
Phishing Analysis
Detailed analysis of captured phishing page
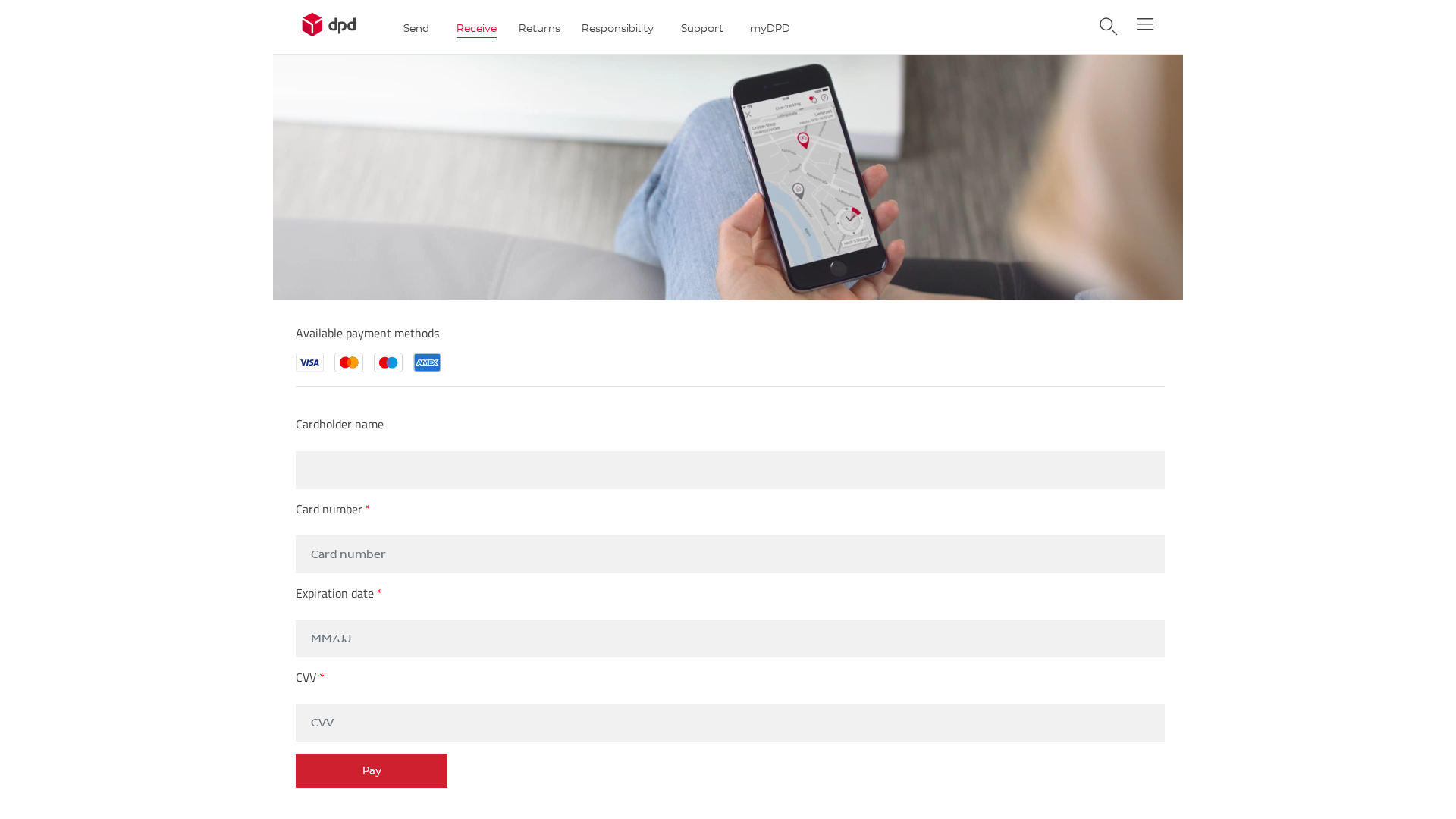
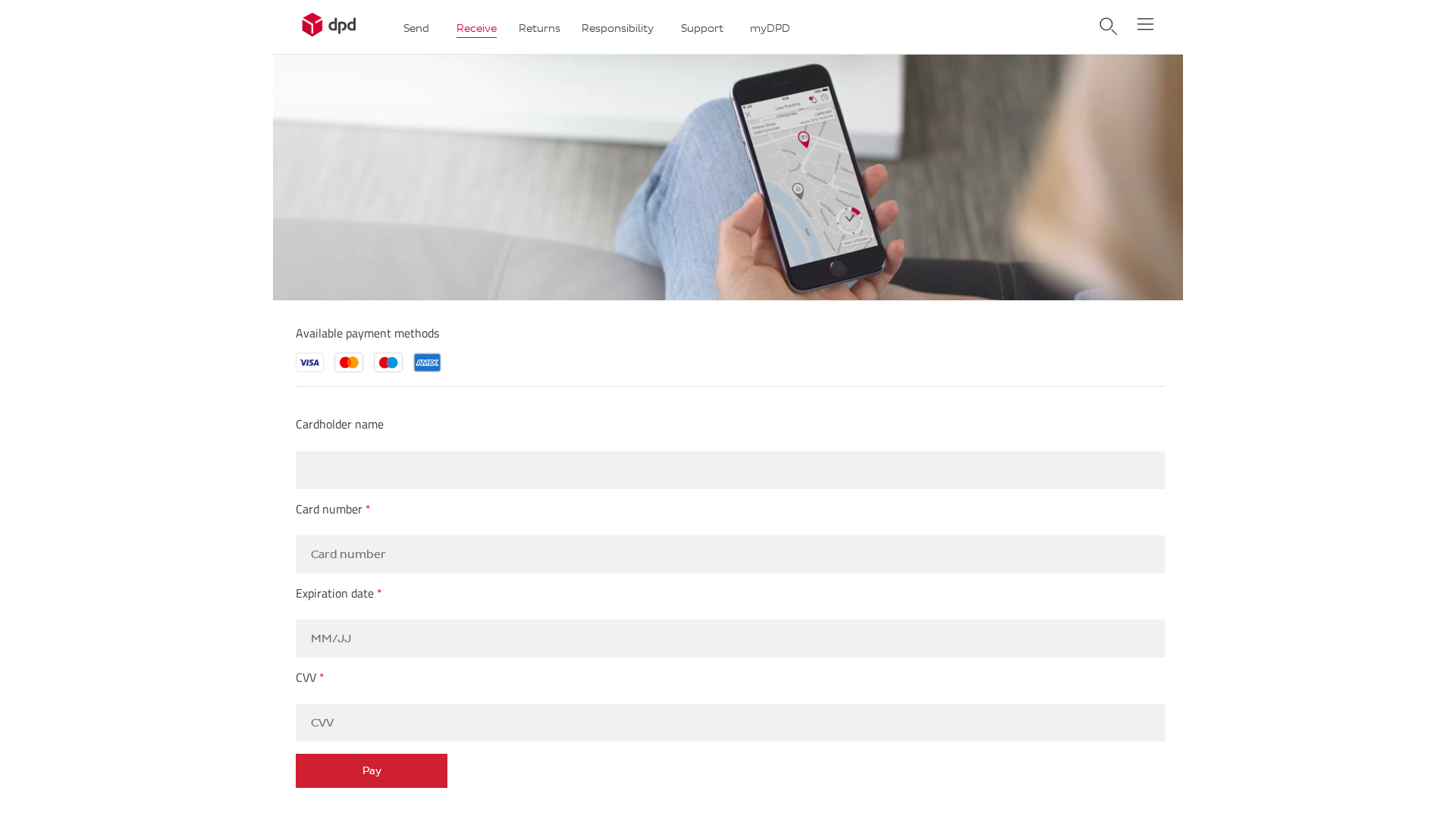
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1FFC2227094B5A57F009F72D1A738A705A3C39382CB520BE567FC936D8BCAE84DC23569 |
|
CONTENT
ssdeep
|
384:2x8xw7pvKpJrVUatKroxNaNp8+XxFUH/JO:txbrKr2sRUHc |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
ed6d6d9392923c30 |
|
VISUAL
aHash
|
f1c181ffffffff9f |
|
VISUAL
dHash
|
230307233b23032b |
|
VISUAL
wHash
|
818181dfd3c3c39f |
|
VISUAL
colorHash
|
07c00000002 |
|
VISUAL
cropResistant
|
230307233b23032b,67e5258787c39767 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: DPD customers
• Method: Impersonation and form-based data theft
• Exfil: action.php
• Indicators: Credit card form, Obfuscated code
• Risk: High
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- base64_strings
🎯 Kit Endpoints
- ./app/wp-content/themes/DPD_Login/css/styles.min5b21.css?ver=6.0.2
📡 API Calls Detected
- POST
- https://whos.amung.us/stats/
- GET
📤 Form Action Targets
- action.php
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 17 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker is attempting to steal credit card credentials through a fake form that impersonates DPD. The user is prompted to enter their credit card information, which is then sent to the attacker. The use of obfuscated JavaScript increases the risk.
🌐 Infrastructure Indicators of Compromise
Domain Information
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Light
- : Light
- : Light
- : None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for 165-227-112-65.cprapid.com
Found 4 other scans for this domain
