
Phishing Analysis
Detailed analysis of captured phishing page
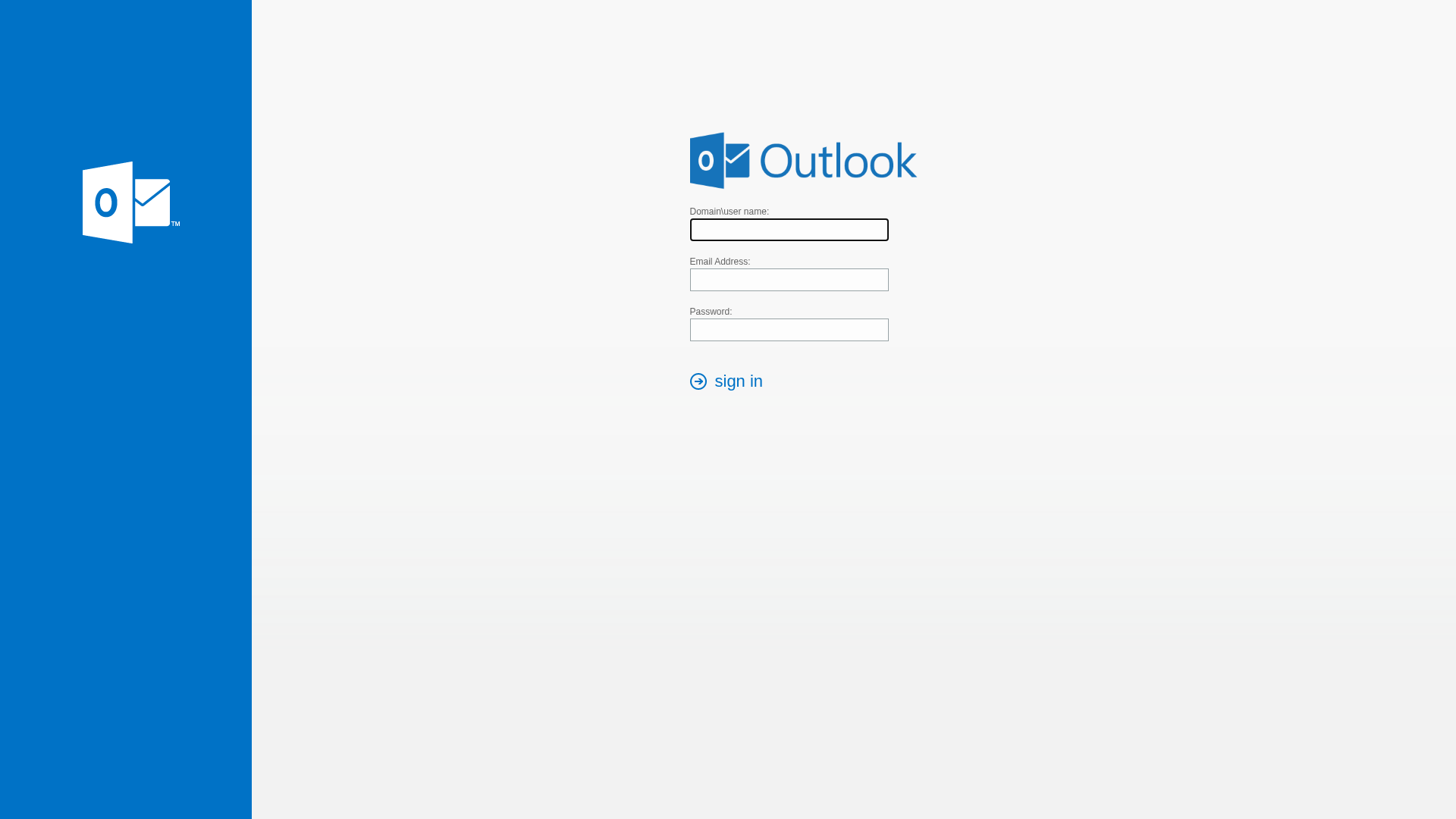
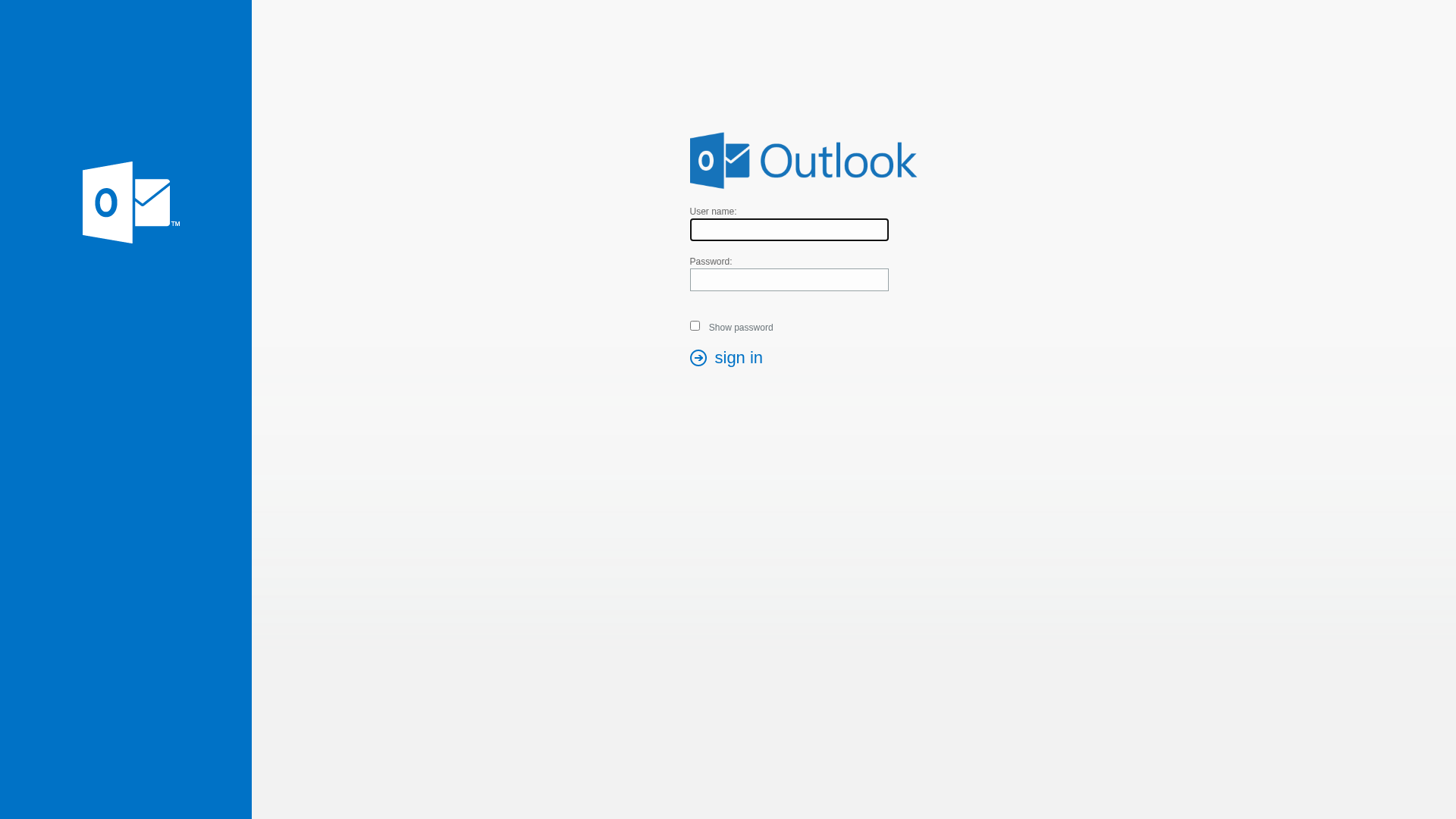
Visual Capture
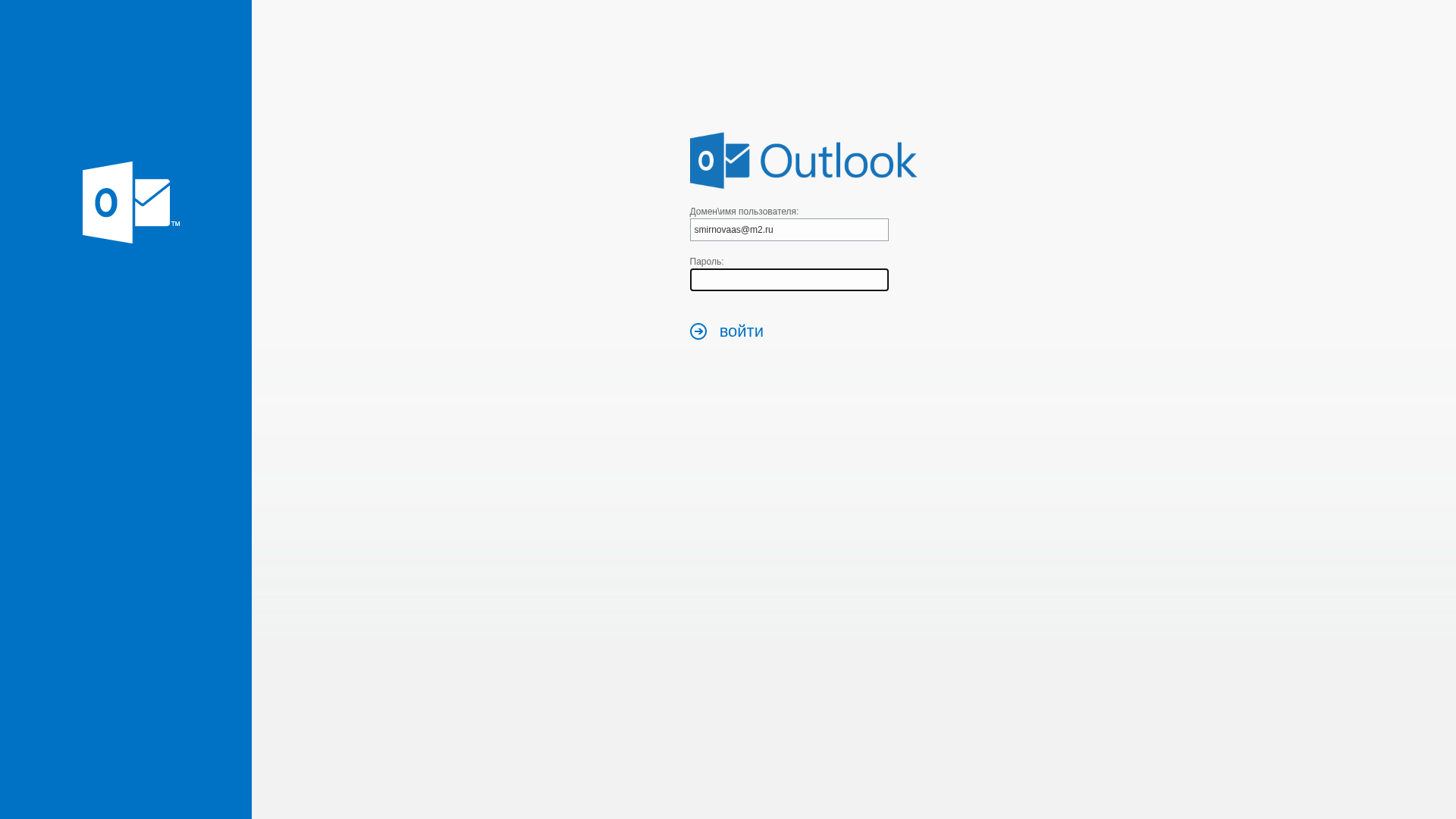
Detection Info
http://mail.info-portall.ru/page?token=337e2fb6f6312be97d20dd50b97154d928163622c58f77a631a6cb16acc87092&isfromlink=true
Detected Brand
Microsoft Outlook
Country
International
Confidence
100%
HTTP Status
200
Report ID
4a7dd56b-eb8…
Analyzed
2026-03-17 01:22
Final URL (after redirects)
https://mail.info-portall.ru/page?token=337e2fb6f6312be97d20dd50b97154d928163622c58f77a631a6cb16acc87092&isfromlink=true
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1D651FF60D01AAC335003E1E8ABD0AF9F3587C315C686294D67B083AD1AF3C4DDFA662C |
|
CONTENT
ssdeep
|
48:LIVNhzJz9uT4NyJbaIncja26CzXAPDQzuTWTdTXMD5yPBLP5u61dA:LWLz9u/baIncebCKDQzuTWFXMtsFxXdA |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
83f67e09890999fc |
|
VISUAL
aHash
|
3f3f3f3f3f3f3f3f |
|
VISUAL
dHash
|
d0ccccddd0d0d0d0 |
|
VISUAL
wHash
|
3f27373f3f0f0000 |
|
VISUAL
colorHash
|
060000001c0 |
|
VISUAL
cropResistant
|
a09c989aa0808080,f184acb6b6ac84f3,0e71710e20000000 |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Microsoft Outlook users
• Method: Impersonation of login page.
• Exfil: Captures credentials. The use of obfuscated Javascript increases the risk.
• Indicators: Mismatched domain, Login form, Obfuscated Javascript,
• Risk: High
🔒 Obfuscation Detected
- eval
- base64_strings
📡 API Calls Detected
- POST
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Domain Mismatch
The domain is not a Microsoft-owned domain.
Form Submission
The presence of a login form collecting sensitive data.
Obfuscation
Presence of obfuscated JavaScript potentially used for malicious purposes
🔬 Comprehensive Threat Analysis
Threat Type
Two-Factor Authentication Stealer
Target
Microsoft Outlook users (International)
Attack Method
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer
- 7 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Microsoft Outlook
Official Website
outlook.com
Fake Service
Outlook email login
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker sets up a fake login page that closely resembles the real Outlook login. Users are tricked into entering their credentials, which are then harvested.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
mail.info-portall.ru
Registered
None
Registrar
None
Status
None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Microsoft Outlook
https://www.5mp.eu/fajlok2/dis1/index_www.5mp.eu_.html
Apr 05, 2026
Microsoft Outlook
http://www.5mp.eu/fajlok2/exchang/index_www.5mp.eu_.html
Apr 05, 2026
Microsoft Outlook
https://www.5mp.eu/fajlok2/frma/index_www.5mp.eu_.html
Mar 24, 2026
Outlook
https://www.5mp.eu/fajlok2/exchang/index_www.5mp.eu_.html
Mar 20, 2026
Microsoft Outlook
https://autodiscover.sociospanama.com/
Feb 28, 2026
Scan History for mail.info-portall.ru
Found 3 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.