
Phishing Analysis
Detailed analysis of captured phishing page
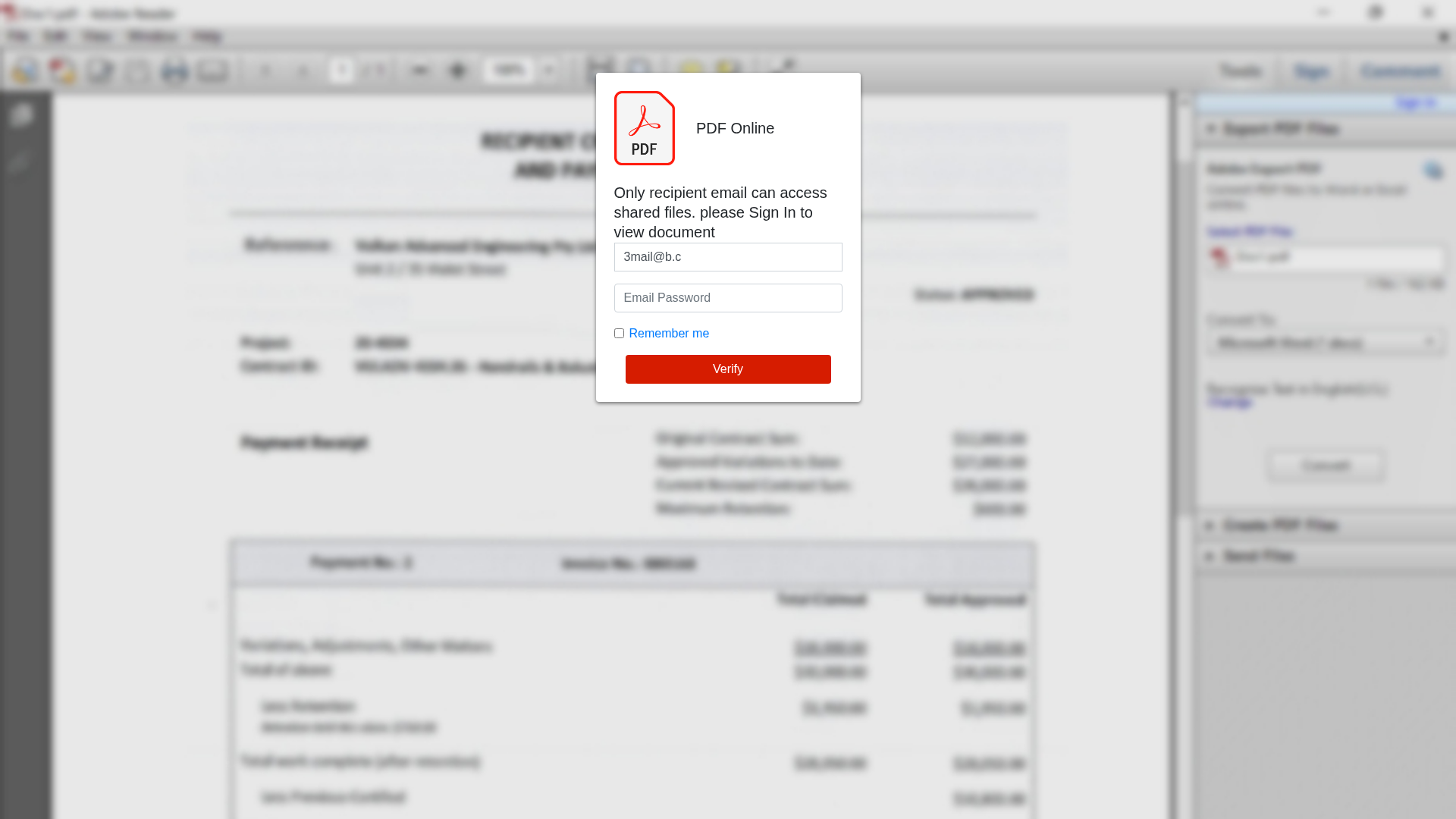
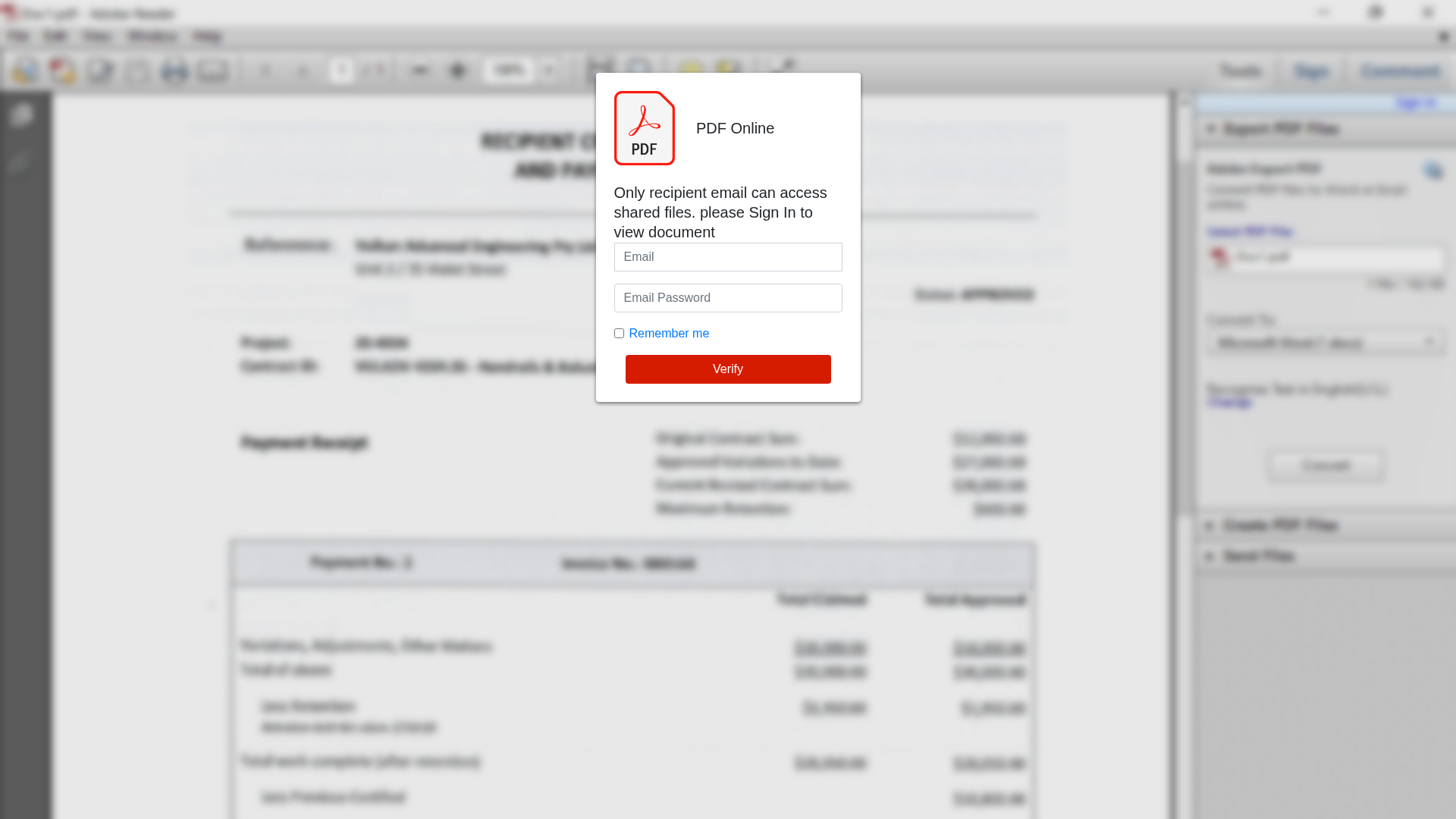
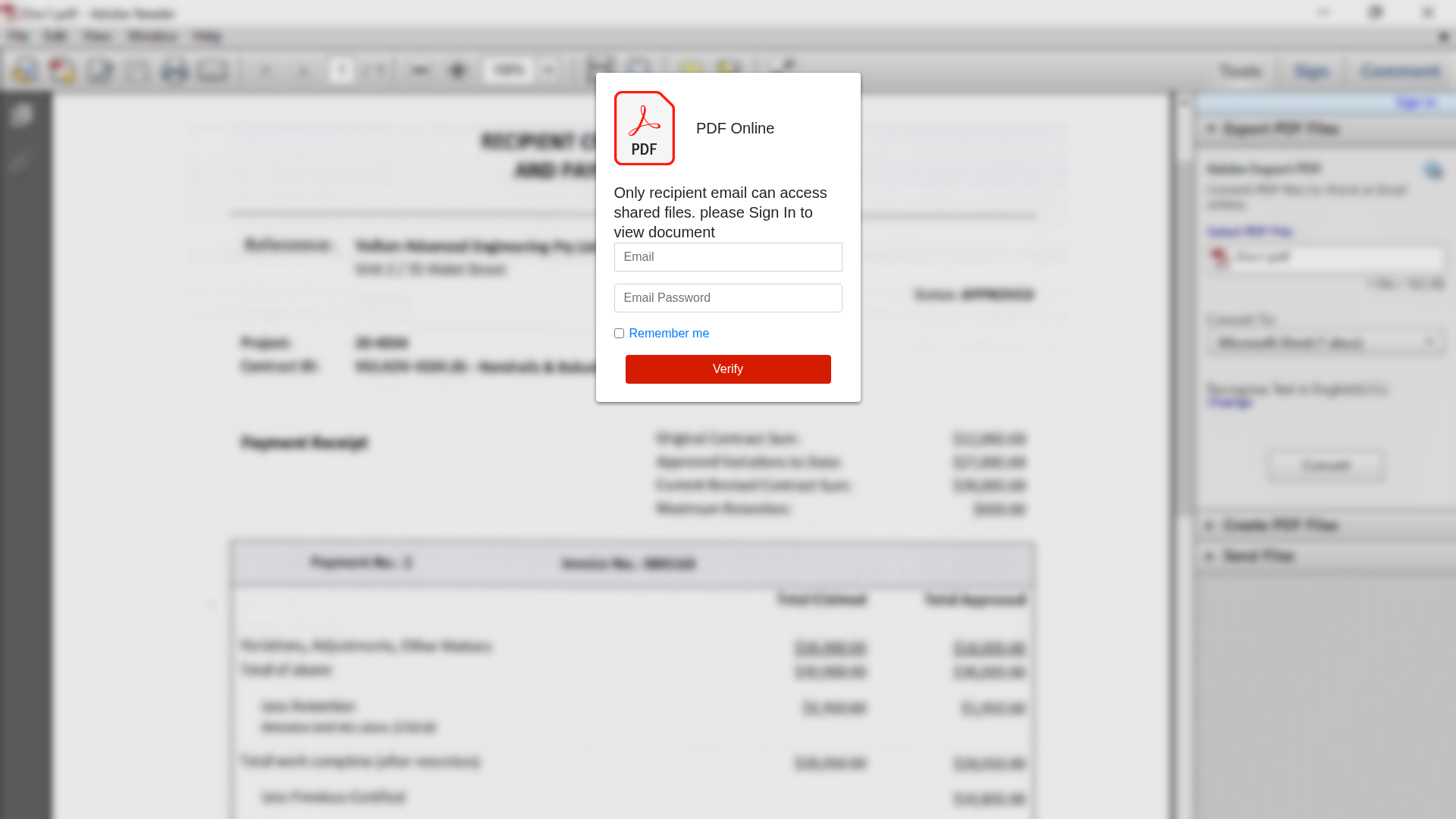
Visual Capture
Detection Info
https://pub-3b2161932db04c4eaa01be3fb152244b.r2.dev/[email protected]
Detected Brand
PDF
Country
International
Confidence
100%
HTTP Status
200
Report ID
4d9690ca-e0b…
Analyzed
2025-12-30 16:52
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1DC61413350002E1E3A32D1A4AFECB71126D1E441D59E2984B1EC67CF9AD4DE7F497268 |
|
CONTENT
ssdeep
|
48:ndqbpBAbbAuYpdLpctRo6wnbTlus5Cx2gEItxLl56of66f2bbi+Lnuk5:nYAbbAuS8GvCNt75lKiUj |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
80395d67272e2dad |
|
VISUAL
aHash
|
185c5c6c74747c7c |
|
VISUAL
dHash
|
f090b1adada4a4a4 |
|
VISUAL
wHash
|
087c5c6c7c647c7c |
|
VISUAL
colorHash
|
07000038000 |
|
VISUAL
cropResistant
|
f090b1adada4a4a4,f189c1c1c1c1c1c1 |
Code Analysis
Risk Score
86/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Credential harvesting phishing attack disguised as a PDF document viewer.
• Target: Users opening PDF files, potentially globally.
• Method: Displays a fake login form overlay on a PDF document, requesting email and password to 'access shared files'.
• Exfil: Unknown - likely a web server or API endpoint.
• Indicators: Unofficial domain, requests login within a supposedly already-opened PDF context, generic "PDF Online" branding, form detected, obfuscated Javascript.
• Risk: HIGH - Immediate risk of credential theft if a user enters their email and password.
🔒 Obfuscation Detected
- fromCharCode
- unescape
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Adobe
http://pub-3b2161932db04c4eaa01be3fb152244b.r2.dev/sweetjan....
Apr 06, 2026
PDF Online
https://pub-3b2161932db04c4eaa01be3fb152244b.r2.dev/sweetjan...
Feb 17, 2026
Adobe PDF (Impersonation)
https://pub-3b2161932db04c4eaa01be3fb152244b.r2.dev/sweetjan...
Feb 17, 2026
Adobe PDF
http://pub-3b2161932db04c4eaa01be3fb152244b.r2.dev/sweetjan....
Jan 14, 2026
PDF
https://pub-3b2161932db04c4eaa01be3fb152244b.r2.dev/sweetjan...
Jan 07, 2026
Scan History for pub-3b2161932db04c4eaa01be3fb152244b.r2.dev
Found 9 other scans for this domain
-
http://pub-3b2161932db04c4eaa01be3fb152244b.r2.dev...
https://pub-3b2161932db04c4eaa01be3fb152244b.r2.de...
https://pub-3b2161932db04c4eaa01be3fb152244b.r2.de...
http://pub-3b2161932db04c4eaa01be3fb152244b.r2.dev...
https://pub-3b2161932db04c4eaa01be3fb152244b.r2.de...
http://pub-3b2161932db04c4eaa01be3fb152244b.r2.dev...
https://pub-3b2161932db04c4eaa01be3fb152244b.r2.de...
https://pub-3b2161932db04c4eaa01be3fb152244b.r2.de...
https://pub-3b2161932db04c4eaa01be3fb152244b.r2.de...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.