Phishing Analysis
Detailed analysis of captured phishing page
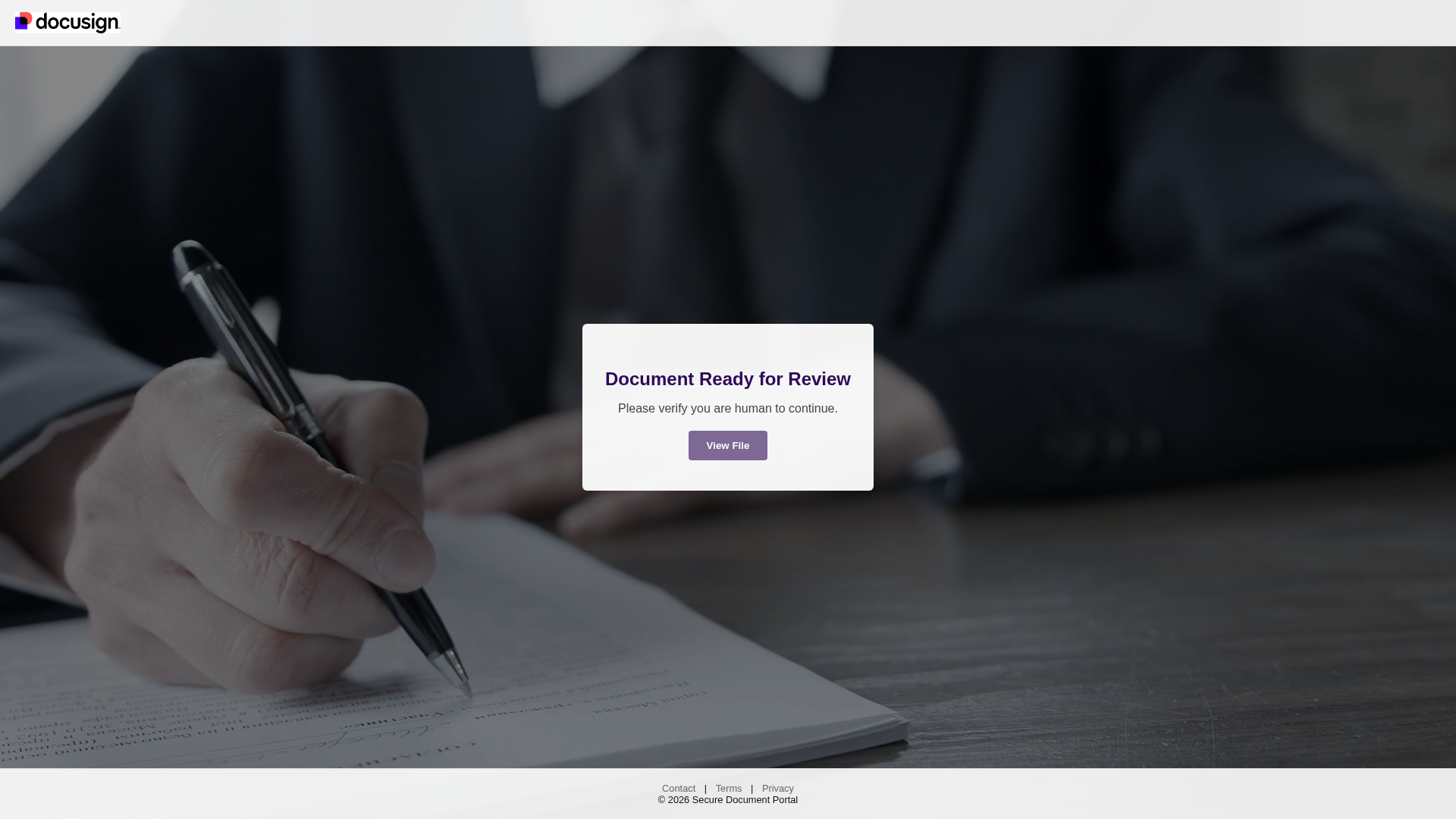
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1AE211530B049D81B4662C2C4F7F0A50B3F81C3D9D7482D1576DFA6AA1EF6D59EC1A0D5 |
|
CONTENT
ssdeep
|
12:hRwMy7FU5GKNJdoRG7wv9Tv6qqET7ADAtJD1G7BzAewPrikkWCFwo7Qa59SCIUeY:hR/CCdo9v9zdnh7DmKvUuTj6vOPwyoTp |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
dc2fa7e2d89ca2c0 |
|
VISUAL
aHash
|
ff000018d8e0f8ff |
|
VISUAL
dHash
|
63636232b2a92064 |
|
VISUAL
wHash
|
ff000018d8f0fcff |
|
VISUAL
colorHash
|
1e007000000 |
|
VISUAL
cropResistant
|
31a1232363636363,ae820baa8eccceb2,4c4c080c0c0c1818,63633232b2ab2060 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: DocuSign users
• Method: Impersonation via a suspicious domain and a call to action button.
• Exfil: Unknown, likely credential theft or malware download.
• Indicators: Domain mismatch, call to action button, request to verify.
• Risk: High
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting / Malware Delivery
The attacker aims to steal user credentials. After clicking the 'View File' button, the user will likely be redirected to a page that attempts to steal credentials through a login form or install malware on the users system.
Secondary Method: Spear Phishing
The email containing the link has likely been sent in bulk, targeting DocuSign users. It may contain personalized information to increase its chance of success.
🌐 Infrastructure Indicators of Compromise
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for docusign-file.fyi
Found 2 other scans for this domain