
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
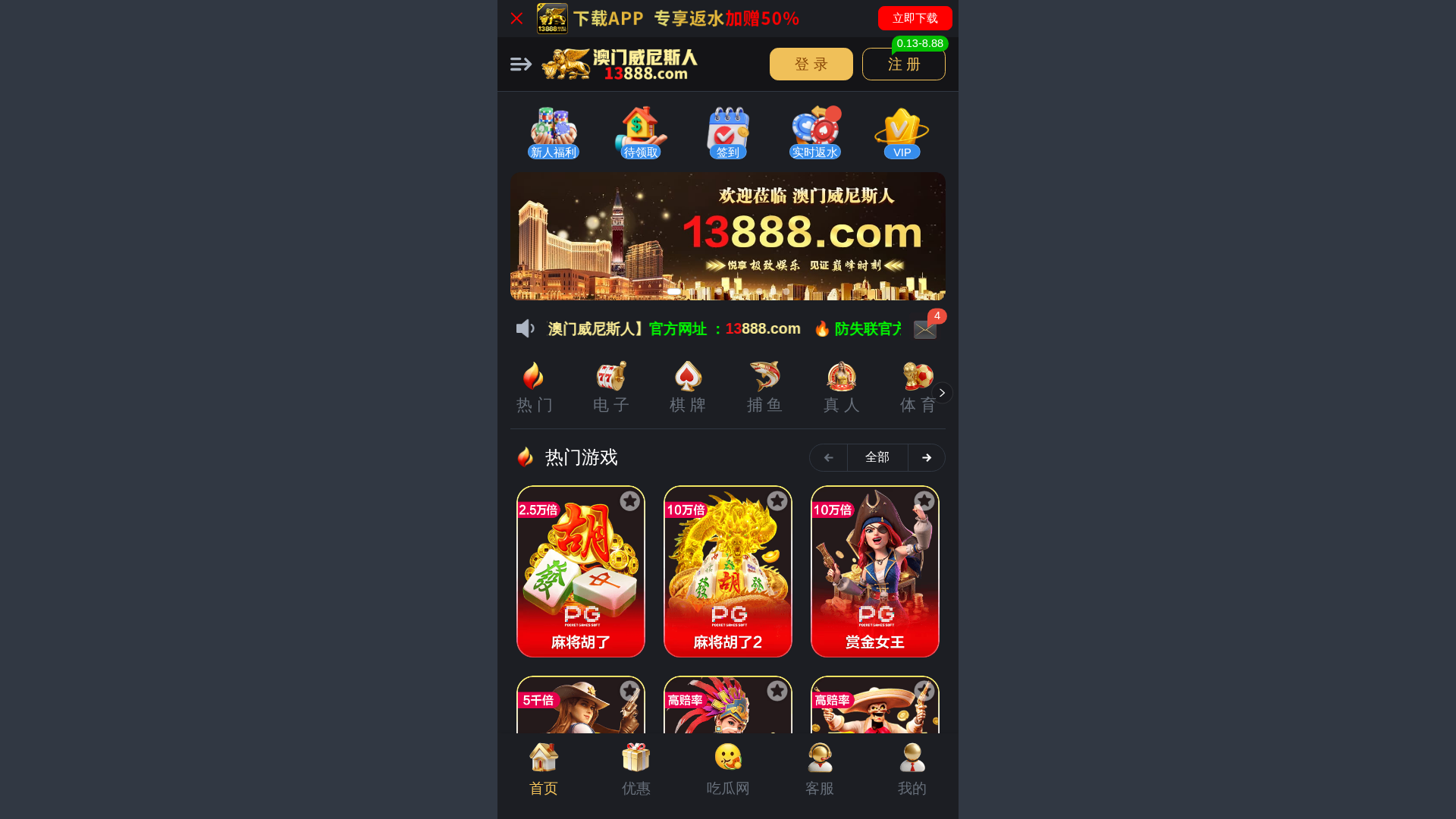
Detection Info
https://806888.co/
Detected Brand
13888 (Gambling/Betting)
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
4d6088b9-eab…
Analyzed
2026-04-01 07:55
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1BA839431F51430AF120355EAF663A628129DE26EF35182A466BC03B5EBD3CF9F673059 |
|
CONTENT
ssdeep
|
1536:1r4jFIqgICL8jU58j8kCjU58j8ujU58j8F:1r4LpjLj89jLj8ujLj8F |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cc3333cc339acc33 |
|
VISUAL
aHash
|
1808380000381c00 |
|
VISUAL
dHash
|
ba12220406b2321e |
|
VISUAL
wHash
|
d8d8f8c0c0fcdcc0 |
|
VISUAL
colorHash
|
0f400010001 |
|
VISUAL
cropResistant
|
f4fab4b5eccca4e0,ba12220406b2321e |
Code Analysis
Risk Score
85/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://806888.co/siteadmin/upload/active_marketing_small_qd1.avif
- https://806888.co/siteadmin/upload/marketing_small_icon_vip1.avif
- https://806888.co/siteadmin/skin/lobby_asset/2-1-common/common/_sprite/icon_btm_cgw.avif?manualVersion=1&version=v7.1.177
- https://806888.co/siteadmin/skin/lobby_asset/2-1-7/common/_sprite/icon_dt_1xx_wd.avif?manualVersion=1&version=v7.1.177
- https://806888.co/siteadmin/upload/active_marketing_small_ssfs1.avif
- https://806888.co/siteadmin/skin/lobby_asset/2-1-7/web/home/icon_dt_pmd.avif?manualVersion=1&version=v7.1.177
- https://806888.co/siteadmin/upload/marketing_small_icon_gjj4.avif
- https://806888.co/siteadmin/upload/marketing_small_icon_jyj1.avif
- https://806888.co/siteadmin/upload/img/2034508273930031106.avif
- login
- https://806888.co/siteadmin/upload/img/2038257144881778690.avif
📡 API Calls Detected
- withdrawTaskList
- agentApplication
- slashOnce
- eventSign
- plazzaRewardGifts
- afterRechargeActivity
- needKycValidate
- claimRule
- HEAD
- devtools
- iframeMaintainPopup
- iframeAccessRestrictedPopup
- withdrawAccounts
- securityForceBinding
- interest
- withdrawalKyc
- iframe
- setRealNameDialog
- GET
- realNameForceModify
- downloadShortcutGuide
- blindBox
- downloadMainDialog
- forbiddenSelf
- kycPerfectProfile
- temporaryAccountGuide
- appDownloadPwaTips
- ageCompliance
- returningBonus
- slashOnceReceive
- moreInterception
- bindNoWalletTip
- manifest
- cutOnce
- distributedReward
- setBirthdayDialog
- switchCurrency
- discountCode
- newCutOnce
- assetSecurity
- setPhone
- setAvatarDialog
- svipLottery
- redeemCenter
- slashOnceReceiveFirst
- verifyBindPhone
- switchLang
- bindRegister
- findUs
- setChatAccountDialog
- eventWithdrawalList
- bettingTaskList
- securityDialogBinding
- recharge
- loginVerify
- plazzaSetUserInfo
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Code Obfuscation
JavaScript code obfuscated using 46 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
13888 (Gambling/Betting) users
Attack Method
obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 46 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
13888 (Gambling/Betting)
Official Website
N/A
Fake Service
Banking/payment service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 46 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
806888.co
Registered
2026-03-31 05:24:40+00:00
Registrar
Gname.com Pte. Ltd.
Status
Recently registered (1 days old)
Hosting Information
Provider
Gname.com Pte. Ltd.
ASN
🤖 AI-Extracted Threat Intelligence

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.