Phishing Analysis
Detailed analysis of captured phishing page
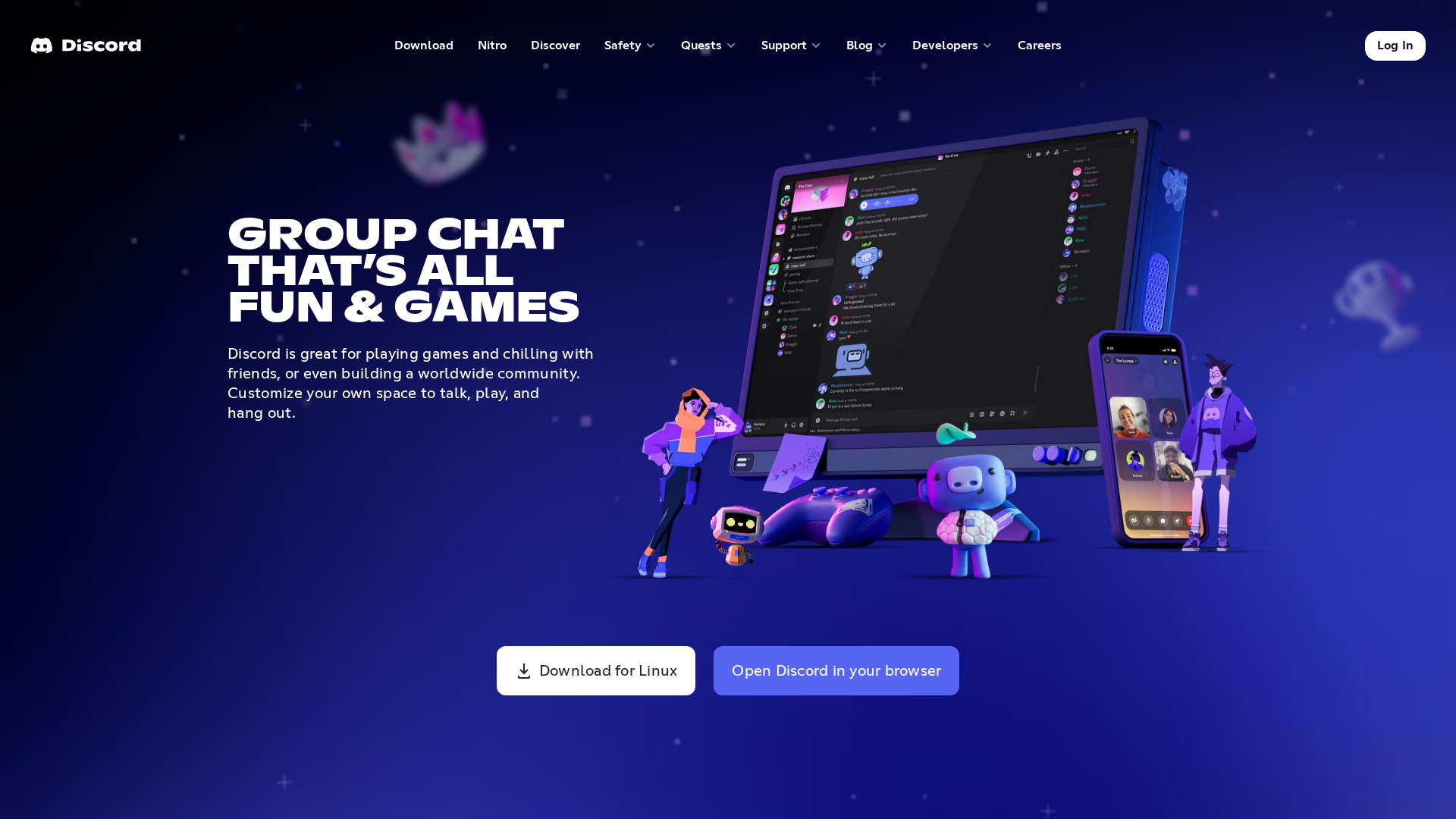
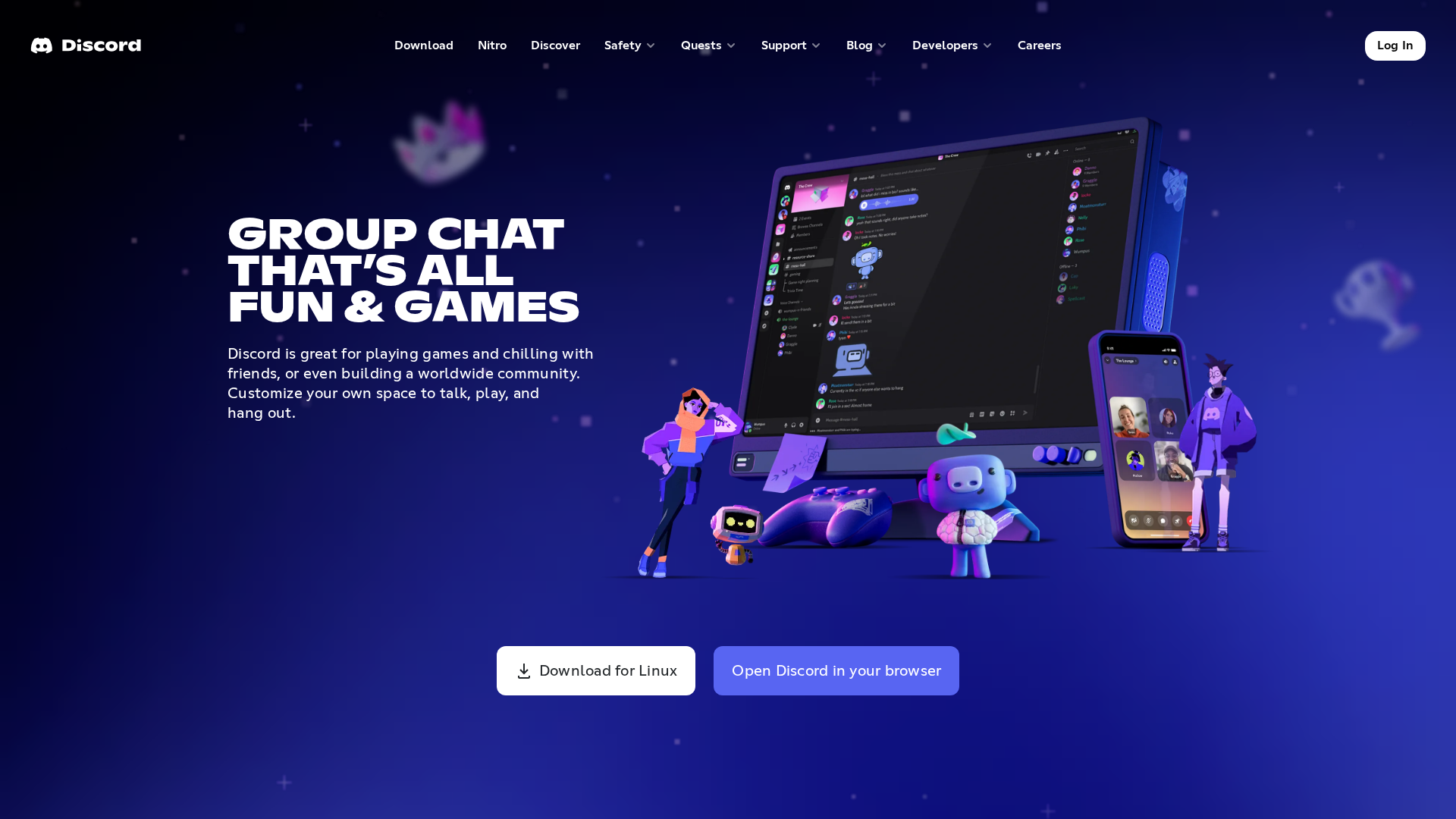
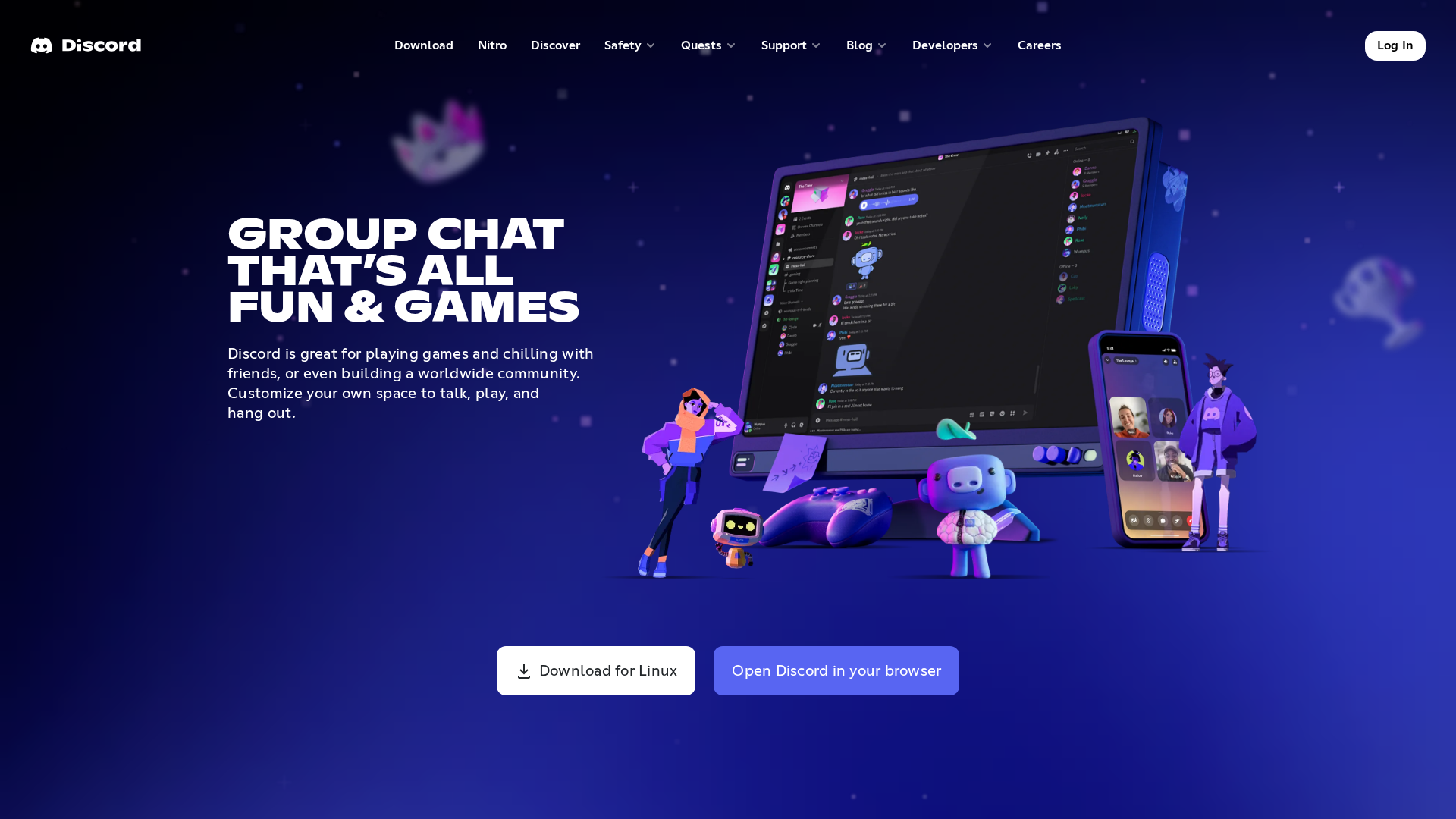
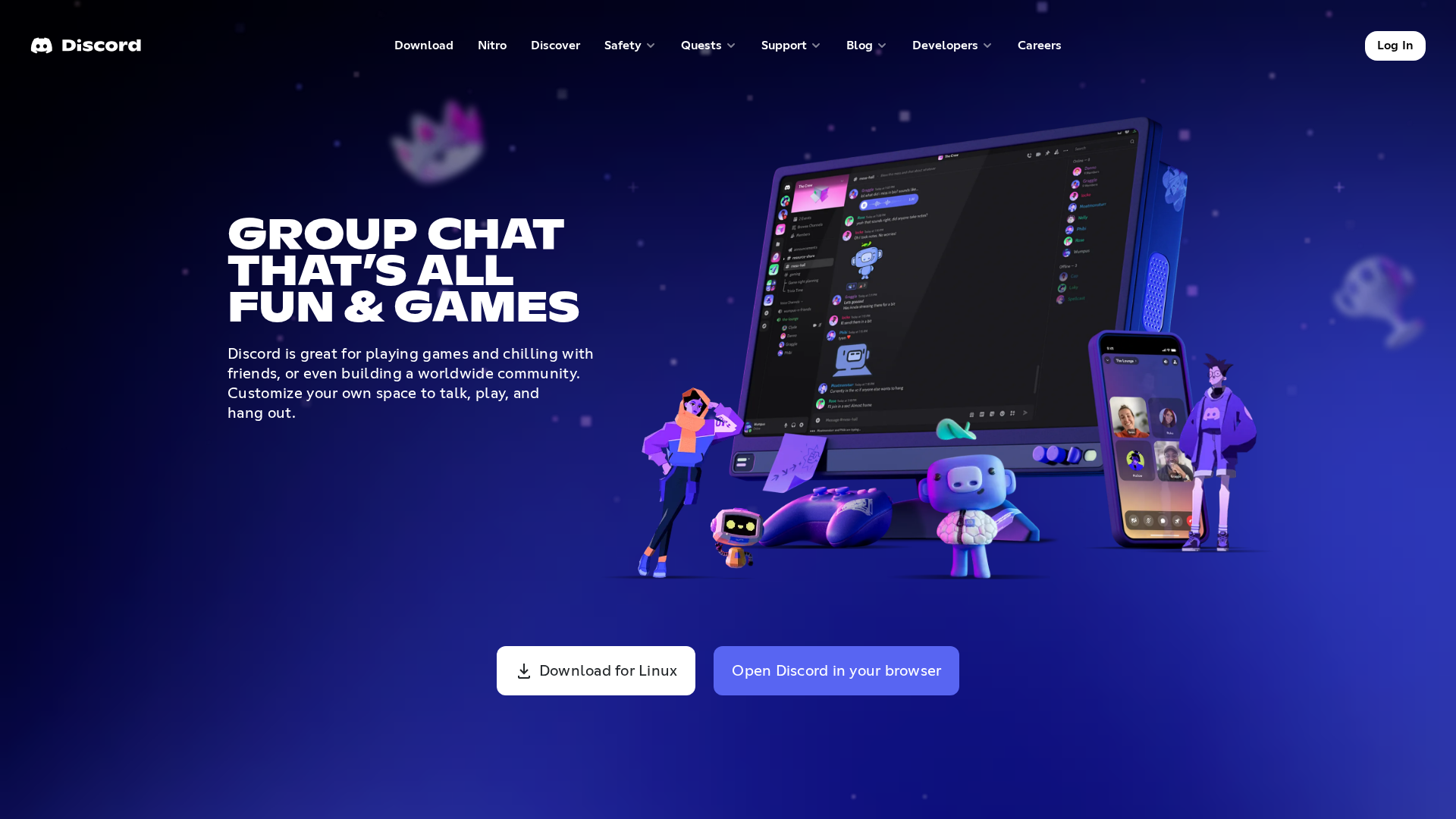
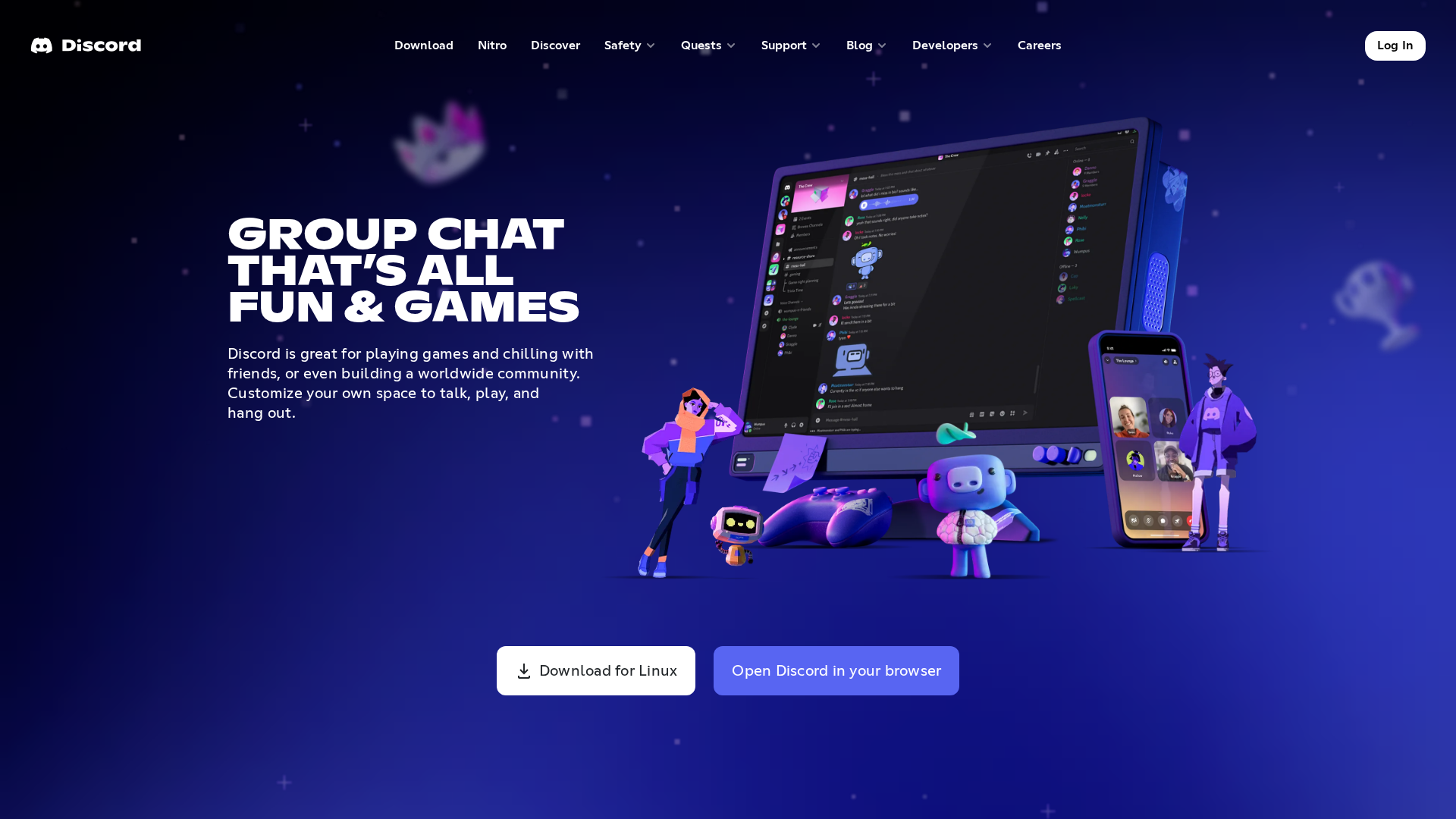
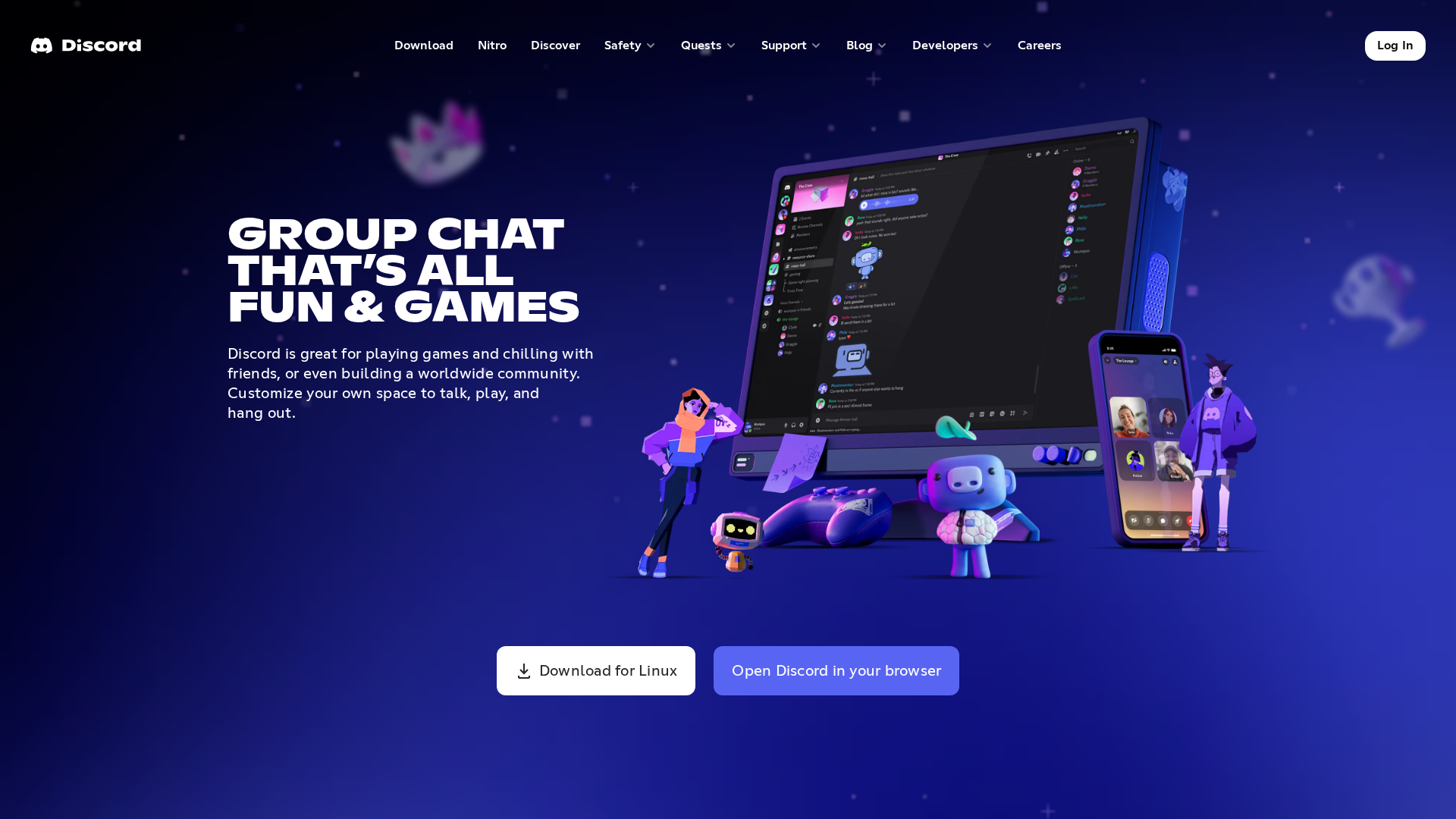
Visual Capture
Detection Info
http://chatgpt0005.eu.org
Detected Brand
Discord
Country
International
Confidence
100%
HTTP Status
200
Report ID
4dd4985b-09f…
Analyzed
2026-01-01 03:29
Final URL (after redirects)
http://chatgpt0005.eu.org/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1BAA3953BE8444017252349F1F7A07F0D5ACAD18FCE878C86ABB887463BD6CE2D85596D |
|
CONTENT
ssdeep
|
1536:XT4PdyfBMgKPjncPjncPjncPjnS4MF/ahRyrM9sP3/HlxEltf:j4Pdyf+guahAgF |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
83737e1c3cce6388 |
|
VISUAL
aHash
|
01006b731f1f3931 |
|
VISUAL
dHash
|
6ddacbc7f6ffe3e3 |
|
VISUAL
wHash
|
01006b7b1f1f3f71 |
|
VISUAL
colorHash
|
30000000180 |
|
VISUAL
cropResistant
|
a280c0260d4280a2,6ddacbc7f6ffe3e3 |
Code Analysis
Risk Score
95/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Discord phishing targeting user accounts.
• Target: Discord users.
• Method: The phishing site uses Discord's branding to trick users into entering their credentials, which are then stolen.
• Exfil: Data is likely exfiltrated via a custom API.
• Indicators: Domain mismatch (chatgpt0005.eu.org), obfuscated JavaScript, and Discord branding.
• Risk: HIGH - Real-time credential theft.
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- /blog
- https://discord.com/blog
- /login
- https://discord.com/login
📡 API Calls Detected
- https://www.google.com/ccm/geo
- https://hubspotonwebflow.com/assets/js/blockedDomains.json
- POST
- GET
Similar Websites
Pages with identical visual appearance (based on perceptual hash)

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.