
Phishing Analysis
Detailed analysis of captured phishing page
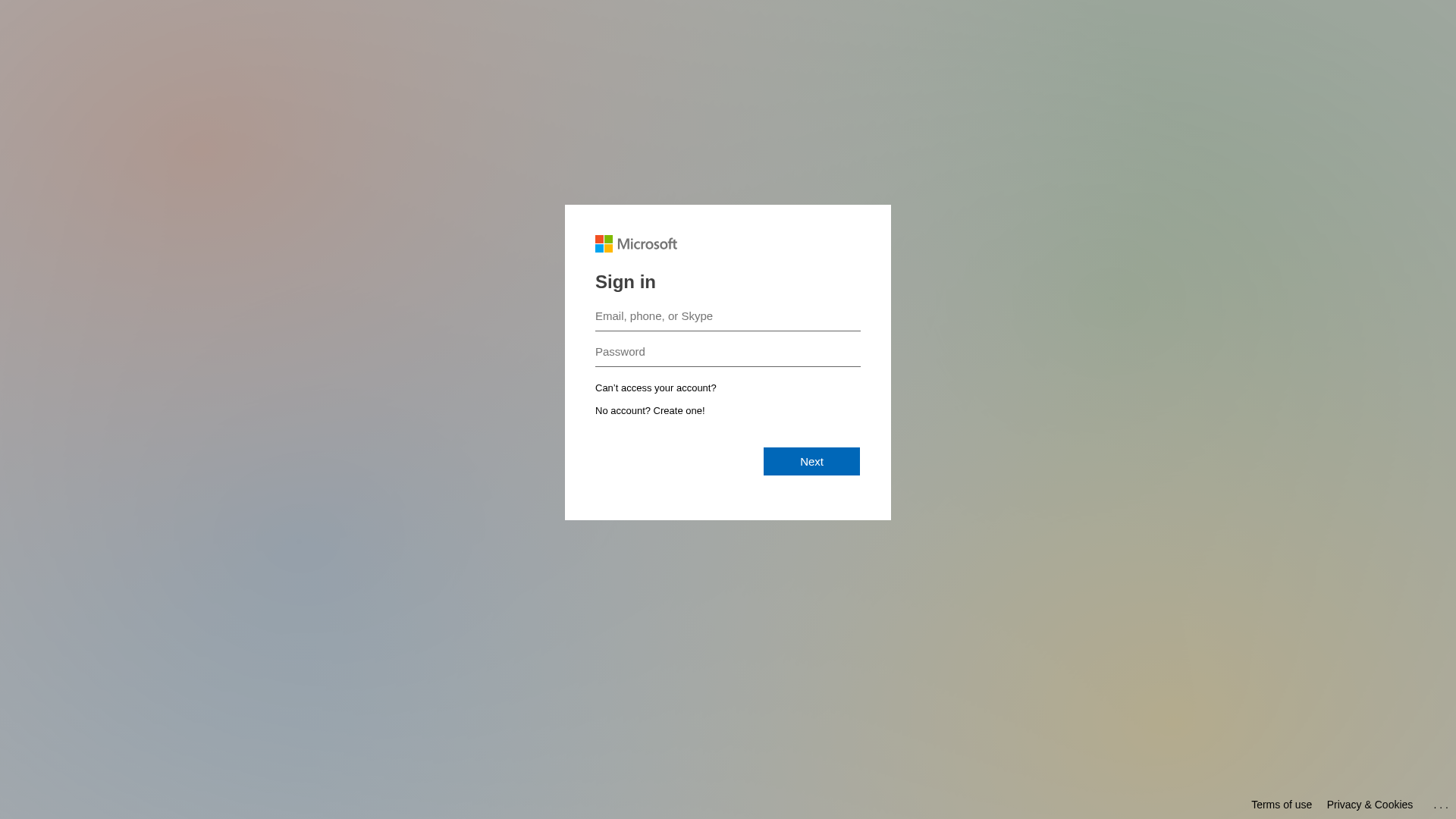
Visual Capture
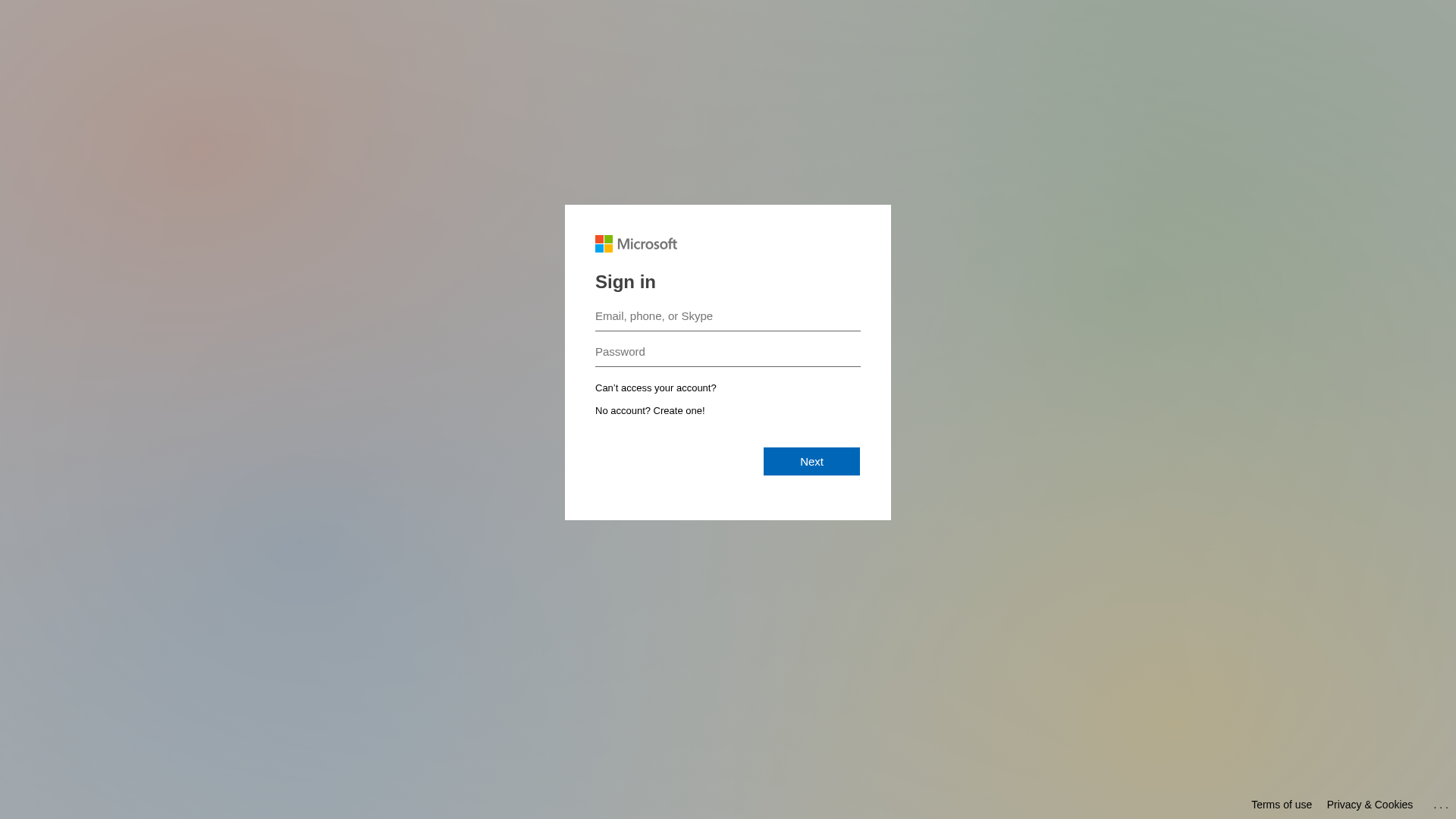
Detection Info
https://outlook-office365.mgamt.com/landing/form/18e77f9c-cdb4-4871-bc7b-c50a9fe8e37d
Detected Brand
Microsoft
Country
International
Confidence
95%
HTTP Status
200
Report ID
502f3150-31a…
Analyzed
2026-01-19 12:19
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T17641A81CD2010346E357EE90F962FBD666140BC0C7134A7C6AB9927AB1CE17553723CD |
|
CONTENT
ssdeep
|
48:n0i0Hls5hwhjO7c2ZgV0jxJF0jIPcU85D4c5hkj0:nfjhh7xg6jxJqjJTt4g5 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9cc97326cc99d98c |
|
VISUAL
aHash
|
0000181818180000 |
|
VISUAL
dHash
|
6171333232327c78 |
|
VISUAL
wHash
|
1818181c1f1f1fff |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
6171333232327c78 |
Code Analysis
Risk Score
50/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🔬 Threat Analysis Report
• Threat: Credential harvesting phishing kit
• Target: Microsoft users
• Method: Fake login form stealing email/phone/Skype and password
• Exfil: Unknown, likely sent to attacker's server
• Indicators: Domain mismatch, unofficial branding, login form
• Risk: HIGH - Immediate credential theft
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Microsoft
https://mgamt.com/landing/form/779d0071-1dcc-4633-902a-d8ea2...
Apr 05, 2026
Microsoft
https://secure-datalink.org/landing/form/5a7d3a80-9d8f-4fab-...
Apr 05, 2026
Microsoft
https://secure-datalink.org/landing/form/f5dfd805-5551-46ee-...
Mar 29, 2026
Microsoft
https://outlook-office365.mgamt.com/landing/form/259885eb-96...
Mar 25, 2026
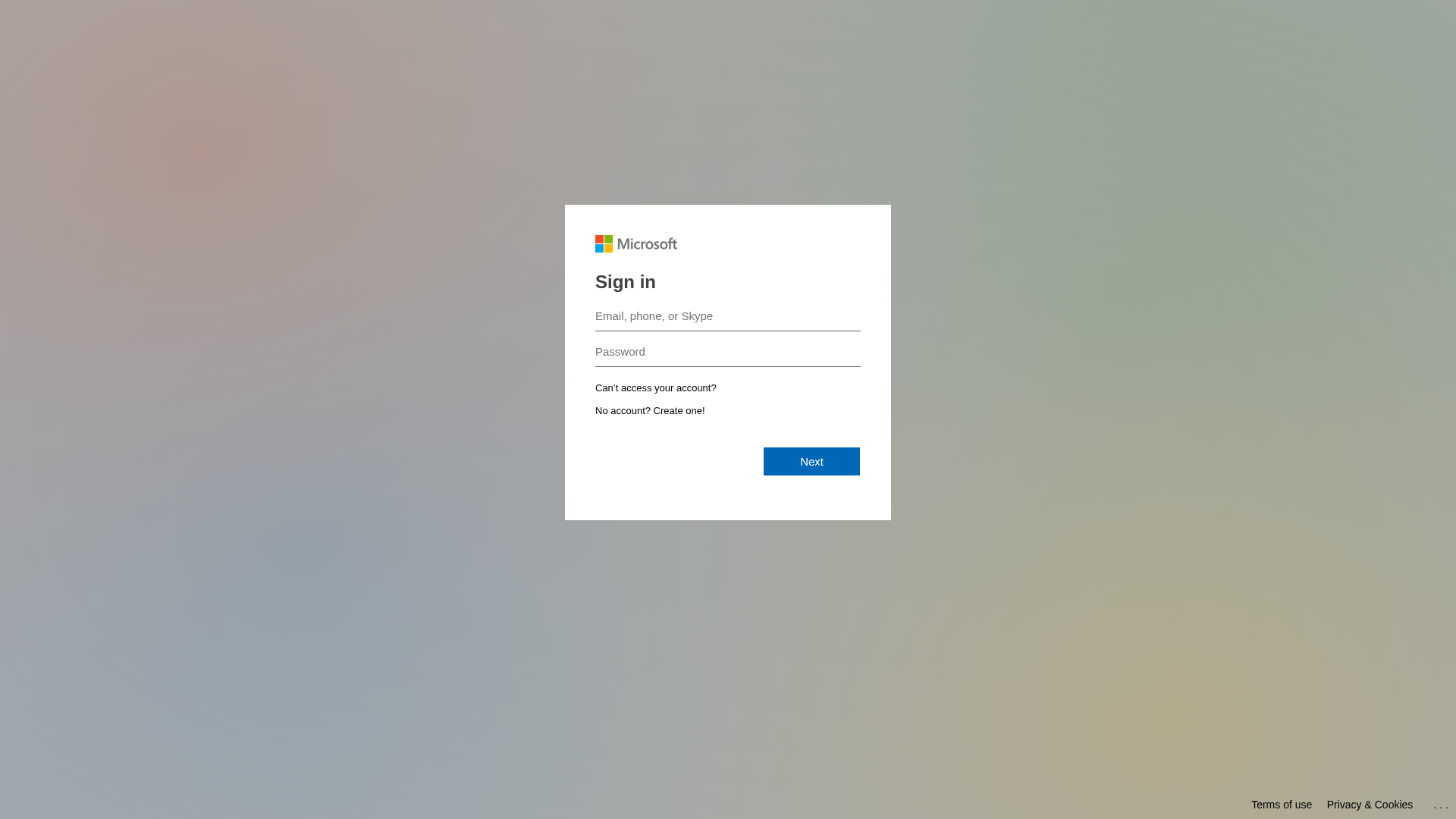
Microsoft
https://mgamt.com/landing/form/ede3e395-327d-4ce9-a5ad-714f8...
Mar 25, 2026
Scan History for outlook-office365.mgamt.com
Found 2 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.