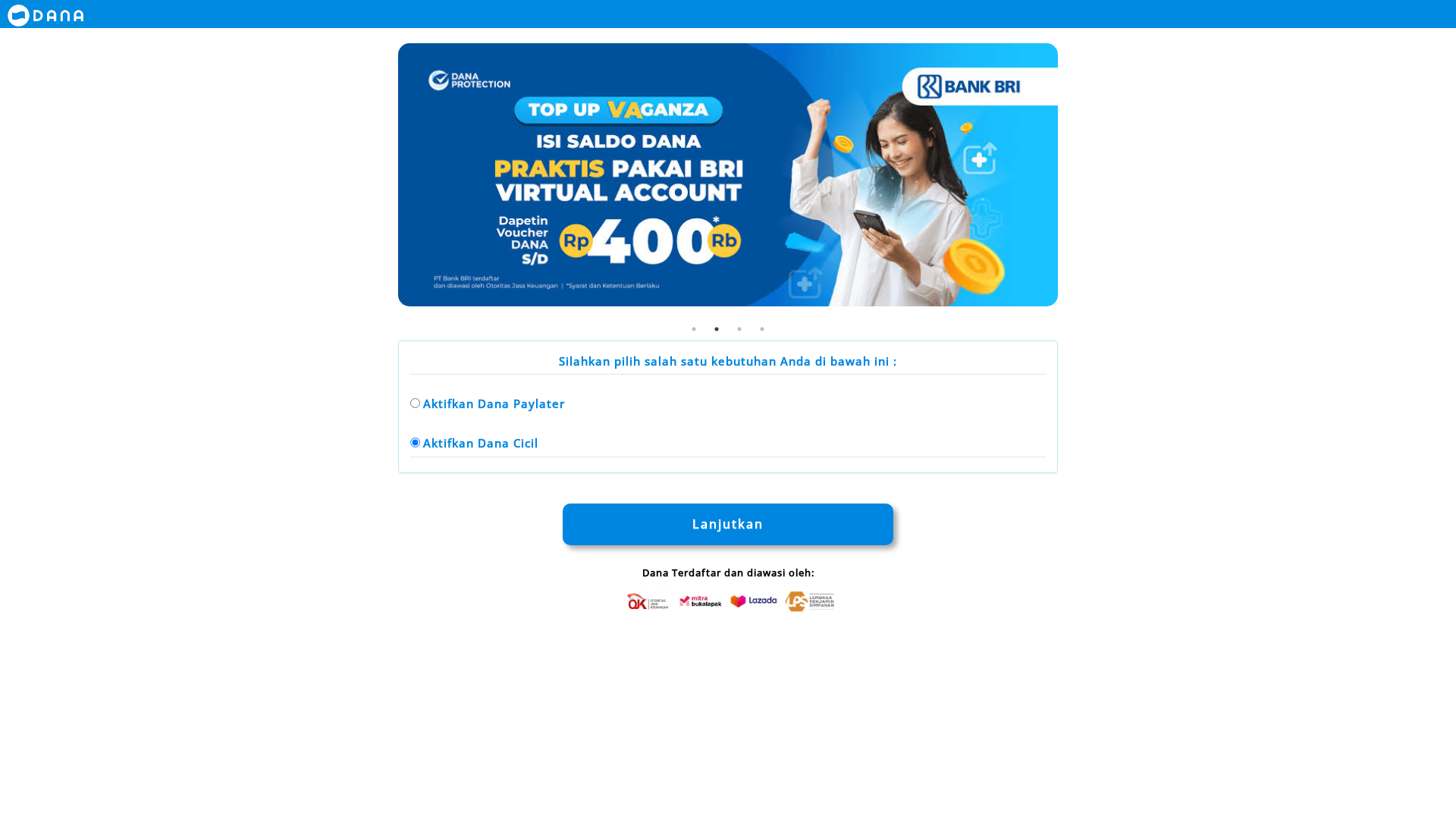
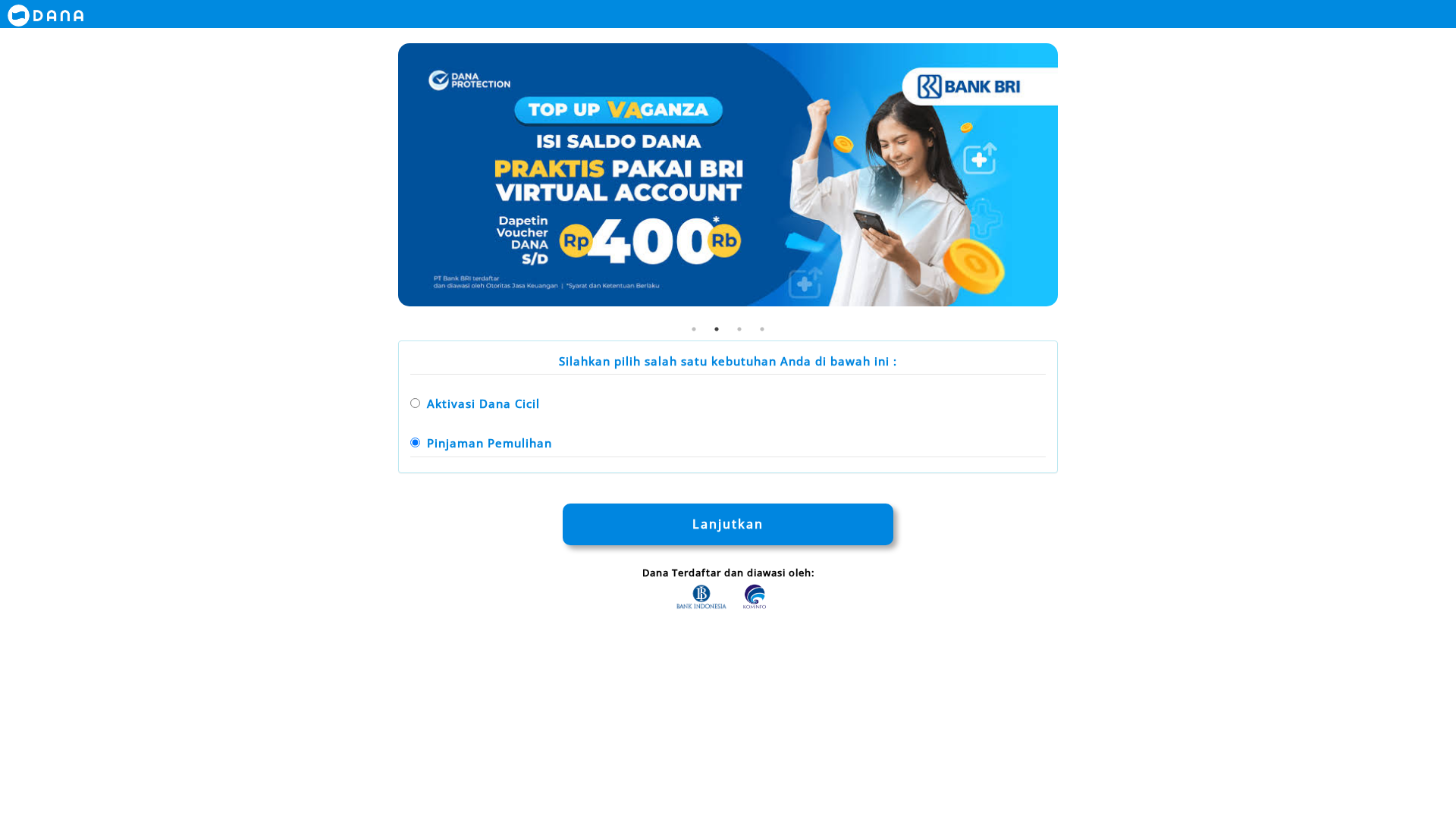
Visual Capture
Detection Info
https://pengaajuaann-danaaa-paylaateerr.armeiza.works/
Detected Brand
DANA
Country
Indonesia
Confidence
95%
HTTP Status
200
Report ID
3f17dc97-be5…
Analyzed
2026-01-05 13:16
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T177F167924404651B022645CE6663BB4A35C3E341DF66185026DE83BB6BDFAF0ECAF3D7 |
|
CONTENT
ssdeep
|
96:n84T4Xs0gnfsJsZdSda0Yi3Fj3PXK4pvu3FduzGVy8yZ373F2z3NgtoLQU:c2oiwQ0YqNfBx+T1R03zQz3N/p |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b0303c47cfcb3359 |
|
VISUAL
aHash
|
00c3c3ffffe7ffff |
|
VISUAL
dHash
|
1e1e9e1e0c4d0004 |
|
VISUAL
wHash
|
00c3c3c303273f3f |
|
VISUAL
colorHash
|
060000001c0 |
|
VISUAL
cropResistant
|
1e1e9e1e0c4d0004,5b1999ea898f4268,0000804040404040,2fd7e6f6d4f7f686 |
Code Analysis
Risk Score
58/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🔬 Threat Analysis Report
• Threat: Phishing attack targeting DANA users to steal personal data.
• Target: DANA users in Indonesia.
• Method: The attack employs a fake DANA landing page with two forms, likely to harvest user credentials.
• Exfil: Data exfiltration is indicated by the presence of obfuscated JavaScript (fromCharCode).
• Indicators: The domain is not the official DANA domain and uses a suspicious URL pattern. Javascript obfuscation is used.
• Risk: HIGH - Potential for immediate credential theft and financial loss.
🔒 Obfuscation Detected
- fromCharCode
📡 API Calls Detected
- POST
Similar Websites
Pages with identical visual appearance (based on perceptual hash)

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.