
Phishing Analysis
Detailed analysis of captured phishing page
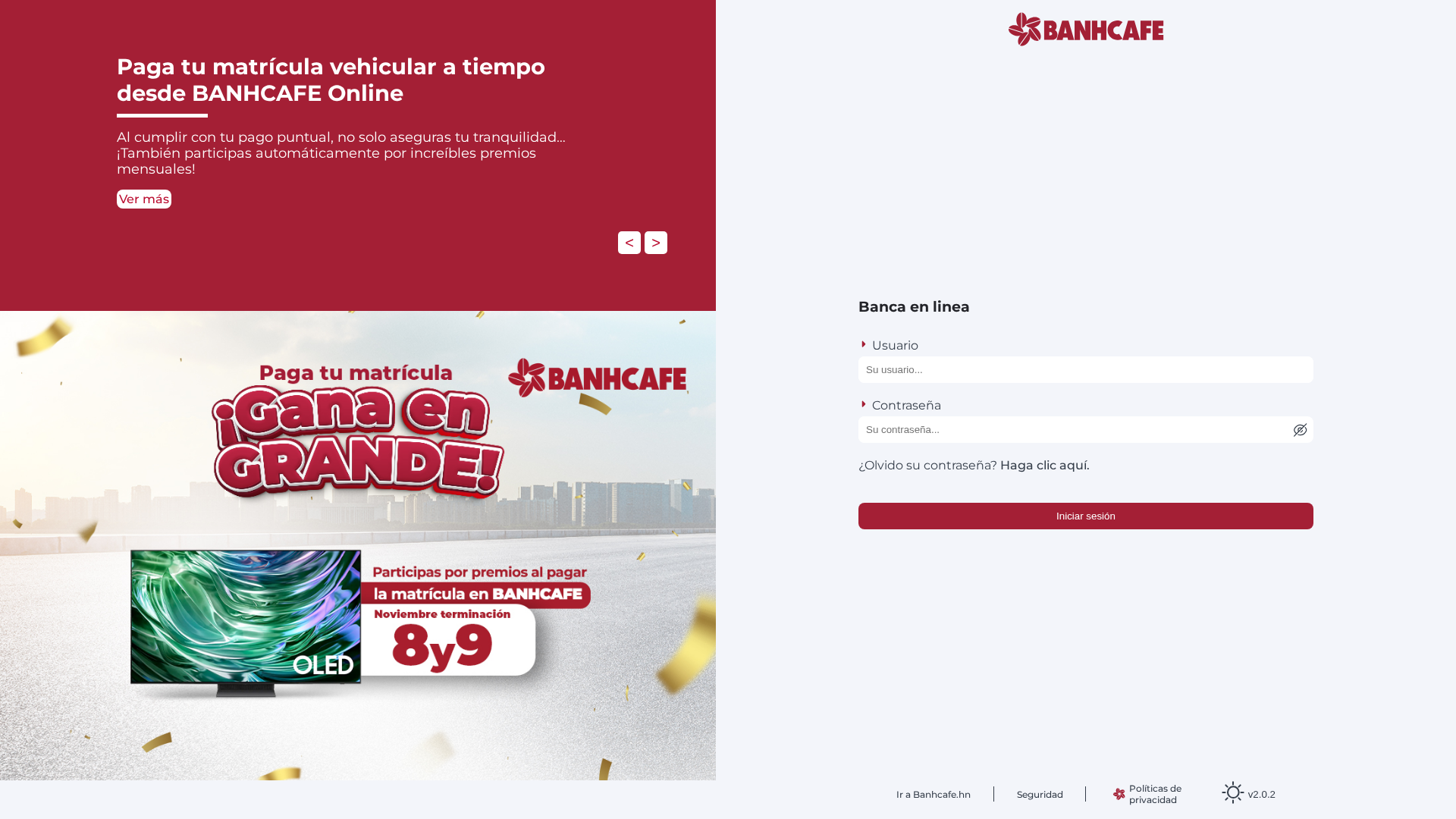
Visual Capture
Detection Info
https://creditohondura.vercel.app/
Detected Brand
BANHCAFE
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
4e39ccd7-df8…
Analyzed
2026-04-03 11:14
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1B45209E243545AACA2438FE4EF267B2A319B60FDDB9A4740C17517D0A5D6BCCE81BC20 |
|
CONTENT
ssdeep
|
192:WehYRPVLfaEI5LMsNpgaIho7700vNybQ3OJbQk2e/94+IEbQMRz7+nBunWAi5k:BCdLaoykho7EEGoeO+IEPJ7+n0nWAiG |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
bb31017fec874919 |
|
VISUAL
aHash
|
0f0f0f9f9f9f1fff |
|
VISUAL
dHash
|
9b9adb3e337378db |
|
VISUAL
wHash
|
0f0f0f8f89090f6f |
|
VISUAL
colorHash
|
06000000007 |
|
VISUAL
cropResistant
|
9b9adb3e337378db,0ae0c0d890936b84,99aa69e98b359b68,0000003232300810,cb8d65a5a3d3cd1b |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
Discord Webhook
🔐 Credential Harvesting Forms
📡 API Calls Detected
- https://api.ipify.org?format=json
📤 Form Action Targets
- hdhdh.php
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer
Credential Harvesting
Credential harvesting detected with 2 form(s) capturing sensitive data
Discord Exfiltration
Data exfiltration via Discord webhooks (1 webhook(s) exposed)
🔬 Comprehensive Threat Analysis
Threat Type
Two-Factor Authentication Stealer
Target
BANHCAFE users
Attack Method
credential harvesting forms
Exfiltration Channel
Discord Webhooks (1 detected) + HTTP POST to backend
Risk Assessment
CRITICAL - Automated credential harvesting with Discord Webhooks (1 detected) + HTTP POST to backend
⚠️ Indicators of Compromise
- 1 Discord webhook(s)
- Kit types: Credential Harvester, OTP Stealer
🏢 Brand Impersonation Analysis
Impersonated Brand
BANHCAFE
Official Website
N/A
Fake Service
Credential harvesting service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: Client-Side Form Interception
JavaScript intercepts form submissions before they reach the fake backend. This allows real-time credential harvesting and validation without server round-trips.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
creditohondura.vercel.app
Registered
Unknown
Registrar
Unknown
Status
Hosting platform (subdomain)
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.