Phishing Analysis
Detailed analysis of captured phishing page
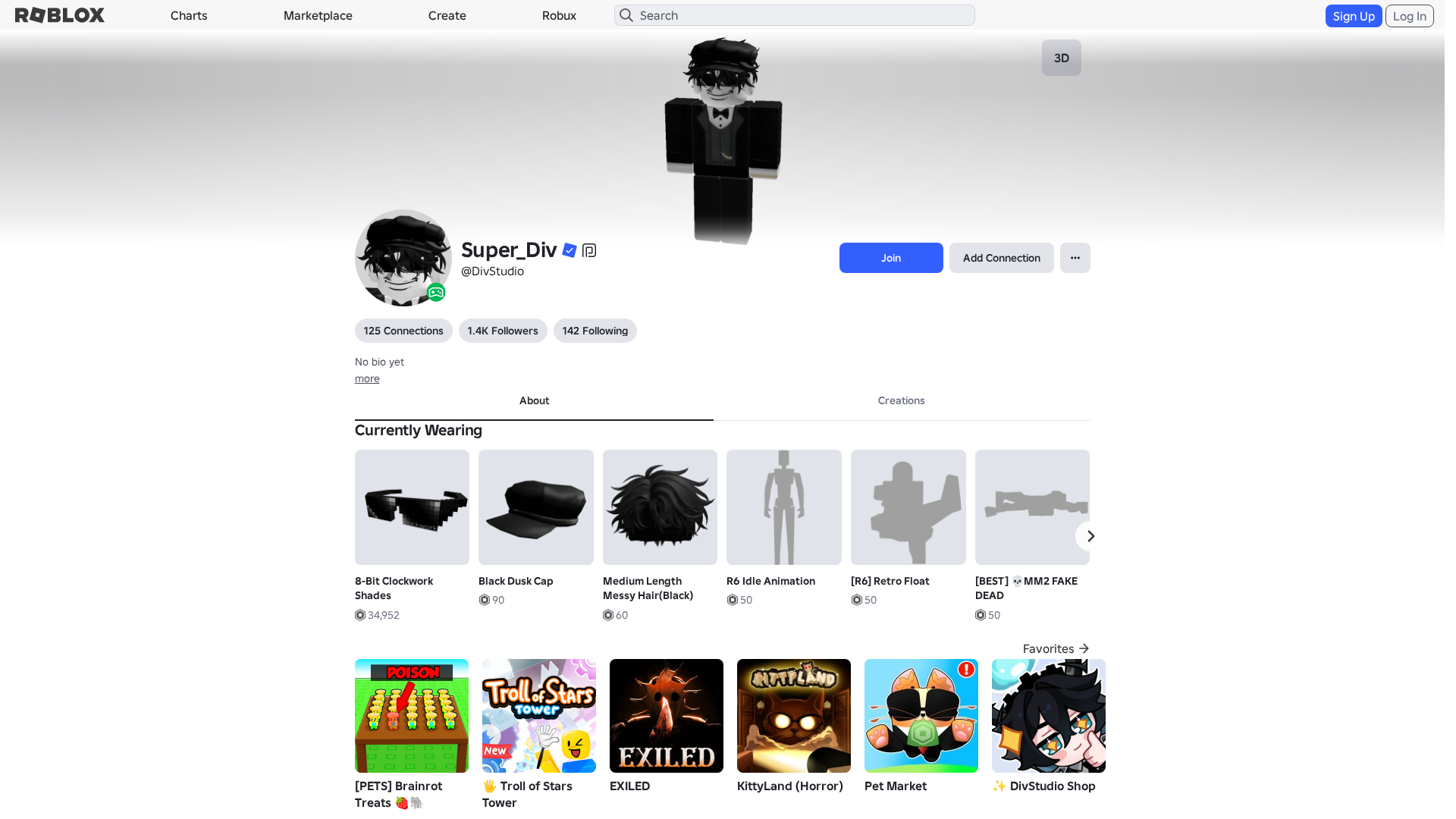
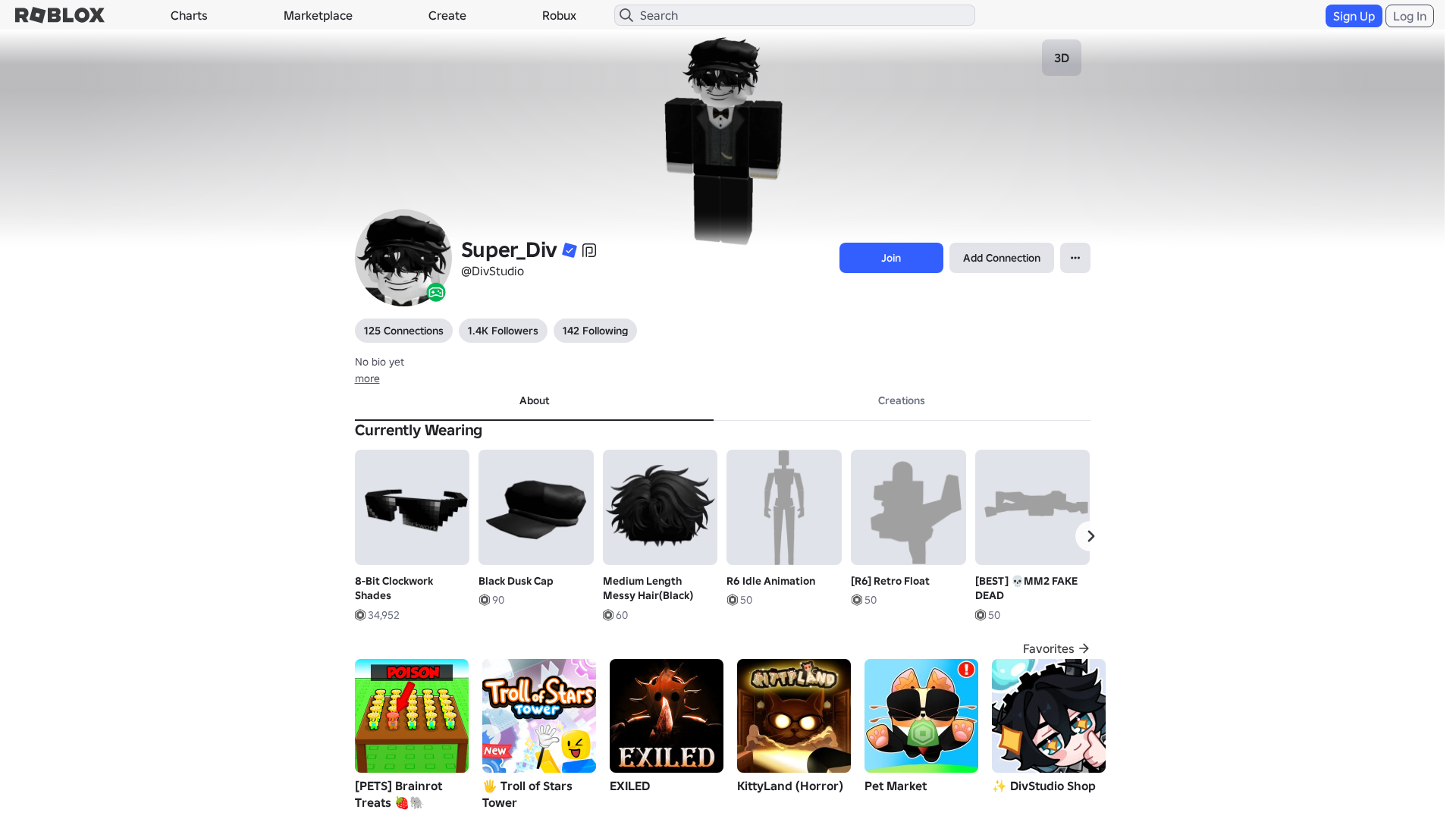
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1A583307292542837617B79DAF064672AD2D3D70FCA8346E1A2FCD39A0FD6CA1E85340D |
|
CONTENT
ssdeep
|
1536:ddAXWn4rWdde3BsgHygDKgIBgZmagVagU6g0Ig9IgLTng4bgOjguLgwjgWLgFzga:jAXWpdUH8Km54ADtTHFnhJi8iejOclEX |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b0166753d9cc9c3c |
|
VISUAL
aHash
|
2424d7ffc7cfc3c3 |
|
VISUAL
dHash
|
c8c826201e1e0b0f |
|
VISUAL
wHash
|
0000d7ffcbc7c3c3 |
|
VISUAL
colorHash
|
07200011040 |
|
VISUAL
cropResistant
|
c8c826201e1e0b0f,7371733117969696,317171555521a575,f88ccc65298ec1f3,838d3365b6b63d1d |
Code Analysis
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/553970606/Blue-Queen-of-the-Night
- https://api.injuries.lu/catalog/12911961302/Medium-Length-Messy-Hair-Black
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/14488197116/Faceless-Dynamic-Head
- https://api.injuries.lu/catalog/103808921832308/R6-Idle-Animation
- https://api.injuries.lu/catalog/72213510878866/Glow-Motion-Animation-Pack
- https://api.injuries.lu/catalog/136648387080677/DARE-Gorillaz
- https://api.injuries.lu/catalog/7978353564/Old-Style-Mafia-Boss-Suit-w-Bow-Tie-By-Jo-wolfy
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F285240618715%2Fprofile
- https://api.injuries.lu/catalog/172309919/Workclock-Headphones
- https://api.injuries.lu/catalog/553970961/Green-Queen-of-the-Night
- https://api.injuries.lu/catalog/10647852134/DefaultFallBackMood
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/878899787/Silver-Emperor-of-the-Night
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F285240618715%2Fprofile
- https://api.injuries.lu/catalog/14088377739/Black-Dusk-Cap
- https://api.injuries.lu/catalog/74891470/Frozen-Horns-of-the-Frigid-Planes
- https://api.injuries.lu/catalog/136737135107143/R6-Retro-Float
- https://api.injuries.lu/catalog/106064265828459/R6-Converter-Left-Arm
- https://api.injuries.lu/catalog/76672609579386/R6-Right-Leg
- https://api.injuries.lu/catalog/127305351640459/Smug-Staring-Face
- https://api.injuries.lu/catalog/136213982609782/R6-Converter-Right-Arm
- /login?returnUrl=
- https://api.injuries.lu/catalog/17521857429/Daemonshank
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/122290199038653/R6-Converter-Torso
- https://api.injuries.lu/catalog/105694625450094/R6-Converter-Left-Leg
- https://api.injuries.lu/catalog/124733969277188/Glow-Motion-Animation-Pack
- https://api.injuries.lu/catalog/450557238/8-Bit-Clockwork-Shades
- https://api.injuries.lu/catalog/439945661/Silver-King-of-the-Night
- https://api.injuries.lu/catalog/70972410468289/BEST-MM2-FAKE-DEAD
- https://api.injuries.lu/catalog/126137138096765/Glow-Motion-Animation-Pack
- https://api.injuries.lu/catalog/91745899537026/Glow-Motion-Animation-Pack
📡 API Calls Detected
- https://kyxn.dev/api/shorten/TKvzwH
- https://kyxn.dev${e.endpoint}
- https://help.roblox.com/hc/articles/30428367965460
- https://ro.blox.com/Ebh5?
- https://kyxn.dev/api/shorten
- GET
- /api/shorten
- get
- POST
- /api/pageview
- https://apis.
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 212 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 212 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for rblox.me
Found 5 other scans for this domain