Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1CD93C8B29251243320BFB1D5F1297709A2D3D74EC68287D1E2FCA36B1ED6CA1F817856 |
|
CONTENT
ssdeep
|
1536:SSeXWnSrascuOhfor8BPmzzXXMd6MiucCOK:feXWdscuOokmzzXXMd6M1cCOK |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
a41363933cccecd6 |
|
VISUAL
aHash
|
0000f3dbffffffc3 |
|
VISUAL
dHash
|
c8c8a63638002606 |
|
VISUAL
wHash
|
000042c3dfffdfc3 |
|
VISUAL
colorHash
|
072000082c0 |
|
VISUAL
cropResistant
|
c8c8a63638002606 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Roblox Users
• Method: Domain spoofing & malicious Javascript.
• Exfil: /search
• Indicators: Misspelled domain, Javascript obfuscation and Form submissions.
• Risk: High
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://accountinformation.roblox.com
- /catalog
- /login?returlUrl=828077091
- https://www.roblox.com/info/blog?locale=en_us
- /login?returnUrl=
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://auth.roblox.com
📡 API Calls Detected
- https://help.roblox.com/hc/articles/30428367965460
- https://ro.blox.com/Ebh5?
- POST
- get
- GET
- https://apis.
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 167 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The site likely attempts to steal login credentials, potentially by prompting users to re-enter their Roblox login or other personal details, through forms submitted to /search endpoint.
Secondary Method: Malware Injection
The obfuscated Javascript could be used to redirect the user to a malware download or execute some other harmful code.
🌐 Infrastructure Indicators of Compromise
🦠 Malicious Files
Functions: sendData, submitForm
🔌 External APIs Abused
- account: null
- purpose: User account management and credential verification
📊 Attack Flow Diagram
User fills <input name='username'> → submitForm() → sendData() → fetch('https://api.roblox.com')
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : None
- : Light
- : Heavy
- : None
- : None
- : Light
- : None
- : None
- : None
- : Light
- : Light
- : None
- : Light
- : None
- : Heavy
- : None
- : Heavy
- : Light
- : Heavy
- : None
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
User fills <input name='username'> → submitForm() → sendData() → fetch('https://api.roblox.com')
🎯 Malicious Files Identified
0c2a7c793ed0761b93b214956992ffb44014abcb404fd8bd2f9a7eb32ea0a600.jsMalicious Functions
sendDatasubmitForm
🌐 External APIs Abused
-
Roblox
Purpose: User account management and credential verification
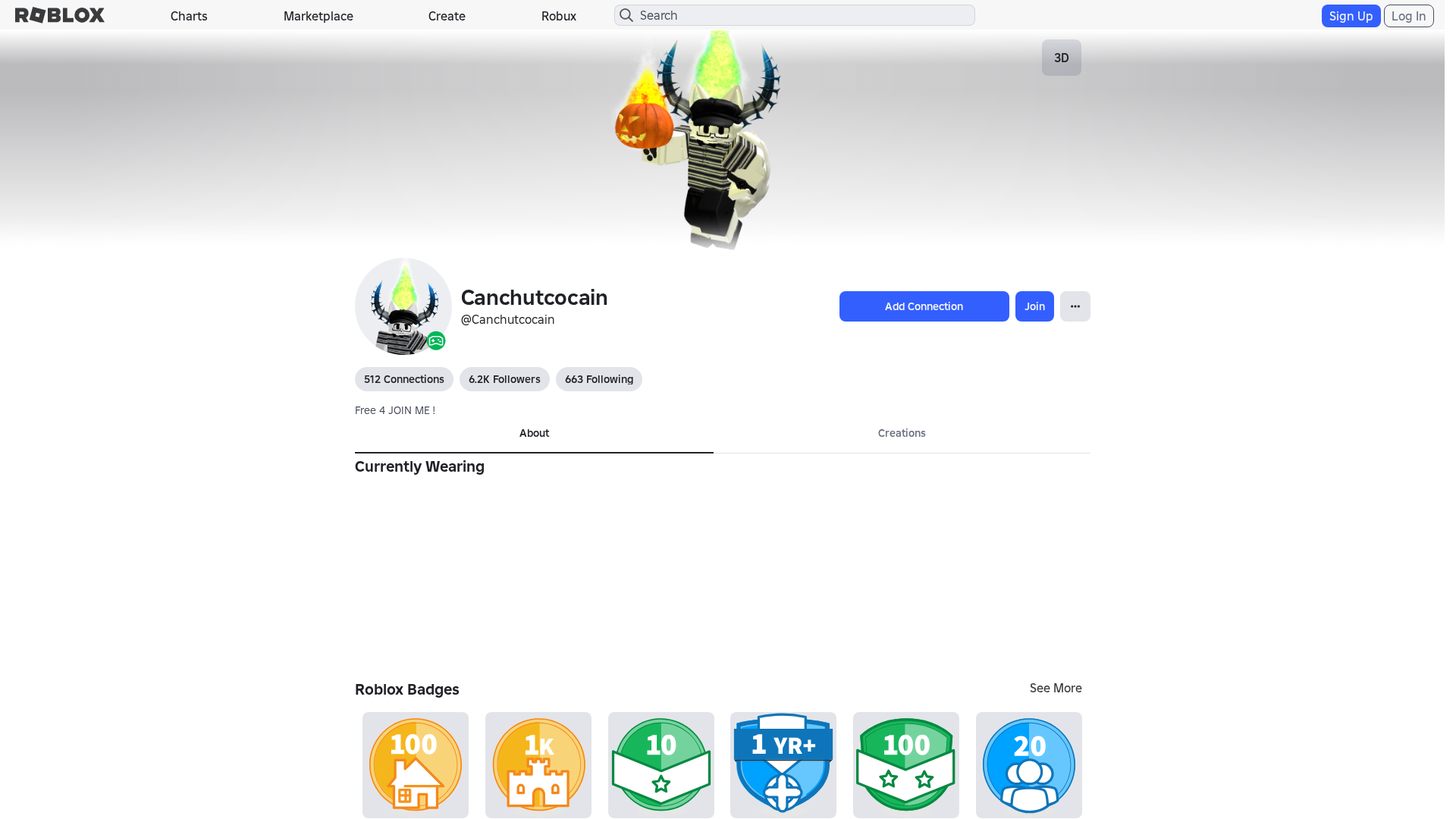
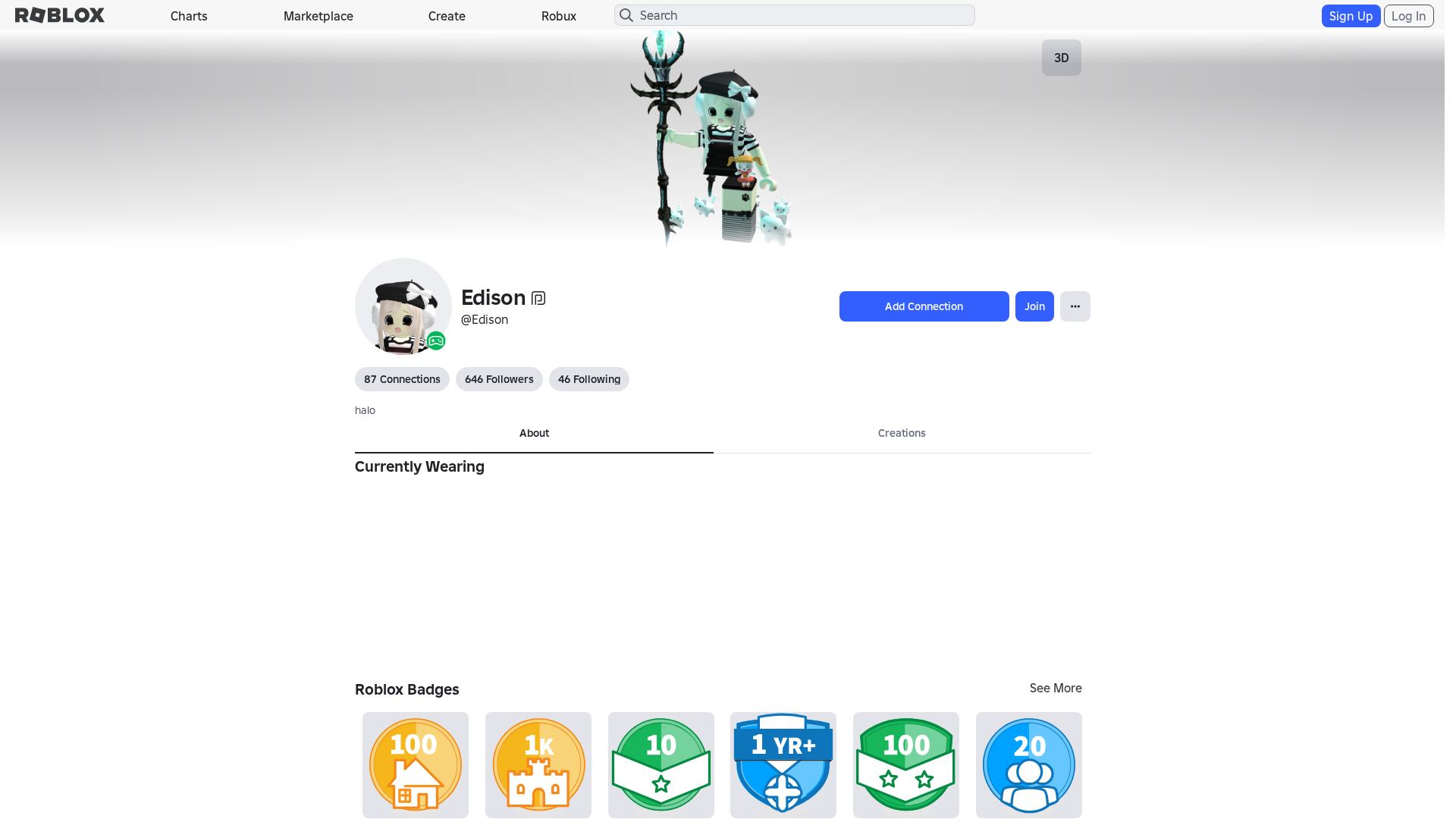
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for www.robloxr.com.es
Found 2 other scans for this domain